ADCS misconfigurations create a broad privilege-escalation attack surface allowing attackers to obtain certificates that can impersonate high-value domain accounts and potentially lead to full domain and hybrid cloud compromise. Notable tools like Certipy and Certify automate enumeration and exploitation of 16 identified ESC techniques, some of which (e.g., ESC15) exploit known CA vulnerabilities such as CVE-2024-49019. #Certipy #ESC15
Keypoints
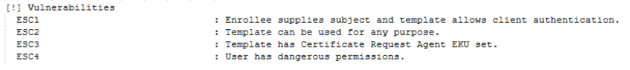
- Misconfigured AD Certificate Services (ADCS) certificate templates and CA settings enable 16 distinct privilege-escalation techniques (ESC1–ESC16) that can yield domain authentication and full compromise.
- Attackers can abuse template settings like authentication EKUs, client-specified SANs, enrollment-agent EKUs, missing security extensions, and issuance policy OIDs to escalate privileges.
- Tools such as Certipy, Certify (including Certify 2.0), Metasploit, and built-in certreq.exe are used for enumeration, certificate issuance, and exploitation, with Certipy covering many ESC techniques comprehensively.
- NTLM relay techniques (ESC8, ESC11) and CA vulnerabilities (ESC15 / CVE-2024-49019) extend on-prem ADCS compromises to hybrid cloud identity services like Microsoft Entra CBA, enabling lateral movement to cloud resources.
- Defensive measures include enumerating templates (e.g., using Certipy), minimizing enrollment rights, disabling unused templates and interfaces, avoiding NTLM for ADCS, auditing certificate operations, and monitoring certificate-related network activity.
- Cato SASE Cloud Platform provides detection and prevention by identifying certificate enrollment requests, certificate-based authentication attempts, and suspicious certificate-related network activity, and by blocking known exploitation tools.
- An appendix maps all ESC techniques to attack surfaces (templates, AD objects, CA servers, NTLM relay, server auth settings, and YubiHSM2 abuse) to guide remediation and detection priorities.
MITRE Techniques
- [T1558] Steal or Forge Kerberos Tickets – ADCS misuse to obtain certificates enabling Kerberos PKINIT authentication and impersonation of domain accounts (“…privilege escalation leading to lateral movement, persistence and even full domain compromise…”).
- [T1078] Valid Accounts – Issuing certificates for authentication to impersonate legitimate accounts and gain domain access (“…enroll for certificates in their name…”).
- [T1190] Exploit Public-Facing Application – NTLM relay to ADCS web enrollment interfaces (ESC8) to coerce and relay authentication (“…relays authentication requests to the web enrollment interface (HTTP-based)”).
- [T1566] Phishing for Information (coercion to authenticate) – Forcing users to authenticate to attacker-controlled systems to capture and relay NTLM credentials for ADCS enrollment (“…coerce legitimate users to authenticate to their machine, then relay those authentication requests…”).
- [T1609] Container and Resource Discovery (PKI/Certificate enumeration) – Use of Certipy and enumeration routines to discover certificate templates, EKUs, and enrollment rights (“…enumerate the certificate templates available for their compromised user…”).
- [T1550] Use Alternate Authentication Material – Abuse of certificate-based authentication (CBA) and mapping features like altSecurityIdentities or UPN mapping to authenticate as other accounts (ESC10, ESC14) (“…map certificates to domain accounts based on…UPN…altSecurityIdentities attribute…”).
- [T1211] Exploitation of Hardware Vulnerability – Abuse of vulnerable YubiHSM2 devices on CA servers to extract or misuse signing keys (ESC12) (“…targets ADCS servers using vulnerable YubiHSM2 devices to store and manage their private signing keys…”).
- [T1486] Data Encrypted for Impact (unauthorized certificate issuance leading to domain control) – CA compromise (ESC7/ESC5) enabling unauthorized issuance of certificates and potential domain-wide takeover (“…full CA control, unauthorized certificate issuance and full domain compromise.”).
- [T1195] Supply Chain Compromise (use of tooling) – Use and distribution of offensive tooling such as Certipy and Certify to facilitate ADCS exploitation (“…Certipy, a Python-based open-source toolkit for enumerating and exploiting ADCS…”).
Indicators of Compromise
- [Tool Names] evidence of active exploitation or reconnaissance – Certipy, Certify (Certify 2.0), Metasploit, certreq.exe.
- [CVE / Vulnerability] exploited CA vulnerability – CVE-2024-49019 (ESC15) – referenced as an exploit used to inject application policies into certificates.
- [Network Activity] suspicious certificate-related requests – abnormal certificate enrollment requests and certificate-based authentication attempts detected by network monitoring (example: unexpected CSR traffic to CA servers).
- [AD Object Changes] modified AD attributes or templates – altered certificate templates, issuance policy OIDs, altSecurityIdentities or template enrollment permissions (example: templates allowing client-specified SANs, templates with no security extension).
- [Logs / Events] Kerberos PKINIT and CSR events – Kerberos PKINIT authentication requests and Certificate Signing Request (CSR) logs indicating unusual issuance activity (and other certificate operation events).