Oracle E-Business Suite (EBS) versions 12.2.3–12.2.14 are vulnerable to a complex pre-authentication exploit chain (CVE-2025-61882) that combines SSRF, CRLF header injection, connection reuse, path traversal, and XSLT-based remote stylesheet execution to achieve remote code execution. The chain was analyzed from a public PoC and demonstrates attacker-controlled HTTP requests that fetch and…
Category: Threat Research

Google Threat Intelligence Group (GTIG) details a three-year espionage campaign by PRC‑nexus actor APT24 that deploys a highly obfuscated first‑stage downloader called BADAUDIO to establish persistent access via strategic web compromises, supply‑chain abuse of a Taiwanese digital marketing firm, and targeted phishing. The report analyzes BADAUDIO’s control‑flow flattening, DLL sideloading, AES‑encrypted payload delivery (including Cobalt Strike Beacon instances), advanced browser fingerprinting for tailored targeting, and shares IOCs and YARA rules to aid detection and mitigation. #APT24 #BADAUDIO
Morphisec discovered a sustained campaign that weaponizes Blender .blend files hosted on 3D asset sites to run embedded Python scripts which chain into PowerShell stages and download StealC V2 components. The operation uses decoy documents, Pyramid C2 with ChaCha20-encrypted payloads, and persistence via hidden LNK files, linking the campaign to previously observed Russian-speaking activity. #StealC #Blender
