A Kimsuky campaign delivered an obfuscated Windows Script Host JScript dropper inside an ALZ-compressed email attachment named “건강검진 안내서.alz” that displays a fake PDF while dropping and executing a DLL via rundll32. The malware uses multi-stage Base64 decoding (certutil/PowerShell), stores payloads under C:ProgramData, communicates with C2 at load.samework.o-r.kr using AES-CBC-encrypted POST bodies and a decrypted Chrome 79 user-agent, and achieves persistence via regsvr32 scheduled execution. #Kimsuky #NationalHealthInsurance
Category: Threat Research
Kimsuky and Lazarus operate as a coordinated pair — Kimsuky conducts precise espionage via academic-themed spearphishing to collect network maps and credentials, while Lazarus exploits zero-day vulnerabilities to escalate privileges and steal cryptocurrency. The collaboration uses shared C2 infrastructure, bespoke backdoors (e.g., FPSpy, InvisibleFerret) and evasive techniques to exfiltrate intelligence and millions in crypto with minimal detection. #Kimsuky #Lazarus

ReversingLabs discovered legacy bootstrap scripts in popular Python packages that fetch and execute an installation script from the abandoned python-distribute[.]org domain, creating a potential domain-takeover supply-chain risk for developers who run those scripts. The issue affects packages such as slapos.core, pypiserver and tornado and echoes a prior npm compromise (fsevents), highlighting the danger of hardcoded domains in build automation. #python-distribute #PyPI
