ESET analyzed PlushDaemon’s use of a MIPS32 network implant named EdgeStepper that forwards DNS queries to attacker-controlled nodes to hijack legitimate software updates and deliver downloaders that deploy the SlowStepper backdoor. The report also details LittleDaemon and DaemonicLogistics — two Windows downloaders used in the update-hijacking chain — and provides IoCs including files, domains, and IPs. #EdgeStepper #SlowStepper
Keypoints
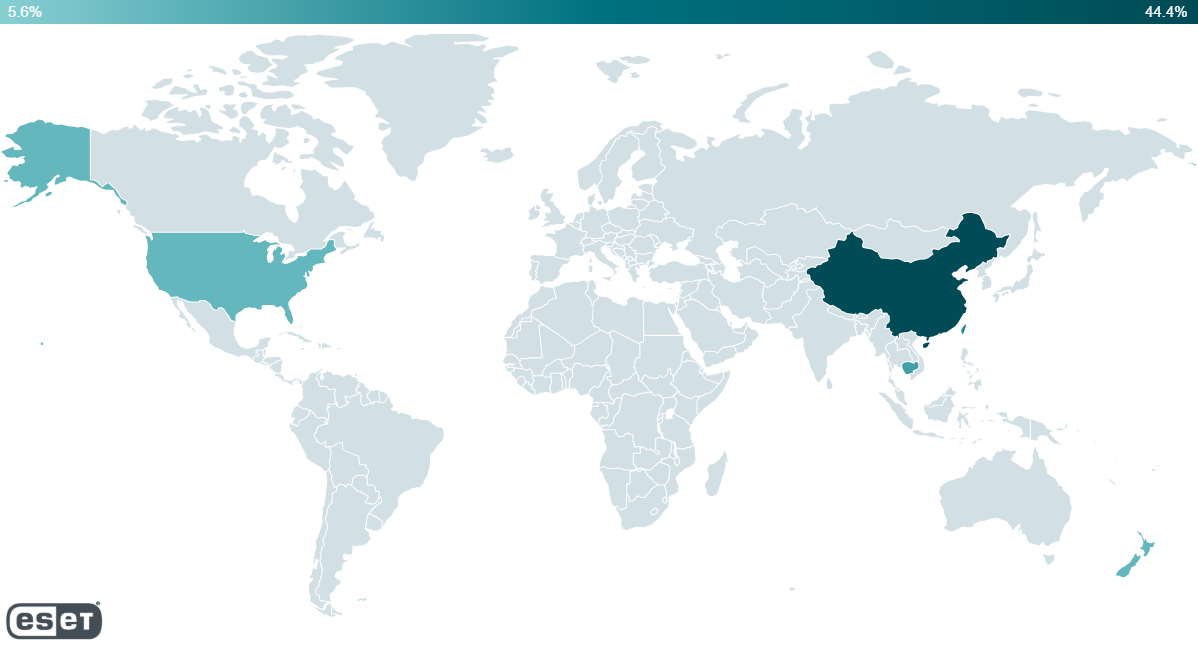
- PlushDaemon is a China-aligned espionage actor active since at least 2018 that hijacks software updates to deliver its SlowStepper backdoor across multiple countries.
- EdgeStepper (dns_cheat_v2) is a Go-based MIPS32 network implant that proxies and redirects DNS queries from compromised network devices to attacker-controlled DNS/hijacking nodes.
- EdgeStepper deploys iptables rules to redirect UDP/53 traffic to a local port (default 1090) and forwards DNS requests to malicious nodes that return hijack IPs for update domains.
- Hijacked update flows cause legitimate update clients (example: Sogou Pinyin) to fetch malicious DLLs such as LittleDaemon served by the hijacking node instead of vendor infrastructure.
- LittleDaemon (DLL/EXE) checks for SlowStepper, contacts the hijacking node or legitimate domains redirected by EdgeStepper, downloads and decrypts DaemonicLogistics, then executes it in memory.
- DaemonicLogistics is position-independent code that interprets HTTP status codes as commands, downloads encrypted payloads (SlowStepper) disguised as ZIP/GIF files, and writes/decrypts them to specific paths.
- ESET provides file hashes, domains, and IP addresses linked to EdgeStepper and the hijacking infrastructure, and notes persistence is performed by the SlowStepper implant rather than LittleDaemon.
MITRE Techniques
- [T1583.001 ] Acquire Infrastructure: Domains – PlushDaemon uses EdgeStepper to redirect traffic to specific subdomains that are part of PlushDaemon’s infrastructure on wcsset[.]com. Quote: ‘PlushDaemon uses EdgeStepper to redirect traffic to specific subdomains that are part of PlushDaemon’s infrastructure on wcsset[.]com.’
- [T1583.002 ] Acquire Infrastructure: DNS Server – Part of the PlushDaemon infrastructure is used to host its malicious DNS nodes. Quote: ‘Part of the PlushDaemon infrastructure is used to host its malicious DNS nodes.’
