A coordinated campaign is impersonating developer tools and trusted services to trick macOS users into pasting base64-encoded curl commands that fetch and execute installer scripts delivering Odyssey Stealer and AMOS. Operators reuse infrastructure, SSL certificates, and domains (e.g., 93.152.230[.]79, 195.82.147[.]38, bonoud.com) to maintain persistence and scale across at least 85 phishing sites. #OdysseyStealer #AMOS #93.152.230.79 #195.82.147.38
Keypoints
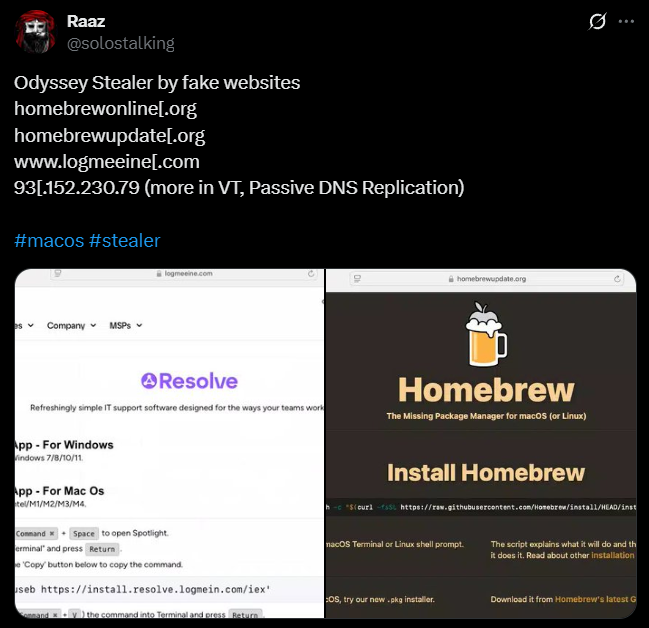
- The campaign targets macOS developers via fake download sites impersonating Homebrew, LogMeIn, and TradingView to increase trust and lure victims.
- Attackers use clipboard manipulation and click/interaction tricks to get users to paste base64-encoded curl commands that fetch and run remote installer scripts.
- Delivered payloads include Odyssey Stealer and AMOS (Atomic macOS Stealer), which harvest system, browser, and cryptocurrency credentials and attempt persistence and stealthy operations.
- Investigators identified over 85 phishing domains that reuse payload infrastructure, SSL certificates, and hosting servers, indicating operational reuse and persistence.
- Key infrastructure includes IPs 93.152.230[.]79 and 195.82.147[.]38, linked via the same SSL certificate and multi-service hosting (HTTP, SSH, FTP, IMAPS/POP3S).
- Payloads employ multi-shell obfuscation, sudo-based privilege escalation attempts, anti-analysis virtual machine checks via system_profiler and osascript, and service manipulation (e.g., killing OneDrive updaters).
- Mitigations recommended: block known domains/IPs, enforce Gatekeeper and script-execution restrictions, tighten sudo policies, monitor for base64 clipboard patterns and xattr/chmod execution chains, and share IOCs for takedowns.
MITRE Techniques
- [T1176 ] Browser Extensions – Clipboard manipulation and page JavaScript covertly place base64-encoded installer commands into the user clipboard to induce paste-and-execute behavior (“the page’s JavaScript is engineered to covertly place a base64-encoded installation command into the user’s clipboard when the visible ‘Copy’ button is clicked”).
- [T1204.002 ] User Execution: Malicious File – Social engineering prompts users to paste and execute downloaded installer commands in Terminal, tricking victims into running malicious scripts (“prompting visitors to paste base64-encoded commands in Terminal, which downloads a secondary payload from remote infrastructure”).
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – The attack uses layered shell invocations (/bin/sh -> /bin/bash -> sudo /bin/zsh) to execute payloads and complicate analysis (“/bin/sh spawns /bin/bash, which invokes sudo to run /bin/zsh”).
- [T1543.003 ] Create or Modify System Process: Launchctl – Malware issues launchctl kill SIGTERM against OneDrive updater daemons to disrupt backup/sync processes (“the malware issues launchctl kill SIGTERM commands targeting Microsoft OneDrive updater daemons”).
- [T1064 ] Scripting – Installer scripts fetched via curl perform actions like xattr -c, chmod +x and execution to bypass Gatekeeper and run payloads (“curl -o /tmp/update …; xattr -c /tmp/update; chmod +x /tmp/update; /tmp/update”).
- [T1063 ] Security Software Discovery – The malware enumerates system hardware and memory via system_profiler to fingerprint the environment and detect analysis sandboxes (“system_profiler SPMemoryDataType and system_profiler SPHardwareDataType to collect detailed hardware and memory information”).
- [T1497 ] Virtualization/Sandbox Evasion – Anti-analysis checks using osascript and system_profiler search for virtualization markers and exit if found to avoid execution in analysis environments (“the script searches for virtualization markers such as ‘QEMU’, ‘VMware’, or ‘KVM’ … if any indicator is found, the script exits with code 100”).
- [T1078 ] Valid Accounts – The payload attempts privilege escalation via sudo invocations that may leverage cached or misconfigured sudoers to gain elevated privileges (“the payload explicitly attempts to escalate privileges by invoking sudo /bin/zsh -c /Users/run/”).
- [T1595 ] Active Scanning – Use of passive DNS and web crawler hunts to discover and map 85 phishing domains and reuse patterns across infrastructure (“Passive DNS data showed these domains were part of an interconnected network” and “This hunt returned 85 unique hostnames”).
Indicators of Compromise
- [IP ] Backend hosting/phishing infrastructure – 93.152.230[.]79 (linked to fake Homebrew sites), 195.82.147[.]38 (secondary host reusing trading.example.com certificate)
- [Domain ] Phishing/impersonation domains used to deliver payloads – homebrewonline[.]org, homebrewupdate[.]org (and other Homebrew-impersonating domains like homebrewclubs[.]org, homebrewfaq[.]org)
- [Domain ] Additional spoofed service domains – logmeln[.]com, logmeeine[.]com (typosquat), tradingviewen[.]com (and other impersonation domains sites-phantom[.]com, filmoraus[.]com)
- [URL / File ] Installer and payload paths – https://bonoud.com/get3/install.sh (installer), https://bonoud.com/get6/update (payload) – installer fetches to /tmp/update and executes after xattr -c and chmod +x
- [Artifact ] Command patterns and clipboard fragments – base64-encoded curl fragments and strings such as ‘Y3VybCAtcy’ or ‘5zaA==’ used in pages to embed installer commands (and 1 more base64 fragment example observed)
Read more: https://hunt.io/blog/macos-odyssey-amos-malware-campaign