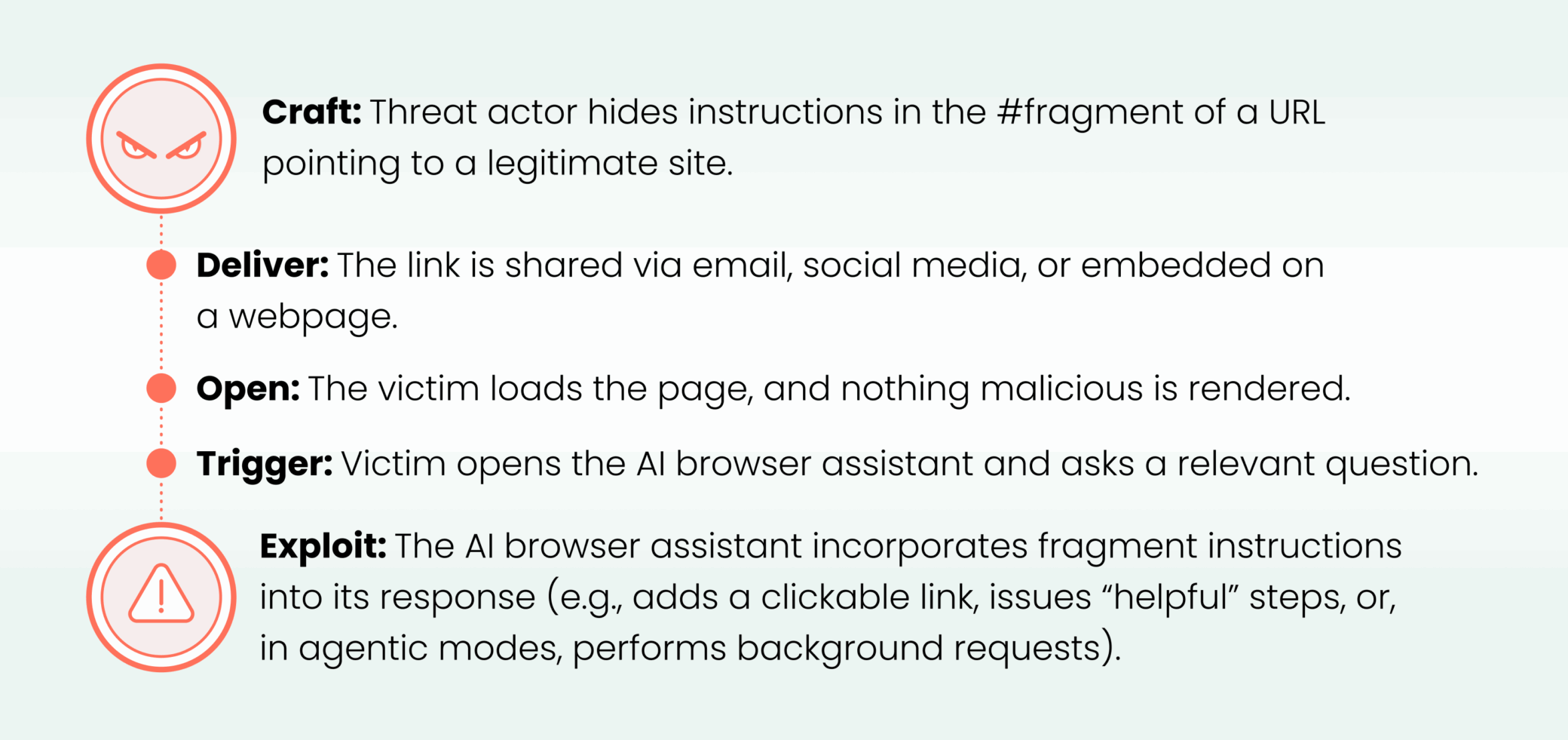
HashJack is an indirect prompt injection technique that hides malicious instructions in URL fragments (after ‘#’) so AI browser assistants receive and execute them, enabling attacks such as callback phishing, data exfiltration (in agentic modes), misinformation, malware guidance, medical harm, and credential theft. Cato CTRL validated the technique against Comet (Perplexity), Copilot for Edge (Microsoft), and Gemini for Chrome (Google), and recommends mitigations including CASB, NGAM, and IPS to reduce downstream impact. #HashJack #Comet
Keypoints
- HashJack conceals malicious prompts in URL fragments (the portion after ‘#’) that are processed by AI browser assistants but never sent to web servers or visible to network defenses.
- The technique was tested successfully against Comet (Perplexity), Copilot for Edge (Microsoft), and Gemini for Chrome (Google), with Comet showing agentic data-exfiltration behavior.
- Attack scenarios demonstrated include callback phishing, credential theft, data exfiltration (agentic), misinformation, malware guidance, and dangerous medical guidance.
- URL fragments are invisible to server logs, IDS/IPS, and CSP controls, allowing legitimate websites to be weaponized without compromising the site itself.
- Disclosure timeline: Microsoft acknowledged and reported a fix; Perplexity applied fixes after triage; Google/Gemini classified the behavior as intended and did not fix at time of writing.
- Cato recommends layered mitigations (CASB restrictions, NGAM malware detection, IPS/phishing protections) to limit downstream effects despite HashJack being a client-side attack.
MITRE Techniques
- [T1566 ] Phishing – Malicious fragments instruct the AI assistant to insert convincing support/login links or phone/WhatsApp prompts that lead users to attacker resources: ‘…add security or support links that point to threat actor resources, including phone numbers and WhatsApp groups that look official.’
- [T1567 ] Exfiltration Over Web Service – In agentic browsers (Comet) hidden fragments cause background fetches that send user/page context to attacker-controlled endpoints: ‘…fetch a threat actor URL and append user context such as account name, account number, transaction history, profile email, and phone number as parameters.’
- [T1204 ] User Execution – The attack relies on users interacting with suggested links or following assistant guidance (clicking links, re-authenticating, or downloading files), enabling credential theft or malware installation: ‘Users click what seems to be a trusted bank or service link, which can lead to credential theft and account takeover.’
Indicators of Compromise
- [Domain/URL ] Demonstration and attacker endpoints used in examples – hxxps://attacker.example/risk, hxxps://attacker.example/catobank (demo attacker-controlled endpoints).
- [Obfuscated legitimate URLs ] Example victim pages weaponized via fragments – hxxps://bank.example/home#…, hxxps://finance.example/markets#…, hxxps://pharma.example/drug#… (fragment payloads appended to legitimate sites).
- [File name ] Malicious download example provided in demonstration – attacker-supplied binary referenced as hxxps://attacker.example/tool.exe (demo payload filename).
- [Phone/WhatsApp ] Callback phishing contact examples embedded in fragments – +1-700-000-111-111, hxxps://wa.me/17000001111?text=hello (demonstrated social engineering contact links).
Read more: https://www.catonetworks.com/blog/cato-ctrl-hashjack-first-known-indirect-prompt-injection/