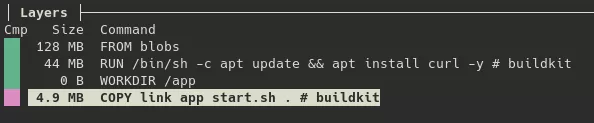
Synacktiv CSIRT analyzed a multi-stage compromise on AWS where a malicious Docker image (kvlnt/vv) led to deployment of vGet (a Rust downloader) and LinkPro, an eBPF-based Linux rootkit that hides via eBPF and ld.so.preload and activates on a specific “magic packet”. The report details LinkPro’s components (Hide and Knock eBPF modules,…
Category: Threat Research

The author demonstrates a technique to inject code into antivirus-protected processes by cloning protected services and replacing a Cryptographic Provider with a malicious, digitally-signed DLL to load during service initialization. The proof-of-concept tool IAmAntimalware (with CertClone for signing) successfully injected SampleDll.dll into Bitdefender, Trend Micro, and Avast processes, allowing file writes…

A polymorphic Python RAT named “nirorat.py” was found on VirusTotal (SHA256:7173e20e7ec217f6a1591f1fc9be6d0a4496d78615cc5ccdf7b9a3a37e3ecc3c) that uses self-modifying techniques (inspect, XOR packing, marshal/zlib) and advanced polymorphic transformations to evade detection. It exposes many remote-access features (network scanning, spreading, file operations, audio/screen capture, cryptomining, and commands to deploy payloads) and logged low detection (2/64). #nirorat #Xworm…
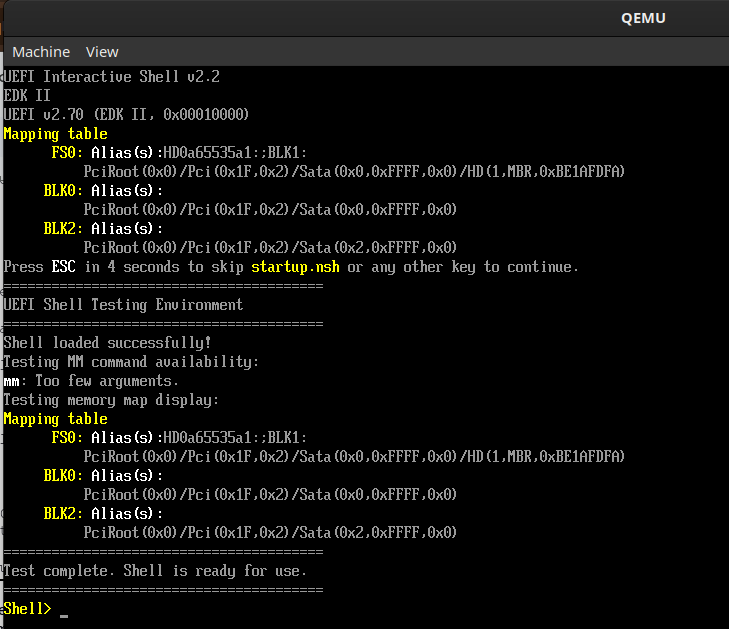
Researchers discovered that signed UEFI shells containing an “mm” memory-modify command can be used to bypass Secure Boot on many systems by overwriting the Security Architectural Protocol handler, enabling pre-OS arbitrary code execution and persistence. Framework-distributed signed shells affecting roughly 200k devices were found vulnerable, and mitigations include DBX revocations, firmware…

The article demonstrates debugging a technique where a VEH handler emulates execution of shellcode stored in non-executable .data memory using chained hardware breakpoints so the memory protection never changes. #Win32HWBPs #MyExceptionHandler…

Singularity is a Loadable Kernel Module (LKM) rootkit for Linux 6.x that implements ftrace-based syscall hooking, multi-layered process/file/network hiding, privilege escalation, module self-hiding, and extensive log sanitization to evade detection. The project supplies dual-architecture (x86_64 and ia32) hooks, tmpfs OPSEC guidance, and anti-forensic scripts; source: https://github.com/MatheuZSecurity/Singularity #Singularity #ftrace…