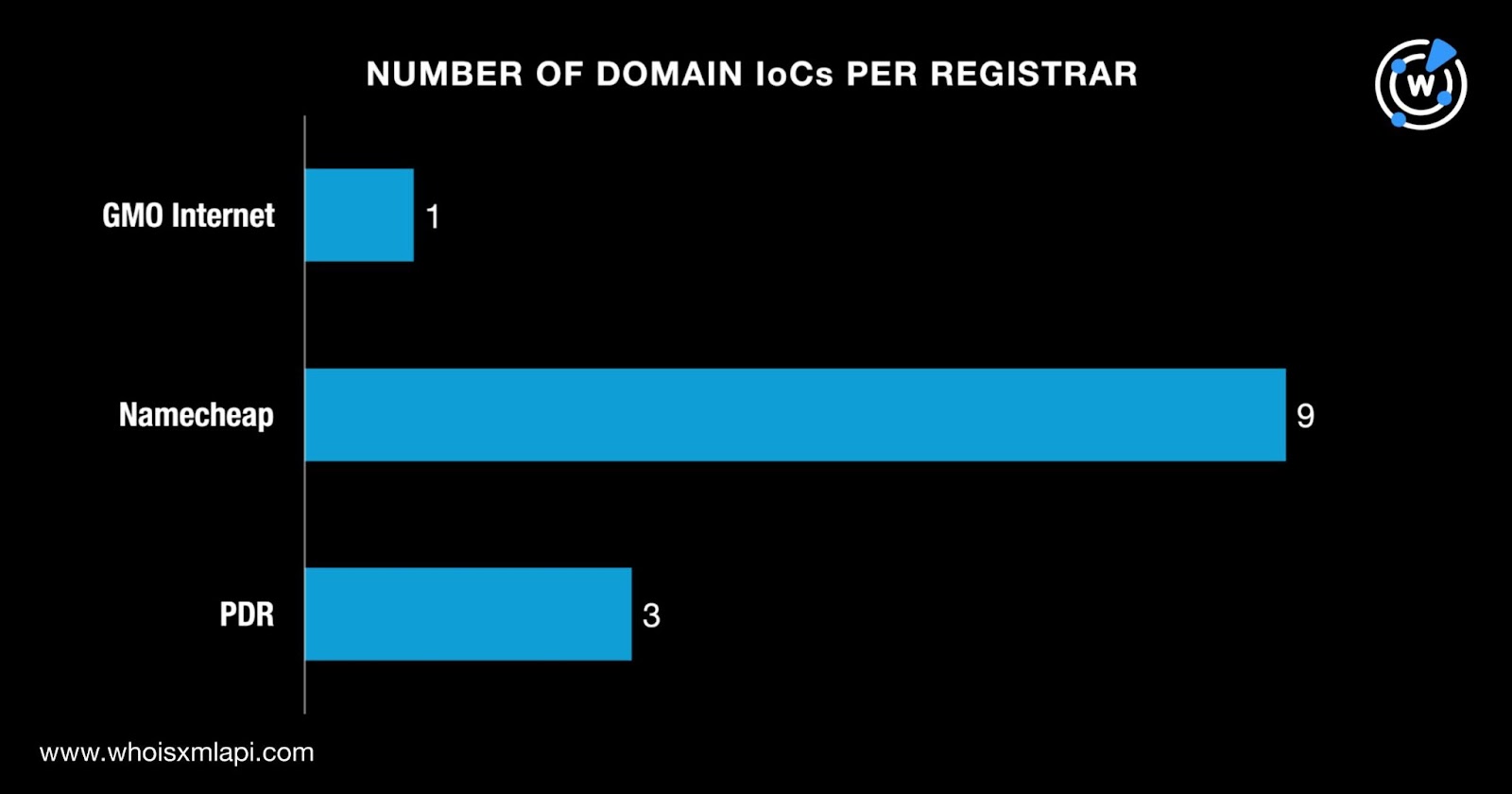
Google Threat Intelligence Group (GTIG) and WhoisXML API reported that Russia-linked COLDRIVER has retooled its homegrown backdoor—originally NOROBOT, then YESROBOT—into a new variant called MAYBEROBOT used in targeted attacks against NGO staff, policy advisors, and dissidents. WhoisXML API’s analysis of GTIG’s 14 IoCs (13 domains, 1 IP) uncovered early warnings for some domains, registrar and geolocation details, historical DNS resolutions, nine email-linked WHOIS records, and four additional malicious IPs discovered during artifact hunting. #COLDRIVER #MAYBEROBOT

The article advocates integrating threat intelligence with vulnerability management to prioritize remediation based on real-world attacker activity and asset criticality rather than raw severity scores. It highlights Recorded Future’s Vulnerability Intelligence and its integrations (e.g., Tenable, Qualys, ServiceNow, Splunk) as a way to enable real-time risk scoring, automated prioritization, and dashboards to reduce MTTR and move from reactive to proactive VM. #RecordedFuture #Tenable #Qualys #ServiceNow #Splunk #MSRC #CISA #KEV #EPSS
