A phishing kit named Tykit uses SVG files embedding obfuscated JavaScript to rebuild payloads, redirect users through trampoline/CAPTCHA steps, and exfiltrate Microsoft 365 credentials via staged POST requests to C2 endpoints. Analysis links many samples to templated domains (e.g., segy*.cc, loginmicr*…*.cc) and consistent client-side logic, indicating a mature PhaaS-style infrastructure. #Tykit…
Category: Threat Research
PassiveNeuron is a multi-stage cyberespionage campaign that targeted Windows servers across Asia, Africa, and Latin America from 2024–2025 using novel implants Neursite and NeuralExecutor, Cobalt Strike, DLL loader chains, and SQL-server-based initial access attempts. Analysis ties some TTPs (Dead Drop Resolver via GitHub delimiters, Phantom DLL Hijacking, MAC-based sandbox checks) to Chinese-speaking threat actors, with low confidence; PDB and behavior overlaps also link one dropped DLL to activity noted by Cisco Talos. #Neursite #NeuralExecutor

Copilot Studio agents can be configured to redirect users to arbitrary OAuth consent flows and exfiltrate tokens, enabling OAuth phishing attacks that leverage legitimate Microsoft domains and services. The technique abuses agent sign-in topics and HTTP actions to forward User.AccessToken to attacker-controlled endpoints, affecting Entra ID tenants and administrative roles. #CopilotStudio #EntraID

