CyberProof investigated a campaign spreading Maverick (aka Maverik) banking malware via WhatsApp downloads, finding multi-stage obfuscated PowerShell and .NET loaders that contact zapgrande[.]com and other C2s to deliver banking-focused capabilities targeting Brazilian users and banks. Analysis shows code, encryption (AES+GZIP), persistence, and victimology similarities with Coyote/Coyote-Maverick campaigns and public reports by Kaspersky, Sophos, and TrendMicro. #Maverick #Coyote #zapgrande
Category: Threat Research

In October 2025 phishing email attachments were dominated by Trojans (47%), with notable use of document OLE downloaders and compressed JS files distributing malware like Remcos RAT. The report highlights Korean-language phishing campaigns, attachment-format case analyses, and provides example MD5 hashes for malware samples. #Remcos…
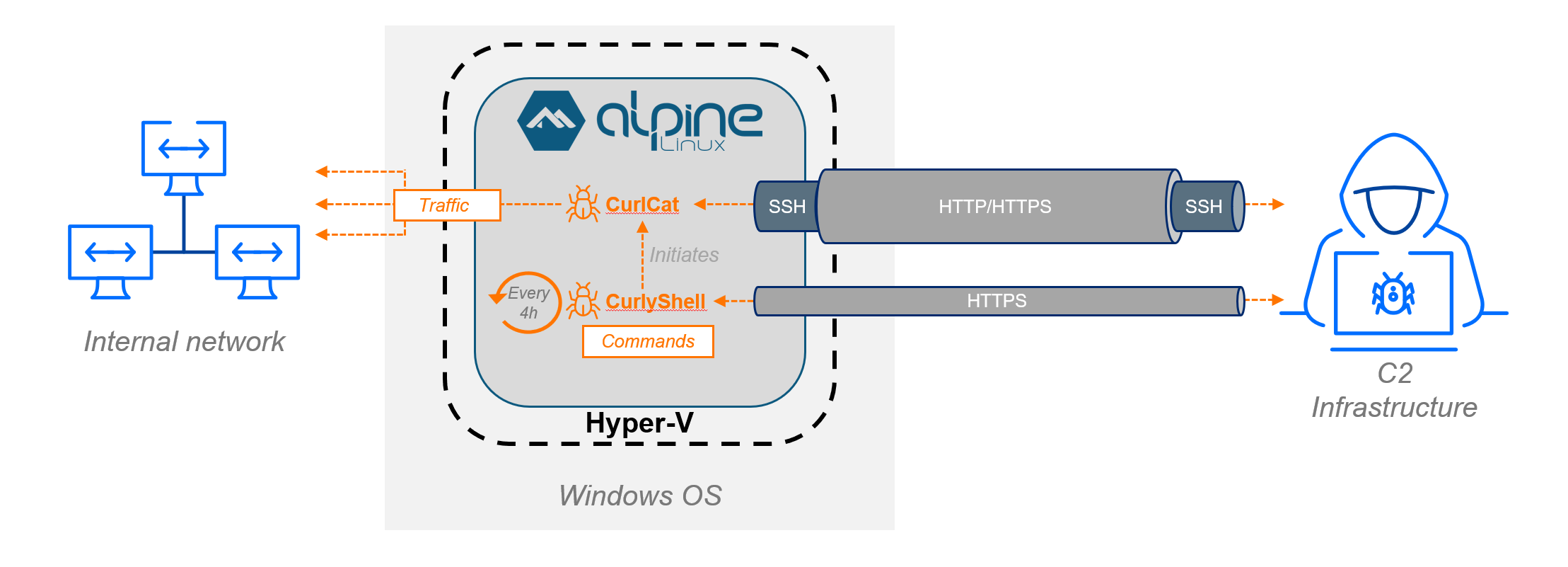
This investigation uncovered Curly COMrades’ novel use of Hyper-V on compromised Windows 10 hosts to run a hidden Alpine Linux VM that housed custom implants CurlyShell and CurlCat, enabling covert, persistent remote access and proxying. Collaborative forensic work with the Georgian CERT revealed deployment commands, PowerShell ticket-injection and persistence scripts, and C2 infrastructure details including SSH-over-HTTP tunneling via a compromised site. #CurlyShell #CurlCat
.jpg)
Episode 3 disclosures reveal APT35/Charming Kitten’s full malware development pipeline, including two RAT families (Saqeb System and RAT-2AC2), custom ASP webshells (m0s.asp variants), training materials, QA procedures, and operational tooling used from 2022–2025. The collection documents targeted regional operations against aviation, law enforcement, and infrastructure with preparations for ransomware (Moses’ Staff) and SCADA reconnaissance. #SaqebSystem #RAT-2AC2