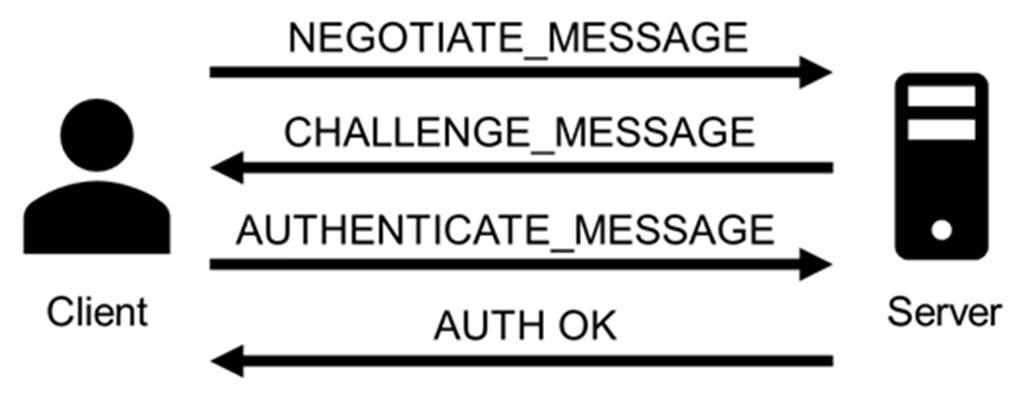
NTLM remains widely present in modern Windows environments and continues to be exploited through both long-standing and newly disclosed vulnerabilities that leak authentication hashes and enable relay/reflection attacks. Notable 2024–2025 flaws (CVE-2024-43451, CVE-2025-24054/24071, CVE-2025-33073) have been weaponized by groups such as BlindEagle and Head Mare to deliver Remcos, PhantomCore, and AveMaria, prompting recommendations to disable/limit NTLM, enable signing and EPA, and monitor NTLM traffic. #Remcos #BlindEagle
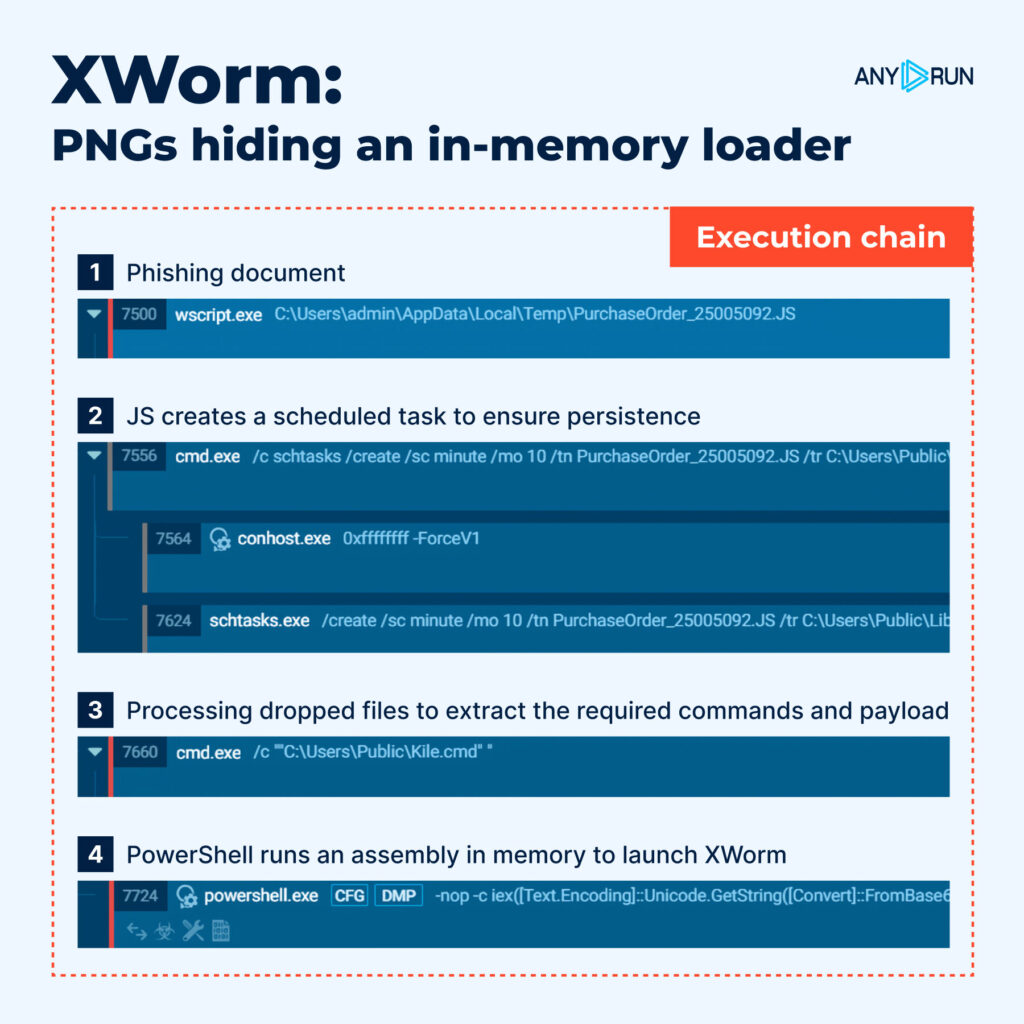
ANY.RUN analysts reviewed November activity dominated by multi-stage loaders, stealers, and targeted campaigns that used PNG-based in-memory loaders and a JScript-to-PowerShell chain. Sandbox analyses and three Threat Intelligence Reports detailed threats across Windows, Linux, and Android, revealing execution flows, persistence artifacts, and IOCs SOC teams can use to strengthen detections before…

Scattered LAPSUS$ Hunters (SLSH) resumed activity in November 2025, claiming new Salesforce-related data theft via a Gainsight breach, threatening deadlines and launching a ransomware-as-a-service offering called ShinySp1d3r. The actors also recruited insiders, posted screenshots and leak-site teasers on Telegram, and prompted affected vendors to revoke tokens and rotate S3 keys. #ShinySp1d3r…
