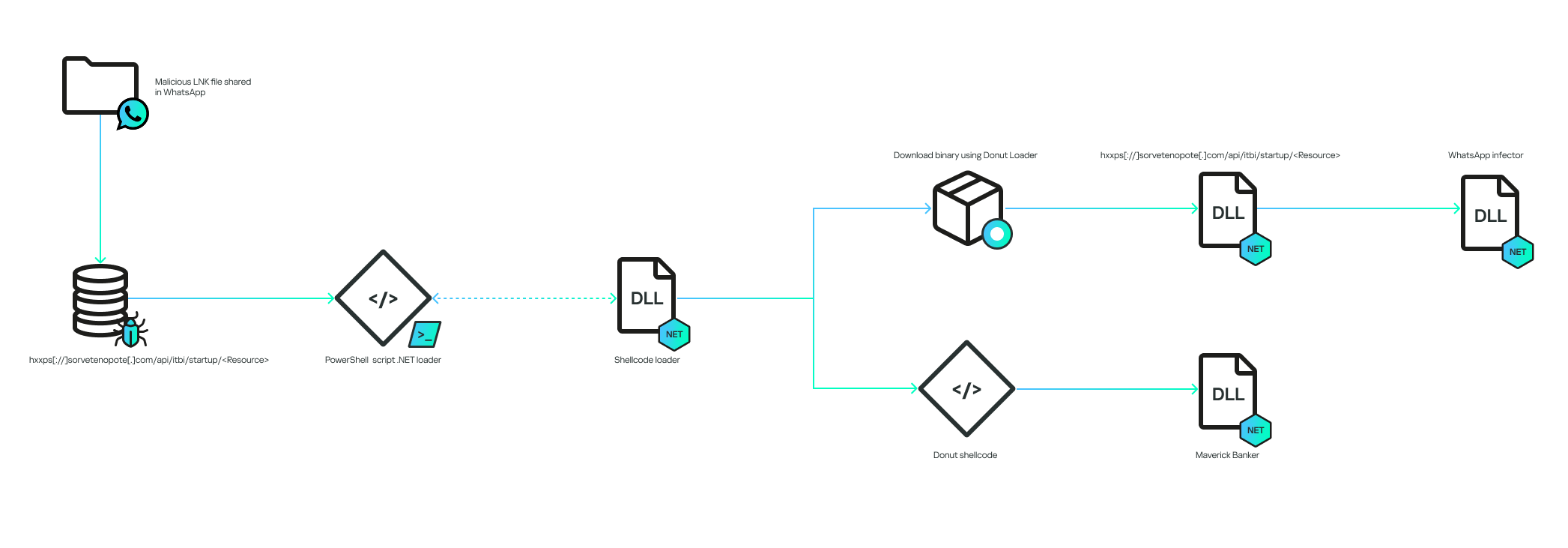
A Brazil-focused campaign spread a new banking trojan named Maverick via WhatsApp by delivering ZIPs containing a malicious LNK that launches a fully fileless infection chain ultimately loading in-memory .NET payloads and Donut shellcode. The campaign uses WPPConnect to hijack WhatsApp accounts for propagation, a C2 that validates user-agent and custom API keys, and shares code overlaps with the Coyote banker. #Maverick #Coyote
Keypoints
- A large WhatsApp-based campaign distributed ZIP archives containing a malicious LNK file that executes PowerShell to start a fully fileless infection chain targeting Brazilian users.
- The malware uses C2 validation (User-Agent and a Base64(HMAC256(Key)) API key) to ensure downloads originate from the malware, preventing generic HTTP downloaders from retrieving payloads.
- Two Donut-encrypted shellcodes are delivered and decrypted in memory; one branch loads a WhatsApp infector (using WPPConnect and Selenium) to spam contacts, the other loads the Maverick banking trojan.
- Maverick checks timezone, locale, region, and date format to ensure victims are in Brazil before activating; if checks pass it persists via a C2-dependent startup .bat and monitors browsers for 26 bank sites, exchanges, and a payment platform.
- Maverick.Agent performs extensive capabilities: screenshots, keylogging, process termination, mouse/keyboard injection, screen overlays and phishing windows, and remote desktop-like screenshot streaming via authenticated C2 commands.
