Ransomware attacks surged to 623 incidents in October 2025, the second-highest monthly total on record, driven by groups such as Qilin, Akira, Sinobi, Medusa, Cl0p, Warlock, BlackSuit, The Gentlemen, and others. Key exploited vulnerabilities and tactics included CVE-2025-61882 (Oracle E-Business Suite), CVE-2025-10035 (GoAnywhere), deserialization RCEs, abuse of legitimate remote management tools, and supply-chain targeting. #Qilin #Sinobi
Category: Threat Research
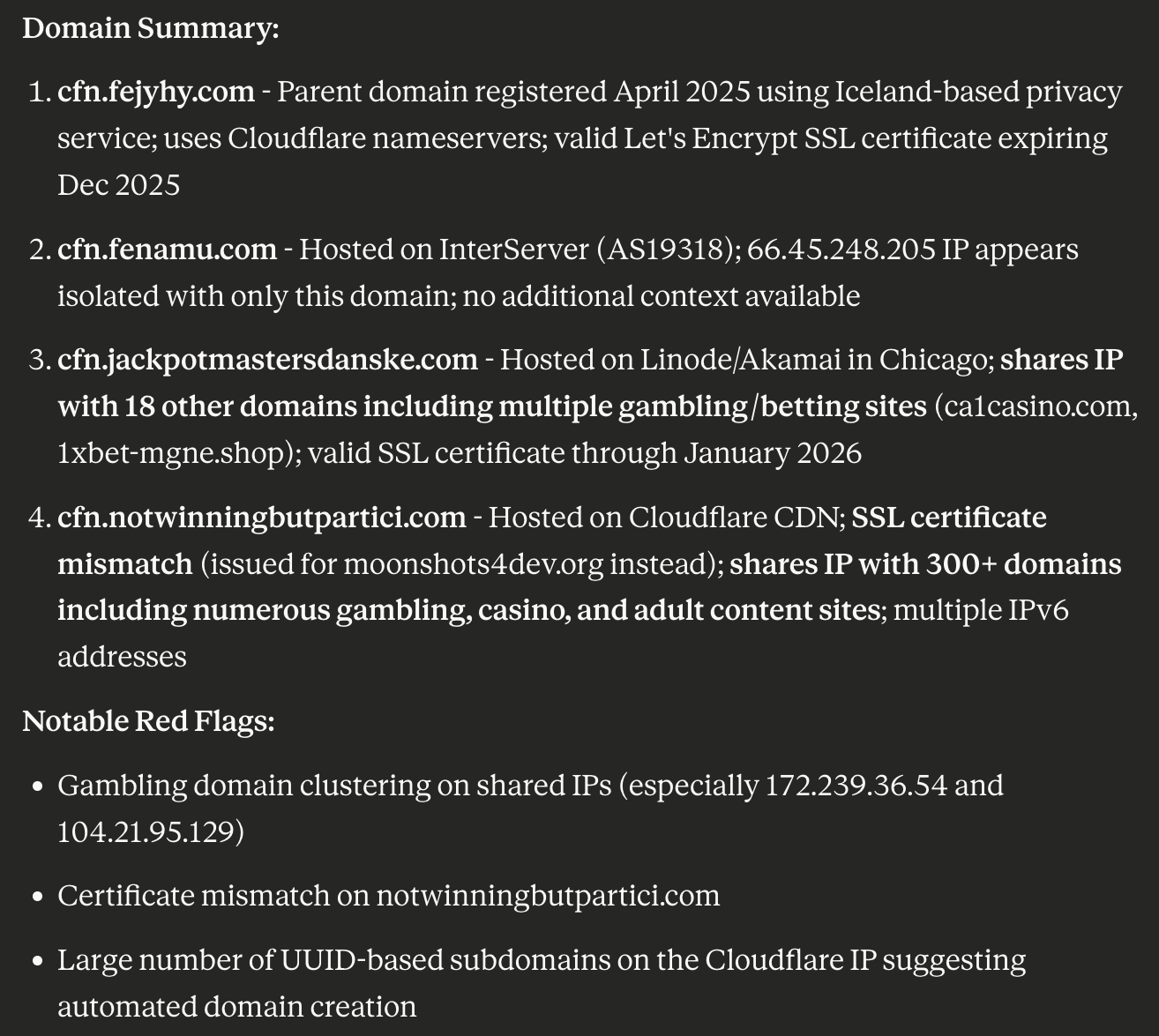
Socket Threat Research Team uncovered 175 malicious npm packages used in the Beamglea phishing campaign that targeted over 135 industrial, technology, and energy companies and were downloaded more than 26,000 times as of 9 October 2025. Researchers identified 16 IoCs (subdomains, domains, emails), tracked domain/IP histories and registrations, and found broad infrastructure links including gambling sites, SSL mismatches, and 344 email-connected domains. #Beamglea #fejyhy.com
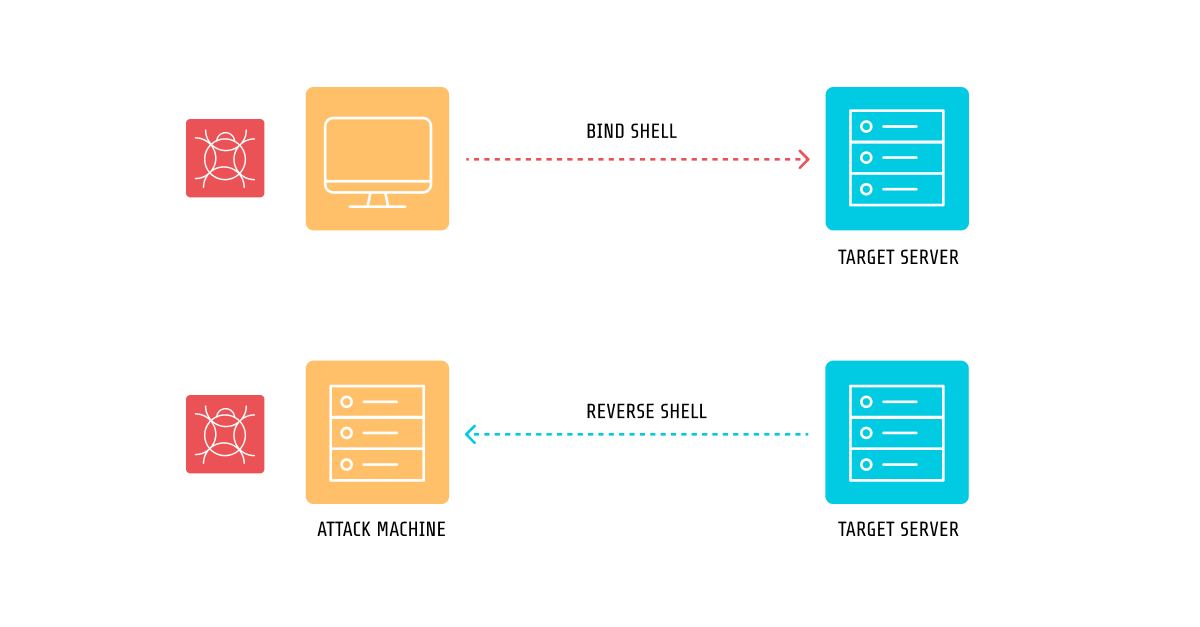
Sysdig describes the anatomy of TCP reverse shells, categorizing them into three types (direct shell with network-redirected I/O, indirect shell via IPC, and direct command execution without an actual shell) and explains associated syscalls and detection