Trustwave SpiderLabs discovered Eternidade Stealer, a Delphi‑compiled banking trojan distributed via a WhatsApp‑propagating worm and social engineering that steals contacts and delivers an MSI dropper which deploys credential‑stealing components. The campaign uses IMAP‑based dynamic C2 retrieval, localized Brazilian targeting, encrypted C2 commands, and overlay/keylogging capabilities. #Eternidade #Casbaneiro
Category: Threat Research
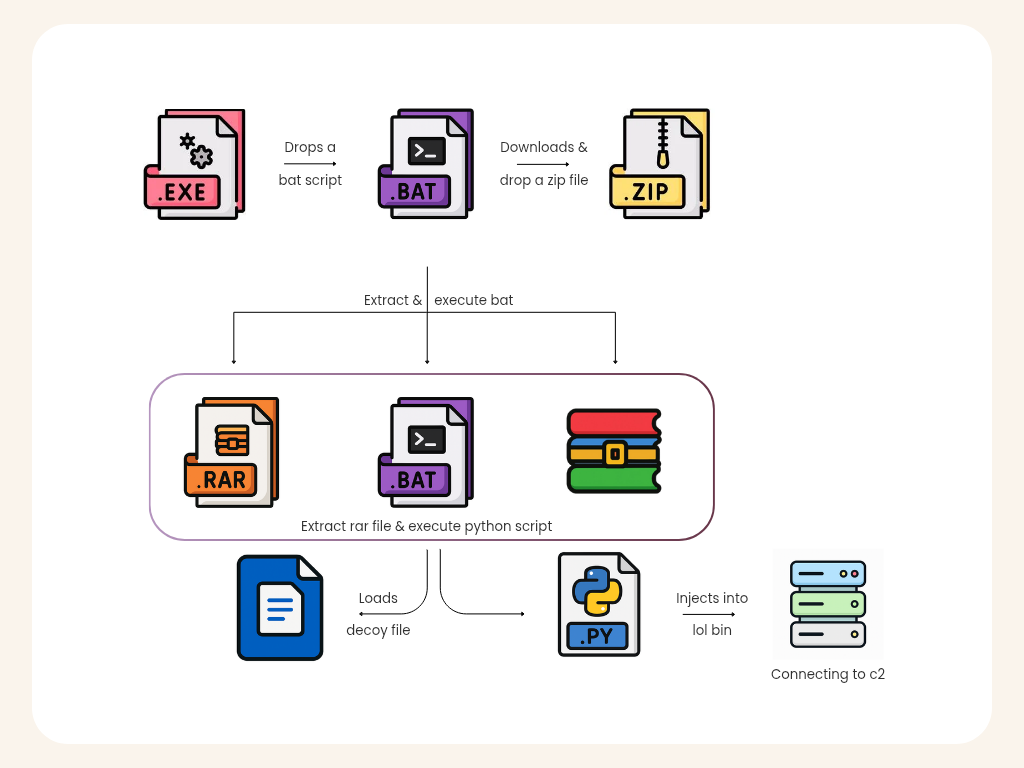
K7 Labs analyzed a Python-based multi-stage obfuscated malware that unpacks a large filler blob to reveal a small marshalled .pyc which performs process injection into cvtres.exe and loads a downloaded .NET component for persistent C2. The infection uses disguised archives and bundled Python runtime (ntoskrnl.exe) to reconstruct and execute payloads from cloud-hosted files and maintain an encrypted RAT-like channel. #cvtres.exe #ntoskrnl.exe
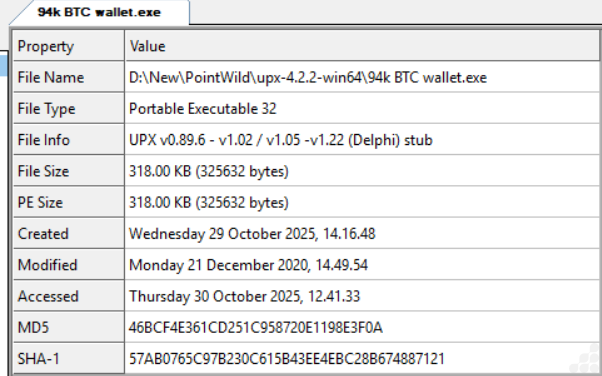
