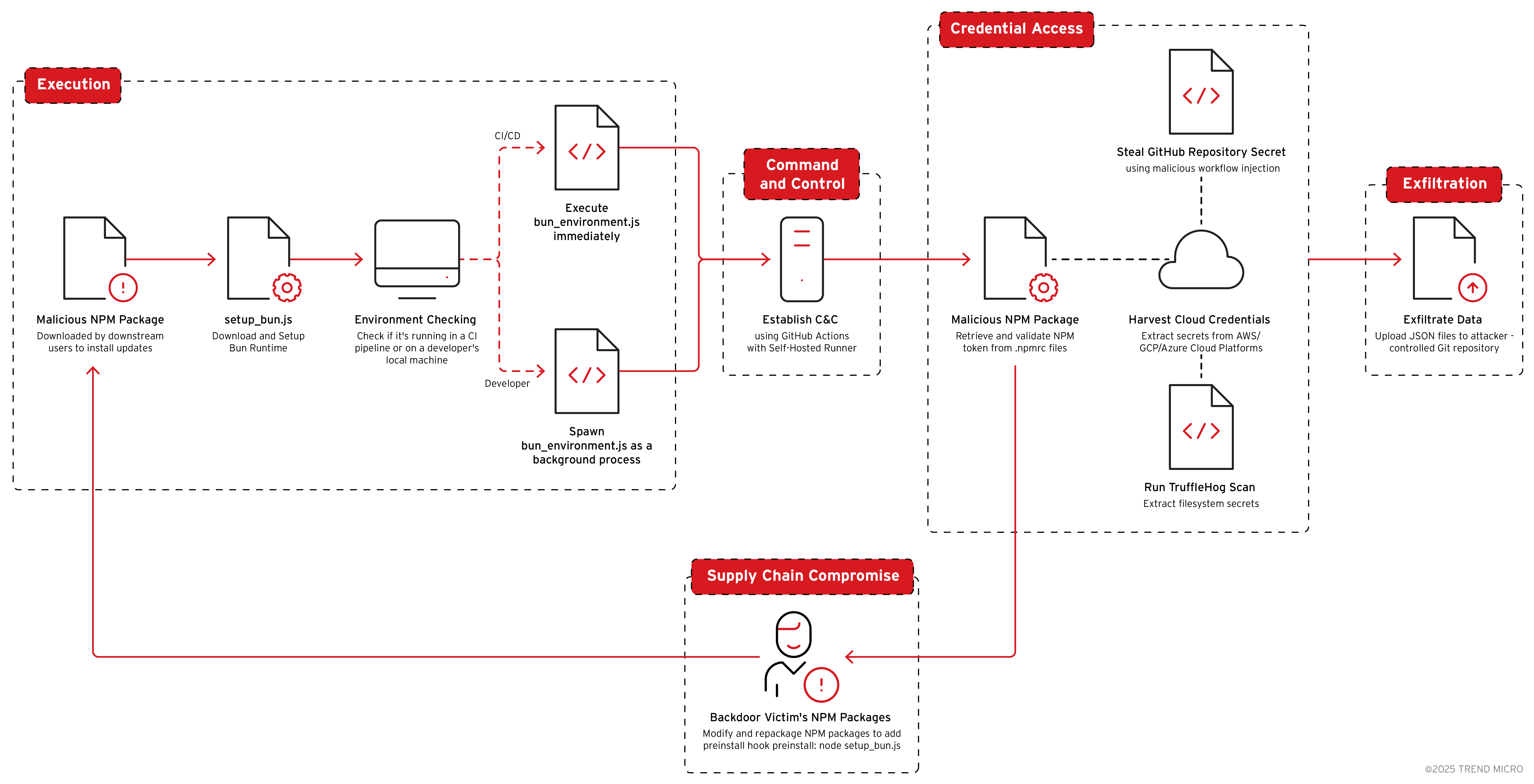
Shai-hulud 2.0 is a sophisticated NPM-supplied malware that steals credentials and secrets from AWS, GCP, Azure, GitHub, and NPM, then uses those credentials to create attacker-controlled GitHub repositories, GitHub Actions runners/workflows, and to republish backdoored NPM packages. The campaign automates worm‑like supply‑chain propagation by injecting malicious preinstall hooks (setup_bun.js → bun_environment.js) into up to 100 packages in parallel, putting thousands of downstream users at risk. #ShaiHulud #NPM
Keypoints
- Shai-hulud 2.0 extends credential theft to AWS, GCP, and Azure plus NPM tokens and GitHub credentials while adding active backdoor and republishing capabilities.
