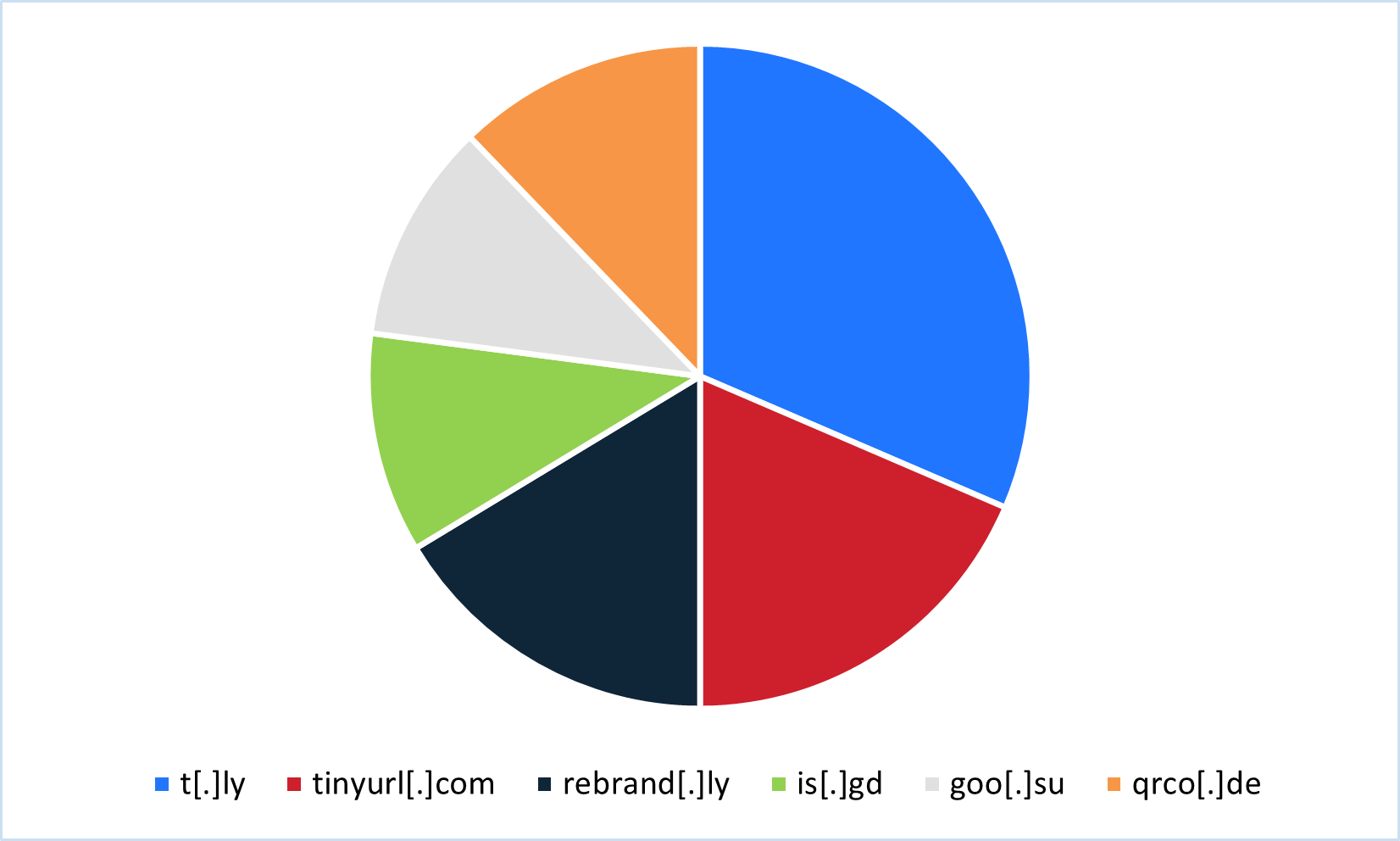
Threat actors abused legitimate URL shortening services between July 2024 and June 2025 to deliver credential phishing and malware, leveraging free tiers, trial accounts, analytics, QR codes, and APIs to scale campaigns and evade analysis. The most commonly abused services included t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd, goo[.]su, and qrco[.]de, with specific malware families observed such as Pure Logs Stealer, Lone None Stealer, Mispadu, Byakugan, and ConnectWise RAT. #PureLogs #LoneNone #Mispadu #Byakugan #ConnectWiseRAT #t.ly #tinyurl.com #rebrand.ly #is.gd #goo.su #qrco.de
Keypoints
- Between July 2024 and June 2025, shortened URLs were widely used in phishing and malware campaigns; 28% of campaigns using common link shorteners delivered malware.
