Security awareness trainings can be effective when designed as a long-term, interactive program with short, repeated learning units rather than a single annual lecture. Misconceptions—such as trainings shifting responsibility onto users or being inherently deceptive or impractical—are refuted, and the article highlights the need for a systemic approach to reduce email-based incidents. #GDATA #phishing-email
Category: Threat Research

Shai‑Hulud 2.0 is a self‑replicating npm worm that backdoored 796 unique npm packages (over 20 million weekly downloads) to install a Bun‑based obfuscated credentials stealer which exfiltrates secrets to public GitHub repositories. The worm propagates without a C2 by reading its own code to infect up to 100 packages per compromised npm account and leverages stolen GitHub and npm tokens plus self‑hosted runners and vulnerable GitHub Actions to execute remote code and persist; #Shai-Hulud-2.0 #asyncapi

Acronis TRU researchers uncovered a novel “JackFix” ClickFix campaign that hijacks the browser to display a convincing full‑screen fake Windows Update prompting victims to run malicious commands. The multistage attack (mshta → PowerShell downloader → final payloads) uses heavy obfuscation, UAC bombardment and a “spray and prey” downloader that executes up to eight payloads including Rhadamanthys and Vidar 2.0, and is detected and blocked by Acronis XDR at the PowerShell stage. #ClickFix #Rhadamanthys

Socket’s Threat Research Team discovered a malicious Chrome extension named Crypto Copilot that injects a hidden SystemProgram.transfer into every Raydium swap, siphoning the greater of 0.0013 SOL or 0.05% of the trade to a hardcoded attacker wallet. The extension’s behavior is obfuscated in the bundle, undisclosed in the Chrome Web Store listing, communicates with typo/parked backend domains, and remains available while a takedown request is pending. #CryptoCopilot #Solana

Berserk Bear is an FSB-linked espionage group active since at least 2010 that conducts long-running, stealthy intrusions against critical infrastructure, especially energy, telecom, aviation, and state/local networks. Their campaigns reuse legitimate admin tools, trojanize vendor software, and exploit router vulnerabilities (notably CVE-2018-0171) while deploying implants such as Havex to maintain persistent access. #BerserkBear #Havex

