Rhadamanthys is a modular information stealer first observed in 2022 that has been widely sold and used by multiple threat actors and delivered via email, web injects, malvertising, ClickFix social engineering, and compromised sites. Law enforcement disrupted its infrastructure and affiliated services during Operation Endgame, impacting its ecosystem and associated services like Elysium Proxy Bot. #Rhadamanthys #ElysiumProxyBot
Keypoints
- Rhadamanthys is a commercially marketed, modular information stealer (MaaS) first seen in 2022 and actively developed with frequent feature updates and evasion techniques.
- The malware is sold with tiered pricing ($300–$500/month) and bundled with services like Elysium Proxy Bot and a Crypt Service, attracting a wide range of affiliates.
- Delivery vectors include email campaigns, ClickFix social engineering (copy-paste PowerShell), web injects on compromised sites, malvertising/SEO poisoning, PDFs with malicious HTA/PowerShell, and URLs leading to loaders like CastleLoader and DOILoader.
- Multiple threat actors and clusters have used Rhadamanthys, including TA571, TA866, TA2541, TA547, TA585, and unattributed groups such as “Aggah.”
- Rhadamanthys is frequently delivered by or alongside loaders and other malware (e.g., CastleLoader, DOILoader, zgRAT, SystemBC, GuLoader, Lumma, XLoader), enabling flexible attack chains and follow-on payloads.
- Operation Endgame law enforcement actions disrupted Rhadamanthys infrastructure and affiliates (November 13, 2025), likely degrading actor trust and availability of the service.
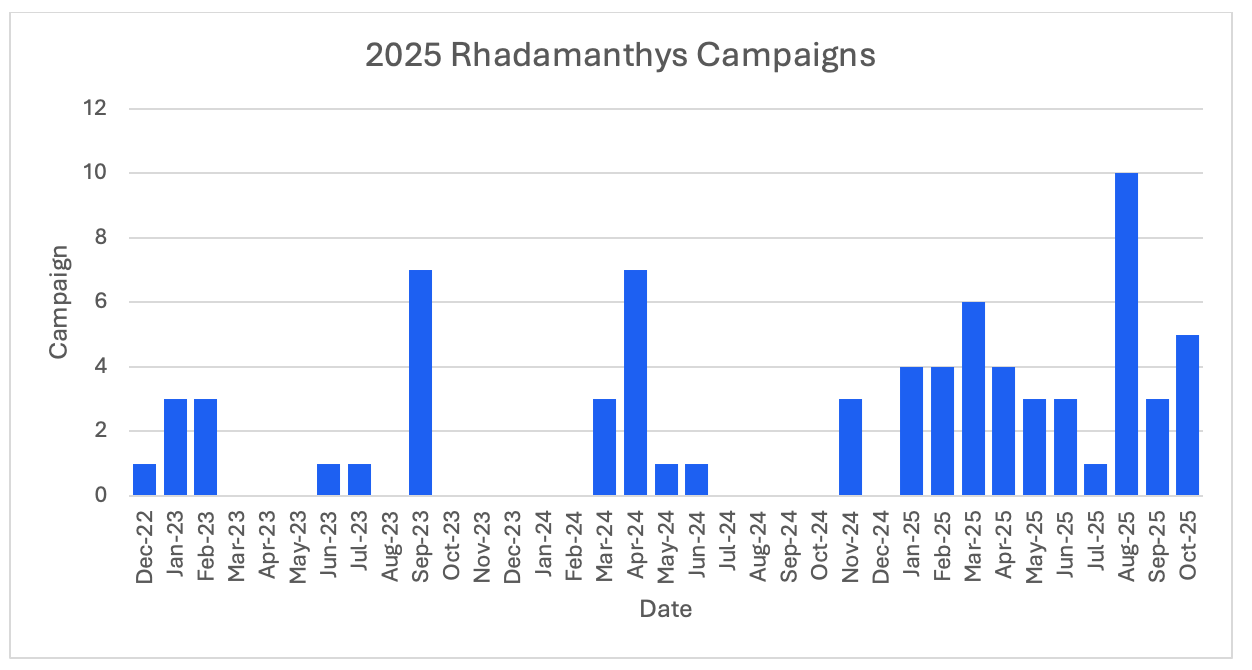
- Proofpoint observed increased Rhadamanthys activity in 2025, leveraging modularity, obfuscation, PNG steganography, OCR for seed phrases, and MSI installer execution to improve distribution and evasion.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used via ClickFix social engineering instructing users to “copy and paste PowerShell scripts” to run commands that download and execute payloads (“…copy and paste a malicious command in the run box…”).