SideWinder, active since at least 2012, conducts targeted cyber-espionage against military, government, and maritime organizations across the Indian Ocean and Mediterranean regions using spear-phishing with malicious Office documents that exploit CVE-2017-0199 and CVE-2017-11882 to deliver a modular in-memory backdoor called StealerBot. AttackIQ released an emulation/attack graph to validate defenses against SideWinder…

Pig-butchering scams are long-form investment frauds that combine extended social engineering, AI-fabricated personas, and fake trading platforms with sophisticated crypto-focused laundering and mule networks to generate tens of billions in annual losses. Investigations link organized criminal groups and militia-protected scam compounds (e.g., DKBA, GTSEZ, Prince Holding Group) to these operations, which have even precipitated institutional collapse such as the Heartland Tri-State Bank case. #DKBA #GTSEZ #PrinceHoldingGroup

AppleScript .scpt files are being repurposed as social-engineered macOS malware droppers, masquerading as fake documents, installers, or update prompts to trick users into executing scripts via Script Editor or Terminal. Samples tie into commodity stealers like MacSync and Odyssey and use techniques such as custom icons in ZIP/DMG containers and obfuscated AppleScript to evade detection. #MacSync #Odyssey
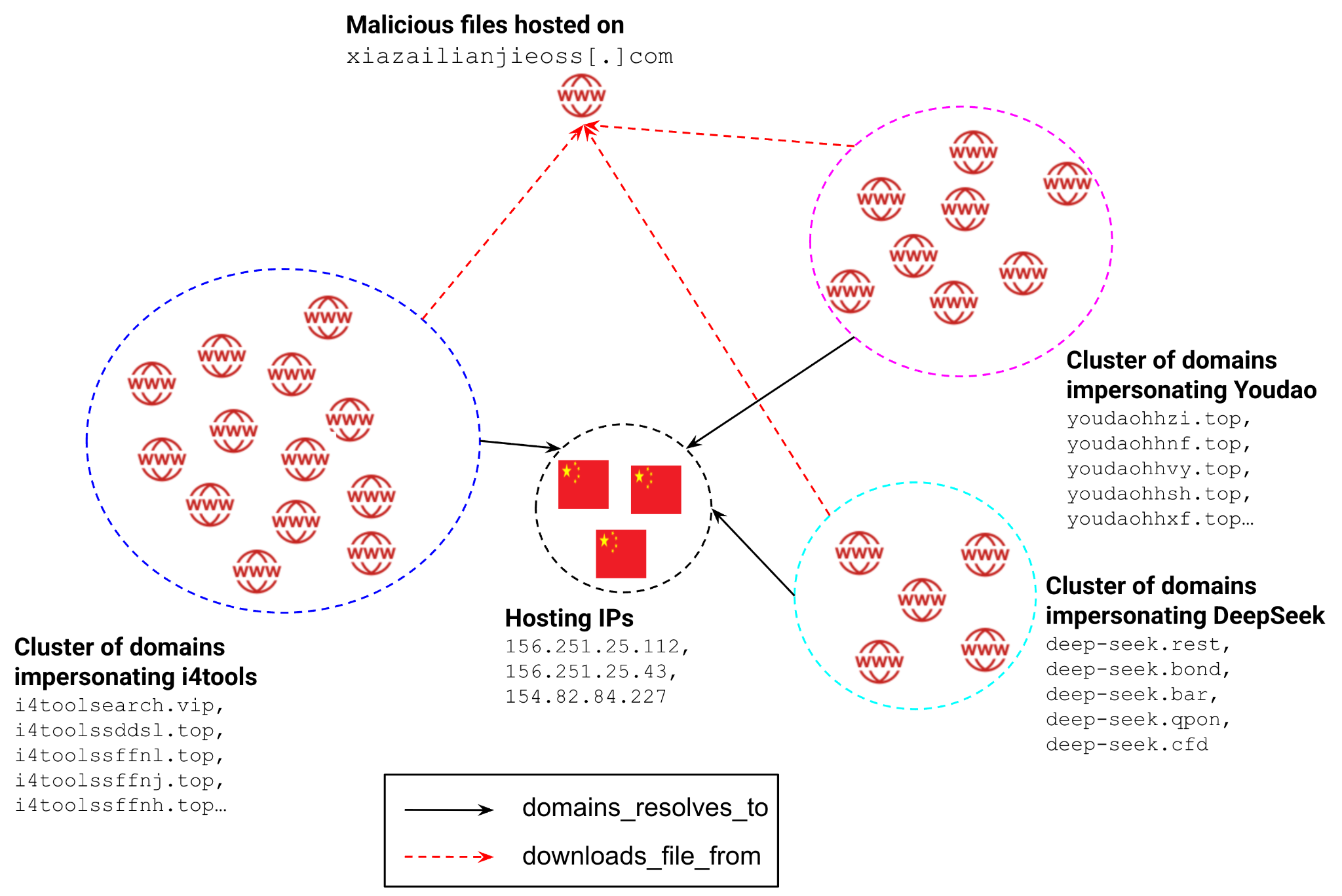
Two interconnected 2025 campaigns used large-scale brand impersonation to deliver Gh0st RAT variants to Chinese-speaking users, evolving from simple droppers to multi-stage chains that misuse signed software and cloud-hosted payloads for evasion. The campaigns registered thousands of disposable domains, hosted payloads on specific IPs and cloud buckets, and employed DLL side-loading…
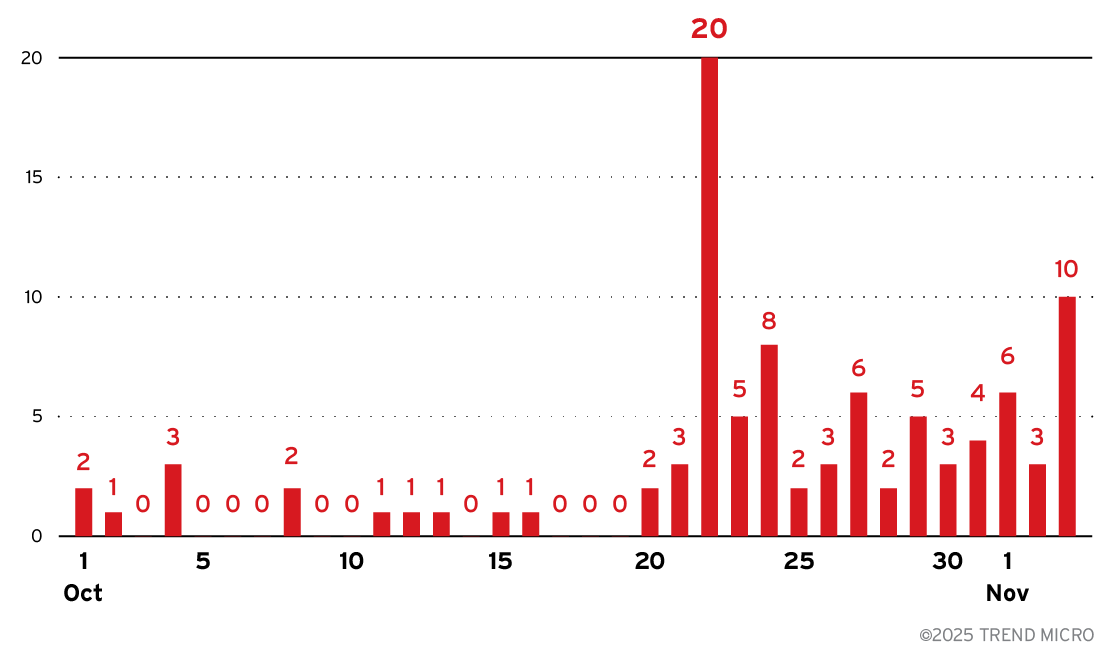
Trend Research observed a resurgence of Lumma Stealer (tracked as Water Kurita) activity beginning the week of October 20, 2025, and documented new command-and-control behavior that layers browser fingerprinting onto existing C2 protocols. The malware now uses JavaScript-based fingerprinting and stealthy HTTP communications to profile victims and guide targeted follow-on actions….