A new wave of the self‑propagating worm known as Sha1-Hulud has compromised 605 npm packages — including @asyncapi/specs (linked as patient-zero) — affecting packages with a combined lifetime download count of over 100 million. The malware is delivered via a package version update that adds setup_bun.js and bun_environment.js executed by a preinstall script, and includes secret‑stealing exfiltration to randomly named public GitHub repositories plus new wiper functionality. #Sha1-Hulud #npm
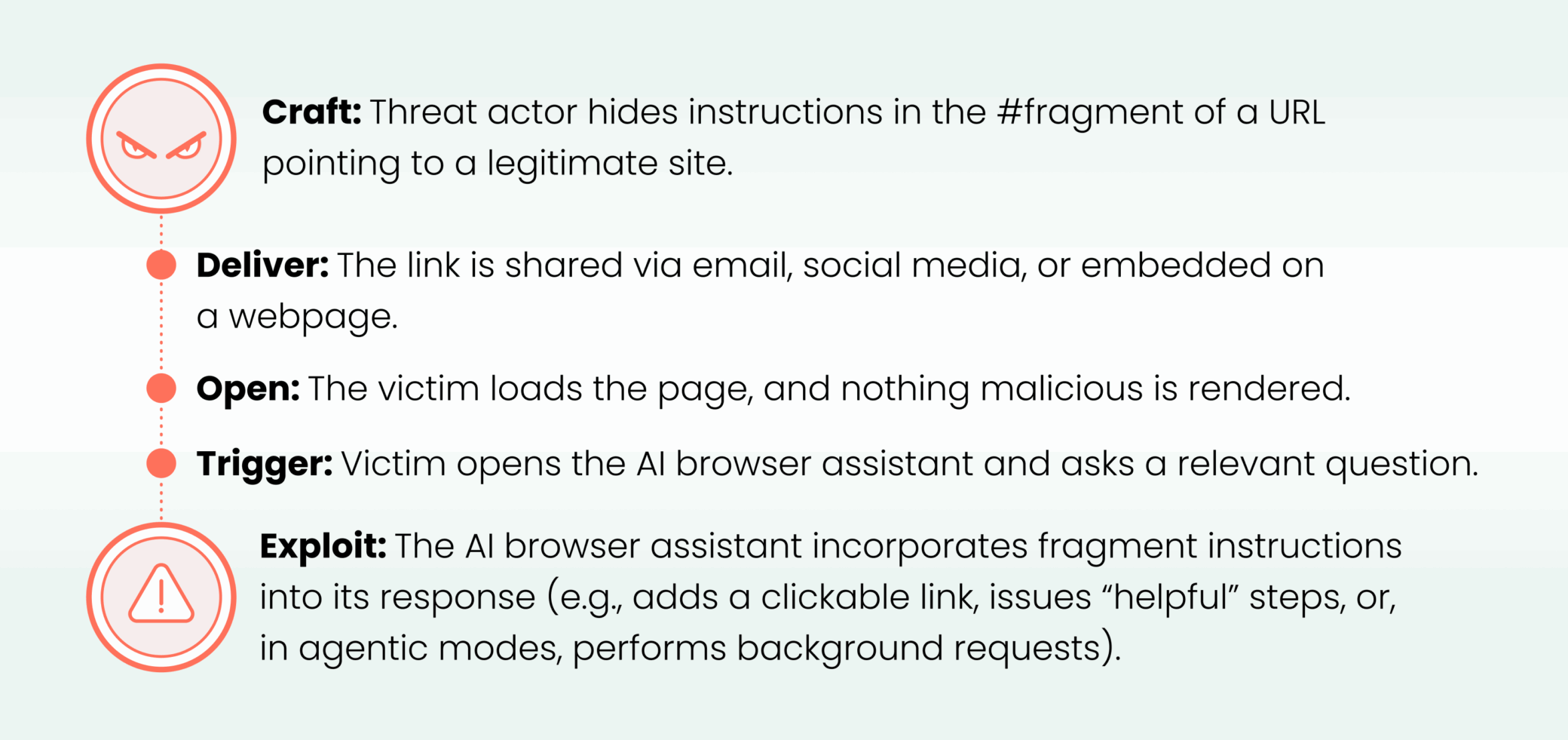
Cato CTRL™ Threat Research: HashJack – Novel Indirect Prompt Injection Against AI Browser Assistants
HashJack is an indirect prompt injection technique that hides malicious instructions in URL fragments (after ‘#’) so AI browser assistants receive and execute them, enabling attacks such as callback phishing, data exfiltration (in agentic modes), misinformation, malware guidance, medical harm, and credential theft. Cato CTRL validated the technique against Comet (Perplexity), Copilot for Edge (Microsoft), and Gemini for Chrome (Google), and recommends mitigations including CASB, NGAM, and IPS to reduce downstream impact. #HashJack #Comet
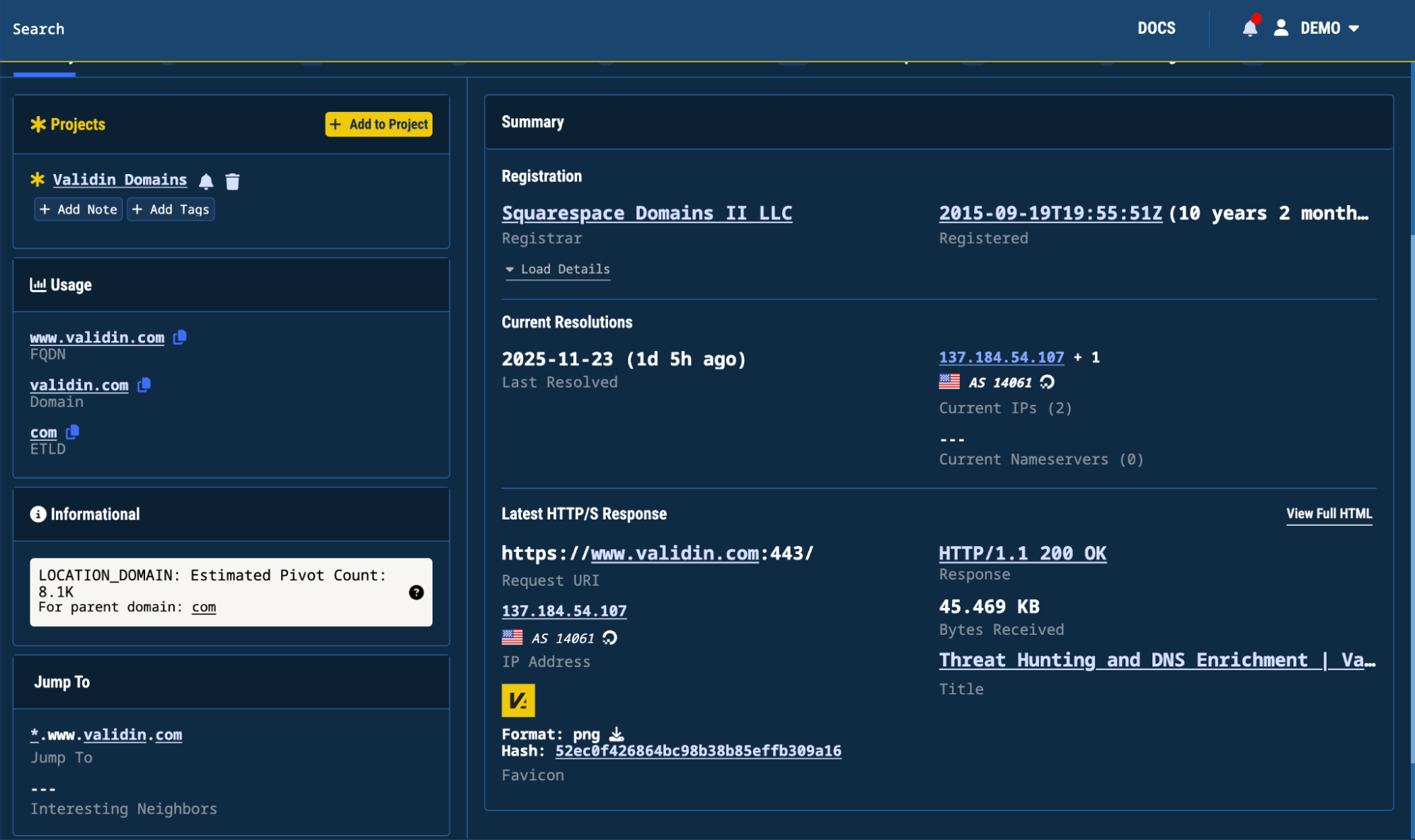
Validin released updates that improve domain and IP summaries on the Search page, a refreshed Projects UI with a context-aware sidebar, and YARA workflow enhancements including new match-table columns, easier deletion and filtering of matches, and visibility into rule activity. YARA-X integration exits beta on December 1st with billing displayed to users and billing beginning January 1st. #Validin #YARA-X