COLDRIVER rapidly replaced its publicly disclosed LOSTKEYS toolset with a new, evolving family of malware—NOROBOT (DLL downloader), YESROBOT (Python backdoor), and MAYBEROBOT (PowerShell backdoor)—delivered via an updated COLDCOPY “ClickFix” lure that tricks users into running a DLL with rundll32. Google Threat Intelligence observed multiple NOROBOT variants, infrastructure rotation, and operational changes aimed at evasion while MAYBEROBOT became the preferred, more extensible final backdoor. #NOROBOT #MAYBEROBOT
StealthServer is a Golang-based cross-platform backdoor (Windows and Linux) that steals files and executes C2 commands while using junk code, anti-analysis checks, and diverse loaders (.desktop, malicious PPT macros) to evade detection. Observed infrastructure and lure themes targeting a South Asian country suggest possible links to APT36 through domain naming patterns and reuse of delivery tactics. #StealthServer #APT36
Scattered LAPSUS$ Hunters conducted Salesforce data theft extortion, leaked alleged PII from six companies across aviation, energy, and retail, and advertised an extortion-as-a-service (EaaS) model and insider recruitment on Telegram. The group also claimed development of a new ransomware called SHINYSP1D3R and signaled a potential pause in activity; #ScatteredLAPSUS$Hunters #SHINYSP1D3R…