A Bitcoin-themed sample of the DarkComet RAT was distributed inside a RAR archive and, once executed, unpacks to a UPX-packed executable that installs persistence, keylogs, and attempts to beacon to a hardcoded C2 at kvejo991.ddns.net:1604. File hashes, install path, mutex, and captured keystroke logs were recovered during analysis. #DarkComet #kvejo991.ddns.net
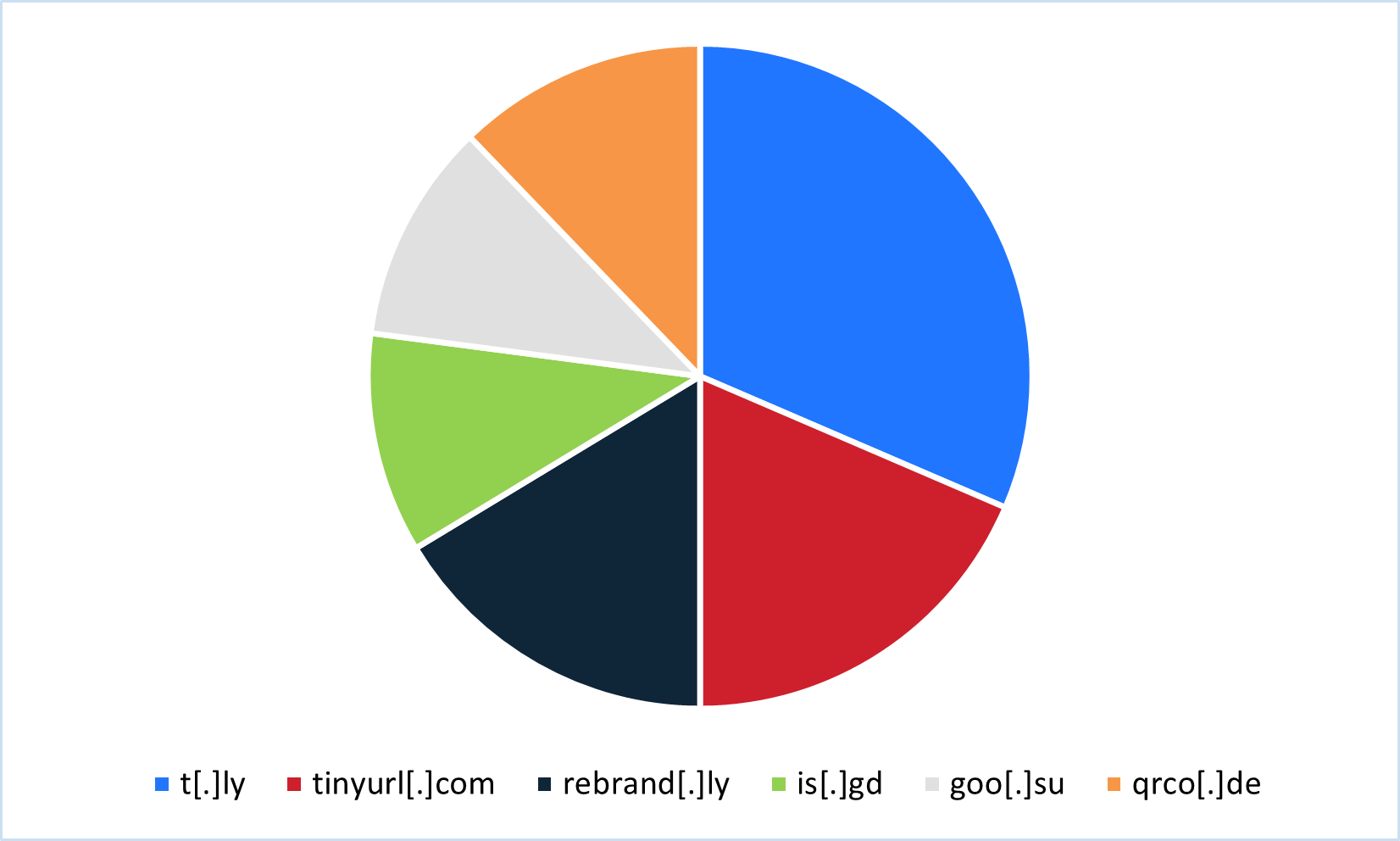
Threat actors abused legitimate URL shortening services between July 2024 and June 2025 to deliver credential phishing and malware, leveraging free tiers, trial accounts, analytics, QR codes, and APIs to scale campaigns and evade analysis. The most commonly abused services included t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd, goo[.]su, and qrco[.]de, with specific malware families observed such as Pure Logs Stealer, Lone None Stealer, Mispadu, Byakugan, and ConnectWise RAT. #PureLogs #LoneNone #Mispadu #Byakugan #ConnectWiseRAT #t.ly #tinyurl.com #rebrand.ly #is.gd #goo.su #qrco.de
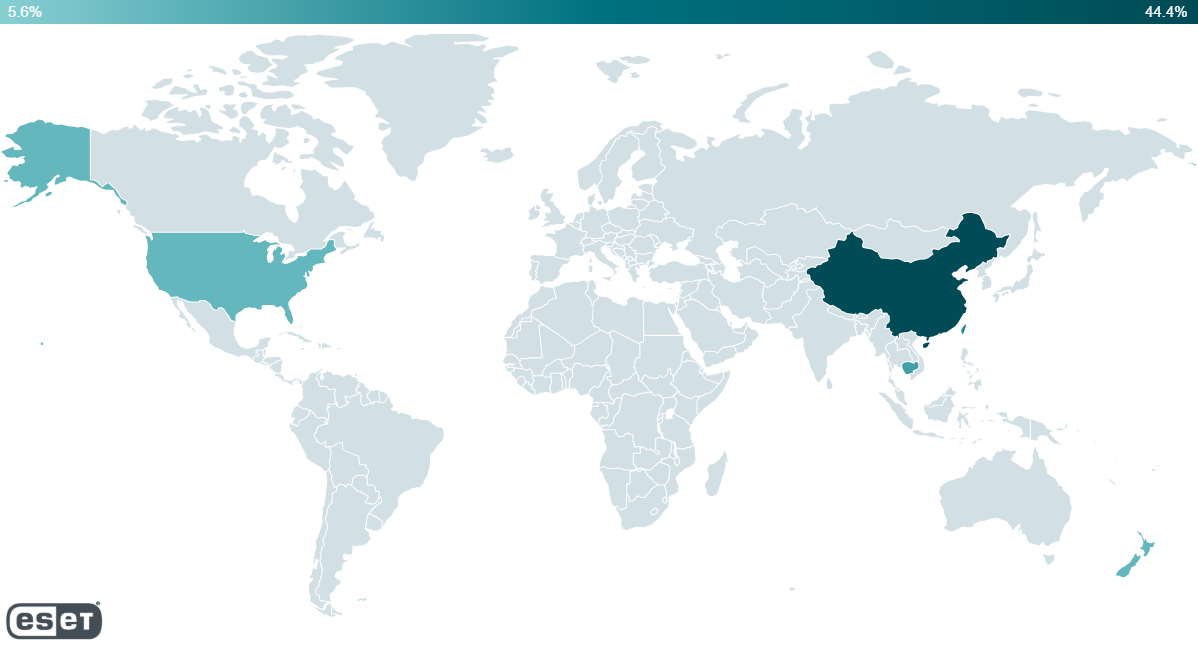