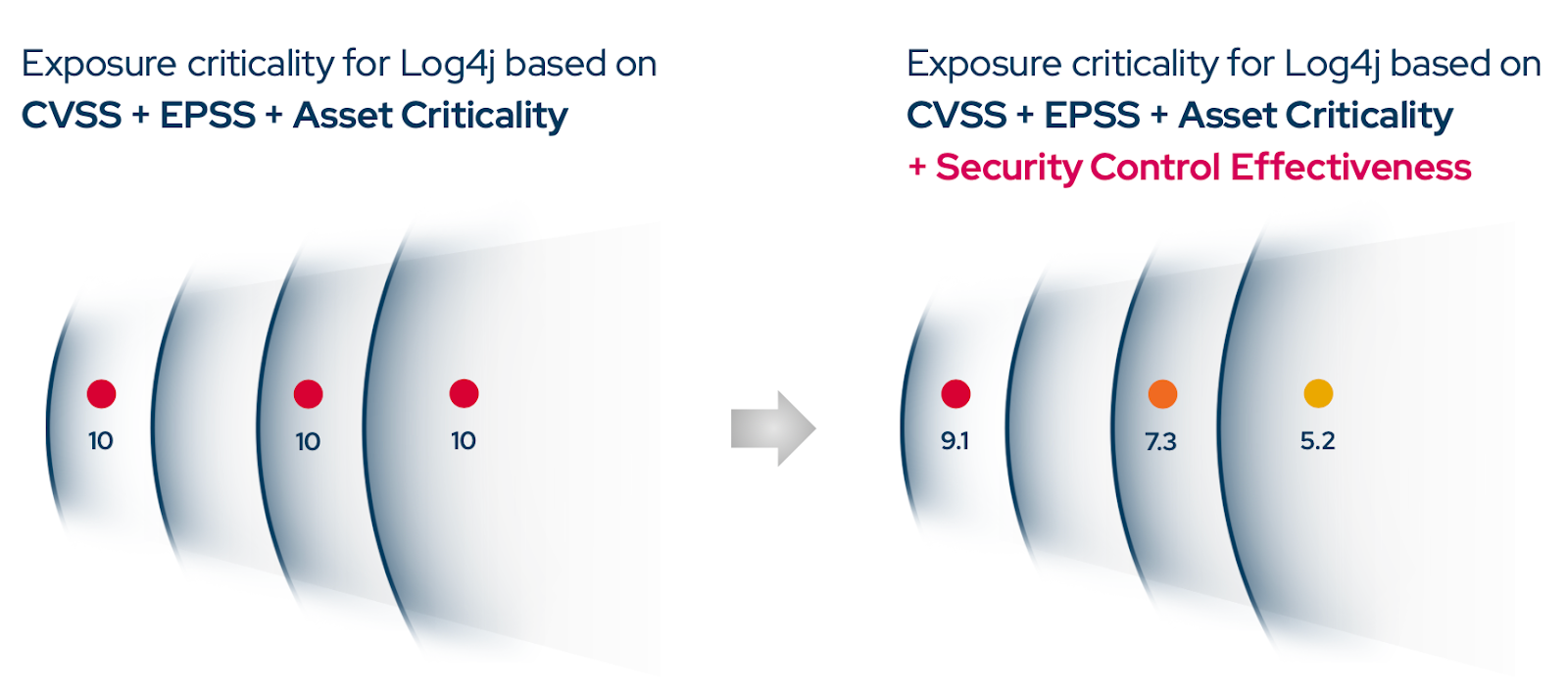
Automated Security Validation (ASV) continuously simulates real-world attacker tactics to validate whether flagged vulnerabilities are actually exploitable in an organization’s specific environment and to measure control effectiveness in real time. Adversarial Exposure Validation technologies—Breach and Attack Simulation (BAS) and Automated Penetration Testing (APT)—help reduce remediation backlogs, speed up MTTR, and provide continuous compliance and remediation validation with platforms such as Picus Security. #Log4j #PicusSecurity

Xillen Stealer is a Python-based cross-platform information stealer whose v4 and v5 updates expand capabilities to harvest credentials, browser data from 100+ browsers, cryptocurrency from 70+ wallets, container and cloud configurations, and biometric/TOTP data while adding persistence, polymorphism, and P2P C2 features. The malware is marketed via Telegram by a group calling itself Xillen Killers and has public GitHub activity and sample hashes published in the appendices. #XillenStealer #XillenKillers
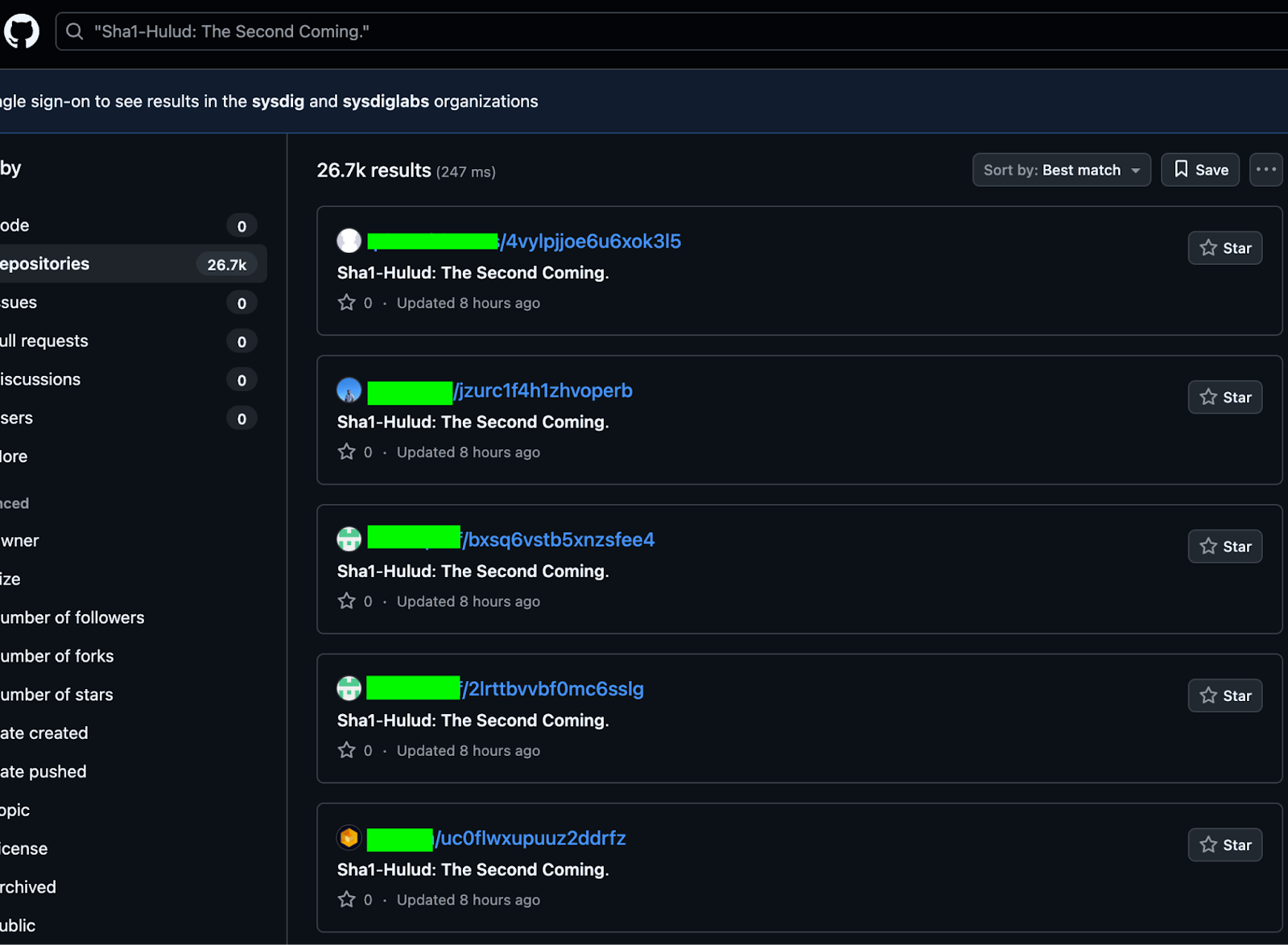