Since late 2023, UNC5142 has used compromised WordPress sites and a multistage JavaScript downloader called CLEARSHORT that leverages BNB Smart Chain smart contracts (EtherHiding) to deliver infostealers such as VIDAR, LUMMAC.V2, RADTHIEF, and ATOMIC. The actor evolved from single-contract Base64 delivery to a three-level AES-encrypted smart contract architecture, abused Cloudflare Pages for lures, and paused observable activity after July 23, 2025. #UNC5142 #CLEARSHORT #EtherHiding #VIDAR #RADTHIEF #LUMMAC.V2 #ATOMIC

Cavalry Werewolf used targeted phishing against Russian organizations by spoofing or compromising Kyrgyz governmental email addresses to deliver RAR attachments containing FoalShell or StallionRAT. The malware provides remote shell access and Telegram-controlled RAT functions, enabling command execution, persistence, data exfiltration, and SOCKS5 proxying. #FoalShell #StallionRAT

Google Threat Intelligence Group (GTIG) observed North Korean actor UNC5342 use EtherHiding—storing and retrieving malicious JavaScript payloads from smart contracts on BNB Smart Chain and Ethereum—to deliver JADESNOW and ultimately the INVISIBLEFERRET backdoor, enabling cryptocurrency theft and data exfiltration. The campaign leverages social engineering (fake interviews, malicious repo downloads), centralized API providers for blockchain reads, and frequent on-chain updates to evade takedowns and complicate mitigation. #UNC5342 #JADESNOW #INVISIBLEFERRET
F5 disclosed that a sophisticated nation-state actor gained persistent access to development systems, exfiltrating portions of BIG-IP source code and information on undisclosed vulnerabilities. F5 reports no evidence of modified code, active exploitation, or leaked critical/RCE vulnerabilities, and agencies are urged to inventory and patch F5 products. #BIG-IP #F5

FortiGuard Labs tracked a cross-border campaign that evolved from Winos 4.0 attacks in Taiwan to new HoldingHands variants impacting Taiwan, Japan, China, and Malaysia, using phishing PDFs/HTML/Excel lures and cloud or custom domains for payload delivery. Investigation linked incidents via shared Tencent Cloud APPIDs, common domains/IPs (e.g., 156[.]251[.]17[.]9), code reuse (BackDoor.pdb, svchost.ini), and operational tactics like Task Scheduler-triggered execution. #HoldingHands #Winos4.0
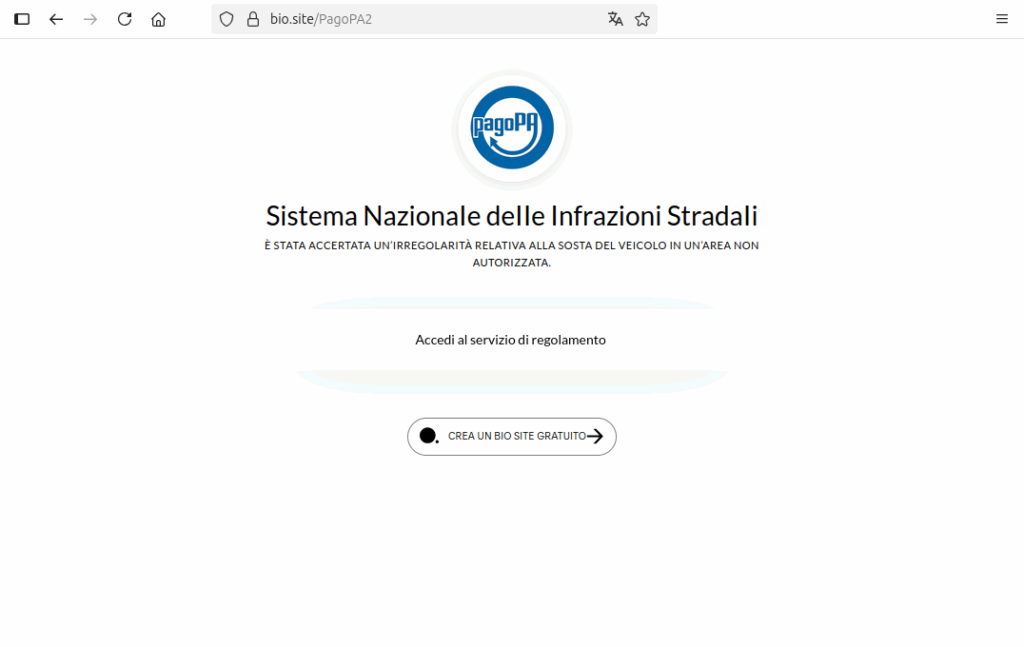
CERT-AGID has observed a new PagoPA-themed phishing campaign that uses Google open-redirect parameters to make malicious links appear legitimate and bypass automated checks. The attack chain leverages legitimate services (Google adservice, bio.site, privatedns.org) to host intermediate pages and a final phishing form that harvests personal and payment card data. #PagoPA #adservice.google.be

