Attackers are weaponizing MSIX packages—using signed developer certificates, malvertising, SEO poisoning, and Loader-as-a-Service offerings—to deliver loaders and remote-access tools that bypass protections and run with elevated capabilities like runFullTrust and PowerShell execution. Defenders can use MSIXBuilder to safely generate realistic signed and unsigned MSIX test packages, validate AppXDeployment and AppXPackaging logging, and deploy the provided Splunk analytics to detect techniques used by groups like FIN7 and campaigns such as Storm-0569. #MSIXBuilder #FIN7
Keypoints
- MSIX is a ZIP-based Windows app package format with containerized execution, registry/file virtualization, and support for runFullTrust and script execution, which can be abused for stealthy malware delivery.
- Adversaries have commercialized MSIX abuse through Loader-as-a-Service offerings and premium code-signed packages that evade SmartScreen and other protections.
- Distribution vectors include malvertising, SEO poisoning, and social engineering via collaboration platforms (e.g., fake SharePoint/OneDrive notifications and Teams messages).
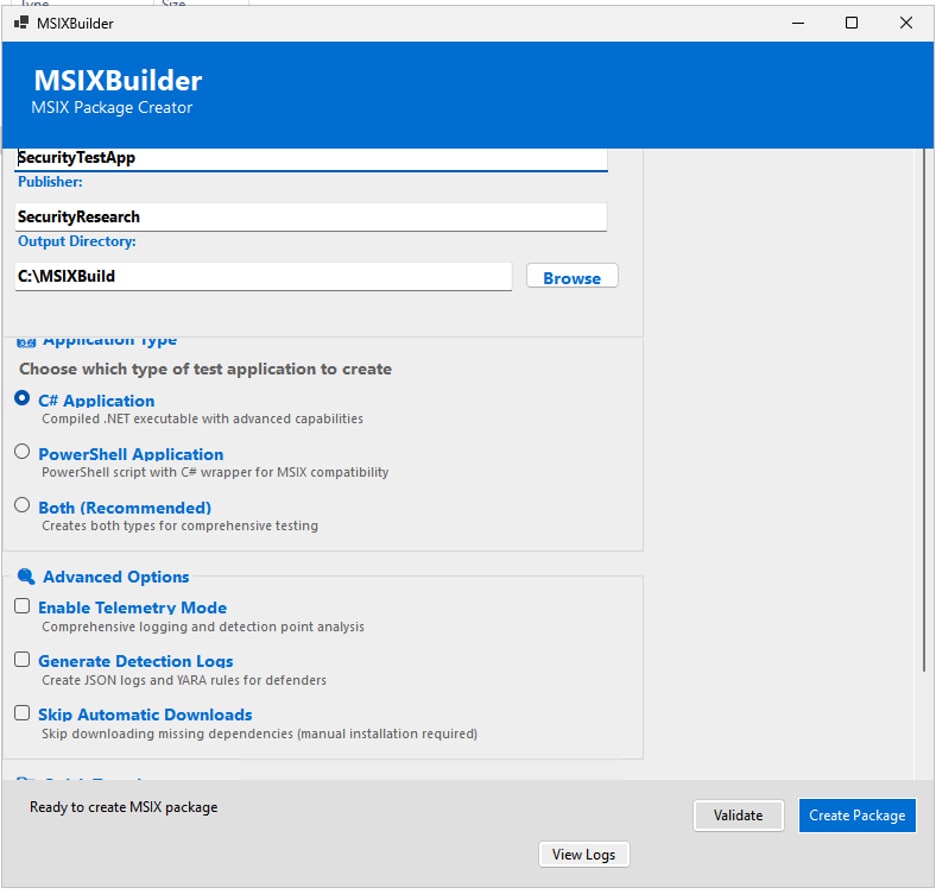
- MSIXBuilder automates certificate handling, signing, dependency resolution, and package creation (signed/unsigned) to let defenders safely test detection coverage and generate telemetry/YARA rules.
