K7 Labs analyzed a Python-based multi-stage obfuscated malware that unpacks a large filler blob to reveal a small marshalled .pyc which performs process injection into cvtres.exe and loads a downloaded .NET component for persistent C2. The infection uses disguised archives and bundled Python runtime (ntoskrnl.exe) to reconstruct and execute payloads from cloud-hosted files and maintain an encrypted RAT-like channel. #cvtres.exe #ntoskrnl.exe
Keypoints
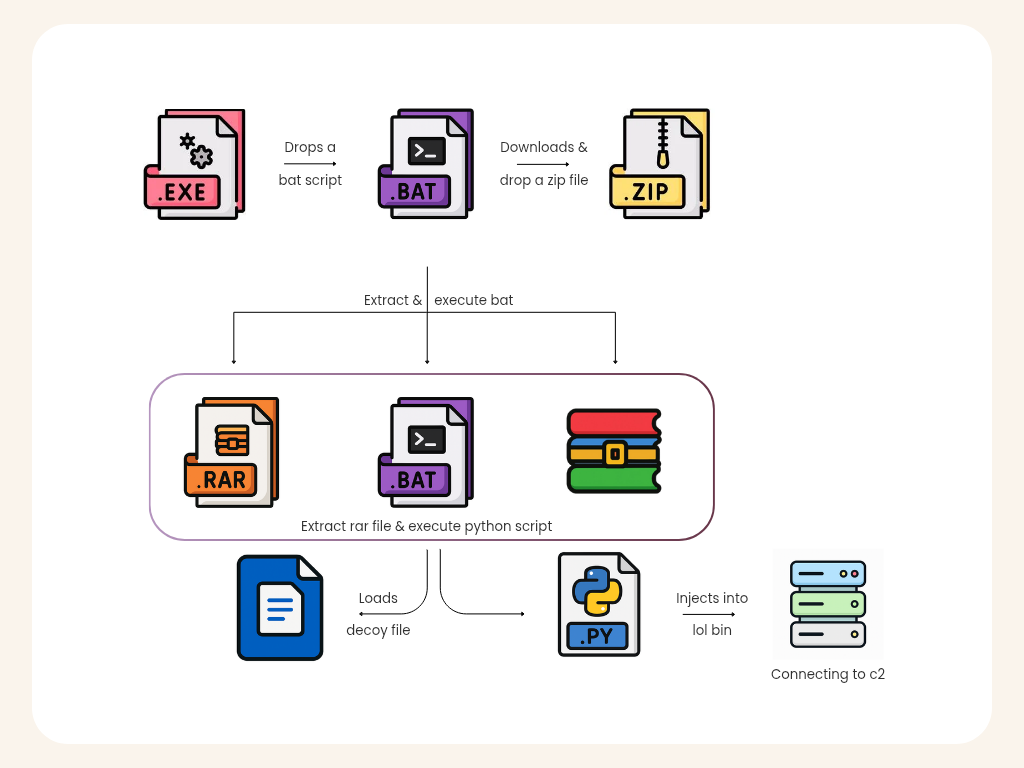
- The initial PE dropper reconstructs and writes a config.bat to disk using a SIMD-based stack buffer routine and persists it before execution.
- config.bat creates C:DragonAntivirus and downloads a file with a .png extension that is actually a RAR archive; tar is used to extract the disguised archive.
- The extracted payload includes a password-protected RAR disguised as AsusMouseDriver.sys, a renamed JSON-to-batch script (Install.bat), and a legitimate WinRAR executable (Inx) used to extract the archive.
- Install.bat extracts to C:UsersPublicWindowsSecurityA where a bundled Python runtime (ntoskrnl.exe) and a large obfuscated blob (Libimage) reside; a decoy PDF is opened to distract the user.
- The Python runtime runs with arguments that trigger layered de-obfuscation (Base64 → BZ2 → Zlib → marshal.loads) and executes a small marshalled .pyc embedded near the end of a ~60–65 MB filler blob.
- The executed payload injects into the legitimate Microsoft process cvtres.exe, then loads a .NET module from a remote C2 into the injected process to handle persistent, encrypted C2 communications.
- Network captures show continuous bidirectional encrypted TCP traffic consistent with a remote-access trojan (RAT) providing command execution, file transfer, and reconnaissance capabilities.
MITRE Techniques
- [T1105 ] Ingress Tool Transfer – The malware downloads a .NET component and other payload files from remote cloud storage to the victim (“…downloads a file from a remote cloud storage service.”).
- [T1204 ] User Execution – The attack uses a decoy PDF and disguised file extensions (.png, .sys) to trick users into executing or allowing extraction (“…the downloaded file has a .png extension, it’s actually a RAR archive” and “Opens a decoy document (a PDF) to distract the user after infection.”).
- [T1036 ] Masquerading – Files and executables are given legitimate or system-like names (ntoskrnl.exe, AsusMouseDriver.sys) to evade detection (“A file named ntoskrnl.exe (pretending to be a Windows kernel file…)” and “AsusMouseDriver.sys — actually a password-protected RAR”).
- [T1140 ] Deobfuscate/Decode Files or Information – The payload uses layered decoding and decompression (Base64 → BZ2 → Zlib → marshal.loads) to reconstruct the executable code (“the layered de-obfuscation (Base64 → BZ2 → Zlib → marshal.loads)”).
- [T1055 ] Process Injection – The Python payload performs process injection into cvtres.exe to run malicious code within a trusted process (“the malware targets cvtres.exe” and “Running malicious code inside cvtres.exe…”).
- [T1106 ] Native API – The dropper reconstructs payloads using low-level operations (stack buffer, movups) and writes files via WriteFile to persist the batch script (“builds a large buffer on the stack… and then writing the reconstructed payload to disk via WriteFile”).
- [T1071 ] Application Layer Protocol – The injected .NET component communicates with C2 over TCP using an encrypted channel to receive commands and data (“performing TCP communication and receiving data over an encrypted channel.”).
- [T1547 ] Boot or Logon Autostart Execution (persistence) – The injected module and techniques enable stealthy persistence and continued C2 communications even after the initial loader exits (“Even if the loader process terminates, the injected process remains alive and continues C2 communication.”).
Indicators of Compromise
- [File Hash ] Parent and injected file hashes observed – 675D475B5C02CA834E83BE009E09DB7C (Parent File), 33DD6D8FCFF3CA256F44A371FA3CF819 (Injected File).
- [File Name ] Disguised and bundled filenames used in the attack – ntoskrnl.exe (bundled Python runtime), AsusMouseDriver.sys (password-protected RAR disguised as a SYS driver).
- [File Path ] Dropped and installation paths – C:UsersPublicconfig.bat (dropped batch script), C:UsersPublicWindowsSecurityA (extraction and runtime location).
- [Network ] Remote download/C2 context – files downloaded from remote cloud storage (downloaded .png that is a RAR) and encrypted TCP C2 channel between injected .NET module and remote server.