The second version of the Shai-Hulud worm is propagating through backdoored NPM packages, executing during npm preinstall to run bundled JavaScript (via node/bun), steal credentials, exfiltrate secrets to attacker-controlled GitHub repositories, install a self-hosted GitHub Actions runner for persistent backdoor access, and delete user files when no NPM token is found. The campaign has trojaned ~800–1,000 NPM packages and leaked credentials from over 25,000 GitHub repositories, with exfiltrated artifacts like cloud.json and actionsSecrets.json available in created repositories. #Shai-Hulud #GitHub

A second major wave of the self‑propagating Shai‑Hulud worm—branded “Sha1‑Hulud: The Second Coming”—has compromised 605 npm packages, including high‑impact packages such as @asyncapi/specs, affecting packages with a combined download count of over 100 million. The attack used a malicious package version update that added setup_bun.js and bun_environment.js and a preinstall script in package.json to execute an obfuscated payload that steals cloud service secrets, exfiltrates them to thousands of public GitHub repositories, and in some cases includes data‑wiping functionality. #Sha1-Hulud #AsyncAPI

Between late 2024 and early 2025 the U.S. government issued indictments or sanctions against three Chinese information security firms—i-SOON, Sichuan Silence, and Integrity Tech—alleging their support for or links to malicious cyber groups targeting U.S. government and critical infrastructure systems. At LABScon 2025 Mei Danowski and Eugenio Benincasa presented research showing these firms and a broader private cybersecurity industry provide commercial cyber ranges and “attack-defense live-fire” exercises that nurture China’s offensive cyber talent and support state-linked operations. #i-SOON #IntegrityTech

Cyble Research and Intelligence Labs (CRIL) uncovered RelayNFC, an Android malware campaign in Brazil that uses phishing sites to install a React Native app which relays NFC APDU commands in real time over WebSockets to attacker-controlled servers to complete contactless payments. The malware uses Hermes bytecode to hinder static analysis and includes a variant experimenting with Host Card Emulation (HCE); VirusTotal detections are currently zero. #RelayNFC #Hermes

Security awareness trainings can be effective when designed as a long-term, interactive program with short, repeated learning units rather than a single annual lecture. Misconceptions—such as trainings shifting responsibility onto users or being inherently deceptive or impractical—are refuted, and the article highlights the need for a systemic approach to reduce email-based incidents. #GDATA #phishing-email
