Tomiris carried out targeted phishing campaigns in early 2025 against foreign ministries, intergovernmental organizations, and government entities, deploying multi-language reverse shells and dropper implants to deliver post-exploitation frameworks such as AdaptixC2 and Havoc. The actors increasingly used public services (Discord, Telegram) as C2 channels and employed registry persistence, script-based downloaders, and reverse SOCKS proxies to maintain stealth and lateral movement. #Tomiris #AdaptixC2 #Havoc #JLORAT #Discord #Telegram
Keypoints
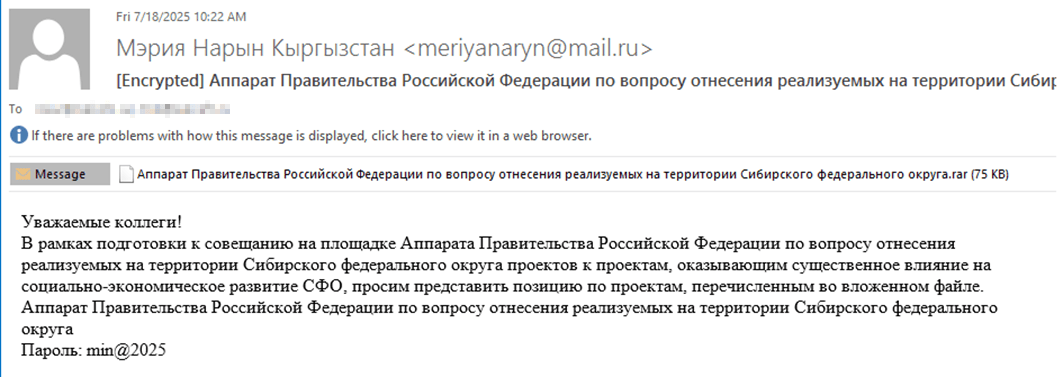
- Initial access was achieved via spear-phishing with password-protected archives containing executables disguised with double extensions or long filenames to hide the .exe extension.
- Multiple first-stage reverse shells and downloaders were observed in Go, Rust, C/C#/C++, and Python that performed reconnaissance and fetched next-stage payloads.
- Public messaging platforms (Discord webhooks and Telegram bots) were abused as C2 channels for multiple implants, including Python-based reverse shells and file grabbers.
- Operators frequently downloaded and deployed open-source post-exploitation frameworks AdaptixC2 and Havoc using built-in OS utilities (bitsadmin, curl, certutil, PowerShell) and registered them for persistence in HKCU Run keys.
- Data collection routines targeted common document and image file types; some tools sent file path listings or archived files to C2 servers via multipart HTTP requests or direct POSTs.
- Reverse SOCKS proxy implants (Go/C++) were hosted on infrastructure used by the campaign, likely to proxy scanner/traffic and enable lateral movement.
- Attribution to Tomiris is supported by consistent patterns: long specific filenames, password format like “xyz@2025”, reuse of tool names (JLORAT), and overlapping hashes and infrastructure.
MITRE Techniques
- [T1566.001] Spearphishing Attachment – Initial access via malicious archives delivered by phishing emails: (‘The infection begins with a phishing email containing a malicious archive.’)
- [T1204.002] User Executed Malicious File – Execution of executables dropped from archives (often disguised with double extensions or long names) leading to compromise: (‘Inside the archive is an executable file… the file name includes a double extension such as .doc.exe.’)
- [T1105] Ingress Tool Transfer – Downloading of next-stage implants and frameworks using built-in utilities: (‘bitsadmin /transfer …’, ‘curl -o …’, ‘certutil -urlcache -f …’, ‘powershell.exe -Command “Invoke-WebRequest -Uri … -OutFile …”‘)
- [T1059] Command and Scripting Interpreter – Use of PowerShell, cmd and scripted loops to execute downloaders and payloads: (‘powershell -ExecutionPolicy Bypass -WindowStyle Hidden -EncodedCommand …’, script.ps1 infinite loop invoking Invoke-WebRequest’)
- [T1547.001] Registry Run Keys / Startup Folder – Establishing persistence by adding downloaded implants to HKCUSoftwareMicrosoftWindowsCurrentVersionRun: (‘reg add HKCUSoftwareMicrosoftWindowsCurrentVersionRun /v WinUpdate /t REG_SZ /d $publicpictureswinupdate.exe /f’)
- [T1071.001] Application Layer Protocol – C2 communications over legitimate application-layer services (Discord, Telegram) to blend traffic: (‘some of the implants use Telegram and Discord to communicate with a C2; … a multipart POST request … to Discord via the URL’)
- [T1005] Data from Local System – Collection of local files and file path listings by downloaders/filegrabbers (targeting .jpg/.png/.pdf/.docx etc.): (‘The Trojan is interested in files with the following extensions: .jpg, .jpeg, .png, .txt, .rtf, .pdf, .xlsx, and .docx.’)
- [T1567.002] Exfiltration Over Web Service – Sending collected system info and file lists via HTTP multipart POSTs to Discord webhooks and other web endpoints: (‘A multipart POST request is used to send the collected system information and the list of discovered file paths to Discord via the URL’)
- [T1090] Proxy – Use of reverse SOCKS proxy implants to proxy traffic and facilitate lateral movement and scanning: (‘reverse SOCKS proxy implants … likely used to proxy traffic from vulnerability scanners and enable lateral movement within the network.’)
- [T1027] Obfuscated Files or Information – Use of obfuscation (PyArmor, Base64-encoded PowerShell) to hinder analysis and detection: (‘the main script is also obfuscated with PyArmor’, ‘extracts a Base64-encoded PowerShell script from itself’)
Indicators of Compromise
- [File Hash ] Samples of detected implants – Distopia Backdoor: B8FE3A0AD6B64F370DB2EA1E743C84BB, Tomiris Python Discord ReverseShell: 091FBACD889FA390DC76BB24C2013B59 (and many more hashes)
- [Domains / Webhooks ] C2 endpoints and webhook URLs – Discord webhook example: hxxps://discordapp[.]com/api/webhooks/1392383639450423359/TmFw-WY-…, Telegram bot API example: hxxps://api.telegram[.]org/bot7562800307:AAHVB7Ctr-…/ (and additional webhook/bot URLs)
- [IP Addresses ] Infrastructure used for hosting and direct connections – Go ReverseShell TCP target: 62.113.114[.]209:443; downloader host used in script.ps1: 193.149.129[.]113 (and other IPs such as 78.128.112[.]209 for Havoc)
- [URLs / Malicious Download URLs ] Malicious download links observed in scripts and commands – example: hxxp://193.149.129[.]113/ (used by script.ps1 to fetch 1.zip), hxxp://62.113.115[.]89/homepage/infile.php (FileGrabber) and many other URLs listed as download hosts
- [File Names ] Lures and decoy filenames used in spear-phishing archives – Russian-language decoy example: “аппарат правительства российской федерации по вопросу …*.exe” and “план-протокол встречи о сотрудничестве представителей*.exe” (same names used to distribute multiple different implants)