Trend Research documents a new “Premier Pass-as-a-Service” model in which Earth Estries functions as an access broker that provides persistent access to Earth Naga, enabling coordinated deployments of backdoors like CrowDoor and ShadowPad. The report outlines a four-tier framework for collaborative APT attacks and highlights targeted campaigns against government, telecommunications, and retail organizations across APAC, NATO countries, and other regions. #EarthEstries #EarthNaga #CrowDoor #ShadowPad
Keypoints
- Trend Research identifies a “Premier Pass-as-a-Service” model where one China-aligned APT (Earth Estries) brokers access for another (Earth Naga), complicating attribution and detection.
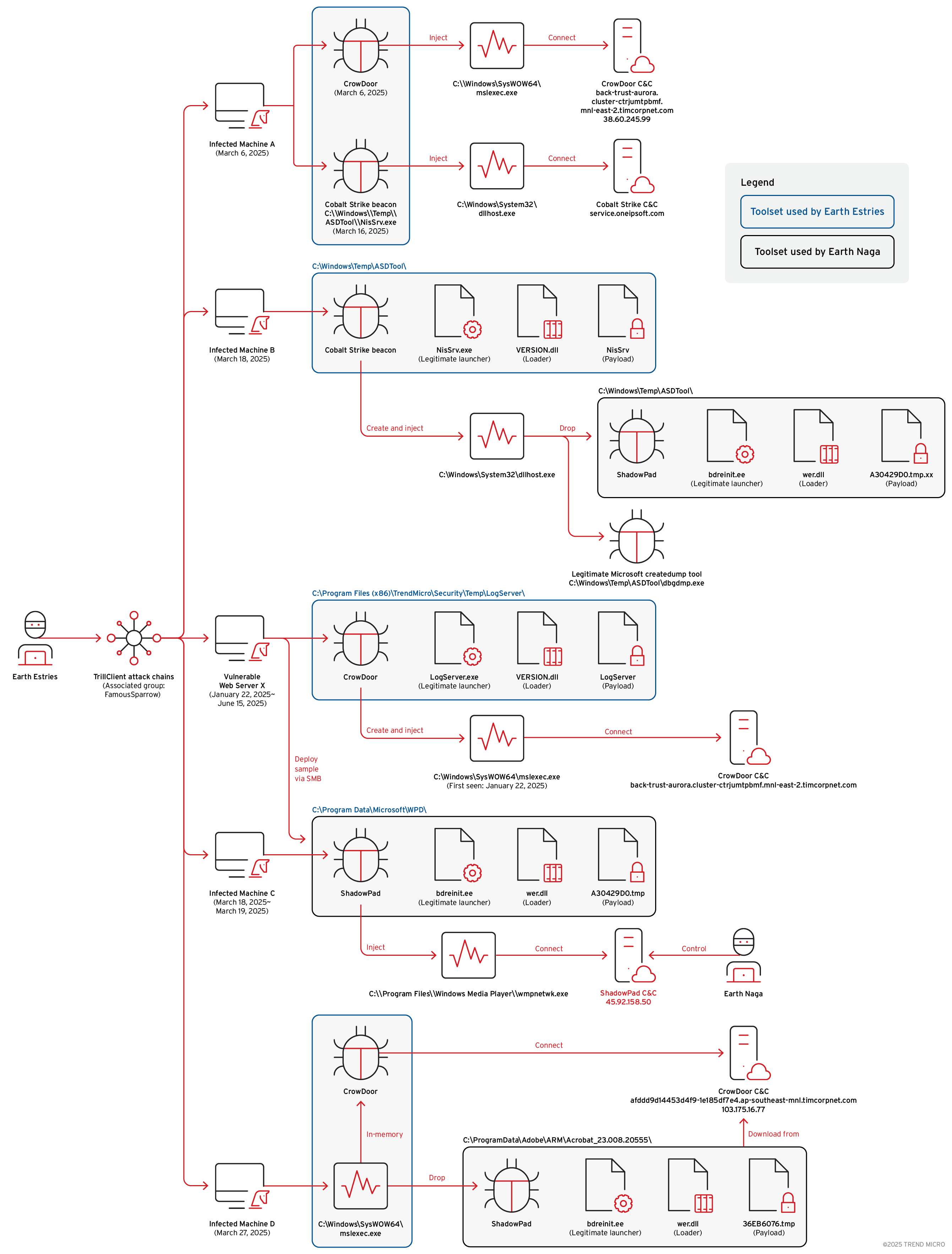
- Case studies show Earth Estries deployed CrowDoor and subsequently facilitated ShadowPad deployments linked to Earth Naga within the same victim environments.
- Recent campaigns targeted government agencies, telecommunications providers, and retail organizations across APAC, NATO countries, Latin America, and other regions.
