BlueNorroff targeted tech executives, venture capitalists, and Web3 developers with two interrelated campaigns—GhostCall (macOS-focused via malicious Zoom updates) and GhostHire (GitHub-based malware disguised as recruitment tests)—that exfiltrated wallets, keychains, API keys, notes, and other sensitive data. Analysis of 39 IoC domains, related IPs, and WHOIS/DNS history revealed bulk registrations, typosquatting clusters, and hundreds of infected client IPs and historical resolutions tied to malicious infrastructure. #BlueNorroff #GhostCall
Keypoints
- BlueNorroff ran two coordinated campaigns—GhostCall (targeting macOS via fake Zoom updates) and GhostHire (malicious GitHub repos used as recruitment tests)—to harvest credentials and sensitive files.
- Victims were socially engineered over Telegram and similar platforms and persuaded to run a malicious Zoom update script or execute code from a GitHub repository.
- Stolen data included crypto wallet information, keychain data, package manager and infrastructure configurations, OpenAI API keys, collaboration app data, and credentials from browsers and messengers.
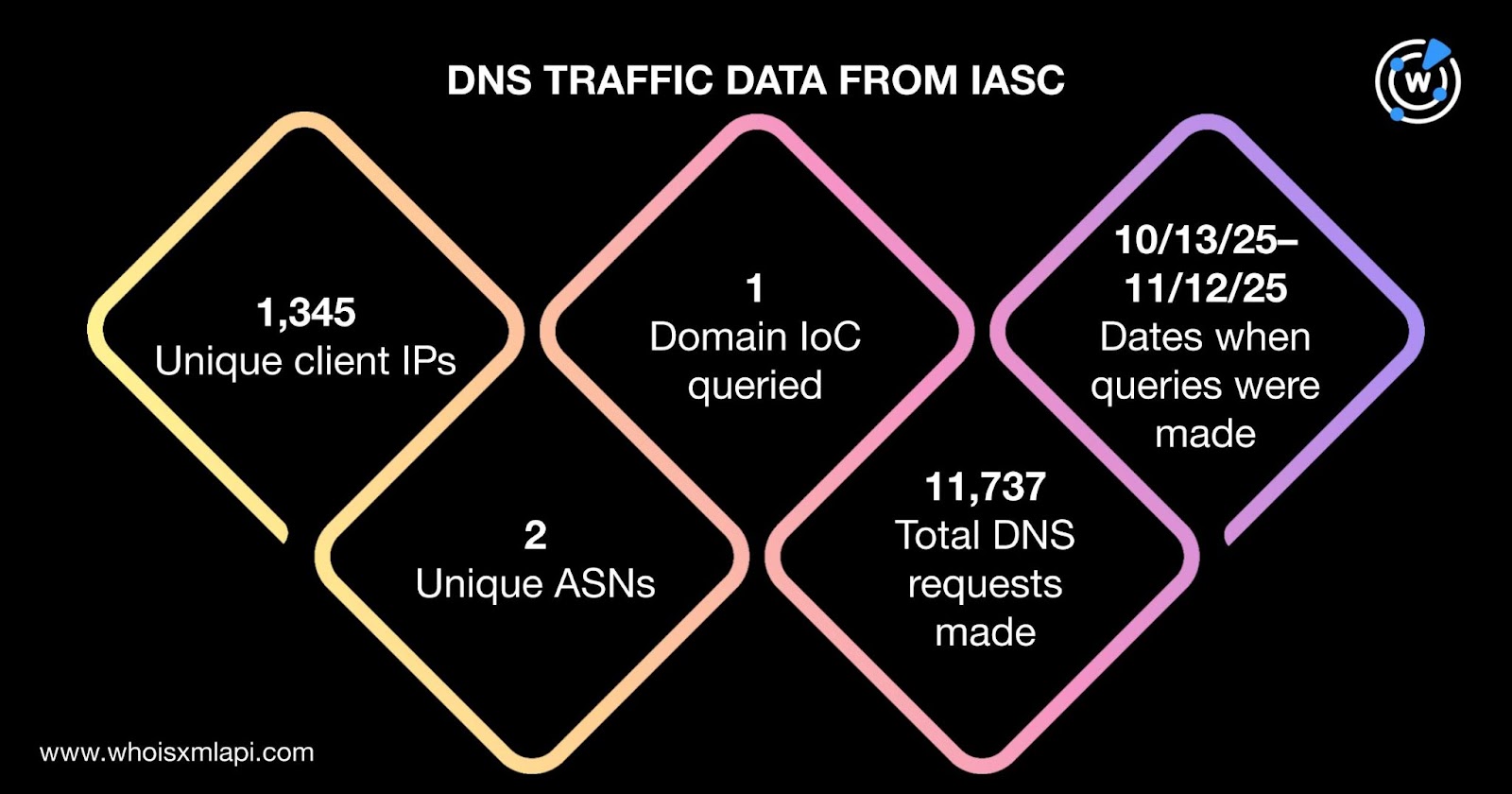
- Securelist and WhoisXML API analysis identified 39 IOC domains; further enrichment found 1,345 unique client IPs communicating with those domains and 11,737 DNS requests in a one-month period.
