Cofense Intelligence analyzed infection URLs embedded in non-English phishing emails that bypassed secure email gateways, finding that legitimate cloud/file-hosting services (e.g., Google Drive, Dropbox, Amazon AWS) are commonly abused while some languages see more compromised or malicious domains. Malware families show strong language targeting: Remcos and Loda appear across several languages, KrBanker dominates Chinese campaigns, and many Portuguese-specific families (e.g., PeepingTile, Lampion) are almost exclusively delivered in Portuguese. #Remcos #KrBanker
Keypoints
- Infection URLs embedded in emails are the initial step in malware delivery chains and often use legitimate services or abused/compromised domains to host redirects or payloads.
- The top five non-English languages by volume for infection-URL campaigns are Spanish, Thai, German, Chinese, and Portuguese; language often indicates regional targeting.
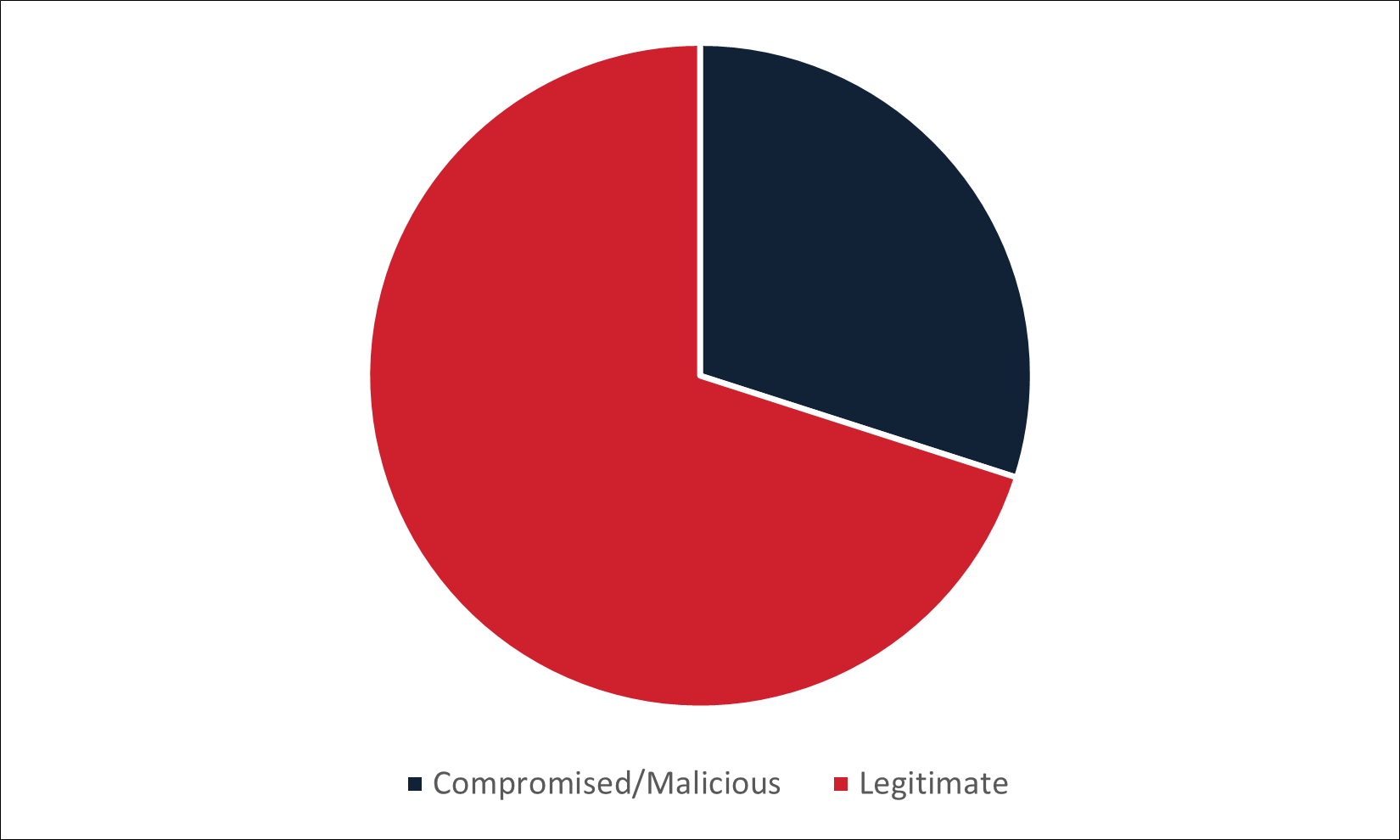
- Legitimate cloud/file-hosting services (OneDrive, Google Docs/Drive, Dropbox, MediaFire, GitHub, WeTransfer, Amazon AWS) constitute the majority of infection URLs across languages.
