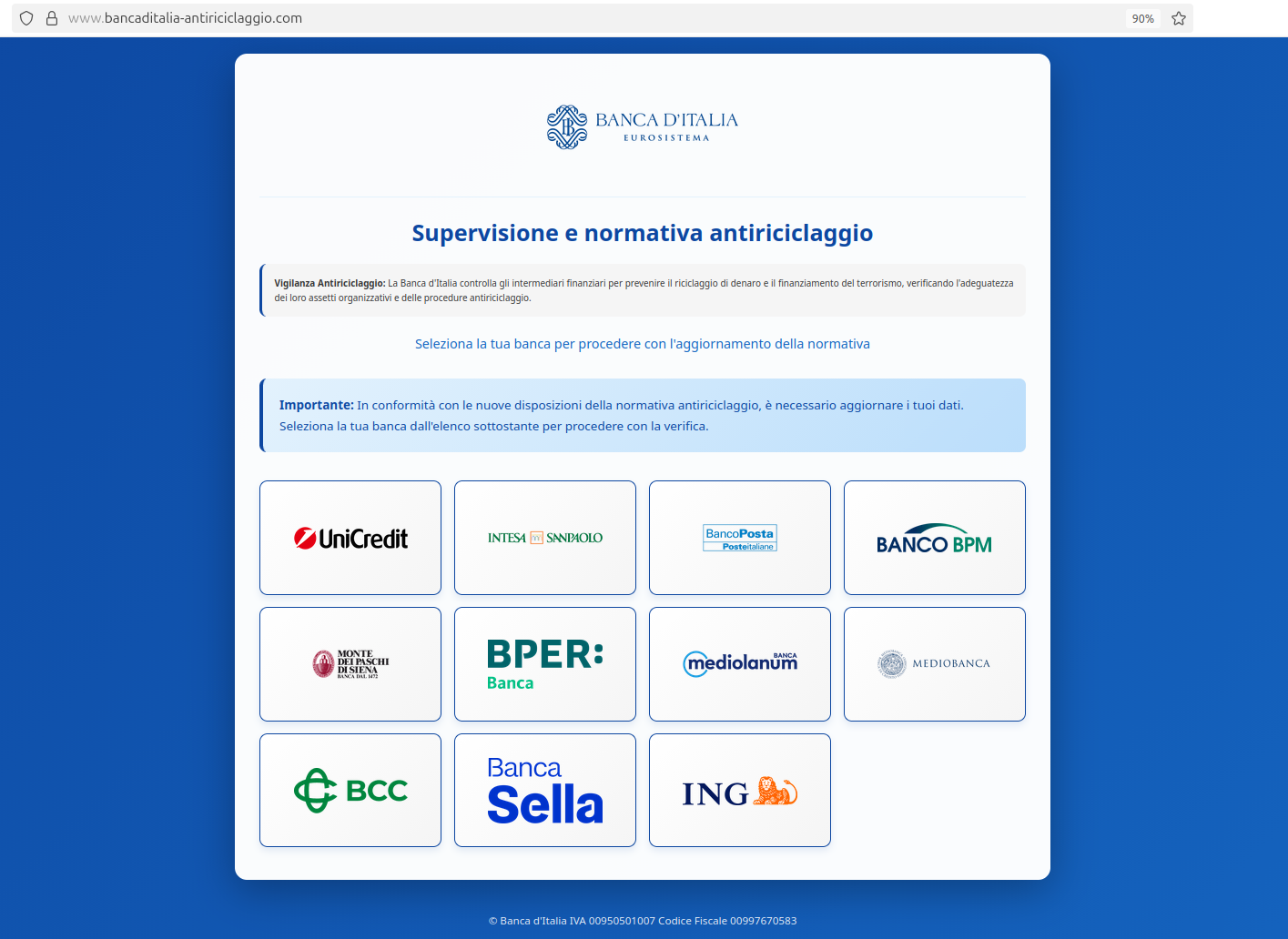
CERT-AGID reported a phishing campaign impersonating Banca d’Italia that uses a fraudulent website to harvest personal and banking information from Italian citizens by asking them to “update” data under the pretext of anti-money laundering rules. The malicious site prompts users to select their bank and enter credentials and OTPs; CERT-AGID notified Banca d’Italia’s security team and requested takedown of the domain. #Banca_dItalia #CERT-AGID
Keypoints
- The campaign impersonates Banca d’Italia using its name and logo to lend credibility to a fake data-update service.
- The phishing page claims to be for compliance with “new anti-money laundering regulations” to trick victims into updating personal data.
- Victims are asked to select their bank from multiple well-known brands and then enter personal details, banking credentials, and OTP codes.
- CERT-AGID detected the campaign and coordinated with Banca d’Italia’s cybersecurity team to request the malicious domain’s removal from the registrar.
- Indicators of Compromise related to the campaign were shared with organizations accredited to receive CERT-AGID feeds.
- The attack specifically targets Italian citizens and leverages social engineering rather than malware delivery to steal credentials.
MITRE Techniques
- [T1531] Drive-by Compromise – The phishing site lures victims to a malicious webpage under the guise of updating personal data (“…a fraudulent website to harvest personal and banking information…”).
- [T1192] Spearphishing Link – Victims are induced to click bank icons and links on the phishing page to submit credentials and OTPs (“…invites the user to select their banking institution… and enter credentials and OTP codes”).
- [T1606] Forge Web Credentials – The site impersonates Banca d’Italia using its name and logo to create fraudulent trust (“…impersonating Banca d’Italia using its name and logo…”).
- [T1499] Data from Information Repositories (User Input) – The campaign collects personal data and banking credentials through form submission on the malicious page (“…enter personal details, banking credentials, and OTP codes”).
Indicators of Compromise
- [Domain ] phishing infrastructure – malicious domain impersonating Banca d’Italia used for the fraudulent data-update page (domain was reported and takedown requested).
- [Shared IoC list ] campaign artifacts – CERT-AGID shared IoCs with accredited organizations (download link referenced: “download the IoCs of the campaign”).
Read more: https://cert-agid.gov.it/news/in-corso-una-campagna-di-phishing-ai-danni-di-banca-ditalia/