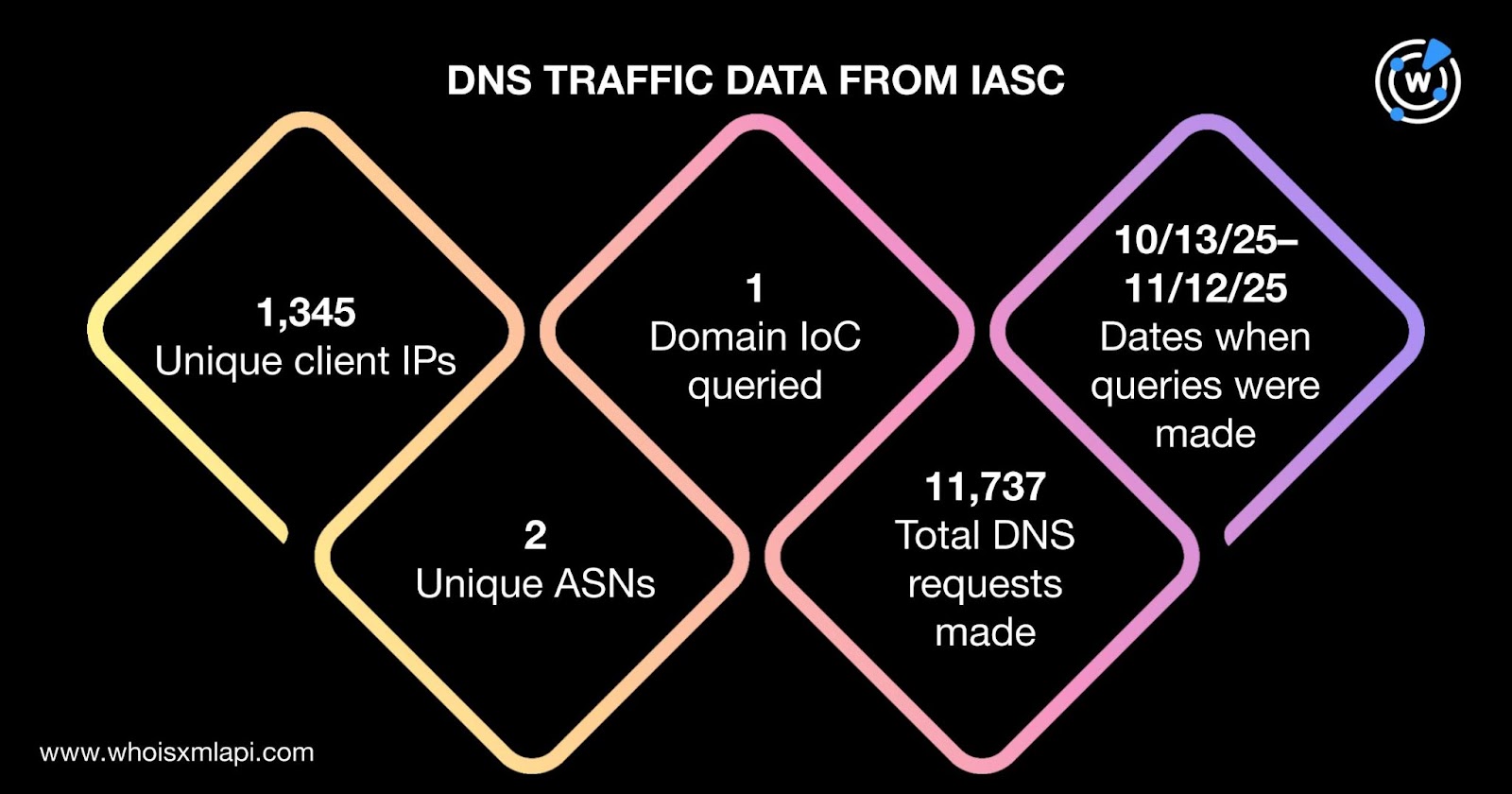
BlueNorroff targeted tech executives, venture capitalists, and Web3 developers with two interrelated campaigns—GhostCall (macOS-focused via malicious Zoom updates) and GhostHire (GitHub-based malware disguised as recruitment tests)—that exfiltrated wallets, keychains, API keys, notes, and other sensitive data. Analysis of 39 IoC domains, related IPs, and WHOIS/DNS history revealed bulk registrations, typosquatting clusters, and hundreds of infected client IPs and historical resolutions tied to malicious infrastructure. #BlueNorroff #GhostCall
Category: Threat Research
The CERT-AGID report examines risks posed by AI agents that can execute commands and interact with operating systems, showing that many dangers arise from the connector code and interfaces rather than the AI model alone. It emphasizes that prevention—through rigorous testing, secure SDK design, and integrating security into architecture from the start—is the only reliable way to keep AI systems under human control. #CERTAgID #GeminiSDK
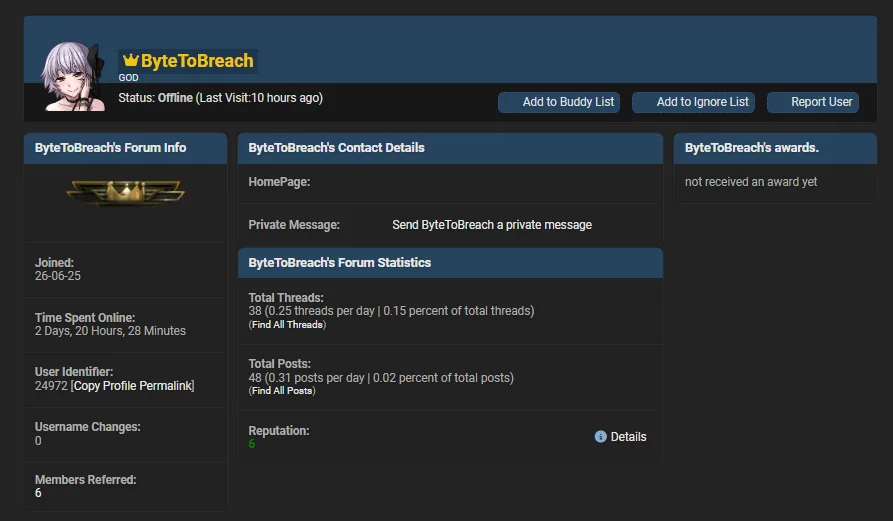
ByteToBreach is a financially motivated data‑leak trader and access broker active since mid‑2025 who sells corporate datasets and access from banks, telecoms, IT providers, and other large enterprises across multiple countries. On November 14, 2025 the actor claimed a breach of Eurofiber’s GLPI service‑management platform, exfiltrating roughly 10,000 password hashes and configuration/ticket data using rented VPS infrastructure to run time‑based SQL extraction. #ByteToBreach #Eurofiber
