Socket Threat Research Team uncovered 175 malicious npm packages used in the Beamglea phishing campaign that targeted over 135 industrial, technology, and energy companies and were downloaded more than 26,000 times as of 9 October 2025. Researchers identified 16 IoCs (subdomains, domains, emails), tracked domain/IP histories and registrations, and found broad infrastructure links including gambling sites, SSL mismatches, and 344 email-connected domains. #Beamglea #fejyhy.com
Keypoints
- Socket Threat Research Team discovered 175 malicious npm packages tied to the global Beamglea phishing campaign, with over 26,000 downloads by 9 October 2025.
- The investigation produced 16 IoCs comprising four subdomains, three domains (after extraction), and nine email addresses for further analysis.
- DNS and WHOIS analysis revealed two IoCs appeared on a malicious-domain feed 176–219 days before being reported (notwinningbutpartici[.]com and fejyhy[.]com).
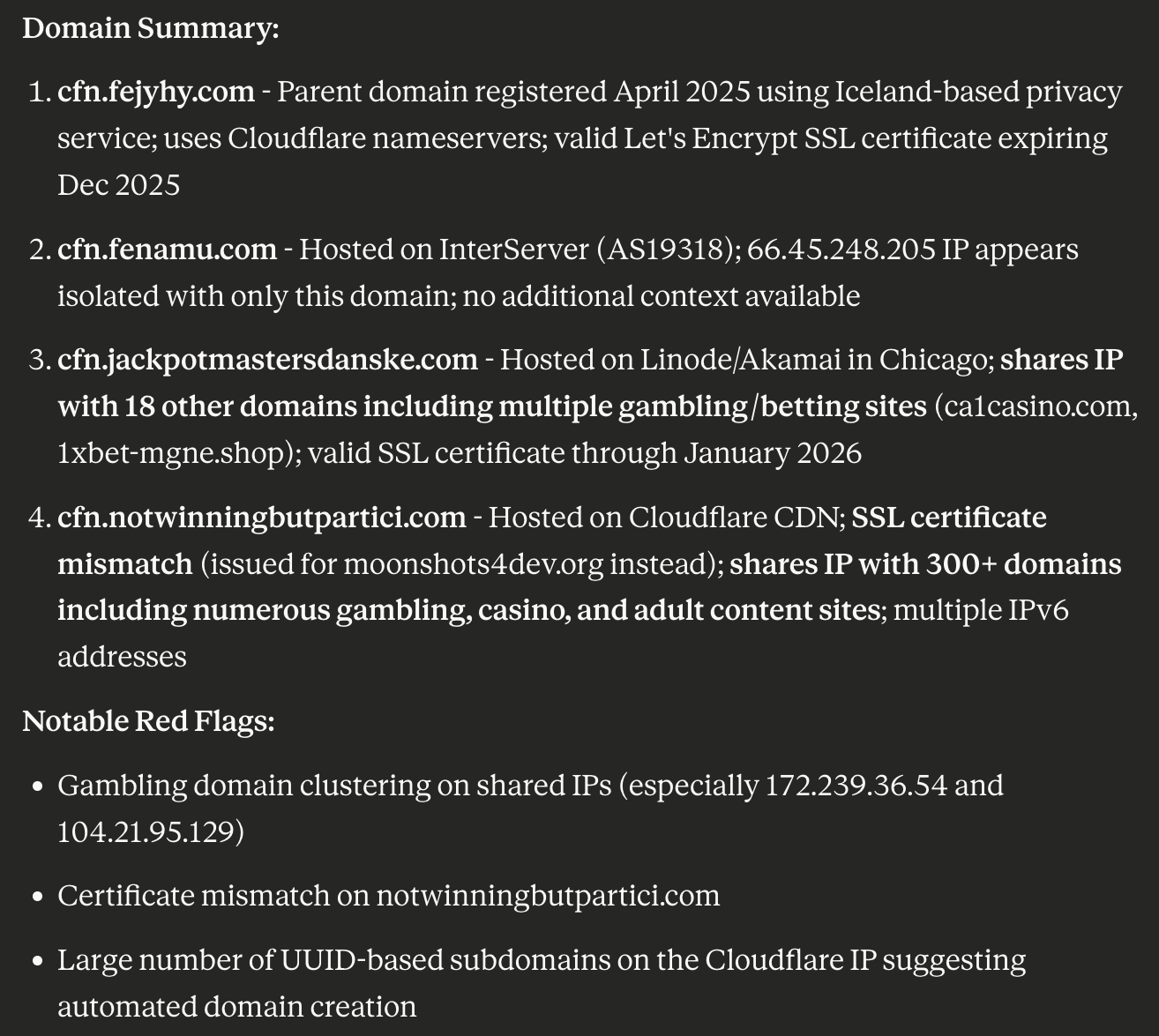
- Deep DNS probing showed shared IPs with gambling, casino, and adult sites and an SSL certificate mismatch where cfn.notwinningbutpartici[.]com used a certificate for moonshots4dev[.]org.
