Researchers discovered dino_reborn, an npm threat actor publishing seven packages that implement a cloaked malware campaign using Adspect to fingerprint visitors and selectively serve a fake CAPTCHA that redirects victims to malicious sites. The campaign links six malware-containing packages and one webpage package, reuses configuration strings and proxy endpoints, and aims to steal crypto by masquerading as decentralized-exchange verification pages. #dino_reborn #Adspect
Keypoints
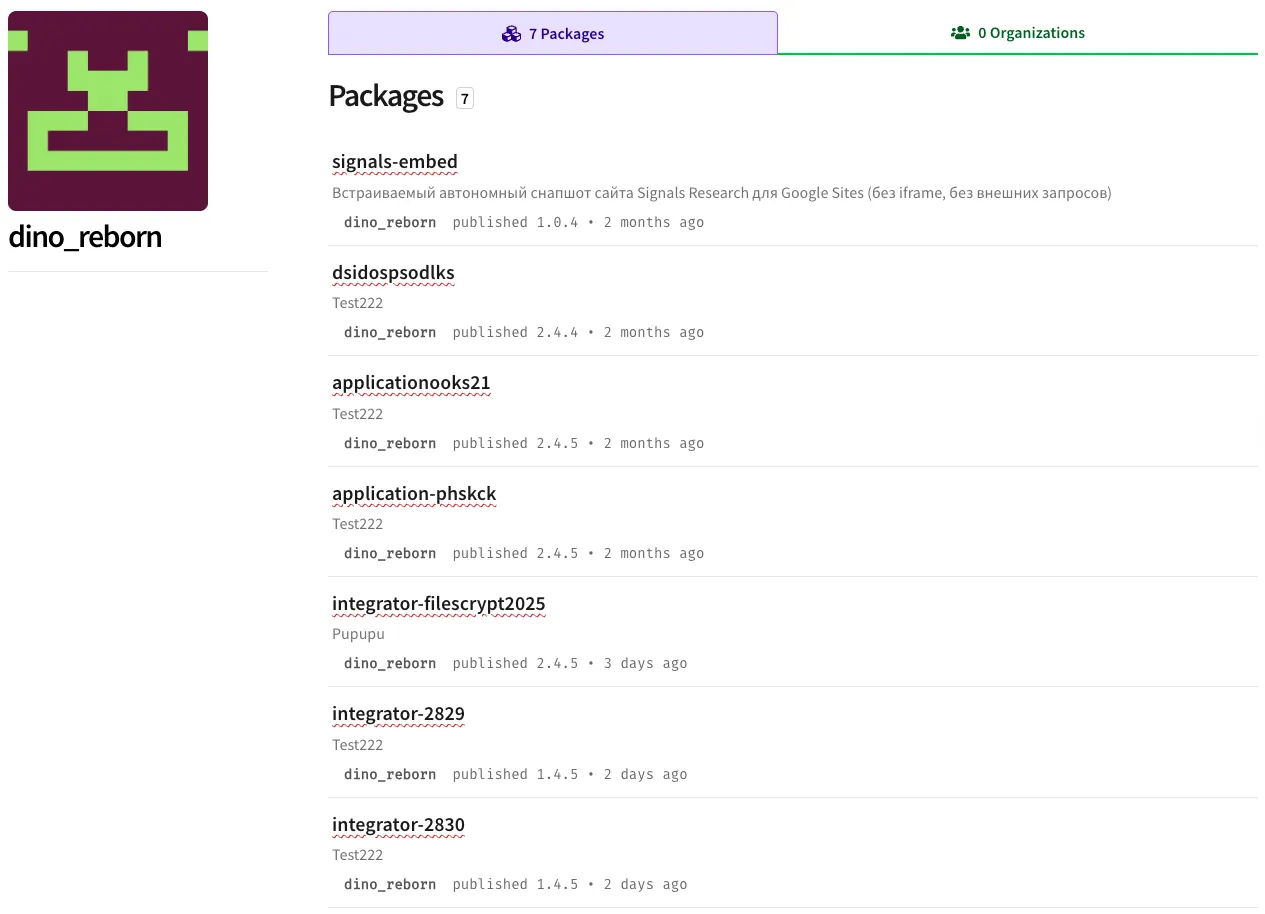
- dino_reborn published seven live npm packages (signals-embed, dsidospsodlks, applicationooks21, application-phskck, integrator-filescrypt2025, integrator-2829, integrator-2830) that were placed into npm security holding after takedown requests.
- Six packages contain a ~39 KB malware payload that fingerprints visitors, uses anti-analysis controls, and calls an Adspect cloaking API via threat-actor-controlled proxy endpoints.
- One package (signals-embed) hosts a 51 KB static webpage used as the “white page” shown to researchers, sharing container IDs so the malware and webpage interoperate.