challenges. The article details how Sysdig improved Falco/Sysdig rules — including new proc.stdin/stdout/stderr fields and stateful observation rules — to reduce false positives and detect complex multi-step reverse shell techniques. #Falco #Sysdig #ReverseShell

Ransomware activity in Q3 2025 remained high and fragmented, with a record 85 active extortion groups and an average of about 535 victims per month, driven largely by small affiliates and a few dominant operators. LockBit resurfaced with LockBit 5.0 while Qilin became the most active group, and targeted campaigns shifted regional and sector concentrations such as Qilin’s focus on South Korea’s financial sector. #LockBit #Qilin
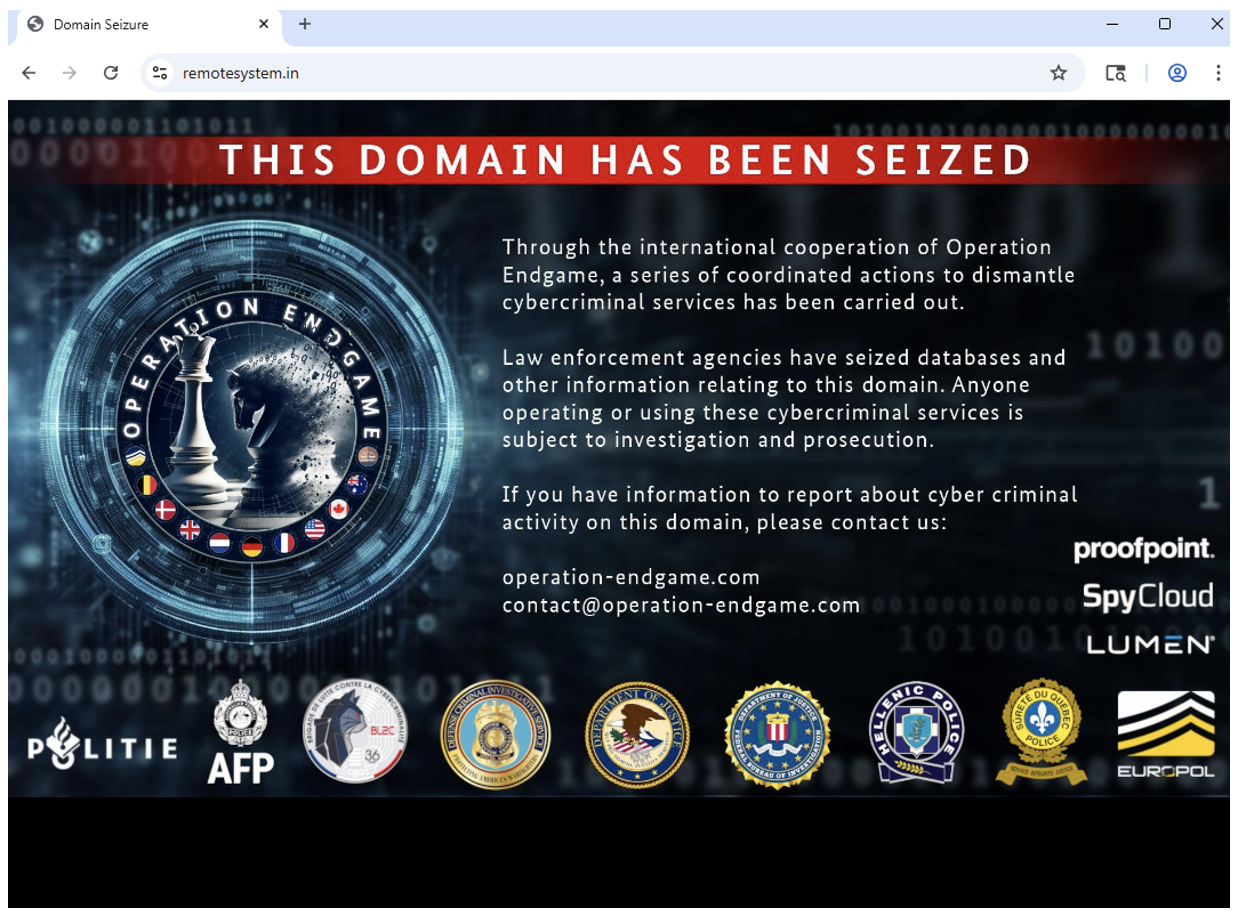
VenomRAT, a Quasar RAT derivative used by multiple cybercriminal actors—most notably TA558—was disrupted by U.S. and international law enforcement on 13 November 2025, with the seizure of distribution and licensing domains and the arrest of the suspected creator in Greece. Proofpoint observed rising VenomRAT usage in email campaigns through mid-2024–2025, and…