ESET analyzed PlushDaemon’s use of a MIPS32 network implant named EdgeStepper that forwards DNS queries to attacker-controlled nodes to hijack legitimate software updates and deliver downloaders that deploy the SlowStepper backdoor. The report also details LittleDaemon and DaemonicLogistics — two Windows downloaders used in the update-hijacking chain — and provides IoCs including files, domains, and IPs. #EdgeStepper #SlowStepper
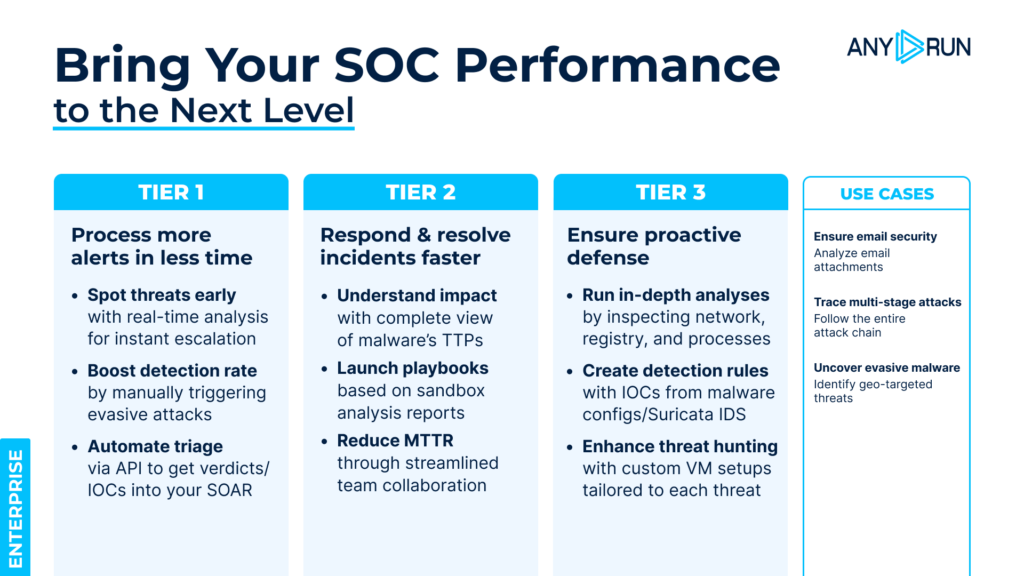
LOLBin attacks abuse legitimate Windows system binaries (rundll32, certutil, mshta, etc.) to load disguised modules, decode hidden payloads, or spawn in-memory execution so malicious activity appears normal. ANY.RUN’s interactive sandbox reveals process behavior, parent–child chains, command lines, and in-memory actions to expose these abuses quickly and provide actionable IOCs. #RUNDLL32 #CERTUTIL…
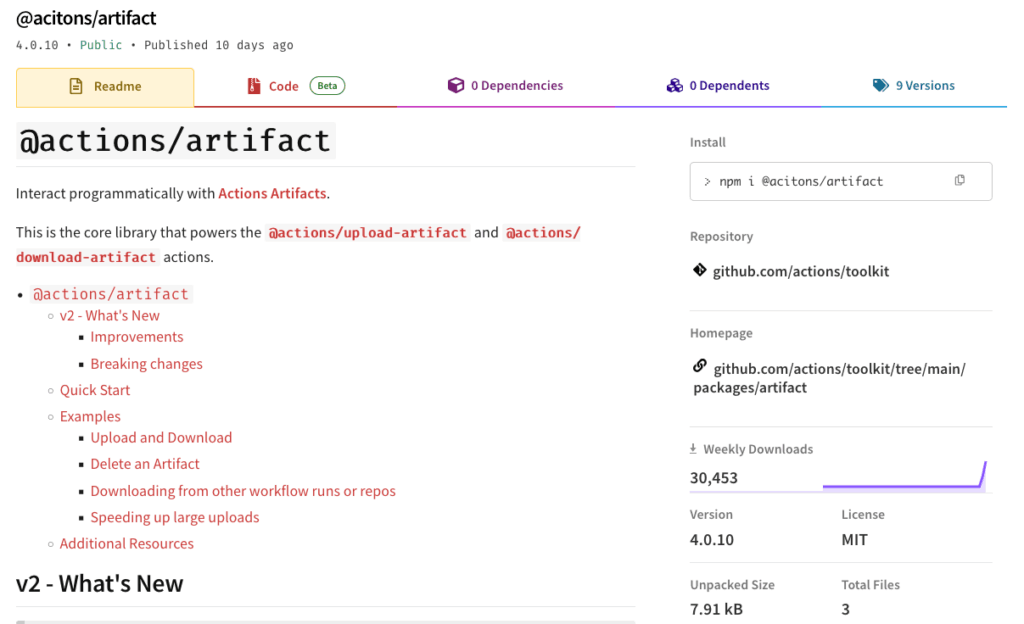
Veracode Threat Research discovered a malicious typosquatting npm package “@acitons/artifact” (masquerading as “@actions/artifact”) that included post-install hooks