SentinelLABS released the open-source sentinelone-validin Synapse power-up to combine Validin DNS, HTTP crawler, TLS certificate, and WHOIS data for time-aware, cross-source infrastructure analysis. Case studies on LaundryBear (Void Blizzard) and FreeDrain show how HTTP body/favicons/certificate pivots and WHOIS enrichment expand small indicator sets into broad campaign infrastructure. #LaundryBear #FreeDrain
Keypoints
- The sentinelone-validin power-up provides unified enrichment across DNS history, HTTP crawls, TLS certificates, and WHOIS in one command (s1.validin.enrich), enabling rapid multi-source reconnaissance.
- HTTP crawler fingerprints (body SHA1, favicon MD5, banner/header/class hashes, certificate fingerprints) serve as effective pivots to discover related infrastructure despite domain rotation and short-lived assets.
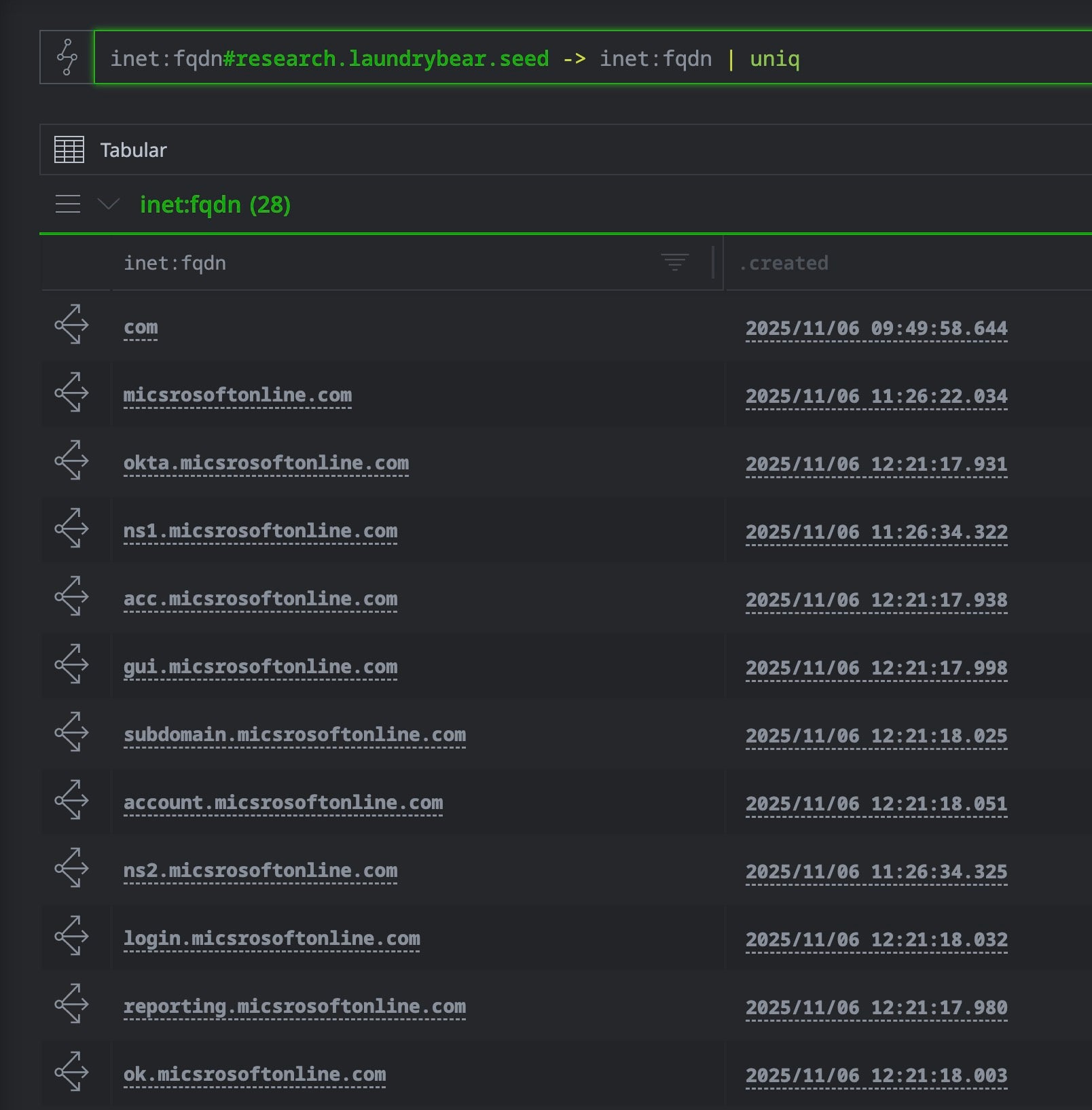
- In the LaundryBear case, body-hash pivoting expanded three published domains into 55 domains and 21 IPs, revealing synchronized provisioning and hosting patterns.