- Observed intrusion chain included initial compromise of a vulnerable internal web server, lateral movement, and multi-vector ShadowPad deployment (Cobalt Strike SMB beacon, SMB file transfers, CrowDoor variant).
- Trend introduces a four-tier categorization of collaborative attacks (Type A–D) distinguishing loose coordination from strict coordination such as deploying third-party payloads or provisioning operational boxes.
- Evidence includes specific C2 domains and IPs (e.g., back-trust-aurora[.]cluster-ctrjumtpbmf[.]mnl-east-2.timcorpnet[.]com; 45[.]92[.]158[.]50; 103[.]175[.]16[.]77) and exploitation of edge device CVE-2025-5777 targeting Citrix devices.
- Recommendations emphasize multi-layered defenses, monitoring for suspicious file deployments and remote administration tools, and focused hunting of edge devices and leaked credentials.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Trend observed exploitation of vulnerable internal web servers (e.g., “Vulnerable Web Server X”) leading to initial compromise: ‘On January 22, 2025, Earth Estries likely leveraged an unmanaged host to compromise a vulnerable internal web server (Vulnerable Web Server X).’
- [T1059] Command and Scripting Interpreter – Use of wget to connect to C2 from a compromised mail server: ‘They connected to their C&C server using the wget command.’
- [T1021] Remote Services (SSH) – Attackers attempted to use a compromised checkpoint mail server to establish SSH connections to other internal hosts: ‘the attackers attempted to use the checkpoint mail server to establish SSH connections to other internal network hosts.’
- [T1078] Valid Accounts – Deployment via compromised user credentials to transfer files over SMB for lateral movement and malware deployment: ‘Deploy malware using compromised user credentials to transfer files via SMB.’
- [T1570] Lateral Tool Transfer – Use of SMB file transfers and SMB Cobalt Strike beacon for lateral movement and payload deployment: ‘Deploy malware via Cobalt Strike SMB beacon’ and ‘transfer files via SMB.’
- [T1105] Ingress Tool Transfer – Transfer and execution of malware loaders and payloads (Draculoader, CrowDoor, ShadowPad) into victim systems: infection flows described for CrowDoor and ShadowPad show staged loaders and payload transfer.
- [T1218] Signed Binary Proxy Execution (DLL Side-Loading) – Use of legitimate signed executables and DLL side-loading to run malicious payloads (LogServer.exe -> VERSION.dll; Bdreinit.exe -> wer.dll): ‘Legitimate Microsoft launcher vulnerable to DLL side-loading’ and ‘Legitimate executable signed by BitDefender vulnerable to DLL side-loading.’
- [T1106] Native API – Use of custom memory dumping tools and LSASS dumping tools (Blindsight, custom SSP dumper) to collect credential material from memory: ‘Blindsight… to dump LSASS memory’ and ‘custom tool dumping memory… detected as HackTool.Win64.MINIDUMP.ZALL.’
- [T1086] PowerShell (or scripting) implied in post-exploitation tooling use – Use of remote administration and post-exploitation tools like AnyDesk and VMProtected EarthWorm SOCKS5 tunnel for persistence and command/control activities: ‘We observed Earth Estries using the following post-exploitation tools (Figure 3): AnyDesk… EarthWorm, a SOCK5 network tunnel.’
- [T1071] Application Layer Protocol – Use of C2 infrastructure and cloud features (VSCode remote tunnel example) and HTTP/S domains for command-and-control communications: multiple C2 domains and cloud-based C2 communications observed (e.g., afddd9d14453d4f9-1e185df7e4[.]ap-southeast-mnl[.]timcorpnet[.]com).
Indicators of Compromise
- [Domain] CrowDoor / CrowDoor C2 – back-trust-aurora[.]cluster-ctrjumtpbmf[.]mnl-east-2.timcorpnet[.]com, afddd9d14453d4f9-1e185df7e4[.]ap-southeast-mnl[.]timcorpnet[.]com
- [IP Address] ShadowPad / CrowDoor C2 – 45[.]92[.]158[.]50 (ShadowPad-linked C2), 103[.]175[.]16[.]77 (resolved CrowDoor C2)
- [Vulnerabilities / CVE] Edge device exploitation – CVE-2025-5777 (Citrix devices) used in campaigns targeting telecommunications providers
- [File names / infection flows] DLL side-loading artifacts – LogServer.exe -> VERSION.dll -> LogServer (CrowDoor flow); bdreinit.exe -> wer.dll -> 36EB6076.tmp or A30429D0.tmp (ShadowPad flow)
- [Tools] Post-exploitation utilities – AnyDesk, EarthWorm (VMProtected SOCKS5 tunnel), Blindsight, and a custom LSASS memory dumper (HackTool.Win64.MINIDUMP.ZALL)
Read more: https://www.trendmicro.com/en_us/research/25/j/premier-pass-as-a-service.html