The leaked October 2025 APT35 corpus documents a quota-driven, bureaucratic IRGC cyber-intelligence apparatus that weaponized Exchange (ProxyShell, Autodiscover, EWS) and Ivanti vulnerabilities, ran HERV-style phishing seeded from harvested Global Address Lists, and maintained persistent mailbox monitoring backed by centralized KPI reporting and on-premises operator attendance logs. #APT35 #ProxyShell
Splunk Threat Research Team analyzed a new .NET steganographic loader variant that decrypts and loads a container module at runtime to hide two image-embedded stagers, one of which yielded a Lokibot payload. The report details the loader’s steganography, extraction attempts with PixDig, Lokibot capabilities (credential theft, injection, scheduled task persistence, downloading additional payloads) and mapped MITRE techniques to support detection development. #Lokibot #QuasarRAT
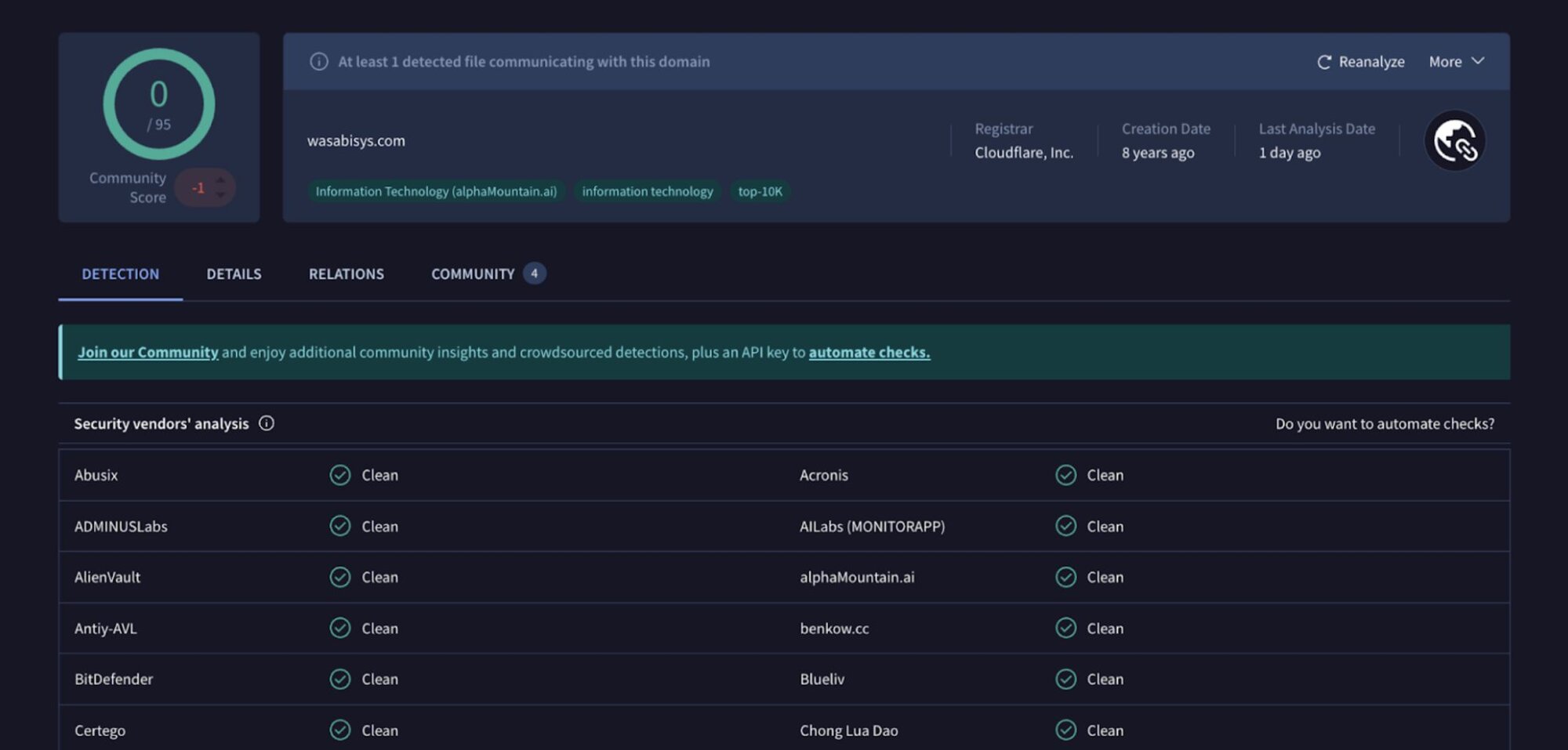
Huntress observed threat actors exploit a recently patched WSUS RCE vulnerability (CVE-2025-59287) to gain initial access and then install Velociraptor to establish command-and-control on the endpoint. The actors retrieved a malicious MSI from s3.wasabisys[.]com and configured Velociraptor to communicate with update[.]githubtestbak[.]workers[.]dev. #CVE-2025-59287 #Velociraptor