Truesec observed a malicious installer distributed from conmateapp[.]com that drops UpdateRetriever.exe and conmate_update.ps1, creates artifacts (updating_files.zip, native.zip), schedules a recurring task, and connects to multiple hardcoded C2 domains. The campaign reuses a signing certificate issued to AMARYLLIS SIGNAL LTD and closely mirrors the earlier PDFEditor activity; Truesec published updated IOCs and hashes and recommends isolating/removing the software and blacklisting the listed domains. #ConvertMate #UpdateRetriever_exe #AMARYLLIS_SIGNAL_LTD #PDFEditor
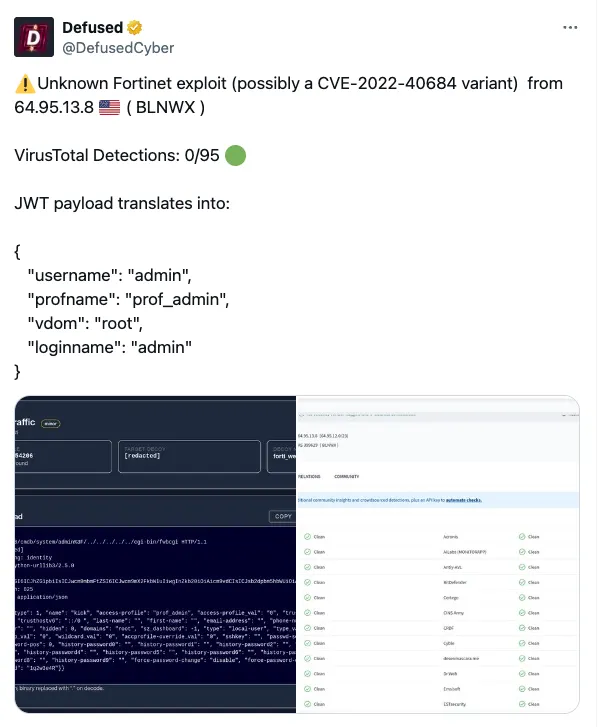
watchTowr Labs discovered a critical FortiWeb vulnerability chain allowing path traversal to reach the fwbcgi CGI and an authentication bypass via a Base64-encoded HTTP_CGIINFO header that permits full admin impersonation. Exploitation enables creation of persistent admin accounts on affected FortiWeb appliances and has been assigned CVE-2025-64446; #FortiWeb #CVE-2025-64446…
Jamf Threat Labs analyzed a new macOS infostealer family named DigitStealer that uses unsigned disk images, multi-stage in-memory payloads, AppleScript/JXA, and hardware-based sysctl checks to target Apple Silicon M2+ systems and evade detection. The campaign modifies Ledger Live to redirect endpoints, exfiltrates credentials and files to attacker-controlled domains (notably goldenticketsshop[.]com), and…

