Proofpoint researchers demonstrated how attackers automate creation of malicious internal (second-party) OAuth applications to gain persistent access to Microsoft Entra ID tenants, allowing continued mailbox and file access even after credential resets or MFA enforcement. The researchers observed an active ATO using this technique linked to AiTM Tycoon phishing activity and provided remediation steps including client secret revocation and application removal. #Tycoon #MicrosoftEntraID
Keypoints
- Attackers can register second-party (internal) OAuth applications in a compromised tenant to obtain persistent access that survives password resets and MFA enforcement.
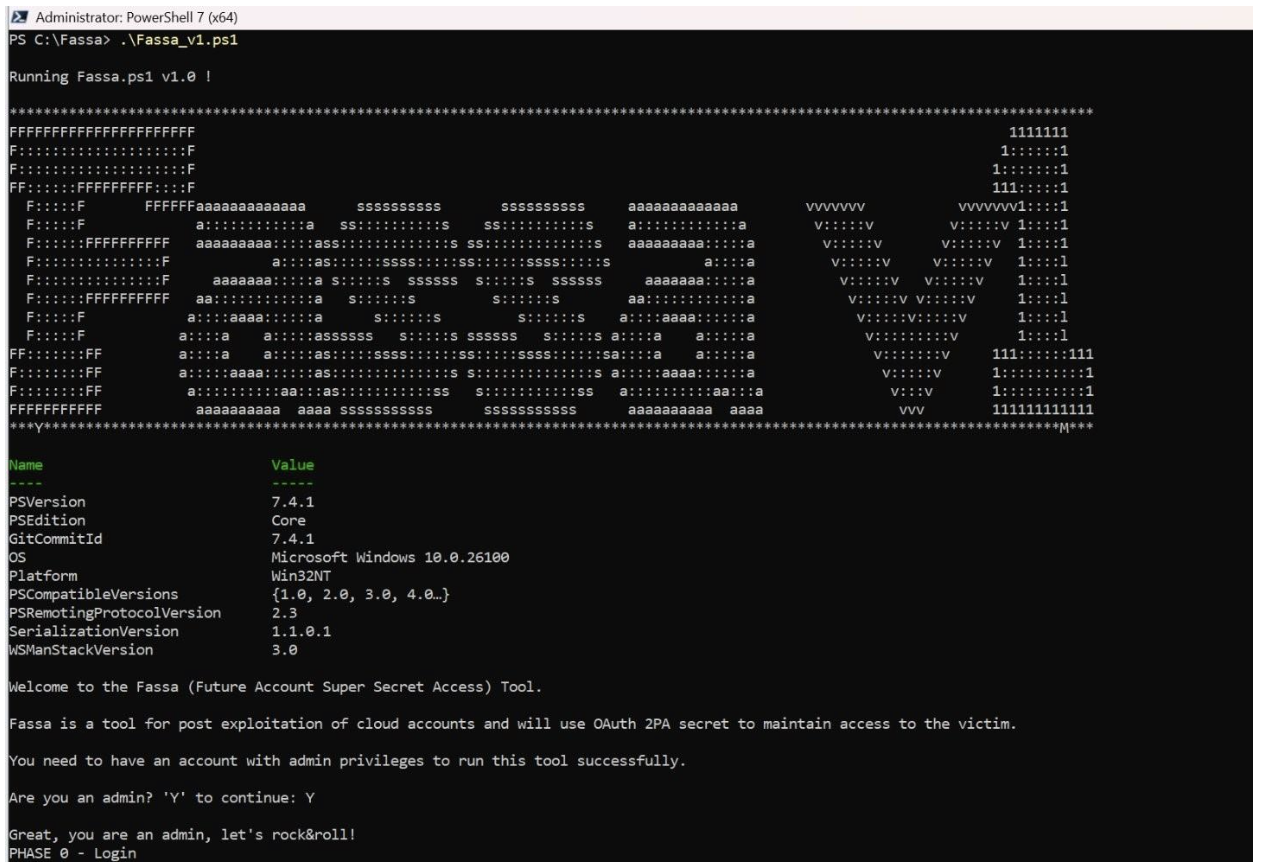
- Proofpoint built an automated tool (PoC) that registers applications, generates client secrets, and harvests access, refresh, and ID tokens to demonstrate persistence.
- Malicious applications inherit implicit trust as internal resources and can be configured with permissions like Mail.Read and offline_access to exfiltrate mail and other Microsoft 365 data.
- The tool’s workflow assigns the compromised user as the application owner, making the app appear legitimate in Entra ID App Registrations and harder to detect.
- Real-world telemetry found an ATO linked to AiTM Tycoon phishing, where an internal app named “test” was registered and maintained access for days despite a password change.
- Persistence is achieved until the application is deleted or client secrets expire; researchers demonstrated a two-year secret validity to illustrate long dwell time risk.
- Recommended remediation: revoke client secrets and user tokens, delete the application and service principals, implement continuous app monitoring, and train users to report suspicious consent requests.
MITRE Techniques
- [T1586] Compromise cloud accounts – Attackers register and authorize malicious internal OAuth applications to maintain access: ‘register new internal applications…authorizing these applications to access critical organizational resources.’
- [T1078] Valid Accounts – Use of compromised user credentials and session cookies to access accounts: ‘Once the attackers have stolen a user’s login credentials, they can establish unauthorized access to the targeted accounts.’
- [T1584] Compromise Infrastructure – Use of reverse proxy toolkits and AiTM phishing to capture credentials: ‘reverse proxy toolkits accompanied by individualized phishing lures…FIDO downgrade attack’ (translated quote in English).
- [T1539] Steal Web Session Cookie – Theft of session cookies via phishing/AiTM to facilitate initial access: ‘individualized phishing lures that enable the theft of credentials and session cookies.’
- [T1608] Abuse Authentication Mechanism – Creation of OAuth client secrets and use of OAuth tokens to authenticate without user credentials: ‘creates a cryptographic client secret…collect multiple OAuth token types…access token, a refresh token, and an ID token.’
- [T1110] Brute Force (contextual) / Credential Access – Use of stolen credentials and subsequent persistence mechanisms to maintain access after password changes: ‘Credential reset test…Despite the password change, the malicious application maintains full access.’
Indicators of Compromise
- [User agent] telemetry context – AiTM-related browser signature likely tied to Tycoon phishing: “Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/126.0.0.0 Iron Safari/537.36”.
- [Application name] malicious app context – internal app registered in tenant: example ‘test’, and example ‘justSOMEniceAPP’.
- [OAuth scopes] permission context – scopes used to enable persistence and data access: Mail.Read, offline_access (examples shown in app configuration).
- [IP address] network context – actor used US-based VPN proxies and later failed logins from a Nigerian residential IP address (no specific IPs provided).
- [Client secret] credential context – active client secrets in ‘Certificates & Secrets’ enabling programmatic access – example: client secret with two-year validity (no hash provided).