to download and run an obfuscated binary and node payload aimed at exfiltrating GitHub Actions environment tokens and publishing malicious artifacts. The campaign included multiple malicious versions and a companion package “8jfiesaf83”, used targeted checks for GitHub organization repositories, and exfiltrated encrypted data to attacker-controlled endpoints. #@acitons/artifact #8jfiesaf83

Cybercrime has evolved into a subscription-based economy where services like phishing, OTP bots, infostealer data feeds, initial access, and advanced malware are rented on pay-as-you-go models, lowering the barrier to entry for low-skill attackers. Notable named services and tools in the article include SpamGPT, MatrixPDF, Atroposia, and Telegram-based OTP bots. #SpamGPT…

Sarcoma is a fast-emerging ransomware group (late 2024) that combines data theft with encryption and aggressive double-extortion tactics, targeting mid-market and larger organizations—especially in manufacturing, technology and construction—primarily in the United States, Italy and Canada. The group operates a controlled RaaS-style model, targets Windows, Linux and ESXi environments, and uses techniques including credential theft, zero-day exploits, anti-recovery steps and public leak pressure. #Sarcoma #ChaCha20

Sandworm (also tracked as APT44, Seashell Blizzard, and Voodoo Bear) conducted intrusions against Ukrainian organizations using exploited web services and a custom webshell called LocalOlive, then relied on living-off-the-land techniques to conduct reconnaissance, persistence, and credential theft. The campaign and associated emulation highlight specific TTPs—including LSASS dumping, scheduled task persistence, and…

UNC1549 targeted aerospace, aviation, and defense sectors using spear-phishing and compromised third‑party relationships to gain access, then deployed custom backdoors (TWOSTROKE, DEEPROOT, LIGHTRAIL, GHOSTLINE, POLLBLEND, MINIBIKE) and tunneling tools to maintain stealthy persistence and C2 using Azure and SSH reverse tunnels. The group used credential