Recorded Future’s Insikt Group identified sixteen high-impact vulnerabilities in September 2025 that should be prioritized for remediation, a slight decrease from August’s eighteen, with Cisco and TP-Link accounting for six of the sixteen issues and several vulnerabilities enabling RCE or command injection. Threat actors exploited Cisco ASA flaws (CVE-2025-20333, CVE-2025-20362) to deploy RayInitiator and LINE VIPER and abused Sitecore CVE-2025-53690 to deliver WEEPSTEEL, EARTHWORM, and SharpHound. #CVE-2025-20333 #CVE-2025-53690

WhoisXML API reduced the false positive rate of its First Watch Malicious Domains Data Feed from 3% to 1.66% by refining machine learning models, expanding training data, improving reputation signals, and addressing name-based biases. This improvement yields more accurate predictive threat intelligence and fewer interruptions for security teams. #FirstWatch #WhoisXMLAPI
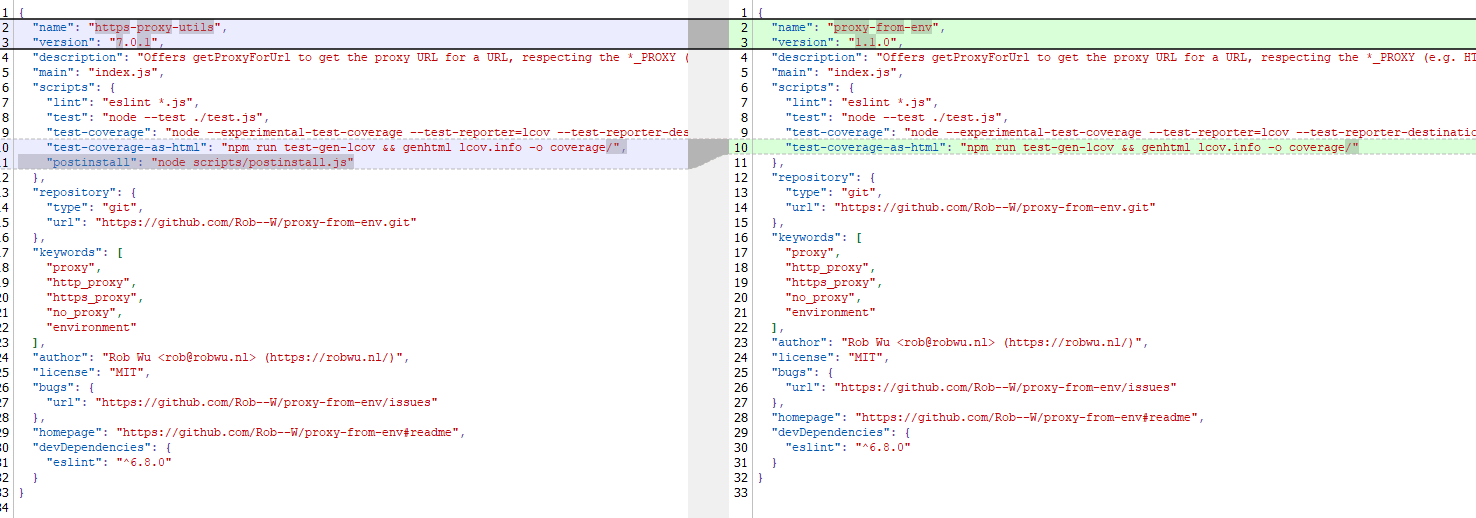
A malicious npm package named https-proxy-utils was published and used to deliver the AdaptixC2 post-exploitation agent via a post-install script that deployed OS-specific payloads for Windows, macOS, and Linux. The campaign abused trusted open-source package names and supply-chain mechanisms, using DLL sideloading on Windows, LaunchAgents on macOS, and /tmp delivery on Linux to achieve persistence and remote access. #AdaptixC2 #https-proxy-utils