Cisco Talos observed the Russian-speaking Kraken ransomware group (linked to HelloKitty) conducting big-game hunting and double-extortion attacks using SMB exploitation for initial access, Cloudflared for persistence, and SSHFS for data exfiltration before deploying cross-platform encryptors that append .zpsc and drop a “readme_you_ws_hacked.txt” ransom note. Kraken benchmarks victim machines to choose full…
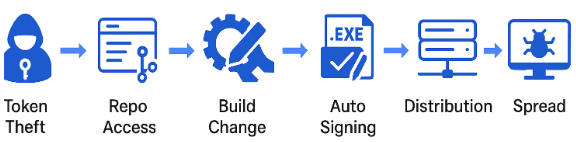
Cato researchers found two default-configuration flaws in Anthropic’s MCP SDK that enable browser-based OAuth token theft, allowing attackers to hijack developer identities and inject malicious code into CI/CD pipelines. The issue can lead to signed, tampered software updates being distributed across vendor-managed supply chains. #AnthropicMCP #CatoCTRL

Socket’s Threat Research Team discovered a malicious Chrome extension named Safery: Ethereum Wallet that steals users’ BIP-39 seed phrases by encoding them into synthetic Sui-style addresses and broadcasting microtransactions from a threat actor-controlled Sui wallet. The extension uses a hardcoded Base64 threat actor mnemonic to send tiny SUI payments to those derived addresses, enabling the actor to decode recipients and reconstruct victims’ full seed phrases. #Safery #Sui
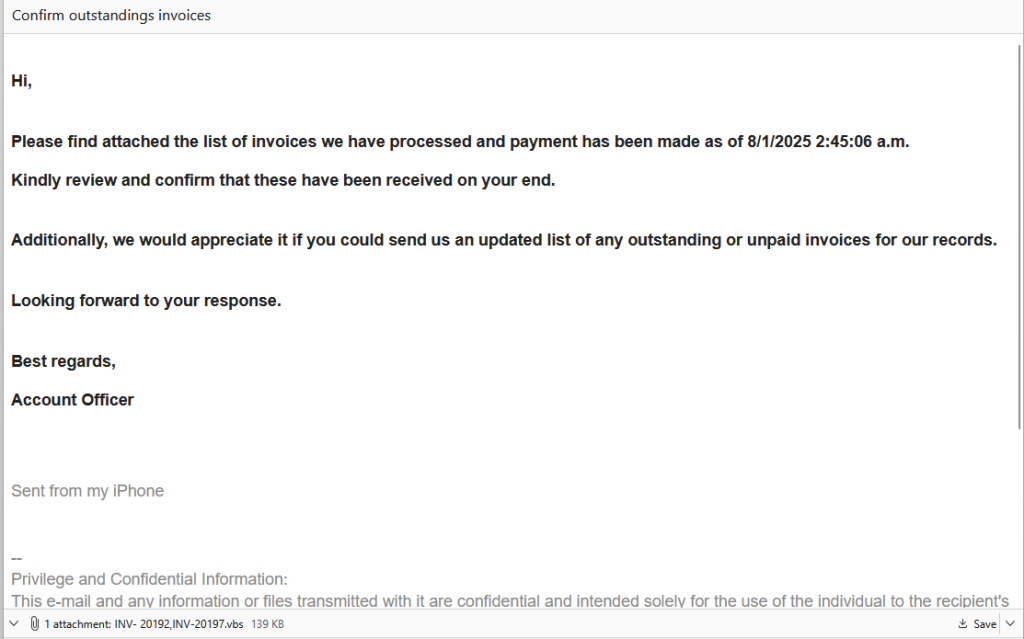