This article demonstrates using Microsoft WinDbg Time Travel Debugging (TTD) to accelerate dynamic analysis of an obfuscated multi-stage .NET dropper that performs classic process hollowing, allowing analysts to quickly locate CreateProcess* and WriteProcessMemory calls and extract an injected PE. The case study shows extracting an AgentTesla payload and configuration from memory by querying the debugger data model and using LINQ filters plus low-level commands like !tt, !dh, and .writemem. #AgentTesla #WinDbg

Elastic Security Labs uncovered a Chinese-language targeted campaign by Dragon Breath APT (APT-Q-27) distributing a modified gh0st RAT via trojanized NSIS installers and a unique loader dubbed RONINGLOADER. The multi-stage chain uses a signed kernel driver, WDAC policy tampering, PPL abuse of ClipUp to disable Microsoft Defender, and thread-pool based remote injection to terminate and bypass popular Chinese endpoint products. #DragonBreath #RONINGLOADER
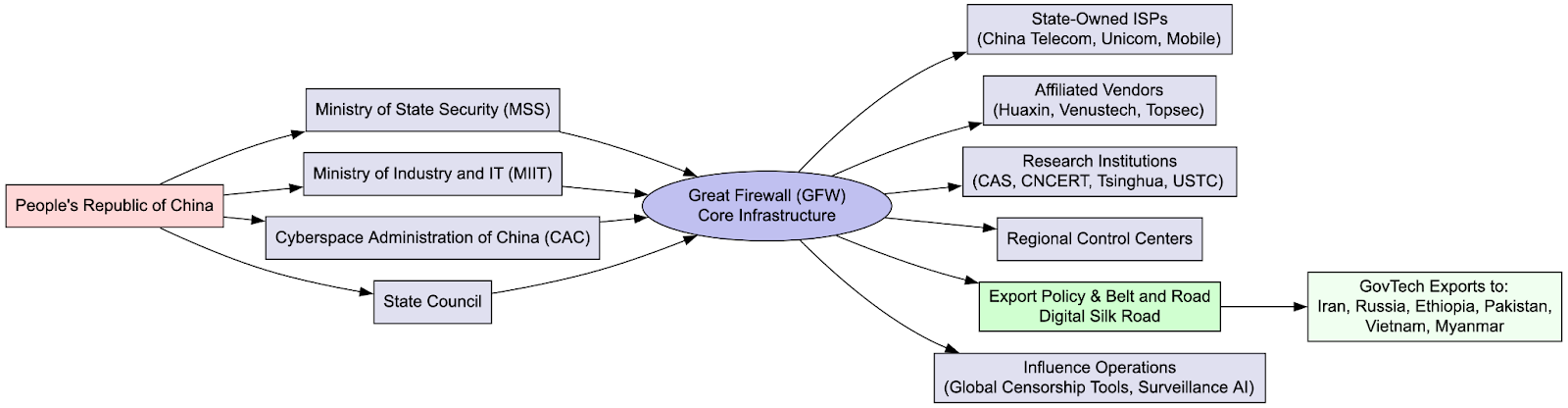
The Great Firewall functions as an integrated governance platform that enforces ideological conformity, facilitates market protection for domestic tech firms, and enables real-time surveillance and adaptive censorship across China’s internet infrastructure. Its design and export through firms like Huawei and initiatives such as the Digital Silk Road are driving a splintering of the global internet and the spread of “internet sovereignty” models to other authoritarian states. #GreatFirewall #Huawei

Researchers observed AI-integrated malware families that query large language models at runtime to generate code, obfuscate payloads, and adapt behavior, with notable families including PROMPTFLUX, PROMPTSTEAL, PROMPTLOCK, FRUITSHELL, and QUIETVAULT. These tools were used for persistence, reconnaissance, data exfiltration, and cross-platform encryption, with APT28 (LAMEHUG) deploying PROMPTSTEAL against Ukrainian targets. #PROMPTFLUX #PROMPTSTEAL
eSentire’s TRU discovered campaigns using ClickFix for initial access to deploy Amatera Stealer (a rebranded ACR/AcridRain) and NetSupport RAT, with Amatera leveraging advanced evasion (WoW64 syscalls, AMSI bypass) and extensive crypto-wallet/password manager theft capabilities. eSentire published decryption helpers and detection guidance, and recommends mitigations including disabling mshta.exe, removing the Run prompt, PSAT, and partnering with 24/7 MDR services. #Amatera #NetSupport

Ransomware attacks surged to 623 incidents in October 2025, the second-highest monthly total on record, driven by groups such as Qilin, Akira, Sinobi, Medusa, Cl0p, Warlock, BlackSuit, The Gentlemen, and others. Key exploited vulnerabilities and tactics included CVE-2025-61882 (Oracle E-Business Suite), CVE-2025-10035 (GoAnywhere), deserialization RCEs, abuse of legitimate remote management tools, and supply-chain targeting. #Qilin #Sinobi