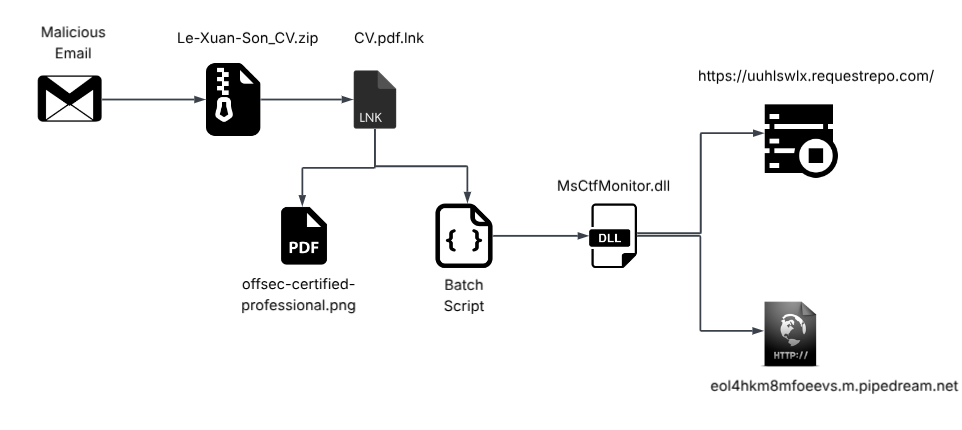
SEQRITE APT-Team identified “Operation Hanoi Thief,” a spear‑phishing campaign using fake resumes and a pseudo‑polyglot document to deliver a multi‑stage infection chain targeting Vietnamese IT and recruitment professionals. The campaign abuses trusted Windows binaries (ftp.exe, DeviceCredentialDeployment.exe, ctfmon.exe) to decode and sideload a DLL implant named LOTUSHARVEST that steals browser credentials and exfiltrates them to attacker-controlled endpoints. #LOTUSHARVEST #OperationHanoiThief
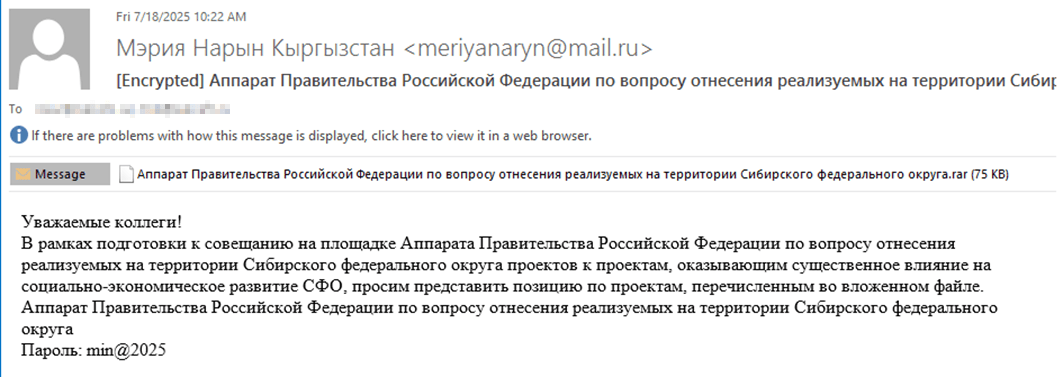
Tomiris carried out targeted phishing campaigns in early 2025 against foreign ministries, intergovernmental organizations, and government entities, deploying multi-language reverse shells and dropper implants to deliver post-exploitation frameworks such as AdaptixC2 and Havoc. The actors increasingly used public services (Discord, Telegram) as C2 channels and employed registry persistence, script-based downloaders, and reverse SOCKS proxies to maintain stealth and lateral movement. #Tomiris #AdaptixC2 #Havoc #JLORAT #Discord #Telegram

The Lazarus Group deployed a new C++ in-memory RAT called ScoringMathTea in the “Gotta Fly” phase of Operation DreamJob to target defense contractors supplying UAV technology to Ukraine. ScoringMathTea uses chained polyalphabetic string decryption, API hashing, PEB walking, full reflective DLL injection of plugins, and TEA/XTEA-CBC encrypted HTTP/S C2 with spoofed User-Agent to evade detection #ScoringMathTea #LazarusGroup

