ToddyCat APT expanded and refined tools to extract browser credentials, DPAPI keys, Outlook OST files, and Microsoft 365 access tokens from compromised environments, using SMB-based collection, a PowerShell TomBerBil variant, a sector-copying tool (TCSectorCopy/xCopy), SharpTokenFinder/ProcDump memory dumps, and XstReader-based extraction. #TomBerBil #TCSectorCopy
Keypoints
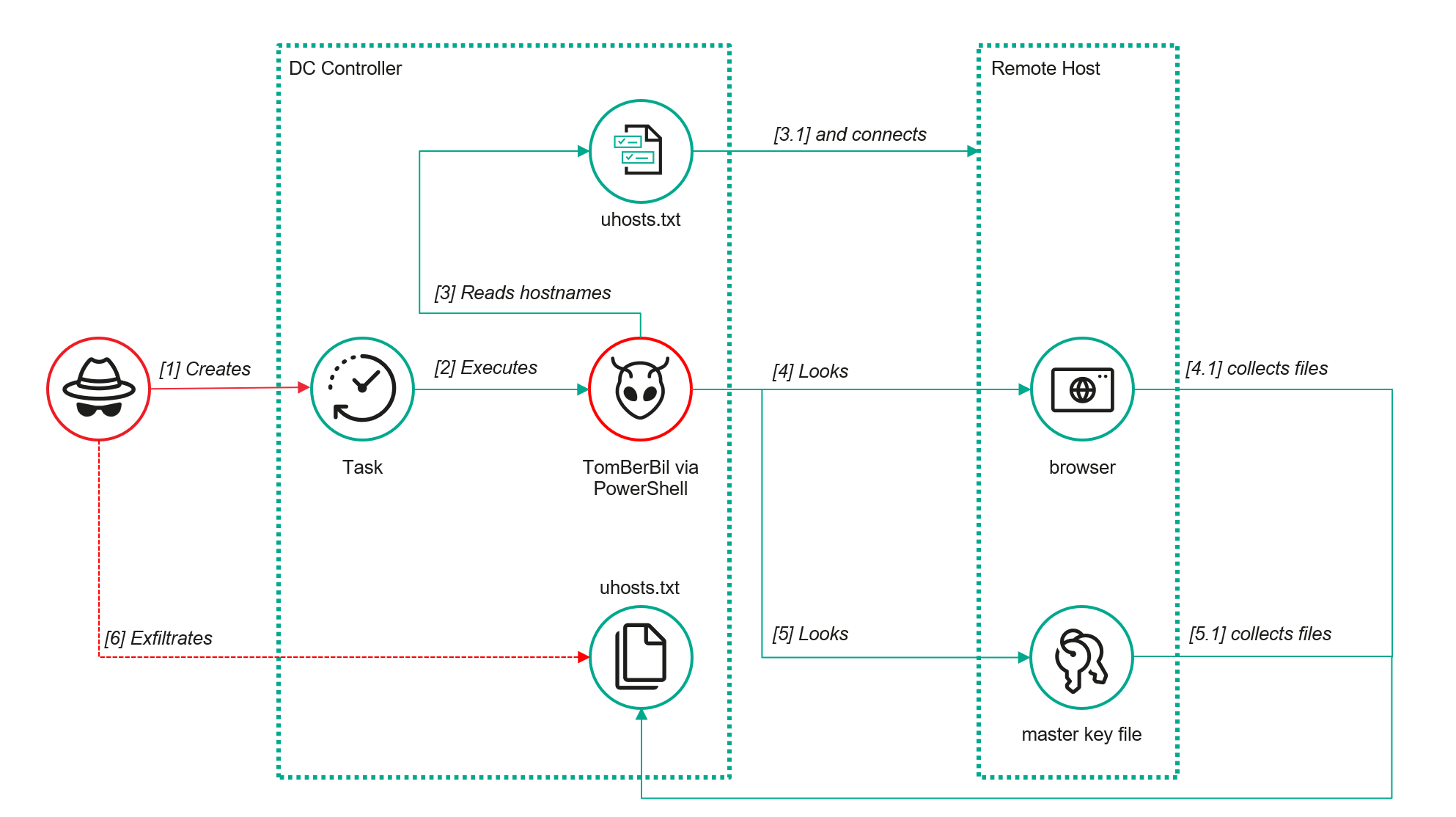
- ToddyCat deployed a new PowerShell variant of TomBerBil that remotely connects to hosts over SMB to copy browser files (Chrome, Edge, Firefox) and DPAPI-related key material from user profiles.