Check Point Research discovered four Microsoft Teams vulnerabilities that let external guests and malicious insiders impersonate executives, edit messages without leaving an “Edited” label, manipulate notifications, change private chat display names, and forge caller identities in calls. Microsoft addressed the issues after disclosure (one tracked as CVE-2024-38197) with fixes rolled out…

ReversingLabs researchers found legacy bootstrap scripts in multiple PyPI packages that fetch and execute an installation script from the abandoned python-distribute[.]org domain, creating a supply-chain risk if that domain is claimed by an attacker. Several popular packages (for example slapos.core, tornado, pypiserver) still contain or invoked bootstrap scripts that could execute arbitrary code via that domain, demonstrating a domain-takeover vector similar to prior npm compromises. #python-distribute #PyPI

Multiple popular npm scopes (including @zapier, @asyncapi, @postman, @posthog and @ensdomains) were compromised via account takeover and developer compromise to inject a stealthy two-stage loader (setup_bun.js → bun_environment.js) that installs or locates the Bun runtime and runs an obfuscated 10MB payload in the background while suppressing all output. The malicious code harvests CI and cloud credentials (GITHUB_TOKEN, NPM_TOKEN, AWS keys), performs aggressive multi-region cloud secret enumeration, propagates by using stolen NPM tokens to republish packages, and includes destructive file-shredding if no valid tokens are found. #Sha1-Hulud #Bun

Gen researchers discovered evidence of infrastructure overlap linking Russia-aligned Gamaredon and North Korea’s Lazarus, with a shared IP (144[.]172[.]112[.]106) hosting an obfuscated InvisibleFerret payload. This overlap, plus other reused IPs across North Korean groups, suggests possible cross-country and intra-national APT cooperation that could enable operational synergy and broaden offensive capabilities. #Gamaredon #Lazarus