During investigation, a noisy secondary group using well-known tools (PowerShell, certutil, ADRecon, GodPotato, mimikatz, secretsdump, Rclone) conducted reconnaissance, created a local admin account, downloaded scripts from 95.142.40[.]51, and collected credentials and files, enabling early detection that likely prevented further impact. Correlation with an Angara Security report and overlap in tools and indicators led researchers to attribute the activity to Thor and note links to LockBit and Babuk. #Thor #QuietCrabs

Gainsight is investigating suspicious API activity through its Salesforce-integrated applications after Salesforce detected non-allowlisted API calls and revoked related access tokens, temporarily disabling several integrations and prompting other vendors to disable connectors. Analysis links some involved IPs to a previous UNC6040 campaign and to malware families including SmokeLoader and Vidar, underscoring supply-chain risk from trusted SaaS integrations. #Gainsight #UNC6040
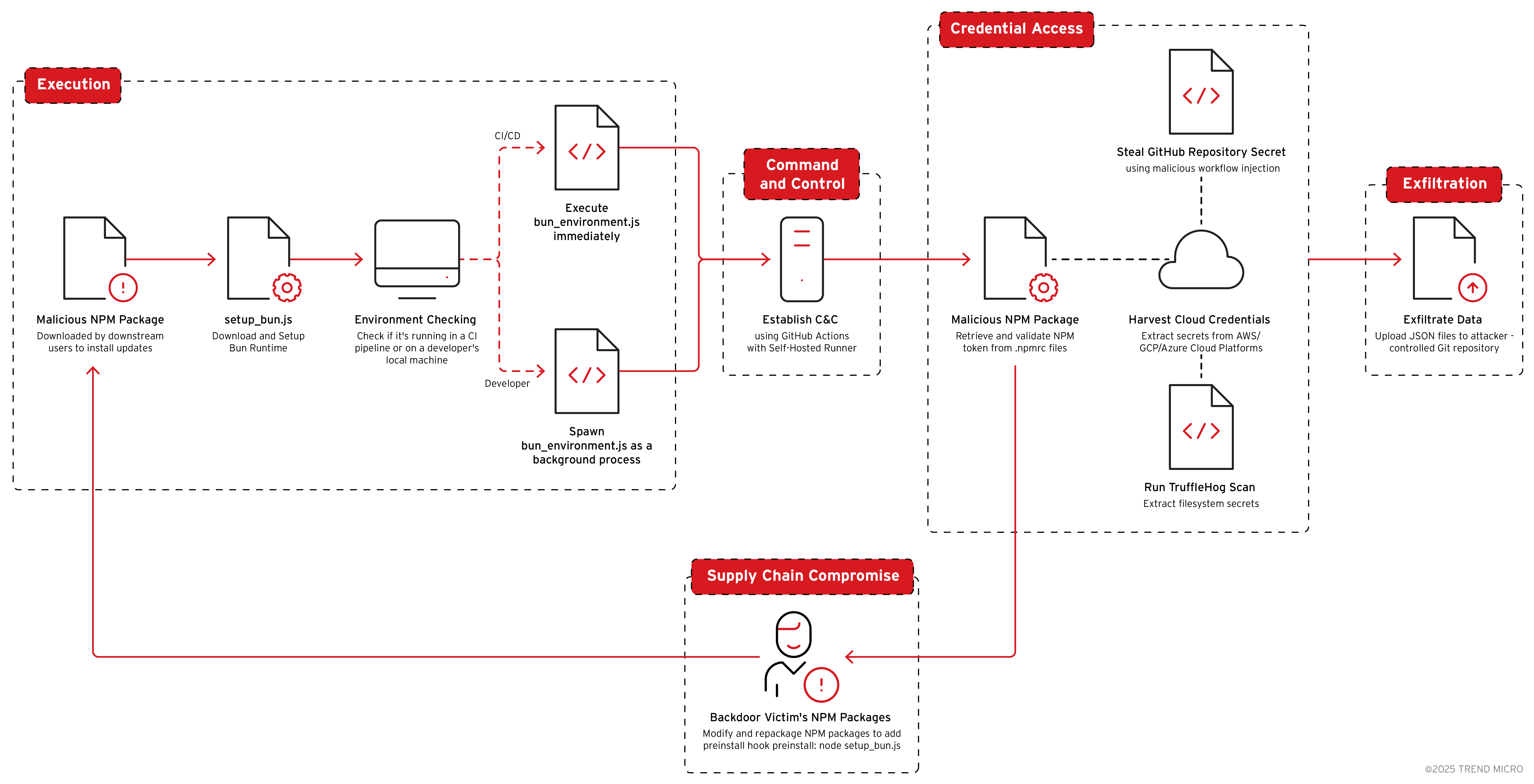
Shai-hulud 2.0 is a sophisticated NPM-supplied malware that steals credentials and secrets from AWS, GCP, Azure, GitHub, and NPM, then uses those credentials to create attacker-controlled GitHub repositories, GitHub Actions runners/workflows, and to republish backdoored NPM packages. The campaign automates worm‑like supply‑chain propagation by injecting malicious preinstall hooks (setup_bun.js → bun_environment.js)…