- The PowerShell TomBerBil runs from scheduled tasks (example: powershell -exec bypass -command “c:programdataip445.ps1”) and creates per-host/per-user directories under C:programdatatemp to store stolen files.
- Attackers used SMB to copy DPAPI protection folders and credential stores so they could decrypt browser-stored cookies, history, and saved passwords offline using collected master keys, SIDs, and passwords.
- To exfiltrate Outlook mail, the group used a sector-level copying tool (TCSectorCopy/xCopy) to bypass file locks on .ost files, then processed the copies with XstReader/XstExport to extract messages and attachments.
- To access Microsoft 365 mail without host-based collection, attackers dumped memory of Office/M365 processes (SharpTokenFinder or ProcDump) to locate JWT-formatted OAuth 2.0 access tokens and use them externally to retrieve mailbox data.
- Kaspersky published detection guidance and hunting rules: SMB access auditing for browser and DPAPI files (EventID 5145), auditing Outlook OST access (EventID 4663), Sysmon RawAccessRead detection (EventID 9), and ProcDump command-line monitoring for Office process names.
- IOCs provided include malicious file hashes, file names/paths (ip445.ps1, xCopy.exe, XstExport.exe), and a PDB path indicating SectorCopy development.
MITRE Techniques
- [T1555.003] Credentials from Web Browsers – TomBerBil collects browser files (Login Data, Cookies, History, Local State, Firefox key files) by copying them over SMB from remote hosts (“…the tool retrieves … list of user directories … copies Login Data, Cookies, History …”).
- [T1555] Credentials from Password Stores – TomBerBil copies DPAPI Protect and Credentials folders to obtain master keys required to decrypt browser-stored secrets (“…copies files containing the user encryption keys that are used by DPAPI”).
- [T1114.001] Email Collection: Local Email – TCSectorCopy/xCopy copies locked Outlook .ost files block-by-block to exfiltrate mailbox data (“…designed for block-by-block copying of files that may be inaccessible by applications … copied user OST files”).
- [T1114] Email Collection – XstReader/XstExport is used to export content and attachments from copied OST files into readable formats for exfiltration (“…used XstReader to export the content of the previously copied OST files … export of all messages and their attachments”).
- [T1057/T1005] Process Discovery / Data from Local System Memory – SharpTokenFinder (and ProcDump usage) dumps memory of Office/M365 processes to locate JWT access tokens in process memory (“…tool searches system for … OUTLOOK … opens each process … dump their memory … searches for ‘eyJ0eX[a-zA-Z0-9._-]+’”).
- [T1563/T1021] Lateral Movement / SMB – The group uses SMB to access remote C$ shares and copy user profile data and browser files from other hosts (“…attempts to establish an SMB connection to the shared resource c$ … copies via SMB to the local folder”).
- [T1560.001] Archive Collected Data – The operators compress dumps and exported files (using WinRAR example) before exfiltration (“…file is added to a dmp.rar archive using WinRAR … sent this file to their host via SMB”).
Indicators of Compromise
- [File Hashes] Malicious binaries and scripts – 55092E1DEA3834ABDE5367D79E50079A (ip445.ps1), 23120377D4F68081DA7F39F9AF83F04A2 (xCopy.exe), B9FDAD18186F363C3665A6F54D51D3A0 (stf.exe)
- [Not-a-virus file hash] Legit/utility used in workflow – 49584BD915DD322C3D84F2794BB3B950 (XstExport.exe)
- [File paths] Known tool/script locations – C:programdataip445.ps1 ; C:WindowsTempxCopy.exe ; C:WindowsTempXstExport.exe ; c:windowstempstf.exe
- [PDB] Development path indicating tool origin – O:ProjectsPenetrationToolsSectorCopyReleaseSectorCopy.pdb
Read more: https://securelist.com/toddycat-apt-steals-email-data-from-outlook/118044/