watchTowr Labs discovered a critical FortiWeb vulnerability chain allowing path traversal to reach the fwbcgi CGI and an authentication bypass via a Base64-encoded HTTP_CGIINFO header that permits full admin impersonation. Exploitation enables creation of persistent admin accounts on affected FortiWeb appliances and has been assigned CVE-2025-64446; #FortiWeb #CVE-2025-64446
Keypoints
- Researchers observed requests that traverse the FortiWeb API path to the fwbcgi CGI (e.g., GET/POST to /api/v2.0/cmdb/system/admin/../../../../../cgi-bin/fwbcgi), indicating a path traversal vulnerability.
- The fwbcgi binary performs minimal input validation (cgi_inputcheck) and accepts any valid JSON body, allowing easy bypass of that check.
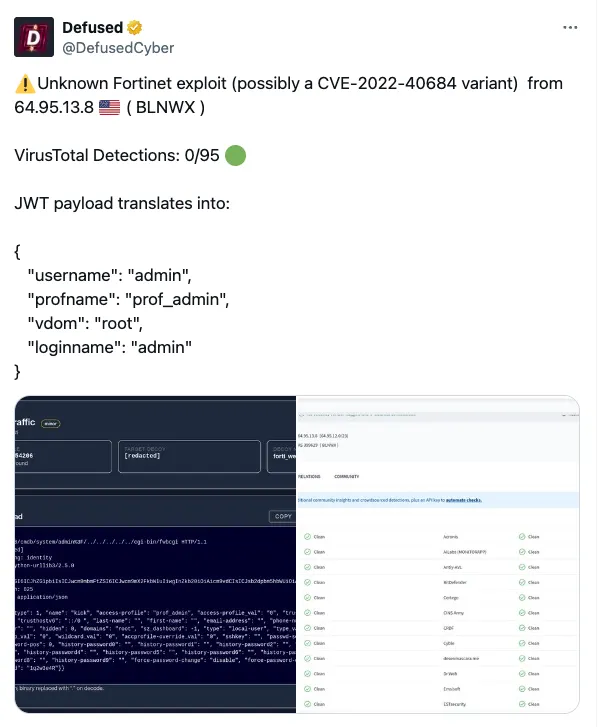
- The CGI processes a Base64-decoded HTTP_CGIINFO header as JSON and uses extracted fields (username, profname, vdom, loginname) to set the login context, enabling impersonation of arbitrary users including built-in admin.
- With impersonation achieved, attackers can execute cgi_process() actions, demonstrated by creating a new administrative local user (example: watchTowr/watchTowr) as persistence.
- Multiple FortiWeb and Fortinet versions are listed as affected; Fortinet later released an advisory assigning CVE-2025-64446 and some versions (e.g., 8.0.2) appear to be patched.
- watchTowr released a Detection Artefact Generator and proof-of-concept resources on GitHub to help defenders identify vulnerable hosts.
MITRE Techniques
- [T1190 ] Exploit Public-Facing Application – Used to reach the fwbcgi CGI via a crafted API path traversal that targets the FortiWeb public-facing interface (‘GET /api/v2.0/cmdb/system/admin/../../../../../cgi-bin/fwbcgi HTTP/1.1’).
- [T1078 ] Valid Accounts – The attack impersonates legitimate users (including built-in admin) by supplying crafted credentials in the HTTP_CGIINFO header so the appliance treats the request as authenticated (‘by supplying a handcrafted HTTP_CGIINFO header, an attacker can impersonate any user, including the built-in admin, and inherit their full privileges’).
- [T1136 ] Create Account – After impersonation, the attacker creates a persistent administrative local user via cgi_process(), exemplified by the payload that creates user “watchTowr” with admin privileges (‘the following payload instructs the appliance to create a new local user named watchTowr with the password watchTowr and administrative privileges’).
- [T1132 ] Data Encoding – The exploit encodes a JSON object in Base64 and places it in the HTTP_CGIINFO header to convey impersonation attributes (‘Base64-encode this JSON’).
Indicators of Compromise
- [HTTP Request URI ] Evidence of exploitation attempts – ‘POST /api/v2.0/cmdb/system/admin%3F/../.. ../../../cgi-bin/fwbcgi’, ‘GET /api/v2.0/cmdb/system/admin/../../../../../cgi-bin/fwbcgi HTTP/1.1’.
- [HTTP Header / Encoded JSON ] Impersonation artifact – Base64-encoded HTTP_CGIINFO containing JSON like {“username”:”admin”,”profname”:”super_admin”,”vdom”:”root”,”loginname”:”admin”} and Base64-encoded payloads used to set admin context.
- [File / Binary ] Targeted executable – fwbcgi (the CGI binary invoked by the traversed URI) and references to /var/log/inputcheck/*.json used by cgi_inputcheck().
- [Account credentials / Payloads ] Persistence evidence – example local user creation payload that creates “watchTowr” with password “watchTowr”, and example password in observed request body “AFodIUU3Sszp5”.
- [Advisory / CVE ] Tracking identifier and resources – CVE-2025-64446 and the detection tool repository https://github.com/watchtowrlabs/watchTowr-vs-Fortiweb-AuthBypass.
- [Affected Versions ] Vulnerable software versions – examples include 8.0