Kaspersky discovered Operation ForumTroll, a targeted espionage campaign that used personalized short-lived phishing links to deliver a Chrome sandbox escape zero-day (CVE-2025-2783) and deploy loaders and spyware including LeetAgent and the commercial Dante spyware. The campaign targeted Russian institutions and used techniques like WebGPU-based validation, COM hijacking persistence, and Fastly-hosted C2s. #CVE-2025-2783 #LeetAgent #Dante
Keypoints
- Kaspersky detected a 2025 wave of infections from personalized spear-phishing links that required only visiting a malicious site in Chromium-based browsers to start the attack.
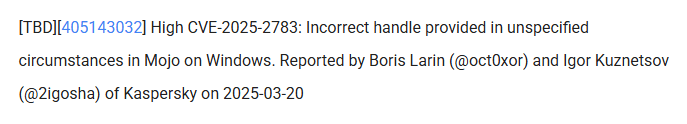
- Attackers exploited a previously unknown Chrome sandbox escape zero-day (CVE-2025-2783) that abused Windows pseudo-handles and IPC (ipcz/Mojo) to execute code in the browser process.
- Persistence was achieved via COM hijacking (overriding twinapi.dll CLSID) to load a malicious DLL loader that decrypts the main payload bound to the machine via BIOS UUID and ChaCha20-like decryption.
- Primary spyware observed included LeetAgent (commands in leetspeak, keylogging and file-stealing) and a more sophisticated commercial spyware identified as Dante from Memento Labs (formerly Hacking Team).
- Dante employs heavy anti-analysis (VMProtect, anti-hooking via direct syscalls, debug/sandbox/environment checks), module encryption (AES-256-CBC with machine-bound key) and orchestrator logic for C2 communication and self-protection.
- Infections used Fastly infrastructure for C2 hosting and distribution of additional tools; attackers targeted media, universities, research centers, government and financial organizations in Russia and Belarus.
- Kaspersky traced LeetAgent and Dante activity back to 2022 and linked code and infrastructure overlaps to attribute use of Memento Labs’ Dante in related operations.
MITRE Techniques
- [T1192 ] Spearphishing Link – Attackers sent personalized phishing emails with short-lived links to entice victims to visit malicious sites (“personalized links to track infections”).
- [T1204.001 ] Web Service – Victim validation and payload delivery performed via malicious websites and WebGPU checks (“calculate the SHA-256 of the random data received from the server using the WebGPU API… verify that the site is being visited by a real user”).
- [T1218 ] Signed Binary Proxy Execution (COM Hijacking) – Persistence via overriding CLSID entries in HKCU to load malicious DLL instead of twinapi.dll (“override the CLSID of twinapi.dll {AA509086-5Ca9-4C25-8F95-589D3C07B48A} and cause the system processes and web browsers to load the malicious DLL”).
- [T1059.003 ] Command and Scripting Interpreter: Windows Command Shell – LeetAgent runs commands via cmd.exe using numeric command IDs (“0xC033A4D (COMMAND) – Run command with cmd.exe”).
- [T1105 ] Ingress Tool Transfer – Attackers downloaded additional tools and modules (7z, Rclone, SharpChrome) and additional malware via Fastly-hosted infrastructure (“attackers used the Fastly.net cloud infrastructure to host their C2… download and run additional tools such as 7z, Rclone, SharpChrome”).
- [T1040 ] Network Sniffing / Collection – Keylogging and file-stealing capabilities implemented in LeetAgent to collect credentials and documents (“runs keylogging and file-stealing tasks in the background… searches for documents with the following extensions: *.doc, *.xls, *.ppt…”).
- [T1064 ] Scripting – Exploit triggers sandbox escape via console.debug JavaScript call that passes shellcode (“attackers call console.debug(0x42, shellcode); from their script” to start sandbox escape execution).
- [T1106 ] Native API – Exploit abuses Windows APIs (GetCurrentThread, DuplicateHandle, SetThreadContext, SuspendThread, ResumeThread) to convert pseudo-handles and execute shellcode in privileged process (“broker passed the -2 pseudo handle… converted -2 into a real handle… suspend the thread, set register values using SetThreadContext, and resume the thread”).
- [T1027 ] Obfuscated Files or Information – Dante uses VMProtect, string encryption and custom anti-hooking (creating syscall stubs) to hinder analysis (“packed with VMProtect… almost every string is encrypted… address resolved using a hash… new system call stub is created and used”).
- [T1574.001 ] Hijack Execution Flow: DLL Search Order Hijacking / COM – Loader re-encrypts and binds payload to BIOS UUID and checks process names before loading to avoid unwanted hosts (“re-encrypt the malware using the BIOS UUID to bind it to the infected machine… checks the name of the current process and only loads the malware when it is executed by certain processes”).
Indicators of Compromise
- [File Hash ] loader – 7d3a30dbf4fd3edaf4dde35ccb5cf9263650c1ac97bd5674e1e3bfa9b26008644edacfed2e39800df1cafbebfa22b437744d80f1b38111b471fa3eb42f2214a5ac7e1f13
- [File Hash ] LeetAgent sample – 33bb0678af6011481845d7ce9643cedc8390e2ebdd0db5d1a950b2c9984a5f429805d48c388a8af43039f5f16a0673a6e342fa6ae2402e63ba7569d20d9ba4894dc0ba59
- [File Hash ] Dante sample – 35869e8760928407d2789c7f115b7f83c25275228c6da54cf578fa72c9f49697e530969407d272b607f082305ce7b1987bfa17dc967ab45c8cd89699bcdced34ea94e126
- [File/Path ] Module folder pattern – %LocalAppData% containing files named as eight-byte Base64 strings (one file named same as folder) – used to identify active infections.
- [File Name ] Malicious attachments – examples seen in phishing: Baltic_Vector_2023.iso, Invitation_Russia-Belarus_strong_partnership_2024.lnk, SCAN_XXXX_.pdf.lnk
Read more: https://securelist.com/forumtroll-apt-hacking-team-dante-spyware/117851/