Tycoon 2FA is a rapidly evolving Phishing-as-a-Service platform that leverages real-time Adversary-in-the-Middle techniques to capture credentials, session tokens, and bypass many legacy MFA methods via high-fidelity phishing pages for Microsoft 365, Gmail, and Outlook. CYFIRMA observed rapid infrastructure expansion, extensive domain rotation, advanced obfuscation (Base64, AES/RC4, dynamic JS), and Telegram-based distribution making it widely accessible to varied threat actors. #Tycoon2FA #ifelse.rlcozx.es

NotDoor is an Outlook VBA macro backdoor tied to APT28 that uses OneDrive DLL sideloading, encoded PowerShell, and registry modifications to persist, monitor incoming emails for C2 triggers, exfiltrate data, and execute commands. The Splunk Threat Research Team provides detection guidance and Splunk analytic content for identifying indicators like SSPICLI.dll and VbaProject.OTM manipulation. #NotDoor #APT28

Sophos analysts uncovered a multi-stage WhatsApp-focused campaign (STAC3150) delivering archive attachments that deploy downloaders which fetch scripts to harvest WhatsApp session data and, in later stages, an MSI installer that installs the Astaroth (Guildma) banking trojan. The campaign used View Once messages, PowerShell and Python loaders, Selenium with WPPConnect to hijack WhatsApp Web, and actor-controlled domains such as varegjopeaks[.]com and manoelimoveiscaioba[.]com. #Astaroth #STAC3150
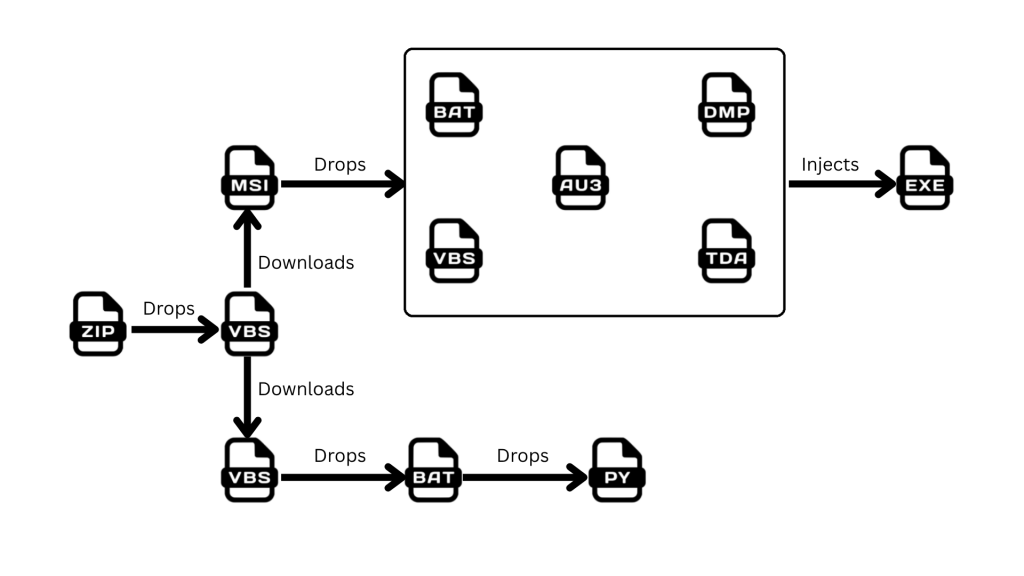