North Korean state-sponsored operators running the Contagious Interview campaign have injected at least 197 malicious npm packages that act as loaders to fetch OtterCookie payloads from a Vercel staging endpoint and a threat actor-controlled GitHub account. The campaign uses typosquatted utilities and polished crypto lures to deliver a multi-platform infostealer/RAT that targets developer systems and crypto wallets. #OtterCookie #ContagiousInterview

Zscaler reconstructed a multi-stage intrusion attributed to the Water Gamayun APT that used a compromised BELAY Solutions site and a lookalike domain to deliver a double-extension RAR disguised as a PDF, exploit MSC EvilTwin (CVE-2025-26633) via mmc.exe, and chain hidden PowerShell stages to deploy a final ItunesC loader. Zscaler attributed the campaign to Water Gamayun based on unique TTPs including MSC EvilTwin exploitation, nested Base64/UTF-16LE PowerShell obfuscation, trusted-binary proxy execution via mmc.exe, window-hiding tradecraft, and dual-path infrastructure patterns #WaterGamayun #CVE-2025-26633
Public administrations increasingly run phishing simulations to test staff awareness, but these exercises can be mistakenly reported to institutional CERTs and treated as real malicious campaigns, risking the inclusion of simulation indicators in operational blacklists. Applying simple technical and procedural signals—HTML comments, visible WHOIS, pre-notifying CERTs, hosting security.txt, and informing users after credential entry—reduces misclassification and helps CERTs focus on genuine threats. #CERT #security.txt
