K7 Labs uncovered a Water-Saci campaign targeting Brazil that spreads a banking trojan and SorvePotel-related components by abusing WhatsApp Web via a Python/Selenium-based automation script and in-memory payload delivery. The attack chain begins with a phishing ZIP containing an obfuscated VBS that downloads an MSI and VBS to install Python, ChromeDriver, and a whats.py script that harvests contacts, sends in-memory payloads through WhatsApp Web, and reports results to PHP C2s. #SorvePotel #Water-Saci
Keypoints
- Campaign uses phishing emails with ZIP-attached, charcode/XOR-obfuscated VBS to evade signature-based detection.
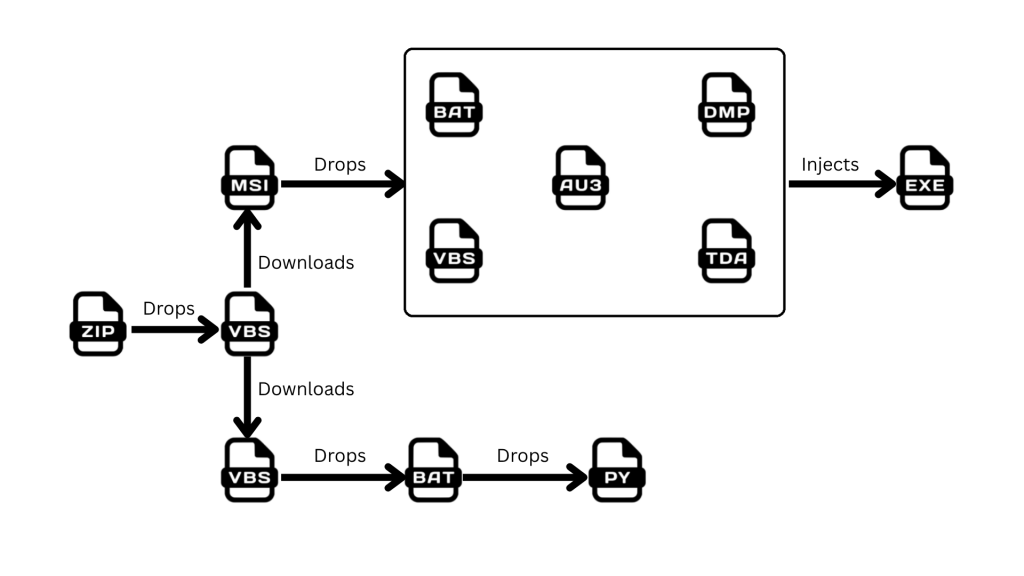
- Obfuscated VBS downloads an MSI and additional VBS then installs Python, ChromeDriver, and Selenium to run whats.py for WhatsApp-based propagation.
- whats.py uses Selenium to inject helper JavaScript into WhatsApp Web, harvests contacts from session artifacts, filters them, and sends a Base64-encoded payload in-memory to contacts to avoid disk-based detection.
- Configuration and results (harvested contacts, send success/failure) are posted back to a PHP C2 (varegjopeaks.com/altor/receptor.php); another C2 observed vip-imap-az.terra[.]com[.]br.
- MSI drops AutoIt, encrypted/compressed payloads (.tda/.dmp), VBS and BAT scripts; AutoIt monitors window titles for Brazilian banks/crypto apps and loads the banking PE in-memory via XOR decryption, RtlDecompressFragment, and reflective loading into svchost.
- AutoIt collects system info (computer name, OS, usernames, local/external IPs via api.ipify.org), AV/product checks (WMI, process names, uninstall registry), and browser history search for Brazilian banking keywords before exfiltration.
- Final banking Trojan executes purely in memory, injects into svchost, and communicates back (IMAP over TCP) to exfiltrate stolen data and facilitate further operations.
MITRE Techniques
- [T1566] Phishing – Delivered initial malicious ZIP with an archived VBS script via email: “…starts with a Phishing email with a ZIP archived malicious VBS script file.”