- [T1583.004 ] Acquire Infrastructure: Server – PlushDaemon has acquired servers to host its DNS/hijacking nodes and C&C servers. Quote: ‘PlushDaemon has acquired servers to host its DNS/hijacking nodes and C&C servers.’
- [T1608.001 ] Stage Capabilities: Upload Malware – PlushDaemon hosts its payloads on DNS/hijacking servers. Quote: ‘PlushDaemon hosts its payloads on DNS/hijacking servers.’
- [T1659 ] Content Injection – Hijacking nodes from PlushDaemon process hijacked traffic and reply to legitimate software with instructions to download malware such as LittleDaemon. Quote: ‘Hijacking nodes from PlushDaemon process hijacked traffic and reply to legitimate software with instructions to download malware such as LittleDaemon.’
- [T1106 ] Native API – DaemonicLogistics executes the SlowStepper implant using the ShellExecute API. Quote: ‘DaemonicLogistics executes the SlowStepper implant using the ShellExecute API.’
- [T1070.004 ] Indicator Removal: File Deletion – Some variants of LittleDaemon can remove themselves. Quote: ‘Some variants of LittleDaemon can remove themselves.’
- [T1036.005 ] Masquerading: Match Legitimate Name or Location – DaemonicLogistics creates a subdirectory named Tencent, where it stores its files. Quote: ‘DaemonicLogistics creates a subdirectory named Tencent, where it stores its files.’
- [T1036.008 ] Masquerading: Masquerade File Type – DaemonicLogistics and SlowStepper’s loader can decrypt files that masquerade as ZIP and GIF files. Quote: ‘DaemonicLogistics and SlowStepper’s loader can decrypt files that masquerade as ZIP and GIF files.’
- [T1027.009 ] Obfuscated Files or Information: Embedded Payloads – Files masquerading as ZIPs and GIF files contain embedded encrypted components. Quote: ‘Files masquerading as ZIPs and GIF files contain embedded encrypted components.’
- [T1027.013 ] Obfuscated Files or Information: Encrypted/Encoded File – Components of the SlowStepper implant are encrypted on disk. Quote: ‘Components of the SlowStepper implant are encrypted on disk.’
- [T1518.001 ] Software Discovery: Security Software Discovery – DaemonicLogistics checks for the presence of 360tray.exe – a component of 360 Total Security. Quote: ‘DaemonicLogistics checks for the presence of 360tray.exe – a component of 360 Total Security.’
- [T1016 ] System Network Configuration Discovery – DaemonicLogistics attempts to obtain the ethernet or Wi‑Fi adapter’s MAC address. Quote: ‘DaemonicLogistics attempts to obtain the ethernet or Wi‑Fi adapter’s MAC address.’
- [T1057 ] Process Discovery – DaemonicLogistics lists processes. Quote: ‘DaemonicLogistics lists processes.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – LittleDaemon and DaemonicLogistics use HTTP to communicate with their server. Quote: ‘LittleDaemon and DaemonicLogistics use HTTP to communicate with their server.’
- [T1573 ] Encrypted Channel – LittleDaemon downloads via HTTP the encrypted DaemonicLogistics that downloads via HTTP the encrypted SlowStepper implant. Quote: ‘LittleDaemon downloads via HTTP the encrypted DaemonicLogistics that downloads via HTTP the encrypted SlowStepper implant.’
- [T1665 ] Hide Infrastructure – LittleDaemon and DaemonicLogistics make downloads by sending HTTP requests to legitimate domains. Quote: ‘LittleDaemon and DaemonicLogistics make downloads by sending HTTP requests to legitimate domains.’
Indicators of Compromise
- [File Hash ] EdgeStepper and configs – 8F569641691ECB3888CD4C11932A5B8E13F04B07 (bioset, EdgeStepper), 06177810D61A69F34091CC9689B813740D4C260F (bioset.conf).
- [File Hash ] LittleDaemon binaries – 69974455D8C13C5D57C1EE91E147FF9AED49AEBC (popup_4.2.0.2246.dll), 2857BC730952682D39F426D185769938E839A125 (sogou_wubi_15.4.0.2508_0000.exe).
- [Domain ] Hijacking/DNS nodes – ds20221202.dsc.wcsset[.]com (associated with 8.212.132[.]120), test.dsc.wcsset[.]com (associated with 47.242.198[.]250).
- [IP Address ] Hosting/hijack nodes – 8.212.132[.]120 (DNS/Hijacking node), 47.242.198[.]250 (DNS/Hijacking node observed 2021–2022).
- [File paths/filenames ] Deployed payload paths and names – %PROGRAMDATA%TencentQQUpdateMgrUpdateFileslogo.gif (written by DaemonicLogistics), plugin.exe and files like popup_4.2.0.2246.dll used as LittleDaemon copies.