- The top six shortened URL services observed were t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd, goo[.]su, and qrco[.]de (Table/Figure references in source).
- Threat actors exploited free tiers, free trials, and APIs to create accounts and generate shortened links at scale, often automating link creation for campaigns.
- Analytics provided by shortener services (click counts, browser, language, geolocation, time) enabled threat actors to validate active inboxes and tailor follow-up spear-phishing.
- QR code generation, link expiration, traffic routing/smart URLs, and password protection were abused to hinder analysis and evade security controls.
- Different shorteners had different primary uses: is[.]gd and goo[.]su were skewed toward malware delivery (notably Pure Logs Stealer and Lone None), while rebrand[.]ly, t[.]ly, tinyurl[.]com, and qrco[.]de were more associated with credential phishing.
- Mitigations include employee training, blocking less-popular shorteners, multi-hop link analysis, expanded-link previews (e.g., t[.]ly “+”, is[.]gd “-”, TinyURL preview toggle), and showing final destinations on hover.
MITRE Techniques
- [T1071] Application Layer Protocol – Shortened-URL services and their APIs were used to deliver phishing and malware via web-based links (‘…shortened URL services…deliver malware and credential phishing…’).
- [T1204] User Execution – QR codes and shortened links were used to induce users to click or scan, enabling credential theft and malware delivery (‘…QR codes have been a popular choice for threat actors…victim clicks the link’).
- [T1588] Obtain Capabilities – Threat actors leveraged free trials and free account creation to obtain services (APIs, analytics, QR generation) for campaign use (‘…free or offer a free trial, allowing threat actors to easily create new accounts for new campaigns’).
- [T1583] Acquire Infrastructure – Use of legitimate shortening platforms (t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd, goo[.]su, qrco[.]de) as infrastructure to host redirects and analytics (‘…the most commonly abused legitimate URL shortening services…’).
- [T1499] Endpoint Denial of Service (Evasion/Anti-analysis via link expiration) – Link expiration and password-protected shortener pages were used to limit analysis time/access (‘…setting link expiration…Password protection also aids threat actors in bypassing analysis’).
- [T1020] Automated Collection (Discovery via analytics) – Shortener-provided analytics (click counts, browser, location, language) were used to collect user/target data to inform follow-up targeting (‘…offers some sort of information regarding the recipient…browser type, language, or date’).
- [T1090] Proxy/Redirection – Smart URLs and traffic routing redirected victims based on user agent/geolocation to avoid analysis or deliver tailored payloads (‘…Smart URLs (traffic routing)…redirect victims to different redirect URLs based on the browser user agent and geolocation’).
Indicators of Compromise
- [Domain ] Shortened URL domains abused as redirect infrastructure – t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd, goo[.]su, qrco[.]de
- [Malware family ] Malware frequently delivered via shortened links – Pure Logs Stealer, Lone None Stealer (often via goo[.]su/is[.]gd), Mispadu (tinyurl[.]com), Byakugan (rebrand[.]ly), ConnectWise RAT (t[.]ly/qrco[.]de), and Remcos/Lumma Stealer (tinyurl[.]com)
- [Technique ] Features abused for evasion and reconnaissance – QR code generation (qrco[.]de, goo[.]su), link expiration and password-protected short links (rebrand[.]ly, tinyurl[.]com), and API-based automated link creation (t[.]ly, tinyurl[.]com, rebrand[.]ly, is[.]gd)
- [Analytics data types ] Click metadata used for targeting – examples: device language, location, browser, time of click (provided by many shorteners to validate targets)
Read more: https://cofense.com/blog/the-6-url-shorteners-you-didn-t-know-were-helping-hackers