theft (DCSYNCER.SLICK, CRASHPAD, TRUSTTRAP), DLL search order hijacking, and long-lived stealth techniques to exfiltrate sensitive data and pivot through suppliers. #UNC1549 #TWOSTROKE
The intrusion began with valid Remote Desktop Protocol (RDP) logons using compromised credentials and progressed through rapid lateral movement, domain account creation, discovery with SoftPerfect NetScan and NetExec, data collection and exfiltration to temp.sh, and culminated in deletion of backups and deployment of Lynx ransomware across backup and file servers. The activity used paid/licensed tooling and bulletproof-hosted infrastructure (Railnet/Virtualine) with a Time to Ransomware of ~178 hours. #Lynx #temp.sh
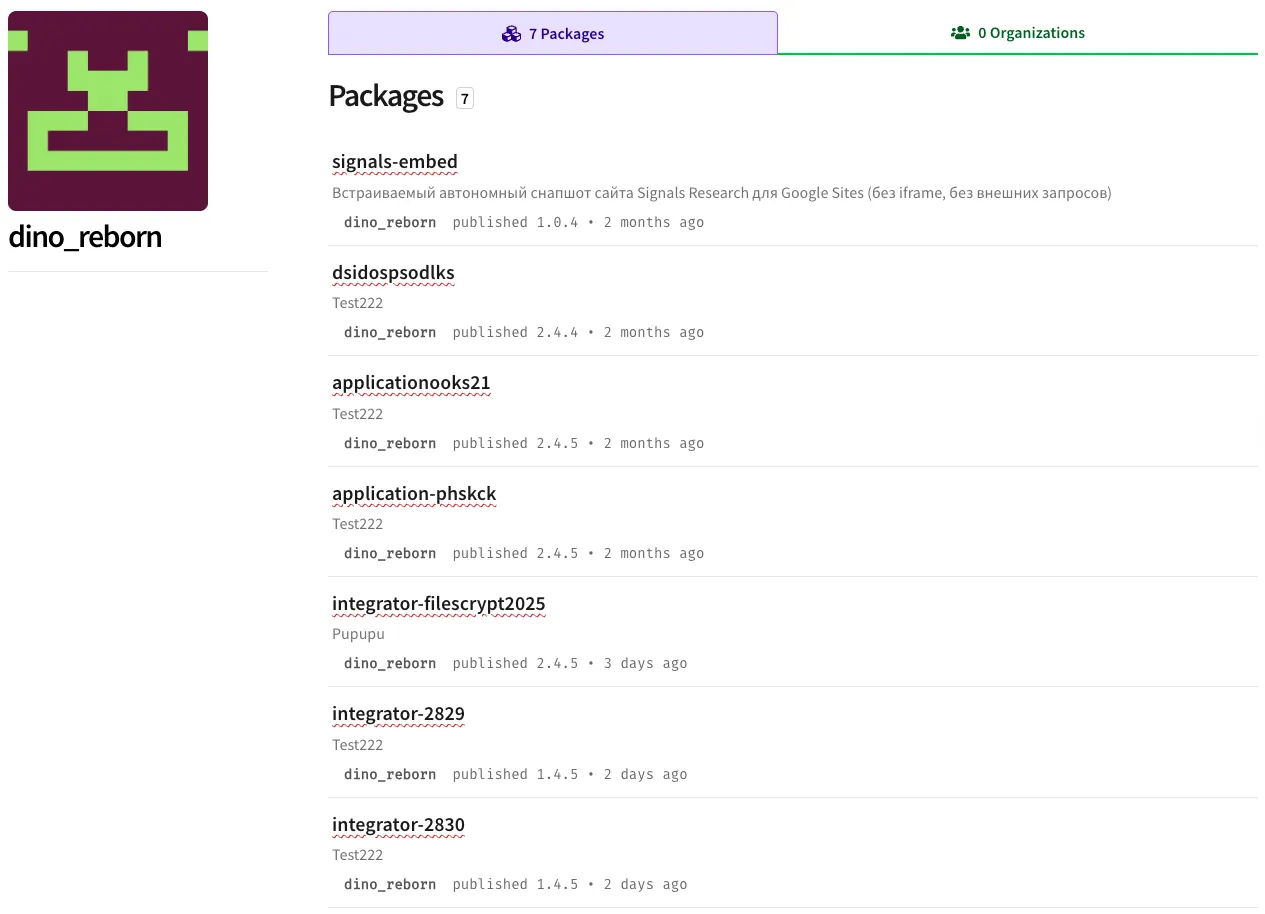
Researchers discovered dino_reborn, an npm threat actor publishing seven packages that implement a cloaked malware campaign using Adspect to fingerprint visitors and selectively serve a fake CAPTCHA that redirects victims to malicious sites. The campaign links six malware-containing