NTLM remains widely present in modern Windows environments and continues to be exploited through both long-standing and newly disclosed vulnerabilities that leak authentication hashes and enable relay/reflection attacks. Notable 2024–2025 flaws (CVE-2024-43451, CVE-2025-24054/24071, CVE-2025-33073) have been weaponized by groups such as BlindEagle and Head Mare to deliver Remcos, PhantomCore, and AveMaria, prompting recommendations to disable/limit NTLM, enable signing and EPA, and monitor NTLM traffic. #Remcos #BlindEagle
Keypoints
- NTLM authentication—despite being deprecated—remains enabled across many Windows systems and is actively exploited in 2024–2025 campaigns.
- Several high-impact CVEs (notably CVE-2024-43451, CVE-2025-24054/24071, CVE-2025-33073) allow NTLMv2 hash leakage or NTLM reflection with little or no user interaction.
- Adversaries (BlindEagle, Head Mare) have used crafted .url and .library-ms files delivered via phishing ZIP attachments to trigger automatic NTLM authentication and deliver RATs such as Remcos and AveMaria.
- Common attack techniques include hash leakage, coercion-based attacks (e.g., PetitPotam/PrinterBug), NTLM relay/reflection, pass-the-hash, lateral movement (Impacket, PsExec, WMIExec), and LSASS dumping (rundll32/comsvcs, custom DLLs, PowerShell minidumps).
- CVE-2024-43451 and related flaws exploit legacy components (MSHTML, WebDAV handling) to force network authentication and, in some cases, automatic download/execution of payloads from attacker-controlled servers.
- Mitigations recommended: disable or limit NTLM, enable SMB/LDAP signing, enable Extended Protection for Authentication (EPA), enforce patching, and actively monitor/audit NTLM authentication logs.
MITRE Techniques
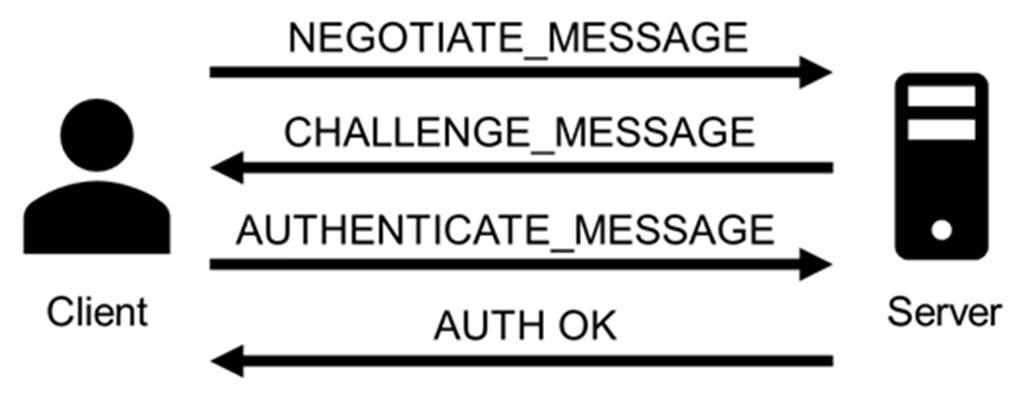
- [T1557.001 ] LLMNR/NBT-NS Poisoning and SMB Relay – NTLM relay and reflection attacks are used to intercept or coerce authentication; (‘NTLM relay remains the most enduring and impactful method… tools include Responder, Impacket’s NTLMRelayX, and Inveigh’)
- [T1550.002 ] Pass the Hash – Captured NTLMv2 hashes are reused to impersonate users and access remote systems; (‘they can execute a pass-the-hash attack (e.g. by using tools like WMIExec or PSExec) to gain network access by impersonating a valid user’)
- [T1566.001 ] Spearphishing Attachment – Phishing emails deliver .url or ZIP attachments that trigger NTLM authentication and payload retrieval; (‘These files were delivered through phishing emails impersonating Colombian government and judicial entities’)
- [T1204.002 ] User Execution: Malicious File – Minimal interactions (preview, single-click, right-click, move) with crafted .url/.library-ms files trigger automatic authentication and sometimes automatic download/execution; (‘a minimal interaction with the malicious file, such as a single click or a right click, triggers automatic connection to the server, file download, and execution’)
- [T1134 ] Access Token Manipulation – NTLM reflection/local relay is used to coerce a host into authenticating to itself and obtain a SYSTEM token for privilege escalation; (‘an attacker can trick the system into believing the authentication request originates from the same host… the injected token is handled as if it were trusted’)
- [T1003.001 ] Credential Dumping: LSASS Memory – Attackers dump LSASS memory using comsvcs.dll, custom DLLs, or PowerShell to extract credentials post-compromise; (‘…invokes an internal function of comsvcs.dll to dump LSASS memory and save it’ and ‘The script leverages MiniDumpWriteDump via reflection’)
- [T1543.003 ] Create or Modify System Process: Windows Service – Persistence is established by creating service entries in the registry after escalation; (‘Persistence was then established by creating a suspicious service entry in the registry under: reg:REGISTRYMACHINESYSTEMControlSet001ServicesYlHXQbXO’)
- [T1021.002 ] Remote Services: SMB/Windows Admin Shares – Lateral movement attempts use administrative shares and remote-execution tools (PsExec, SMBExec) to move across hosts; (‘the attacker attempted lateral movement by writing to the administrative share of another host’)
- [T1021.006 ] Remote Services: WMI – Tools like wmiexec.py are used to execute commands or move laterally using WMI-based remote execution; (‘tools like Mimikatz allow extraction and injection of NTLM hashes… Impacket’s wmiexec.py, PsExec.py, and secretsdump.py can be used to perform remote execution’)
- [T1059.001 ] Command and Scripting Interpreter: PowerShell – Base64-encoded PowerShell was used to run reflective minidump routines to dump process memory; (‘The script leverages MiniDumpWriteDump via reflection. It uses the Out-Minidump function that writes a process dump with all process memory to disk’)
Indicators of Compromise
- [IP address ] attacker infrastructure and payload hosting – 45.87.246.40 (used by Head Mare), 185.227.82.72 (hosting AveMaria), and other infrastructure addresses
- [Domain ] malicious WebDAV/SMB download hosts – document-file[.]ru (document-file[.]ru/files/documents/zakupki/MicrosoftWord.exe) and other attacker-controlled domains
- [File name / extension ] crafted initial droppers and payloads – .url files (e.g., “Сопроводительное письмо.docx” used as a .url), .library-ms files, and MicrosoftWord.exe delivered via UNC/WebDAV
- [Hostname ] manipulated hostnames used in reflection attacks – localhost1UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA (crafted to coerce local authentication)
- [CVE ] vulnerabilities exploited as initial vectors – CVE-2024-43451, CVE-2025-24054 (consolidated with CVE-2025-24071), CVE-2025-33073
- [Malware / Tools ] observed payloads and tooling – Remcos RAT, PhantomCore, AveMaria (Warzone), Mimikatz, Impacket tools (wmiexec.py, smbexec, secretsdump.py)
- [Registry / Service ] persistence indicators – reg:REGISTRYMACHINESYSTEMControlSet001ServicesYlHXQbXO (suspicious service entry created by attacker)
Read more: https://securelist.com/ntlm-abuse-in-2025/118132/