- Recommended detection sources include PowerShell ScriptBlock logging, AppXDeployment-Server and AppXPackaging operational logs, Sysmon process creation, and file activity in WindowsApps.
- Splunk provides analytic detections for unsigned installs, package interactions (EventID 171), successful installs (EventID 854), full-trust installs (EventID 400 HasFullTrust=true), developer-signed installs, AI_STUBS execution, and PowerShell from WindowsApps.
- Multiple malicious MSIX campaigns and malware families are enumerated with file hashes (e.g., Storm-0569/BATLOADER, Storm-1113/EugenLoader, NetSupport RAT, Sangria Tempest/Carbanak), enabling IOC-based hunting and blocking.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – MSIX distribution via SEO poisoning and compromised sites redirects users to fake downloads that host malicious MSIX packages: ‘…injecting malicious code that redirects visitors to fake download pages…’
- [T1204.002] User Execution: Malicious File – Users are socially engineered through Teams and fake SharePoint/OneDrive notifications to open MSIX packages: ‘…attackers sending fabricated SharePoint and OneDrive sharing notifications…’
- [T1553.002] Create or Modify System Process: Code Signing – Adversaries use developer-signed MSIX packages (and premium signed offerings) to appear legitimate and bypass SmartScreen: ‘…premium tiers… provide properly code-signed packages that slip past Windows Defender SmartScreen…’
- [T1105] Ingress Tool Transfer – Malvertising campaigns purchase legitimate ad placements to deliver malicious MSIX payloads mimicking popular software downloads: ‘…purchasing legitimate ad placements for popular software searches… distribute malicious MSIX packages instead of legitimate software.’”
- [T1195] Supply Chain Compromise – Loader-as-a-Service and commercialized packaging of malware into MSIX demonstrates abuse of packaging/deployment supply chains to distribute malicious payloads: ‘…commercial malware services… offering MSIX-packaged malware as a subscription service.’”
- [T1059.001] Command and Scripting Interpreter: PowerShell – MSIX packages execute PowerShell scripts via Package Support Framework, and attackers spawn PowerShell from WindowsApps: ‘…can run PowerShell scripts via Package Support Framework (PSF)’ and ‘PowerShell spawning from App path…’
- [T1543.003] Create or Modify System Process: Windows Service – FullTrust MSIX installations grant extensive system API access enabling privileged actions outside container boundaries: ‘…With runFullTrust capability, apps have extensive system access’.”
Indicators of Compromise
- [File Hash – SHA256] Malicious MSIX samples – 48aa2393ef590bab4ff2fd1e7d95af36e5b6911348d7674347626c9aaafa255e (Storm-0569 BATLOADER), 44cac5bf0bab56b0840bd1c7b95f9c7f5078ff417705eeaaf5ea5a2167a81dd5 (Storm-1113 EugenLoader)
- [File Hash – SHA256] Additional malware families – e300c44b45b07f3766586e500f4f3596c23ffd80171eaa5334bb4db3e8d027e0 (GoogleMeet.msix / NetSupport RAT), 2ba527fb8e31cb209df8d1890a63cda9cd4433aa0b841ed8b86fa801aff4ccbd (Sangria Tempest / Carbanak)
- [File Hash – MD5] FakeBat/MSIX related – 09b7d9976824237fc2c5bd461eab7a22, f5244c0d5c537efb24c9103e866eea26 (ArechClient2/Redline)
- [Event Log Entries] AppX/XDeployment events useful as IOCs – EventID 171 (AppXPackaging interaction), EventID 603 with Flags=8388608 (-AllowUnsigned), EventID 854 (installation success), EventID 400 with HasFullTrust=true (full trust install)
- [File Path / Process] AI_STUBS / popupwrapper.exe artifacts – Process paths containing AI_STUBSAiStubX64Elevated.exe and original filename popupwrapper.exe associated with Advanced Installer built MSIX packages
Read more: https://www.splunk.com/en_us/blog/security/msix-weaponization-threat-detection-splunk.html