On November 5, 2025, multiple high-profile YouTube creators reported receiving fake DMCA takedown notices that linked to malicious downloads, prompting researchers to analyze the campaign and disclose numerous related domains and IPs. Public analysis identified phishing domains (e.g., dmca-security[.]com, ms-team-ping4[.]com), rotating infrastructure with distinctive host banners and certificates, and additional related domains discovered via DNS and host-response pivots. #dmca-security #ms-team-ping4
Keypoints
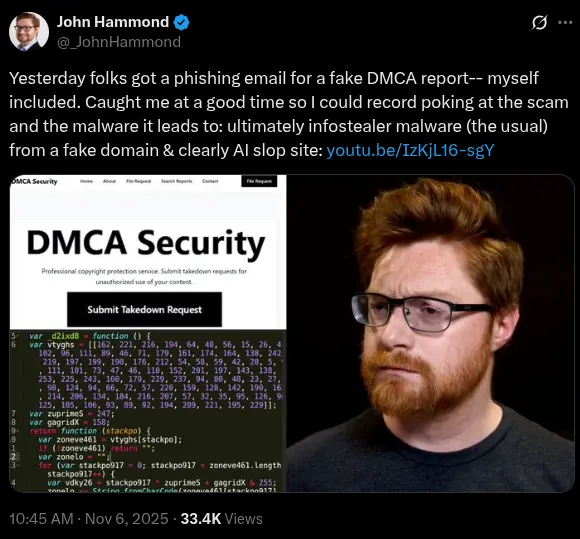
- High-profile victims (Scott Manley, John Hammond) reported fake DMCA takedown emails that led to malicious downloads and credential-stealing malware.
- Initial indicators included dmca-security[.]com and a set of ms-team-ping*.com domains that were pivoted on via Validin, Shodan, and any.run.
- DNS-history pivots revealed short-lived IP resolutions (e.g., 101.99.92[.]246, 101.99.89[.]94) and newly observed domains like dmca-abuse[.]video tied to those IPs.
- Host-response and banner/header hashing in Validin uncovered large clusters of lookalike domains (DMCA-themed and MS-themed) and additional domains not previously reported.
- C2 infrastructure showed many rotating IPs returning similar self-signed certificates and banner hashes (e.g., BANNER_0_HASH 5dab1fa5f7d42e5eca2385ce3dad1f03), allowing further pivots.
- Some IPs and domains appear to use DGA-like naming and short-lived hosting, complicating attribution but enabling hunting via favicon/header/hash-based pivots.
- Validin’s multi-layered DNS and host-response data was used to expand the indicator set to dozens of domains and IPs for defensive blocking and hunting.
MITRE Techniques
- [T1566] Phishing – Threat actors sent fake DMCA takedown emails to trick content creators into downloading malicious files (“fake DMCA takedown notices with links to malicious downloads”).
- [T1204] User Execution – Lures encouraged victims to download and run malicious executables from provided links (“links to malicious downloads” and “malicious executable reached out to ms-team-ping4[.]com”).
- [T1588] Acquire Infrastructure – Operators registered multiple lookalike domains and used Cloudflare proxies and short-lived IP hosting to support the campaign (“domain names … registered … hosted behind Cloudflare proxies” and “IPs … rotating regularly”).
- [T1598] Phishing as a Service / Malicious Domains – Use of many lookalike DMCA and Microsoft-themed domains to create convincing pages and hosting for payloads (“ms-team-ping*[.]com … ms-onedrive-updater*[.]com … dmca-security[.]com”).
- [T1071] Application Layer Protocol – Malicious activity and C2 communications observed over HTTP/S and unique banner/header signatures on ports 80/443 and RDP on port 3389 (“returned features on port 443 … unique certificate on port 3389 (RDP)”).
- [T1583] Acquire Domain Names – Large set of lookalike and typosquatted domains created to impersonate DMCA/Youtube/Microsoft related services (“list of likely related domains … dmca-guardian[.]com … youtube-dmca[.]com”).
Indicators of Compromise
- [Domain ] initial phishing domain and related campaign domains – dmca-security[.]com, ms-team-ping4[.]com (and dozens more listed in the article such as dmca-abuse[.]video and ms-team-ping7[.]com).
- [Domain ] lookalike and tool-themed domains used in pivots – ms-onedrive-updater1[.]com, bucket-aws-s1[.]com (and many similar domains like ms-team-connect[.]com and payments-adsense[.]com).
- [IP ] short-lived hosting and C2 candidates – 101.99.92[.]246, 101.99.89[.]94 (used briefly after registration and for DNS pivots).
- [IP ] banner/certificate cluster associated with C2-like behavior – 45.80.231[.]244, 185.153.198[.]115 (observed in any.run analysis; 45.80.231[.]244 returned a distinctive banner hash 5dab1fa5f7d42e5eca2385ce3dad1f03).
- [Hash/Favicon/Banner ] host-response cookie (feature) identifiers used for pivots – FAVICON_HASH 863a129608d053b67081c8243c72e9e1, BANNER_0_HASH 5dab1fa5f7d42e5eca2385ce3dad1f03, header hash d40097143f9b1abeee08 (used to find additional related domains).
Read more: https://www.validin.com/blog/fake_dmca_notice_scam_hunting/