- The malware reconstructs PHP-style server context in JavaScript to send high-fidelity fingerprints (including user agent, host, referrer, locale, and timing) to the Adspect API through proxies, allowing server-side gating of victims vs. researchers.
- If Adspect classifies a visitor as a victim, the site shows a fake CAPTCHA that, after a short delay, opens a malicious redirect URL supplied by the Adspect response; researchers are shown a benign white page.
- Configuration similarities (ADSPECT_STREAM_ID, PROXY_URL, ADSPECT file endpoints, TARGET_CONTAINER) across packages enable tracking of actor behavior and rapid rotation of final payloads without republishing packages.
- Defensive recommendations include monitoring for /adspect-proxy.php and /adspect-file.php paths, treating scripts that disable user interactions or post detailed client fingerprints to unknown PHP endpoints as red flags, and using supply-chain tooling to block such packages.
MITRE Techniques
- [T1195.002 ] Supply Chain Compromise – Threat actor published malicious npm packages to distribute cloaking and redirect logic (“dino_reborn … with seven packages constructing an intricate malware campaign.”).
- [T1583.001 ] Acquire Infrastructure: Domains – Actor registered and used multiple domains for proxies and payload hosting (“association-google[.]xyz”, “appprotector[.]online”, “protectorapp[.]online”).
- [T1583.006 ] Acquire Infrastructure: Web Services – Actor used Adspect cloaking service to gate traffic (“Adpsect is a cloaking service to ensure only legitimate visitors see a real website.”).
- [T1082 ] System Information Discovery – Malware collects device and browser fields such as navigator.userAgent and navigator.language (“HTTP_USER_AGENT: navigator.userAgent … HTTP_ACCEPT_LANGUAGE: navigator.language”).
- [T1592 ] Gather Victim Host Information – Code gathers host information including HTTP_HOST, SERVER_NAME, and REQUEST_URI (“HTTP_HOST: window.location.host, SERVER_NAME: window.location.hostname, REQUEST_URI: window.location.pathname + window.location.search”).
- [T1590 ] Gather Victim Network Information – Malware obtains network-relevant fields like SERVER_PORT and HTTPS to fingerprint connections (“SERVER_PORT: window.location.port … HTTPS: window.location.protocol === ‘https:’ ? ‘on’ : ‘off’”).
- [T1204 ] User Execution – The attack relies on user interaction with a fake CAPTCHA to trigger the redirect (“showCaptchaWithRedirect … Verify you are human by completing the action below.”).
- [T1189 ] Drive-by Compromise – Malicious code is delivered via npm packages and executes automatically in the browser without explicit compilation by the victim (“code automatically executes because it’s wrapped in IIFE (Immediately Invoked Function Expression)”).
- [T1071.001 ] Application Layer Protocol: Web Protocols – The malware uses HTTP(S) endpoints to send fingerprint data and receive Adspect responses (“PROXY_URL: ‘https://association-google[.]xyz/adspect-proxy[.]php’”).
- [T1090 ] Proxy – Actor routes Adspect API traffic through actor-controlled proxy endpoints to hide structure and obtain real IPs (“these data points … are then sent to the Adspect API through the threat actor’s proxy endpoint”).
- [T1036 ] Masquerading – The campaign uses fake branded webpages and CAPTCHA UI (standx.com, jup.ag, uniswap) to appear legitimate (“The URL standx[.]com is displayed in the fake CAPTCHA … jup.ag in the CAPTCHA interface”).
- [T1622 ] Debugger Evasion – JavaScript disables right-click, F12, Ctrl+U, and detects devtools to hinder analysis (“Disable right-click … If window.devtools && window.devtools.open { window.location.reload(); }”).
- [T1059.007 ] Command and Scripting Interpreter: JavaScript – The attack uses JavaScript embedded in npm packages to perform fingerprinting, cloaking calls, and redirection (“Malware reconstructs PHP-style request context in JavaScript and pushes it through a proxy”).
Indicators of Compromise
- [Email ] Threat actor registration – geneboo@proton[.]me
- [Domains ] Proxy and file endpoints used by the actor – association-google[.]xyz (adspect-proxy[.]php), appprotector[.]online (adspect-proxy[.]php / adspect-file[.]php)
- [Domains ] Additional proxy/file endpoints and hosting – protectorapp[.]online (adspect-proxy[.]php, adspect-file[.]php), fanqut[.]eu[.]com/about[.]html (fake Offlido page)
- [Package Names ] Malicious npm packages – integrator-2829, integrator-2830, integrator-filescrypt2025, dsidospsodlks, applicationooks21, application-phskck, signals-embed
- [Configuration IDs ] ADSPECT stream IDs used to track package performance – 81330cb9-f454-414c-a166-9841238cb086, fbaf1202-e5ff-4b06-9c94-9692d823b8cd, f942b777-086e-4b8c-a9f3-ad2b233e98f5
Read more: https://socket.dev/blog/npm-malware-campaign-uses-adspect-cloaking-to-deliver-malicious-redirects