A malicious email with a Visual Basic Script (.vbs) invoice attachment delivered a multi-stage loader that ultimately deployed Backdoor.XWorm, a remote-access trojan capable of stealing data, keylogging, spying, and installing other malware. The attack used obfuscated .vbs and .bat scripts to drop a PowerShell loader that decoded, decrypted, decompressed, and executed…
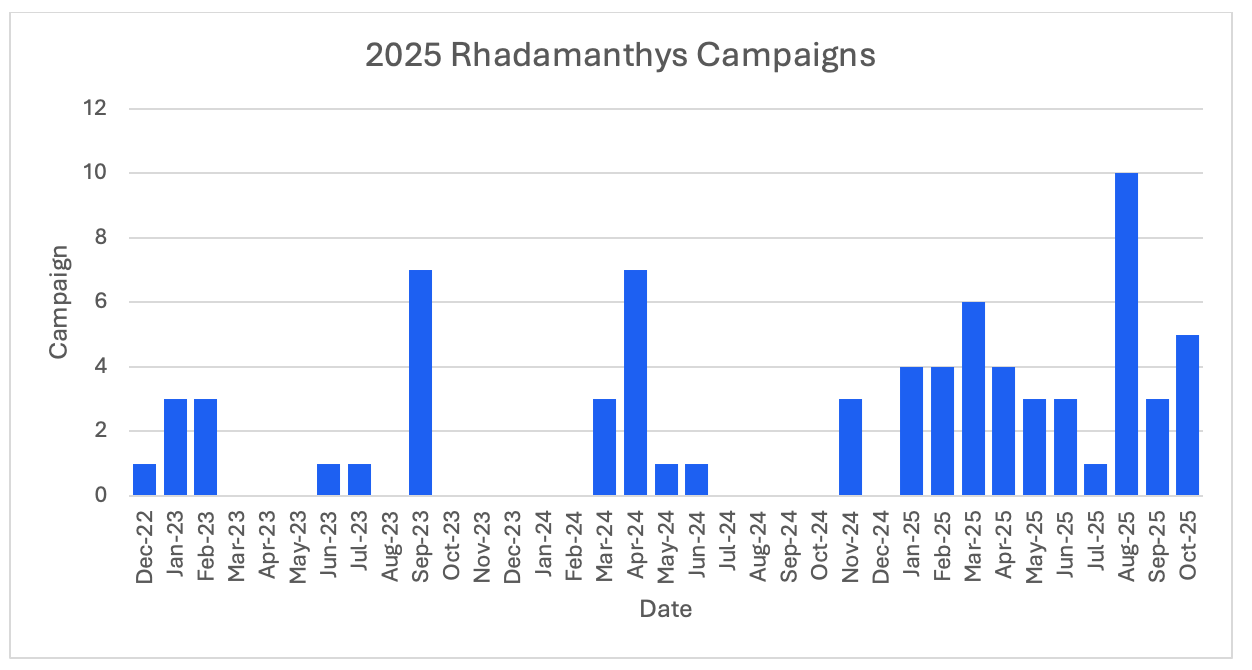
Rhadamanthys is a modular information stealer first observed in 2022 that has been widely sold and used by multiple threat actors and delivered via email, web injects, malvertising, ClickFix social engineering, and compromised sites. Law enforcement disrupted its infrastructure and affiliated services during Operation Endgame, impacting its ecosystem and associated services…

Yurei is a Go‑based ransomware first identified in September 2025 that encrypts corporate files using ChaCha20‑Poly1305 and protects per-file encryption keys with secp256k1‑ECIES, then extorts victims via a dedicated dark web site. Known victims include organizations in Sri Lanka and Nigeria across transportation, IT software, marketing and food & beverage, with…

Attackers are sending spoofed “Email Delivery” notifications that redirect through cbssports[.]com to a phishing site on mdbgo[.]io which harvests credentials via an obfuscated site and a websocket for instant exfiltration and possible 2FA prompts. Unit42 alerted to similar campaigns; this variant includes base64-encoded spoofed addresses in links and personalized fake login…

Threat actors modified the open-source SteamCleaner tool, repackaged it as Setup.exe, and distributed it from malicious GitHub repositories and redirect pages to install malware that deploys Node.js-based backdoors communicating with multiple C2 servers. The malware includes sandbox evasion, installs persistent scheduled tasks, and can execute arbitrary commands via two Node.js scripts…

Threat intelligence has shifted from a tactical defensive tool to a strategic, enterprise-wide capability used to inform board-level decisions, procurement, risk tolerance, and incident response planning. Recorded Future’s 2025 report shows widespread adoption—83% run full-time intel teams and organizations use intelligence across security, GRC, and executive functions. #RecordedFuture #2025StateOfThreatIntelligence

AhnLab ASEC observed attacks where threat actors abused legitimate RMM tools LogMeIn Resolve and PDQ Connect to deploy the PatoRAT backdoor by luring users to fake utility download pages that install the RMM client disguised as common programs. The campaigns used multiple LogMeIn CompanyId values and C2 domains such as patolino.theworkpc.com…
