Trend Research observed a resurgence of Lumma Stealer (tracked as Water Kurita) activity beginning the week of October 20, 2025, and documented new command-and-control behavior that layers browser fingerprinting onto existing C2 protocols. The malware now uses JavaScript-based fingerprinting and stealthy HTTP communications to profile victims and guide targeted follow-on actions. #LummaStealer #WaterKurita
Keypoints
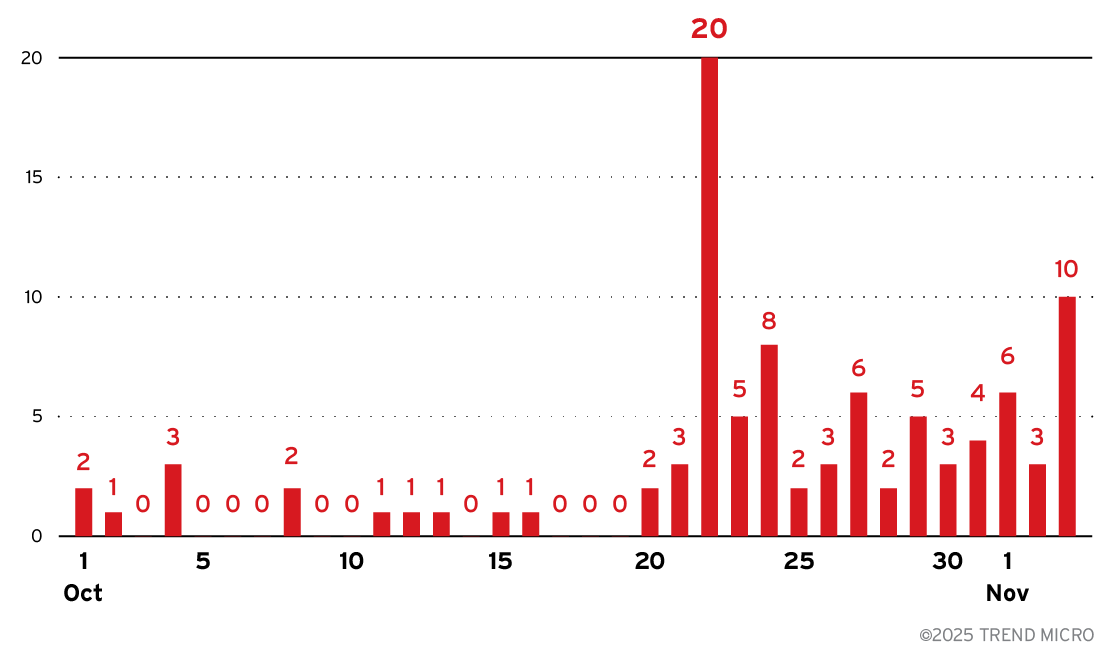
- Trend telemetry detected increased Lumma Stealer activity starting the week of October 20, 2025, after a prior decline following doxxing of alleged operators.
- Lumma Stealer now uses browser fingerprinting via a dedicated /api/set_agent endpoint to collect extensive system, network, hardware, and browser data.
- The fingerprinting payload is delivered as JavaScript, collects WebGL, canvas, audio, WebRTC, and other profiling data, serializes it to JSON, and POSTs it back to C2 with act=log.
- Samples show process injection into Chrome (remote thread injection from MicrosoftEdgeUpdate.exe into chrome.exe), enabling execution in trusted browser contexts.
- Fingerprinting augments rather than replaces existing C2: traditional parameters (uid, cid) and WinHTTP-based communications remain in use.
- Operationally, the hybrid approach improves evasion (detecting VMs/sandboxes), enables selective targeting, and preserves operational continuity despite degraded underground infrastructure.
- Observed IOCs include file hashes and C2 domains (e.g., jamelik[.]asia and pabuloa[.]asia); Trend Vision One provides detections, hunting queries, and intelligence for defenders.
MITRE Techniques
- [T1055] Process Injection – Lumma Stealer performs remote thread injection from MicrosoftEdgeUpdate.exe into chrome.exe to execute within a trusted browser process (“…remote thread injection from MicrosoftEdgeUpdate.exe into legitimate Chrome browser processes (chrome.exe)…”).
- [T1071] Application Layer Protocol – Malware uses HTTP GET/POST requests (including /api/set_agent and act=log POSTs) to communicate fingerprinting data and traditional C2 parameters (“…initial GET request… and transmits it back to the C&C server via a POST request…”).
- [T1436] Browser Extensions (Browser-based Data Collection) – Uses JavaScript fingerprinting scripts delivered via the C2 to collect browser and system characteristics (WebGL, canvas, audio, WebRTC) (“…C&C server responds with JavaScript code designed to collect an extensive array of system and browser characteristics…”).
- [T1078] Valid Accounts / Abuse of Trusted Processes – Executes within legitimate browser processes to blend with normal traffic and evade detection (“…execute within the context of a trusted browser process, effectively bypassing many security controls and appearing as legitimate browser traffic…”).
- [T1005] Data from Local System – Collects system and hardware information (CPU cores, device memory, screen resolution, fonts, plugins) as part of fingerprinting for profiling (“…Platform details, user agent strings… CPU cores, device memory… Screen resolution… Available fonts and browser plugin information”).
- [T1041] Exfiltration Over C2 Channel – Serializes fingerprint data to JSON and exfiltrates via URL-encoded form POSTs to the C2 with act=log parameter (“…script serializes all information into JSON format and transmits it back to the C&C server via a POST request…”).
Indicators of Compromise
- [File Hash] malware sample – 516cd47d091622b3eb256d25b984a5ede0d5dd9540e342a28e199082395e65e5 (TrojanSpy.Win64.LUMMASTEALER.THKAABE).
- [Domain] C2 servers – jamelik[.]asia (browser fingerprinting /api/set_agent endpoint), pabuloa[.]asia (C2 server).
- [File Name / Behavior] injected processes – evidence of MicrosoftEdgeUpdate.exe injecting into chrome.exe as part of process injection activity.
Read more: https://www.trendmicro.com/en_us/research/25/k/lumma-stealer-browser-fingerprinting.html