K7 Labs uncovered a Water-Saci campaign targeting Brazil that spreads a banking trojan and SorvePotel-related components by abusing WhatsApp Web via a Python/Selenium-based automation script and in-memory payload delivery. The attack chain begins with a phishing ZIP containing an obfuscated VBS that downloads an MSI and VBS to install Python, ChromeDriver, and a whats.py script that harvests contacts, sends in-memory payloads through WhatsApp Web, and reports results to PHP C2s. #SorvePotel #Water-Saci
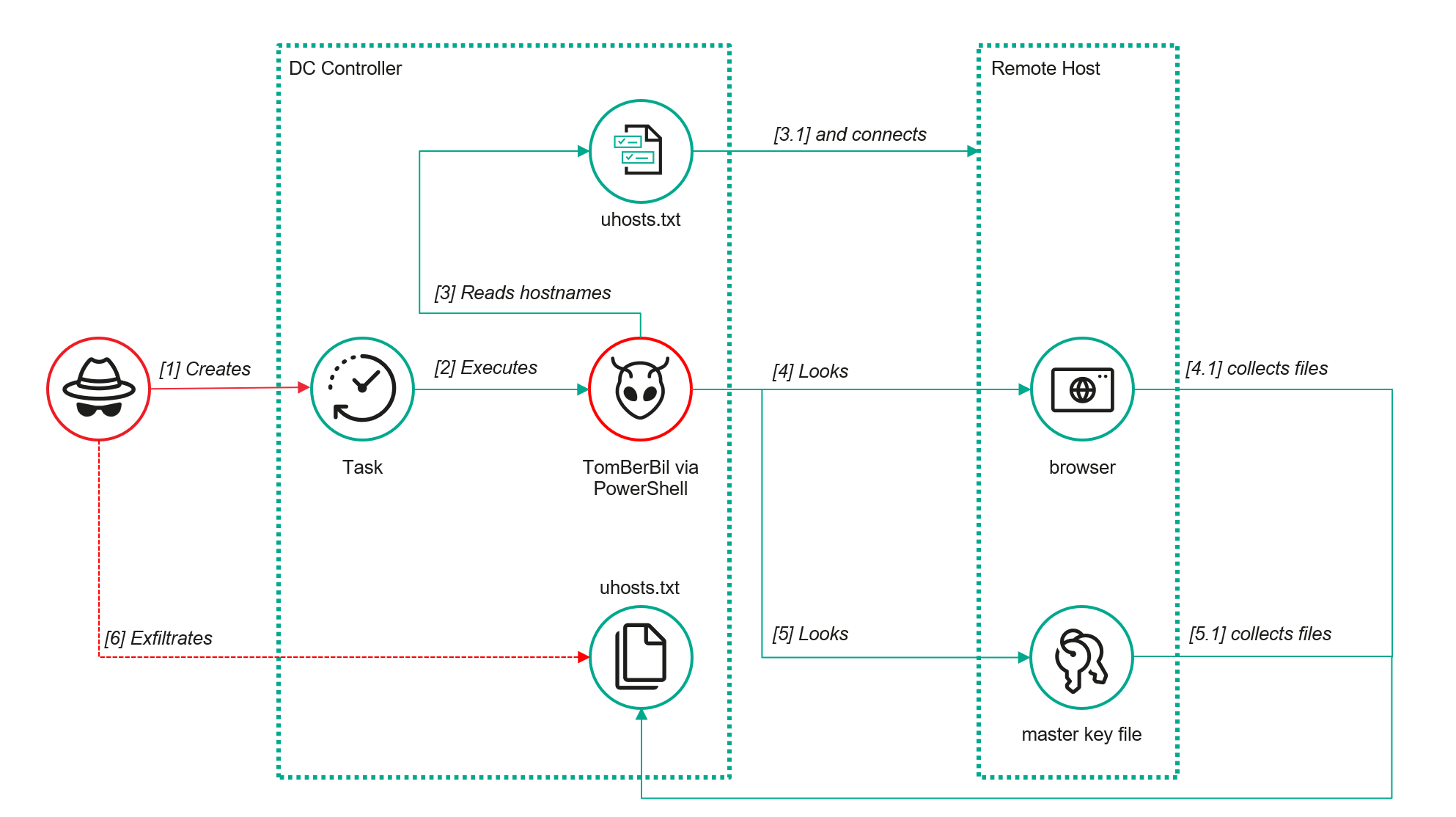
ToddyCat APT expanded and refined tools to extract browser credentials, DPAPI keys, Outlook OST files, and Microsoft 365 access tokens from compromised environments, using SMB-based collection, a PowerShell TomBerBil variant, a sector-copying tool (TCSectorCopy/xCopy), SharpTokenFinder/ProcDump memory dumps, and XstReader-based extraction. #TomBerBil #TCSectorCopy

The Gentlemen emerged around July 2025 as an advanced Ransomware-as-a-Service group using dual‑extortion to encrypt and exfiltrate data, publishing dozens of victims on a darknet leak site within months. Their cross‑platform lockers (Windows/Linux/ESXi), modular features (self‑restart, run‑on‑boot, WMI/PowerShell propagation), and affiliate support make them a rapidly evolving threat. #TheGentlemen #XChaCha20

