Google Threat Intelligence Group (GTIG) and WhoisXML API reported that Russia-linked COLDRIVER has retooled its homegrown backdoor—originally NOROBOT, then YESROBOT—into a new variant called MAYBEROBOT used in targeted attacks against NGO staff, policy advisors, and dissidents. WhoisXML API’s analysis of GTIG’s 14 IoCs (13 domains, 1 IP) uncovered early warnings for some domains, registrar and geolocation details, historical DNS resolutions, nine email-linked WHOIS records, and four additional malicious IPs discovered during artifact hunting. #COLDRIVER #MAYBEROBOT
Keypoints
- COLDRIVER has iteratively redesigned its backdoor from NOROBOT to YESROBOT and now MAYBEROBOT, which was used in the latest targeted campaign.
- Primary targets included high-profile individuals in NGOs, policy advisors, and dissidents, with MAYBEROBOT appearing aimed at more specific targets than prior variants.
- GTIG published 14 IoCs related to the campaign: 13 domains and one IP address.
- WhoisXML API found four of the domain IoCs were flagged as likely to turn malicious 127–182 days before GTIG’s public reporting (examples: documentsec[.]online, system-healthadv[.]com).
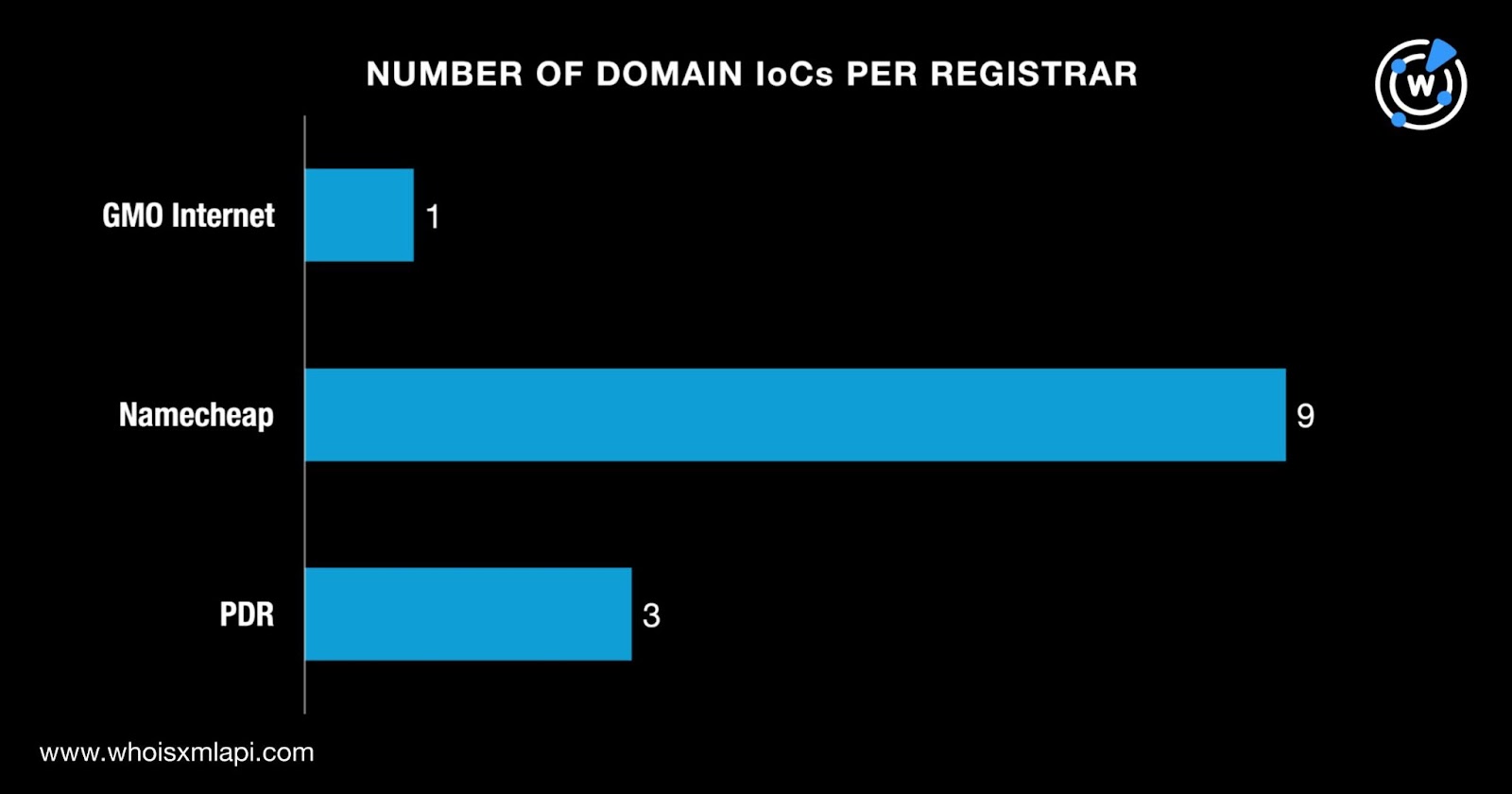
- The 13 domain IoCs were all newly created between 2 April and 2 July 2025 and were registered primarily through Namecheap (9 domains), PDR (3), and GMO Internet (1).
- DNS history showed 57 domain-to-IP resolutions across the domains with individual domains showing multiple resolutions and first/last resolution dates (examples: inspectguarantee[.]org, southprovesolutions[.]com).
- Artifact hunting revealed nine unique email addresses in WHOIS history (one public), six domains with active IP resolutions that mapped to four additional IPs, and all four additional IPs were flagged as weaponized for malware distribution.
MITRE Techniques
- No MITRE ATT&CK techniques were mentioned in the article.
Indicators of Compromise
- [Domains ] GTIG published 13 domain IoCs related to the campaign – documentsec[.]online, system-healthadv[.]com, and 11 more domains.
- [IP addresses ] One primary IP IoC (geolocated in the U.S., administered by TimeWeb) plus four additional malicious IPs discovered during hunting – 185.28.119.41, 192.99.241.162, and 3 more IPs (194.213.18.25, 37.139.52.50, plus the original IoC IP).
- [Email addresses ] WHOIS history included nine unique email addresses (one public) linked to the domains – no specific email strings published in the article, one public email connected to an additional domain, and 8 other addresses.
Read more: https://circleid.com/posts/coldrivers-mayberobot-in-the-dns-spotlight