- Dry-run pivot statistics (–dry-run) let analysts assess pivot scope (counts) before committing to expensive graph ingestion, helping filter out CDN/benign noise and isolated assets.
- WHOIS enrichment exposed bulk registrar usage in the FreeDrain campaign, linking redirect domains to known CNO facilitators and enabling high-confidence attribution signals.
- Hash-based pivoting allows selective enrichment by querying hashes (favicon/body/cert) via Validin’s API before materializing nodes in Synapse, reducing ingest costs.
- The power-up includes download and parse capabilities (s1.validin.download + fileparser.parse) to create file:bytes nodes and extract embedded IOCs from response bodies and certificates.
MITRE Techniques
- [T1598] Gather Victim Network Information – Used by querying DNS records and passive DNS history to map network infrastructure and reveal shared nameservers and registration timing (“…enables analysts to quickly search, pivot through, and investigate network infrastructure for time-aware, cross-source analysis”).
- [T1583] Acquire Infrastructure – Observed via bulk domain registrations and registrar relationships for FreeDrain (“…domains registered on the same day can indicate batch infrastructure provisioning” and use of a registrar tagged #cno.infra.dns.bulk).
- [T1595] Active Scanning – Mitigated/avoided by leveraging Validin’s passive crawler data (Crawlr) rather than performing active scans: “…provides access to pre-existing crawl observations, allowing instant analysis without active scanning.”).
- [T1204] User Execution via Malicious Link – Phishing infrastructure and redirectors funnel victims from legitimate hosting to attacker-controlled pages (“…redirect domains used by FreeDrain operators to funnel victims from legitimate hosting platforms to attacker-controlled phishing infrastructure”).
- [T1078] Valid Accounts (Credential Harvesting support) – Credential phishing infrastructure (typosquats and Microsoft/corporate service impersonation) used to harvest credentials (“Most are Microsoft/corporate service typosquats used for credential phishing”).
- [T1608] Stage Capabilities – Templated infrastructure (favicons, body content, redirects) and reuse across thousands of lure pages indicate staging and automated provisioning of phishing pages (“…templated infrastructure with reused favicons, redirector domains, and phishing pages hosted on Azure and AWS S3”).
Indicators of Compromise
- [Domain ] phishing and redirect domains tied to campaigns – example tags shown as #research.laundrybear.seed, #research.freedrain.href (used as seed/tagged domain context).
- [Hash ] HTTP/body and favicon fingerprints used as pivots – body SHA1 example: 38c47d338a9c5ab7ccef7413edb7b2112bdfc56f; favicon MD5 examples referenced as pivotable values (and other MD5/sha1 hashes).
- [IP Address ] shared hosting infrastructure revealed by pivots – example: “22 IP address shared by multiple domains” (context: LaundryBear hosting cluster), and mentions of multiple IPs linked to hashes (and other IPs).
- [WHOIS/Registrar ] registrar names and registration dates used to link bulk-registered domains – context: registrar tagged #cno.infra.dns.bulk and registrar filter examples (registrar name redacted as ).
- [Certificate Fingerprint ] TLS certificate fingerprints used to pivot SAN relationships – examples: certificate fingerprint and certificate fingerprint SHA256 referenced as pivotable fields (and additional certificate entries in CT logs).