packages and one webpage package, reuses configuration strings and proxy endpoints, and aims to steal crypto by masquerading as decentralized-exchange verification pages. #dino_reborn #Adspect
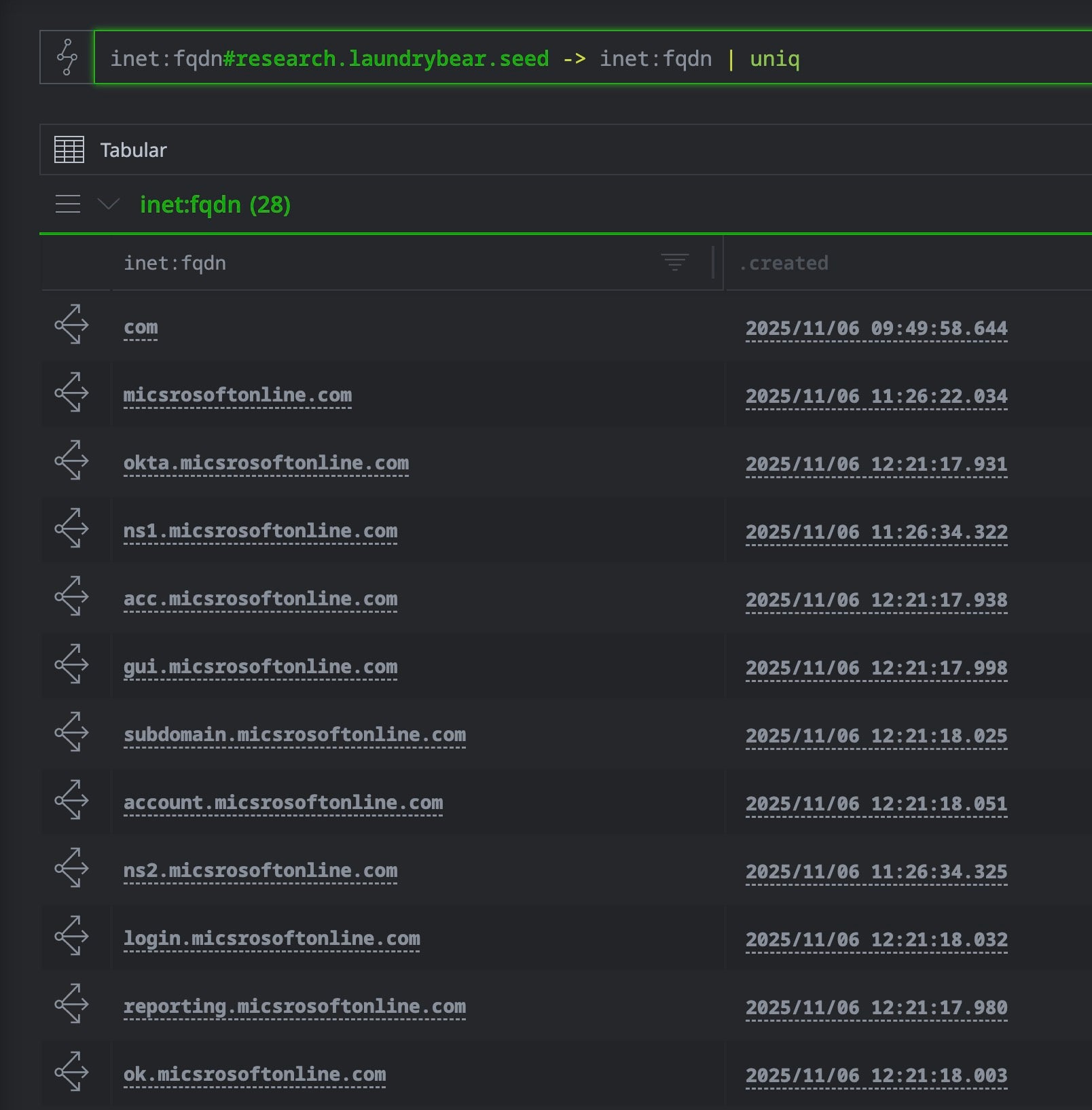
SentinelLABS released the open-source sentinelone-validin Synapse power-up to combine Validin DNS, HTTP crawler, TLS certificate, and WHOIS data for time-aware, cross-source infrastructure analysis. Case studies on LaundryBear (Void Blizzard) and FreeDrain show how HTTP body/favicons/certificate pivots and WHOIS enrichment expand small indicator sets into broad campaign infrastructure. #LaundryBear #FreeDrain

AhnLab ASEC’s October 2025 analysis found Infostealer distribution heavily using SEO-poisoned crack/keygen posts and an increasing use of DLL SideLoading and a new loader DLL type that fetches configs from C2s like evgshippingline[.]com. The most common Infostealers were Rhadamanthys, ACRStealer, and LummaC2, with LummaC2’s volume fluctuating and specific C2 paths (/nfront.php,…