Varonis researchers discovered that invisible Unicode characters allowed attackers to bypass Microsoft’s reserved-name safeguards and register malicious Azure applications with deceptive names like “Azure Portal,” enabling illicit consent grants and device code phishing to obtain access tokens without stealing passwords. Microsoft patched the initial vulnerability in April 2025 and a broader…
Fortinet uncovered an August 2025 SEO-poisoning campaign that used malicious SEO plugins and look-alike domains to lure Chinese-speaking users into downloading fake software, resulting in installations of Hiddengh0st and Winos variants. The investigation identified 13 initial IoCs (five domains, four subdomains, four IPs), narrowed to nine primary IoCs for DNS analysis, and expanded to reveal 7,741 email-connected domains and additional malicious IPs. #Hiddengh0st #Winos

The ICO report details a March 2023 BlackBasta ransomware attack on Capita that led to exfiltration of over six million individuals’ records and a £14 million fine, with systemic detection, containment, and AD privilege-management failures enabling the breach. Post-incident analysis highlights operator TTPs including credential harvesting, lateral movement using a backupadmin…
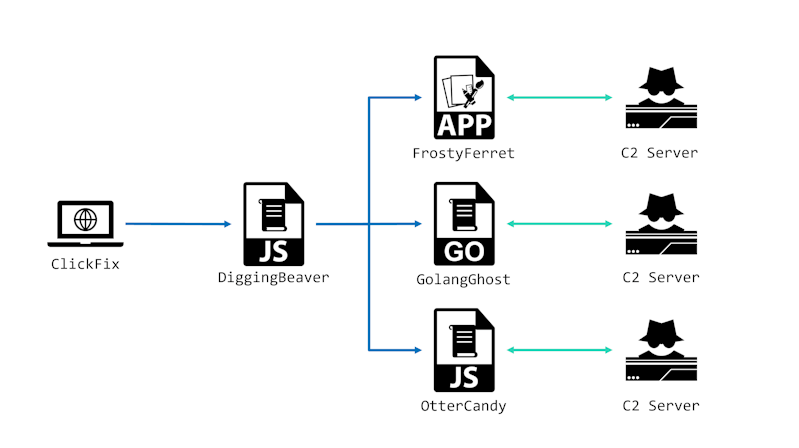
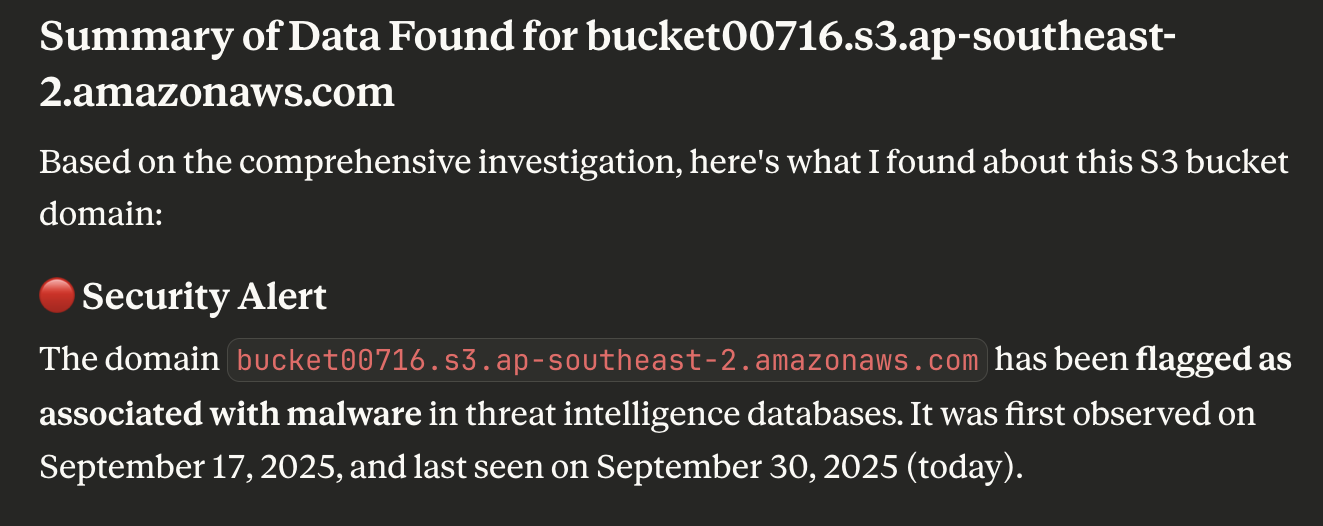
WaterPlum Cluster B (BlockNovas) has been observed distributing a new Node.js RAT/infostealer named OtterCandy across Windows, macOS, and Linux to steal browser credentials, crypto wallets, and files via Socket.IO-connected C2 servers. An August 2025 update (v2) added client_id for improved victim identification, expanded browser-extension theft targets, full Chromium data exfiltration, and…
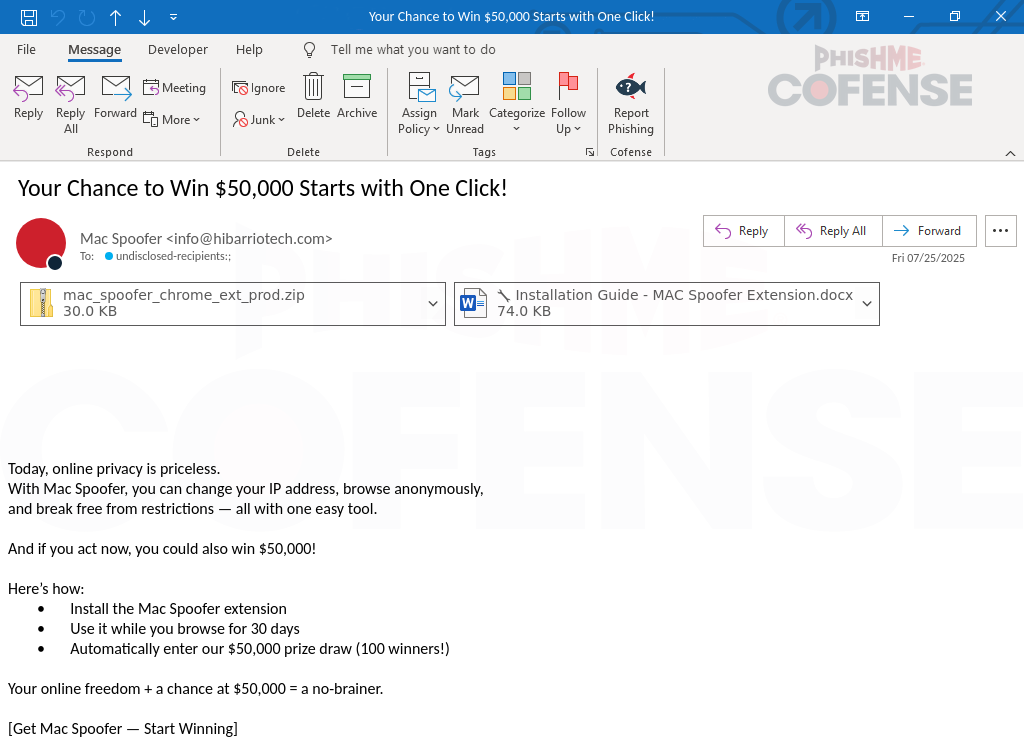
Cofense PDC discovered a phishing campaign delivering a malicious Chrome extension named “Mac Spoofer” via a ZIP attachment that, when sideloaded, captures credentials and exfiltrates them to reader.hibarriotech[.]com/api/send-anything. The extension was distributed with step-by-step installation instructions and a social-engineering lure promising $50,000 to compel installation and 30 days of use. #MacSpoofer #hibarriotech
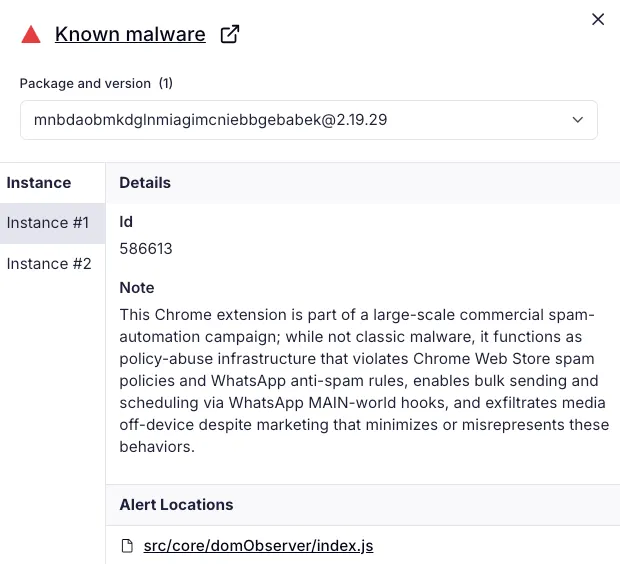
A cluster of 131 rebranded Chrome extensions share a single codebase that injects into WhatsApp Web to automate bulk messaging and scheduling, enabling large-scale spam and evasion of WhatsApp anti-spam controls while violating Chrome Web Store and WhatsApp policies. The operation uses a white‑label reseller/franchise model (DBX Tecnologia / Grupo OPT) to distribute near-identical clones across dozens of listings and marketing sites, accounting for at least 20,905 active users. #DBXTecnologia #GrupoOPT