- [T1204.002] User Execution: Malicious Link – URLs in phishing emails redirected targets to ClickFix or fake landing pages that induced command execution (“…messages contained URLs leading to a website instructing the recipient to sign a form and click ‘submit’… redirected to a ClickFix landing page”).
- [T1566.001] Phishing: Spearphishing Attachment – Malicious PDFs with links to fake DMCA/YouTube sites contained HTA payloads and linked artifacts that led to shellcode execution (“…messages contained a PDF with a link to a fake ‘Youtube DMCA’ themed website… executed an HTA script”).
- [T1204.002] User Execution: Malicious Instruction – ClickFix technique specifically coerced victims into executing commands via copy/paste into Run, effectively tricking users into self-infection (“…instructs the user to copy and paste a malicious command in the run box…”).
- [T1105] Ingress Tool Transfer – Attack chains downloaded archives and loaders (tar archive -> CastleLoader -> DOILoader -> Rhadamanthys), showing staged payload transfer (“…download a tar archive and run CastleLoader. CastleLoader was observed loading DOILoader and Rhadamanthys”).
- [T1055] Process Injection – Shellcode downloaded from a .bin was executed via VirtualAlloc + RtlMoveMemory + CreateThread into the Excel process to run Rhadamanthys in memory (“…executed it via classic shellcode injection using VirtualAlloc + RtlMoveMemory + CreateThread into the Excel process”).
- [T1027] Obfuscated Files or Information – Malware updates hardened packing and network obfuscation and reintroduced PNG steganography for hiding payloads (“…hardened network and packing obfuscation… reintroduced PNG steganography for hiding payloads”).
- [T1086] PowerShell – PowerShell scripts were used in social engineering chains (ClickFix) and as part of delivered commands to retrieve and execute payloads (“…advise people to copy, paste, and run PowerShell scripts to infect themselves with malware”).
- [T1112] Modify Registry – HTA enabled VBA macros via registry changes to allow Excel to run a downloaded macro (“…the HTA enabled VBA macros via registry changes and built an Excel workbook via COM in-memory”).
Indicators of Compromise
- [SHA256] example payload hashes – 13f0bf908679bea560806fd3c14ef581b3cadbab2ff07a6adf04d97995924707 (shielders.msi), b0c9d619256fdf220fbb39945fac5a040b5e836f1eae0459b4fcbf2b451420a7 (DpiChrysler.exe)
- [Domains] actor-controlled and ClickFix domains – strike-submit[.]com (ClickFix landing and payload URLs such as google[.]strike-submit[.]com/DMCA_Notice.hta), theguardshield[.]com, support-review[.]org
- [URLs] payload and C2 URLs – hxxps://84[.]200[.]80[.]8/gateway/53c06hop.fp0g1 (Rhadamanthys C2), hxxps://google[.]strike-submit[.]com/agreeses[.]bin (ClickFix payload)
- [IP Addresses] example infrastructure IPs – 85[.]192[.]61[.]140 (Rhadamanthys C2), 193[.]221[.]200[.]93 (Rhadamanthys C2)
- [File names] observed malicious filenames – shielders.msi, DpiChrysler.exe, kick.dat (ClickFix HTA payload), agreeses.bin
- [Other hashes] ClickFix payload hashes and HTA/PS1 hashes – bc2508708feb0ccc652494f8e28620bd871a8b6e1d26c7cdd61ab070f2594bbc (ClickFix payload), ff14b28408121ebe4a5d0c2f14b9dc99e987e89b56392dc214481197d4815456 (HTA)
Read more: https://www.proofpoint.com/us/blog/threat-insight/operation-endgame-quakes-rhadamanthys