North Korean threat actor Kimsuky is suspected of compromising a wedding photo editing company to distribute maliciously crafted image files to customers, using personalized wedding photos to increase infection likelihood. The attack chain uses Base64-encoded JScript to drop files under C:ProgramData, decodes payloads with certutil, and loads the final payload via regsvr32; #Kimsuky #certutil
Google Threat Intelligence Group (GTIG) reports that PRC‑nexus threat actor APT24 has run a three‑year espionage campaign delivering a heavily obfuscated first‑stage downloader named BADAUDIO—often using strategic web compromises, supply‑chain compromise of a Taiwanese marketing firm, and targeted phishing to deploy AES‑encrypted payloads such as Cobalt Strike Beacon. The report details BADAUDIO’s control‑flow flattening, DLL sideloading execution chain, fingerprinting‑based targeting, extensive infrastructure churn, and provides IOCs and YARA rules for detection. #BADAUDIO #APT24 #CobaltStrikeBeacon #twisinbeth.com
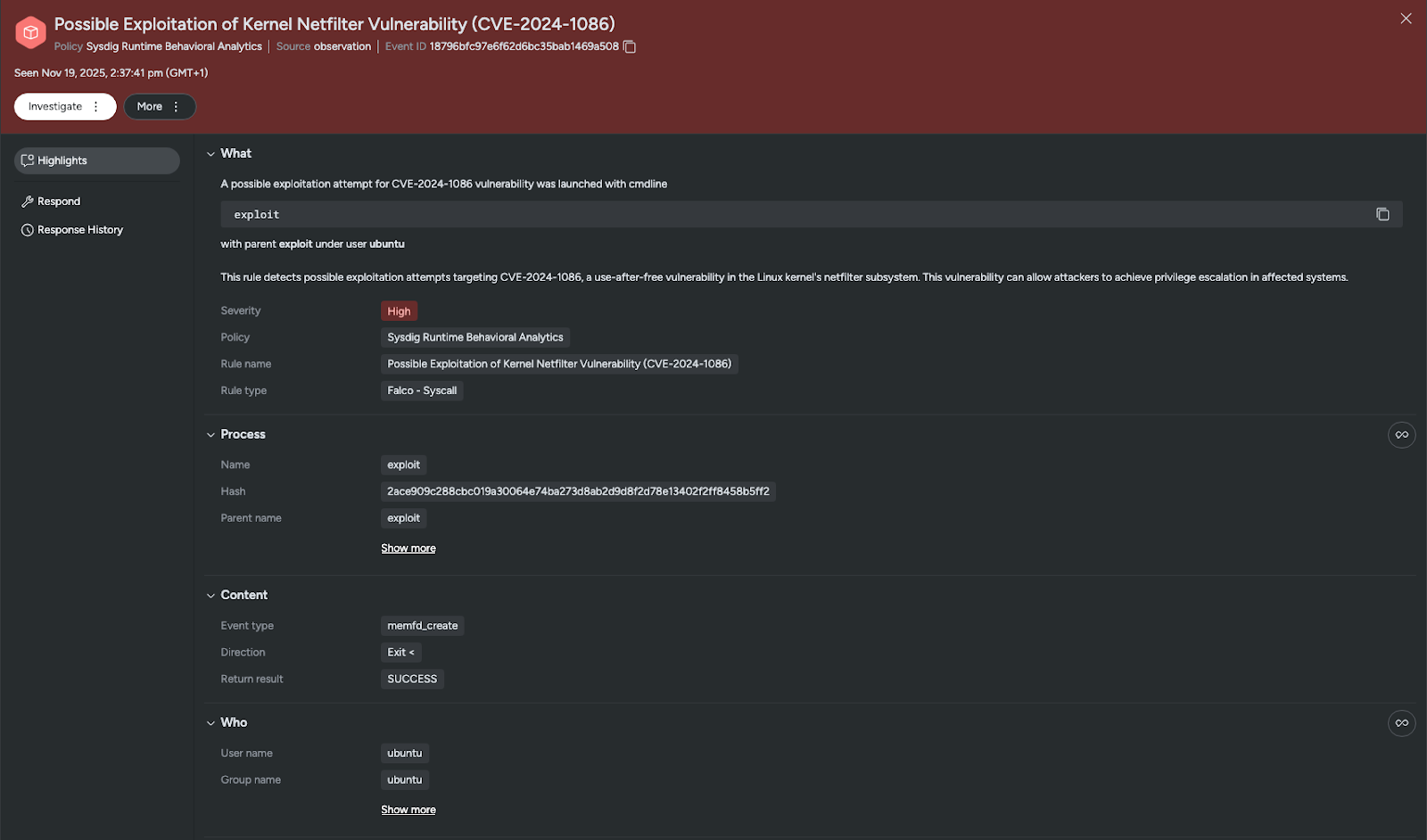
CVE-2024-1086 is a decade-old use-after-free vulnerability in the Linux kernel’s netfilter (nftables) component that allows attackers to gain root privileges and is being actively exploited in ransomware campaigns. Public PoC availability and default-enabled features like unprivileged user namespaces have expanded the attack surface, putting legacy and cloud Linux systems at high risk. #CVE-2024-1086 #nftables