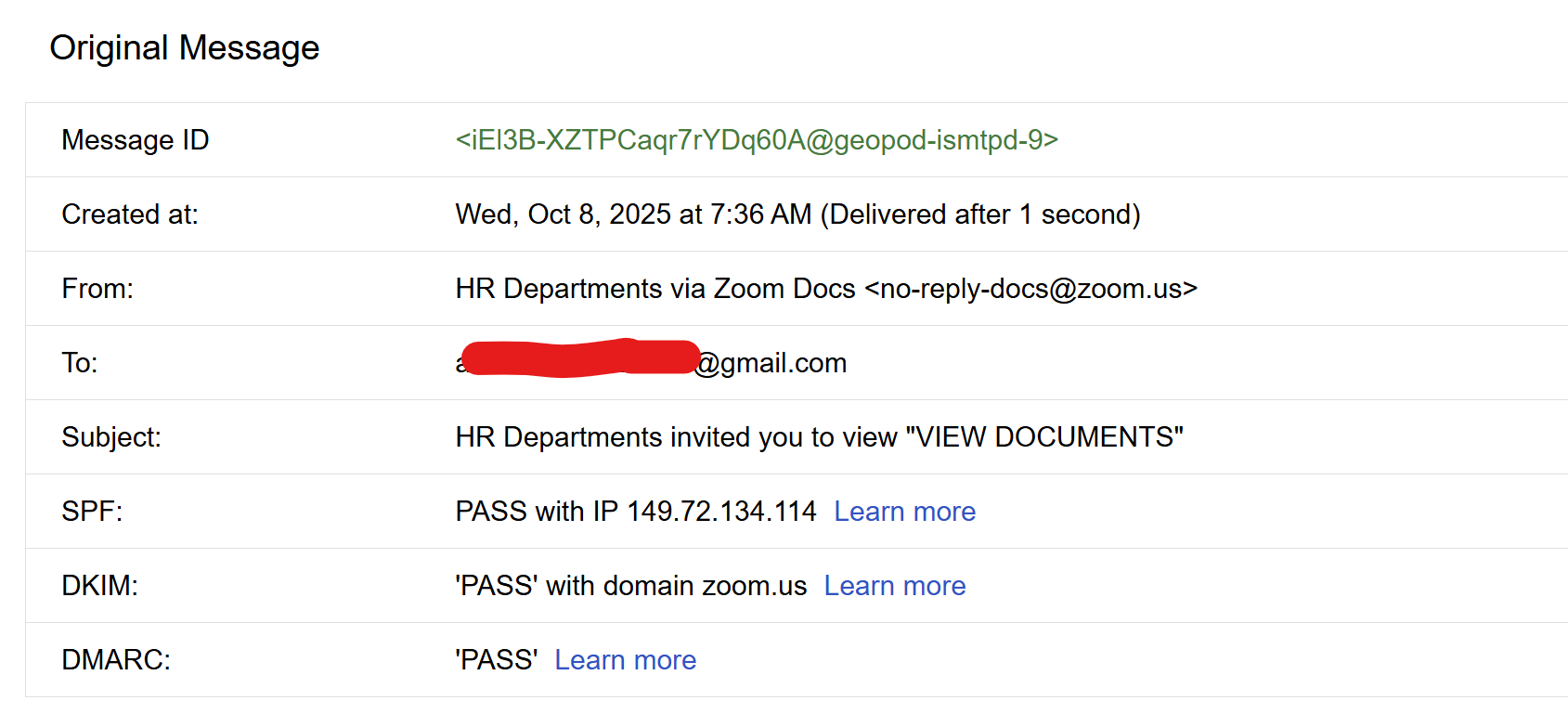
An attacker abused Zoom’s legitimate document-sharing notifications to deliver a link that redirected victims through a fake “bot protection” gate to a Gmail credential-phishing page which exfiltrated credentials in real time over a WebSocket and validated them on the backend. #overflow.qyrix.com.de #WebSocket…
Mustang Panda (China-Nexus) delivered a politically themed phishing payload in June 2025 that used DLL side-loading with a hidden libjyy.dll to load a Claimloader which decrypts strings, establishes persistence, and deploys a Publoader shellcode via API hashing and callback abuse. The campaign used file attribute obfuscation, multiple string decryption routines (single-byte…
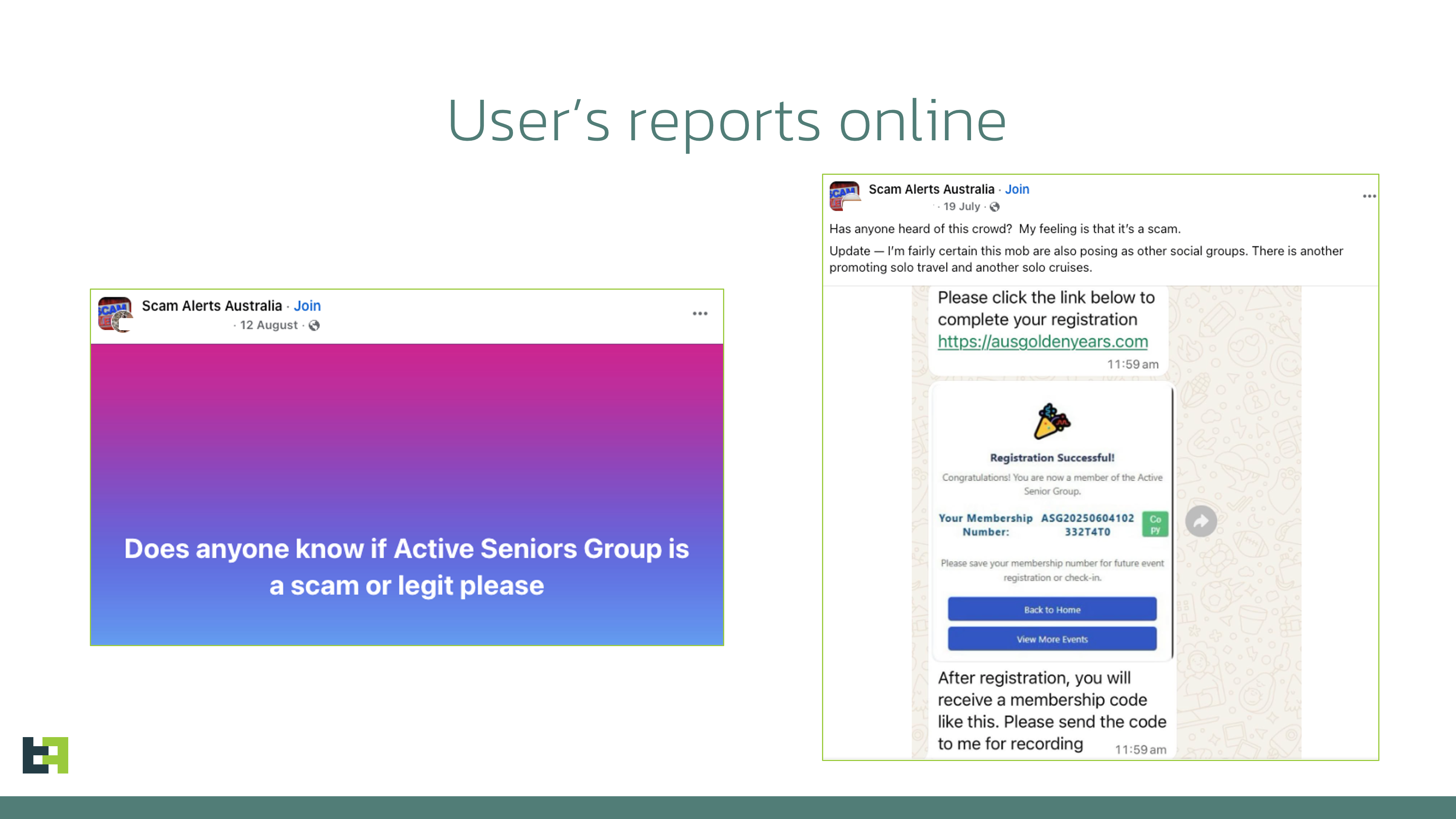
ThreatFabric discovered a Device-Takeover Android Trojan named Datzbro used in social-engineering campaigns that targeted seniors via fake Facebook groups promoting “active senior trips,” enabling remote control, audio/video capture, keylogging, and banking-focused accessibility logging. The malware’s C2 application and builder were leaked, making Datzbro freely available to global threat actors and expanding…