Netskope discovered a new Python-based remote access trojan that impersonates a Minecraft client named “Nursultan Client” and uses the Telegram Bot API as its command-and-control channel to steal Discord tokens, capture screenshots and webcam images, and perform system reconnaissance. The sample includes a hardcoded Telegram bot token and allowed user ID, demonstrates cross-platform C2 capabilities despite flawed Windows persistence, and appears to be a Malware-as-a-Service offering signed “by fifetka”. #NursultanClient #TelegramBotAPI
Keypoints
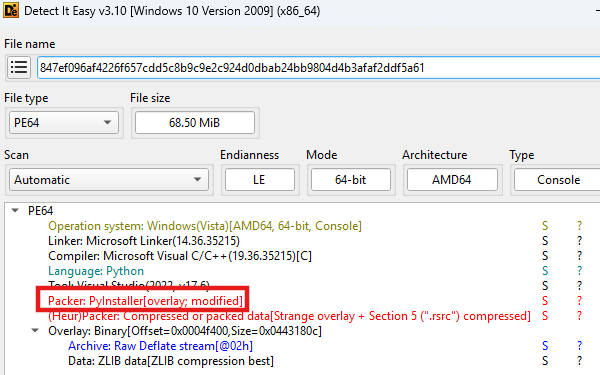
- Netskope found a multi-function Python RAT packaged with PyInstaller that masquerades as “Nursultan Client” to trick gamers.
- The malware uses the Telegram Bot API as its C2 channel with a hardcoded bot token and allowed Telegram user ID to receive commands and exfiltrate data.
- Main capabilities include stealing Discord authentication tokens, system profiling (/info), screenshots and webcam capture (/screenshot, /camera), and showing/opening arbitrary text, URLs, and images.
- The malware’s core C2 and several surveillance features use cross-platform libraries and can operate on Windows, Linux, and Darwin, though persistence and some features are Windows-specific.
- Persistence attempts create a “NursultanClient” registry Run key but are likely to fail due to incorrect paths when compiled with PyInstaller.
- The author signs reports as “by fifetka” and the malware’s design suggests a MaaS model where the ALLOWED_USERS ID serves as a simple licensing mechanism.
- Despite broad functionality, coding mistakes, lack of advanced anti-analysis, and flawed persistence indicate the author is not highly sophisticated.
MITRE Techniques
- [T1543] Create or Modify System Process – Adds a registry Run key named “NursultanClient” under HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun to achieve persistence; “attempts to add itself to the Windows startup process by creating a registry key named ‘NursultanClient’”.
- [T1588] Acquire Infrastructure – Uses Telegram Bot API as a C2 channel with a hardcoded bot token and allowed user IDs to manage infected hosts; “contains a hardcoded Telegram Bot Token (‘8362039368:AAGj_jyw6oYftV2QQYiYoUslJOmXq6bsAYs’) and a hardcoded list of allowed Telegram user IDs (‘6804277757’)”.
- [T1056] Input Capture – Captures screenshots and webcam photos via commands (/screenshot, /camera) and exfiltrates the images over Telegram; “allow the attacker to capture a live screenshot of the victim’s desktop or take a photo using the computer’s webcam”.
- [T1537] Transfer Data to Cloud Account – Exfiltrates stolen Discord tokens, system profiles, and captured media through the Telegram bot channel to the attacker; “All data is exfiltrated to the attacker through this same Telegram channel”.
- [T1530] Data from Cloud Storage Objects – Searches local browser and Discord client storage (LevelDB, SQLite, .ldb/.log) to locate Discord authentication tokens and exfiltrates them; “searches for tokens in the local storage files (‘.ldb’ and ‘.log’) of Discord clients… and user data directories of major web browsers”.
- [T1204] User Execution – Uses social engineering by masquerading as a legitimate Minecraft client and displaying a fake installation progress bar to trick users into running the executable; “prints a fake installation progress bar to the console, using the name ‘Nursultan client’ to impersonate legitimate software”.
- [T1304] Social Engineering – Displays attacker-sent text or images as pop-ups or opens attacker-sent URLs in the victim’s browser for adware/phishing purposes; “If the attacker sends a text message… the text is displayed on the victim’s screen in a pop-up message box” and images are opened in the default viewer.
Indicators of Compromise
- [File Hash] Sample executable – SHA256: 847ef096af4226f657cdd5c8b9c9e2c924d0dbab24bb9804d4b3afaf2ddf5a61
- [Telegram Bot Token] Embedded C2 credential – 8362039368:AAGj_jyw6oYftV2QQYiYoUslJOmXq6bsAYs
- [Telegram User ID] Allowed operator identifier – 6804277757
- [Registry Key] Persistence artifact (Windows) – HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun -> “NursultanClient”
- [File/Artifact Names] Targeted storage locations for token theft – Discord local storage files (‘.ldb’, ‘.log’), browser user data LevelDB/SQLite (e.g., Chrome, Edge, Firefox, Opera, Brave)
Read more: https://www.netskope.com/blog/new-python-rat-targets-gamers-via-minecraft