- Threat intelligence queries flagged multiple domains and IPs as malicious or likely-to-turn-malicious well before October 28, 2025, and revealed typosquatting groups and bulk-registrations across many IoCs.
- Infrastructure analysis showed 24 active IPs (17 likely dedicated hosts) distributed across U.S., Netherlands, and France, hosted by providers including Hostwinds, Linode, Amazon, and Google Cloud.
MITRE Techniques
- [T1566 ] Phishing – Actors lured targets via messaging platforms: (‘They approached victims on Telegram and similar platforms, luring them with potential investments.’)
- [T1204 ] User Execution – Victims were tricked into running a malicious Zoom update script: (‘once the call ensued, they were tricked into updating Zoom with a malicious script that downloaded a malicious ZIP file.’)
- [T1059 ] Command and Scripting Interpreter – Attackers delivered and executed scripts/repos to run malware: (‘downloading and executing a GitHub repository containing malware disguised as a skill assessment test for recruitment’ / ‘malicious script that downloaded a malicious ZIP file.’)
- [T1555 ] Credentials from Password Stores – The campaigns extracted stored credentials and key material: (‘they lost secret files, including crypto wallet information, keychain data…credentials stored in browsers, messengers, and Telegram.’)
- [T1005 ] Data from Local System – Sensitive local files and media were collected and exfiltrated: (‘stole sensitive information, including videos and profile images’ and ‘victims lost … notes, API keys for OpenAI, collaboration application data’).
- [T1195 ] Supply Chain Compromise – Malware was distributed via a trusted developer channel (GitHub) masquerading as recruitment material: (‘downloading and executing a GitHub repository containing malware disguised as a skill assessment test for recruitment.’)
- [T1583 ] Acquire Infrastructure – Attackers used and registered extensive domain infrastructure (39 IoCs) and bulk-registered/typosquatted domains to support operations: (‘shared the same infrastructure and identified 39 domains as IoCs’ / ‘six domains identified as IoCs were bulk-registered with two look-alike domains each’).
- [T1071 ] Application Layer Protocol – Command and control activity observed on IPs tied to IoCs: (‘Command and control (C&C)’) as listed in threat intelligence for several IP addresses.
Indicators of Compromise
- [Domain ] Malicious and suspicious domains used as infrastructure and lures – autoupdate[.]online, system-update[.]xyz, and 37 other domains from the 39 identified IoCs.
- [IP address ] Active/resolving IPs tied to IoCs and weaponized for distribution/C&C – 13.248.169.48, 76.223.54.146, and 22 other IPs (24 total IPs referenced).
- [Typosquatting / Look‑alike domains ] Bulk-registered look-alikes used to mask malicious sites – flashstore[.]sbs, ms-live[.]us, and other domains in five typosquatting groups.
- [Email-connected domains ] Domains that appeared in historical WHOIS emails and were linked to malicious activity – sidezoom[.]us (used to distribute malware) and other email-connected domains (three of four were flagged malicious).
- [File artifacts / repositories ] Malware delivery artifacts referenced in analysis – a malicious ZIP file from a fake Zoom update and a GitHub repository posing as a skill assessment (samples available for download from the analyst site).
Read more: https://circleid.com/posts/going-dns-deep-diving-into-ghostcall-and-ghosthire