- The malware executes via an NPM preinstall hook (modified package.json with “preinstall”: “node setup_bun.js”) that ensures a Bun runtime and then runs the main payload bun_environment.js.
- It harvests credentials from environment variables, local config files (e.g., .npmrc, AWS/GCP/Azure SDK config), container metadata endpoints, and cloud secret managers (AWS Secrets Manager, GCP Secret Manager, Azure Key Vault).
- Shai-hulud creates attacker-controlled GitHub repos and deploys self-hosted runners and malicious Actions workflows (e.g., .github/workflows/discussion.yaml and a “Code Formatter” push-trigger) to serve as C2 and to exfiltrate repository secrets.
- The malware automatically enumerates and repackages up to 100 NPM packages maintained by a compromised account—injecting preinstall hooks and republishing using the victim’s NPM token to maximize downstream impact.
- If credential harvesting fails, the payload includes destructive fallback behavior that attempts to wipe user files; Trend Vision One provides detections, hunting queries, and IOC coverage for this campaign.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Shai-hulud uses Node.js scripts executed during NPM install to run its loader and payload (‘modified package.json with “preinstall”: “node setup_bun.js”‘).
- [T1552.001] Credentials in Files – the malware extracts authentication tokens and credentials from local config files (e.g., .npmrc) and environment variables (‘searches for .NPMrc configuration files…extract NPM authentication tokens’).
- [T1078] Valid Accounts – stolen NPM and GitHub tokens are used as valid credentials to publish backdoored packages and create attacker-controlled repositories (‘publishes modified packages… using the victim’s NPM authentication token’ and ‘createRepo() function uses the GitHub Octokit API’).
- [T1195] Supply Chain Compromise – the campaign backdoors and republishes NPM packages maintained by victims to propagate malicious payloads downstream (‘automatically backdoors every NPM package maintained by the victim, republishing them with malicious payloads’).
- [T1567] Exfiltration Over Web Service – stolen data and secrets are aggregated into JSON files and uploaded to an attacker-controlled GitHub repository and workflow artifacts for exfiltration (‘aggregates and uploads four distinct categories of stolen data to an attacker-controlled Git repository’).
- [T1566] Phishing – the initial compromise vector included a targeted phishing campaign used to gain access to an NPM package maintainer account (‘highly targeted phishing campaign to compromise the account of an NPM package maintainer’).
Indicators of Compromise
- [File names] Loader and payload – setup_bun.js, bun_environment.js (loader and main malware payload executed via NPM preinstall).
- [Repository/workflow artifacts] Attacker-controlled GitHub repo and workflow files – repository description “Sha1-Hulud: The Second Coming.”, runner name/SHA1HULUD, and workflow path .github/workflows/discussion.yaml (used for C2 and artifact exfiltration).
- [NPM metadata / scripts] Malicious package.json entries and branch pattern – preinstall entry “preinstall”: “node setup_bun.js” and temporary branch naming add-linter-workflow-{timestamp} (used for stealthy workflow injection).
- [Artifact & exfiltrated filenames] Exfiltration artifacts and JSON files – artifact name “formatting” containing format.json, and created upload files contents.json, environment.json, cloud.json, truffleSecrets.json (contain stolen metadata, env vars, cloud secrets, and TruffleHog results).
- [Domains / API endpoints] Installer and tooling endpoints – bun.sh (official Bun installer used by the loader), GitHub API endpoints (e.g., repos.createForAuthenticatedUser, /actions/runners/registration-token), and the unauthenticated releases endpoint /repos/trufflesecurity/trufflehog/releases/latest (used to fetch TruffleHog).