A malicious email with a Visual Basic Script (.vbs) invoice attachment delivered a multi-stage loader that ultimately deployed Backdoor.XWorm, a remote-access trojan capable of stealing data, keylogging, spying, and installing other malware. The attack used obfuscated .vbs and .bat scripts to drop a PowerShell loader that decoded, decrypted, decompressed, and executed payloads directly in memory. #Backdoor.XWorm #IrisBud.bat
Keypoints
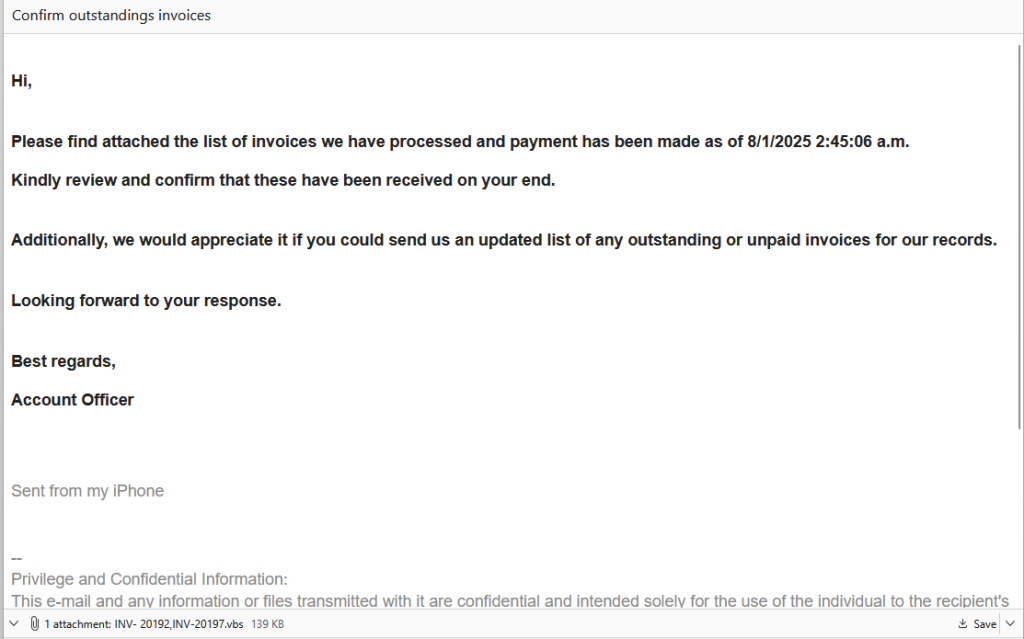
- The phishing email used a generic greeting and a .vbs attachment named INV-20192,INV-20197.vbs, which is highly suspicious for business correspondence.
- The .vbs dropped IrisBud.bat into %TEMP% and invoked it via WMI; the batch file copied itself to the user profile as aoc.bat and restarted minimized to run invisibly.
- The batch file contained heavy obfuscation and padding variables to hinder analysis; two comment-like lines (::) hid Base64 and encrypted payload data.
- A PowerShell loader extracted Base64 content and decrypted/decompressed payload data from aoc.bat, then loaded two executables directly into memory (fileless execution).
- The final payload was identified as Backdoor.XWorm (a MaaS RAT) capable of data exfiltration, keylogging, spying, and delivering additional malware including ransomware.
- IOCs include the attachment and dropped filenames plus a SHA256 hash; a known mutex (5wyy00gGpG6LF3m6) confirmed XWorm family attribution.
- Recommended defenses: verify unexpected attachments by known contact methods, never open executable-script attachments (.vbs/.bat/.exe/.scr), show file extensions, and keep real-time anti-malware updated.
MITRE Techniques
- [T1566 ] Phishing – The attacker sent a fraudulent invoice email with a malicious .vbs attachment to induce the recipient to open and execute the script. Quote: ‘Please find attached the list of invoices…’
- [T1204 ] User Execution – The .vbs file required the user to open the attachment, which then executed scripts and dropped further payloads. Quote: ‘If the recipient had opened the attached Visual Basic Script (.vbs) file, it would have quietly installed a remote-access Trojan known as Backdoor.XWorm.’
- [T1204.002 ] Malicious File – The initial delivery was a Visual Basic Script (.vbs) attachment used to run code on the host. Quote: ‘.vbs attachment named INV-20192,INV-20197.vbs.’
- [T1047 ] Windows Management Instrumentation – The .vbs invoked the batch via WMI to execute the next-stage payload. Quote: ‘The .vbs dropped IrisBud.bat into %TEMP% … and invoked it via WMI.’
- [T1059.005 ] Command and Scripting Interpreter: Visual Basic – The attack used a .vbs script to orchestrate dropping and execution of further scripts. Quote: ‘The .vbs file at first sight looked like alphabet soup…’
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – A heavily obfuscated .bat file (IrisBud.bat / aoc.bat) was used to persist, hide execution, and construct a PowerShell loader. Quote: ‘The .bat restarted itself in a way so it ran invisibly… copied itself to the user profile as aoc.bat.’
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – A PowerShell loader decoded Base64, removed padding, decrypted (AES), decompressed (GZip), and executed payloads directly in memory. Quote: ‘powershell.exe -nop -c … GetString([Convert]::FromBase64String(…))’ and ‘decrypts the data… decompresses it… loads and runs the malware… directly into memory.’
- [T1105 ] Ingress Tool Transfer – The script retrieved or reconstructed payload binaries from embedded data inside aoc.bat and loaded them into memory rather than saving to disk. Quote: ‘reads encrypted data from aoc.bat… decrypts the data… loads and runs the malware… directly into memory.’
- [T1053 ] Scheduled Task/Job (implicit persistence via copy and autorun) – The batch copies itself to the user profile and uses restart/minimized execution to maintain execution; indicative of persistence techniques. Quote: ‘copy “%sourceFile%” “%userprofile%aoc.bat”… cmd /c start “” /min “%~dpnx0” %* & exit’.
- [T1053.005 ] Service Execution / Hidden Window Execution (technique of hiding execution) – The batch restarts itself minimized and uses techniques to run without visible windows. Quote: ‘start “” /min … the new hidden instance continues running…’
Indicators of Compromise
- [Attachment Filename ] Malicious email attachment – INV-20192,INV-20197.vbs
- [Dropped File ] Temporary and profile-located scripts – IrisBud.bat (in %TEMP%), aoc.bat (in %user% folder)
- [Mutex ] Runtime artifact – 5wyy00gGpG6LF3m6 (associated with XWorm family)
- [File Hash ] Malware binary SHA256 – 0861f20e889f36eb529068179908c26879225bf9e3068189389b76c76820e74e (Backdoor.XWorm)