- Communication uses WatsonTCP over SSL with an encrypted local X509 certificate (password Maverick2025!) and a specific authentication password; many design elements overlap with the Coyote banking trojan.
- The campaign exhibited high scale in Brazil (62,000 blocked LNK attempts in first 10 days of October) and demonstrates the use of AI in code-writing tasks such as certificate decryption.
MITRE Techniques
- [T1204] User Execution – The victim is tricked into opening a ZIP and a malicious .LNK received via WhatsApp which executes cmd.exe to run PowerShell.
- [T1204.002] Malicious File – LNK – The campaign distributes a malicious .LNK inside ZIP archives sent over WhatsApp to trigger the initial script execution.
- [T1059.001] Command and Scripting Interpreter: PowerShell – PowerShell is used to decode embedded .NET files, load assemblies in memory, and execute the infection chain (“The decoded commands point to the execution of a PowerShell script”).
- [T1106] Native API – Donut shellcode loaders embed .NET executables and are executed in memory using shellcode techniques to avoid writing files to disk (“the encrypted shellcode is a loader using Donut”).
- [T1218.005] Signed Binary Proxy Execution: cmd.exe – The LNK is encoded to execute cmd.exe with arguments that ultimately launch PowerShell scripts.
- [T1547.001] Boot or Logon Autostart Execution: Startup Folder – Persistence is attempted by creating a .bat in the user’s Startup folder that reboots the in-memory bootstrap from the C2 (“HealthApp-.bat” stored in Start Menu Programs).
- [T1071.001] Application Layer Protocol: Web Protocols – The malware communicates with C2 over HTTP(S) and a WatsonTCP SSL tunnel, including API routes like “/api/v1/…” and custom headers (“hxxps://sorvetenopote.com/api/v1/3d045ada0df942c983635e”).
- [T1041] Exfiltration Over C2 Channel – The agent can send screenshots, keylogger logs, and other harvested data to the C2 on demand (“SCREENSHOT … compressed with gzip”, “KEYLOGGER … send only when the server specifically requests”).
- [T1056.001] Input Capture: Keylogging – The malware includes a keylogger that captures keystrokes locally and sends logs when requested by the server (“Enable the keylogger, capture all locally, and send only when the server specifically requests the logs”).
- [T1113] Screen Capture – The agent takes screenshots and streams or sends multiple screenshots to the C2, computing hashes to detect changes (“Take a screenshot and send it to C2, compressed with gzip” and “send multiple screenshots to the machine when they change”).
- [T1531] Account Discovery/Access – The WhatsApp infector uses WPPConnect and Selenium to instrument WhatsApp Web and send messages from hijacked accounts to spread the malware (“uses the open-source project WPPConnect to automate the sending of messages in hijacked accounts via WhatsApp Web”).
- [T1490] Inhibit System Recovery – The malware can reboot the machine and kill processes, interfering with recovery and remediation (“REBOOT” and “KILLAPPLICATION” commands available via C2).
Indicators of Compromise
- [Domain] C2 and distribution domains – sorvetenopote.com, casadecampoamazonas.com (C2/API hosts used to serve encrypted payloads and WatsonTCP connection).
- [File name] Persistence and payload names – HealthApp-.bat (startup .bat created for persistence), Maverick Agent / Maverick.Agent (embedded banking payload), Maverick.StageOne (namespace in downloader), ZAP (WhatsApp infector namespace).
- [API key / secret] Hardcoded keys and passwords – HMAC key “MaverickZapBot2025SecretKey12345” used to generate API key; C2 agent password “101593a51d9c40fc8ec162d67504e221”; certificate password “Maverick2025!”.
- [URL/API path] Example API path – hxxps://sorvetenopote.com/api/v1/3d045ada0df942c983635e (resource used to request encrypted shellcode), and /api/itbi/startup/NEW_GUID (used in persistence command generation).
- [Detection names] AV detections – HEUR:Trojan.Multi.Powenot.a, HEUR:Trojan-Banker.MSIL.Maverick.gen (signatures used by Kaspersky to detect the threat).
Read more: https://securelist.com/maverick-banker-distributing-via-whatsapp/117715/