A malicious ZIP named China’s Governance of Rare Earths and its Global Implications.zip contained a password-protected PDF and a lure executable (SecurityKey.exe) that displays the PDF password and then loads shellcode to download further payloads. The loader uses PEB walking, a modified FNV API-hashing routine, wininet.dll for retrieving a payload from www.global-reia[.]com, and executes downloaded shellcode via a fiber. #SecurityKey #global-reia
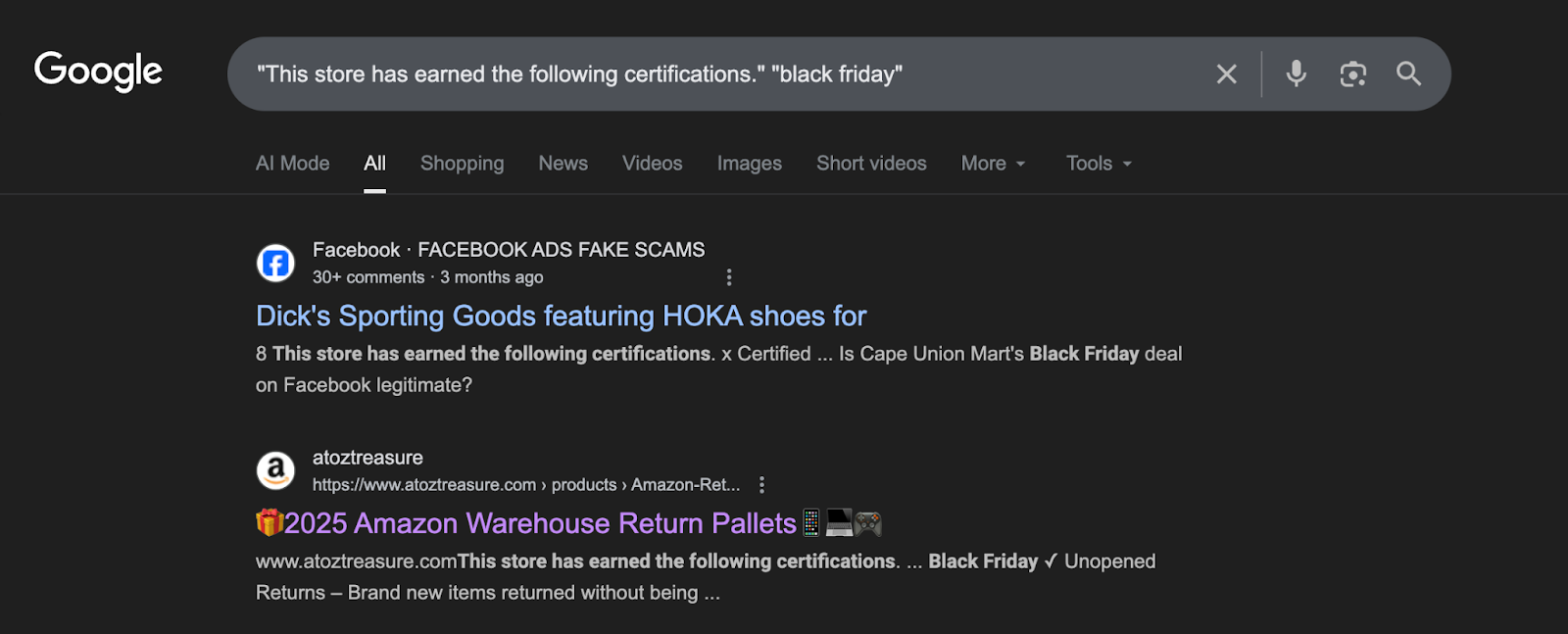
Two large, coordinated clusters of holiday-themed fake storefronts were identified: one with 750+ largely Amazon-typosquatted domains using shared CDN-hosted assets and urgency templates, and a second .shop ecosystem reusing an identical Black Friday modal and JavaScript body across many impersonating domains. These scams harvest full billing/payment details via fraudulent checkout flows and shell payment redirections to enable immediate financial theft and mass data harvesting. #Amazon #PayPal

A Kimsuky campaign delivered an obfuscated Windows Script Host JScript dropper inside an ALZ-compressed email attachment named “건강검진 안내서.alz” that displays a fake PDF while dropping and executing a DLL via rundll32. The malware uses multi-stage Base64 decoding (certutil/PowerShell), stores payloads under C:ProgramData, communicates with C2 at load.samework.o-r.kr using AES-CBC-encrypted POST bodies and a decrypted Chrome 79 user-agent, and achieves persistence via regsvr32 scheduled execution. #Kimsuky #NationalHealthInsurance