- Spanish campaigns heavily abused Google services (62% Google domains) and commonly delivered Remcos RAT (42% of malware in Spanish campaigns).
- Thai campaigns commonly used Dropbox, MediaFire, and Google, with Remcos and Loda each comprising about 29% of delivered malware; many Thai campaigns were finance-themed.
- German campaigns predominantly abused Dropbox (68% of domains) and frequently delivered RATs, notably XWorm (28%); multiple RAT families were often delivered simultaneously.
- Chinese and Portuguese campaigns showed higher proportions of compromised/malicious domains: Chinese campaigns heavily delivered KrBanker (94%) and used many .cn domains; Portuguese campaigns delivered many malware families that are nearly exclusive to Portuguese victims.
MITRE Techniques
- [T1204] User Execution – Infection URLs embedded in emails required recipients to interact and click links, initiating downloads or redirect chains: ‘Infection URLs are the first step… embedded in emails and represent the first action that a victim must take to become infected.’
- [T1190] Exploit Public-Facing Application – Threat actors used compromised or malicious web hosts and domains to serve malware, indicating exploitation or abuse of public-facing services: ‘the domains hosting the malware… will be considered to be an abused legitimate service or a compromised/malicious domain.’
- [T1566] Phishing – Use of multilingual phishing emails tailored to Spanish, Thai, German, Chinese, and Portuguese to lure victims into clicking infection URLs: ‘This report focuses on the URLs embedded in emails that bypassed email security controls…’
- [T1090] Proxy/Redirection – Use of legitimate redirect services and intermediary documents (e.g., bit.ly, documents with links) as part of infection chains: ‘legitimate redirect services, such as bit[.]ly, are used… legitimate services may also be used as an intermediate step to host documents with links to the next stage.’
- [T1105] Remote File Copy – Delivery of malware via direct file downloads hosted on cloud storage or compromised domains (e.g., Google Drive, Dropbox, Amazon AWS): ‘these URLs often lead directly to a file download or intermediary service with a link to a file download.’
Indicators of Compromise
- [Domain] abused legitimate services – docs.google.com, drive.google.com (Spanish campaigns: 62% Google domains)
- [Domain] abused legitimate services – dropbox.com, drive.google.com (German and Thai campaigns: Dropbox and Google abuse)
- [Domain] compromised/malicious domains – luynhk[.]com (Chinese campaigns) and ccrhs[.]shop (Thai campaigns)
- [Domain] compromised/malicious domains – datei-online[.]geodezja[.]lublin[.]pl and datei[.]mylocoltd[.]co[.]ke (German campaigns)
- [Domain] compromised/malicious domains – amazonaws[.]com (abused in Portuguese campaigns), and ###[.]###].]###[.]host[.]secureserver[.]net (example pattern seen in Spanish/Portuguese reporting)
- [Malware family] language-focused delivery – Remcos (Spanish, Thai, and across languages), KrBanker (Chinese, 94% of Chinese campaigns), Loda (Thai, ~29%)
Read more: https://cofense.com/blog/international-threats-infection-urls-used-in-regional-phishing-campaigns