- WHOIS and WHOIS History queries found seven domains had 15 historical email addresses (11 unique for analysis) and registrations spread across Namecheap, MozDomains, NameSilo, and PDR with varied registrant countries.
- DNS Chronicle revealed rich DNS histories: 57 historical domain-to-IP resolutions across the seven domains, with resolution dates ranging from Feb 2024 to Oct 2025.
- Infrastructure enumeration identified five unique IP addresses (three flagged malicious), 18 IP-connected domains, three string-connected domains, and 344 email-connected domains derived from reverse WHOIS analysis.
MITRE Techniques
- [T1584] Compromise Infrastructure – Attackers registered and reused domains and subdomains to host phishing and malicious artifacts; researchers noted “shared the IP addresses… with multiple gambling sites” indicating shared or compromised hosting.
- [T1588] Obtain Infrastructure – Domains and subdomains were registered across multiple registrars (Namecheap, MozDomains, NameSilo, PDR) to prepare infrastructure for the campaign (“five were created just this year, two were created in 2024”).
- [T1598] Phishing – Use of malicious npm packages and targeted phishing to industrial and energy companies as part of the Beamglea campaign (“175 malicious npm packages threat actors used in the widespread Beamglea phishing campaign”).
- [T1583] Acquire Publicly Available Infrastructure – Attackers leveraged third-party hosting and certificates; an SSL certificate mismatch was observed (“its certificate was issued for the domain moonshots4dev[.]org”).
- [T1608] Stage Capabilities – Distribution of malicious packages via npm to deliver phishing/malicious payloads (“packages have been downloaded more than 26,000 times”).
- [T1586] Compromise Accounts – Email address reuse and historical WHOIS email links facilitated linking and expansion of infrastructure (“344 email-connected domains” discovered via Reverse WHOIS API).
Indicators of Compromise
- [Domain] domains identified as IoCs – notwinningbutpartici[.]com, fejyhy[.]com, and others (total seven domains).
- [Subdomain] malicious subdomains – cfn.fejyhy[.]com, cfn.jackpotmastersdanske[.]com (shared IPs with gambling sites), cfn.notwinningbutpartici[.]com (SSL cert mismatch).
- [IP address] infrastructure IPs – 172[.]239[.]36[.]54, 104[.]21[.]95[.]129 (shared with gambling sites); five unique IPs found in total, three flagged malicious.
- [Email address] registrant and historical emails – nine IoC email addresses plus two public addresses used for discovery; led to 344 email-connected domains.
- [File/Artifact] malicious npm packages – 175 malicious npm packages used in the Beamglea campaign (downloaded >26,000 times); sample artifacts available for download from the researchers’ website.
Read more: https://circleid.com/posts/burrowing-into-the-beamglea-campaign-dns-infrastructure