- [T1027] Obfuscated Files or Information – VBS and other scripts use charcode and XOR encoding to evade signature detections: “…leverages charcode and XOR encoding techniques to evade the Sign based detections.”
- [T1105] Ingress Tool Transfer – Scripts download MSI, VBS, Python components, ChromeDriver, and payloads from remote URLs: “…the script contains 2 functionalities, downloading a MSI file and a VBS file and executing them.”
- [T1176] Browser Extensions – Abuse of browser session and in-page APIs (WhatsApp Web) via injected helper JavaScript to interact with web app internals: “…inject a malicious JS code in WhatsApp Web… uses WhatsApp web internal APIs… helper JS file from Github.”
- [T1056] Input Capture (Web Session Hijacking) – Copies browser session artifacts (Cookies, Local Storage, IndexedDB) and launches Chrome with user-data-dir to reuse logged-in WhatsApp session: “…inspects standard profile folders… Artifacts are copied to a temporary folder… launch the browser with the victim’s past whatsapp web session, to avoid the need of QR-scan authentication.”
- [T1204] User Execution – Spam messages sent from trusted contacts entice recipients to open the payload delivered via WhatsApp: “…the malicious file is sent by someone already in our contacts… reduces our caution and increases the chances of the malware being opened and executed.”
- [T1564] Hide Artifacts – Transfers payload as Base64-encoded string into browser memory and sends as in-memory Blob to avoid writing files to disk: “…a Base64-encoded String is stored… transfers the binary data as text to the browser memory without touching the victim’s disk…”
- [T1086] PowerShell (analogous scripting) / [T1059] Command and Scripting Interpreter – Use of VBS, BAT, Python, AutoIt scripts to orchestrate stages and persistence: “…drops a .bat script which downloads and installs Python.zip, ChromeDriver.exe and PIP… executes a Python script whats.py.”
- [T1547] Boot or Logon Autostart Execution – Registers dropped VBS under the Run registry entry for persistence: “The script registers dropped VBS under run entry in registry for persistence.”
- [T1486] Data Encrypted for Impact (not for ransom but in-memory packing) – Payloads compressed/encrypted (.tda/.dmp) and decrypted in-memory before decompression and reflective loading: “…a compressed and encrypted payload in .tda and .dmp file format… reads it, decrypts it, decompresses it all in memory.”
- [T1218] Signed Binary Proxy Execution – Use of svchost injection and reflective loading to execute payloads in memory and evade disk-based detection: “…the loader calls VirtualAlloc… copies sections, applying relocations… loader calls VirtualProtect… injected PE then injects itself into SVCHOST…”
- [T1071] Application Layer Protocol – Exfiltration and C2 communications via HTTP POSTs to PHP server and IMAP over TCP: “…harvested contacts and successful payload send-result logs are typically POSTed back to the attacker’s PHP server… Connects back to server… using IMAP over TCP connection.”
Indicators of Compromise
- [File Name ] Delivered and dropped files observed – Installer.msi, Installer.VBS, whats.py, instalar.bat
- [File Hash ] Sample file hashes and contexts – Installer.msi DB0EAB25B047F82A4644B3B86767A1AA, whats.py 45027D8EA53921B59C70C38D90DD8C14 (and 4 more hashes)
- [Malicious File Types ] Encrypted/compressed payloads used for in-memory loading – .tda (NsmKL5.tda 5BCB9F18…), .dmp (95p1jx.dmp 8DBF4404…)
- [Domains / C2 ] Command-and-control servers – hxxps[:]//varegjopeaks.com/altor/receptor.php, vip-imap-az.terra[.]com[.]br
- [URLs / API ] External IP lookup used by malware – https://api.ipify.org (used to fetch external IP for system profiling)
Read more: https://labs.k7computing.com/index.php/brazilian-campaign-spreading-the-malware-via-whatsapp/