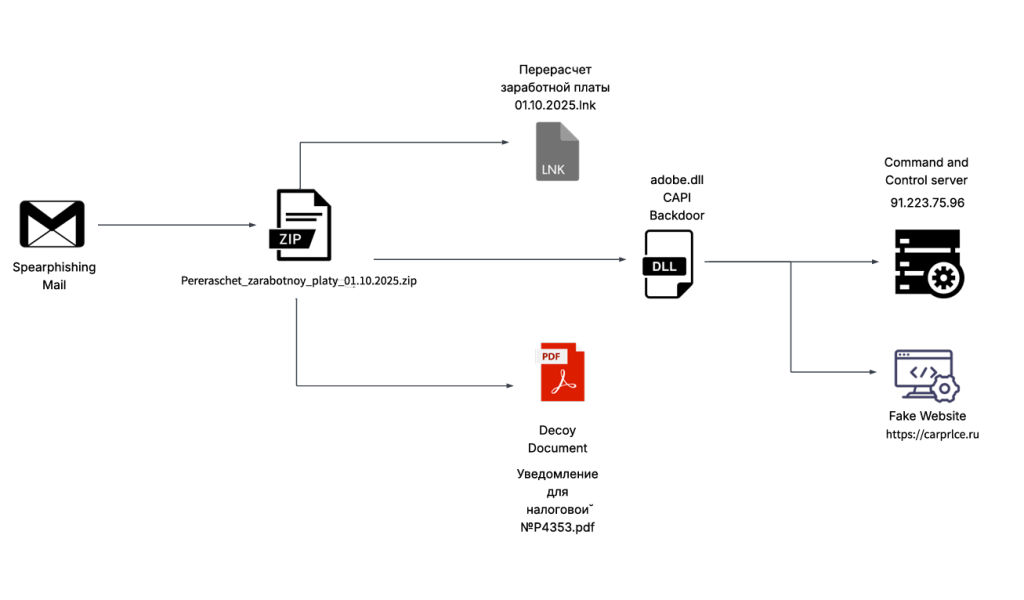
Seqrite Labs uncovered a spear-phishing campaign targeting the Russian automobile and e‑commerce sectors that used a malicious ZIP with a decoy PDF/LNK to execute a .NET backdoor dubbed CAPI Backdoor. The implant performs reconnaissance, browser data theft, screenshots, persistence via Startup LNK and Scheduled Task, and communicates with C2 infrastructure such as carprlce[.]ru and IP 91.223.75[.]96. #CAPI_Backdoor #carprlce.ru
Keypoints
- SEQRITE Labs discovered a campaign (first observed 3 Oct 2025) targeting Russia’s automobile-commerce and e‑commerce industries using a spear-phishing ZIP named Перерасчет заработной платы 01.10.2025 (Payroll Recalculation).
- The ZIP contained a malicious LNK that launches a .NET DLL (adobe.dll / client6.dll, dubbed CAPI Backdoor) via rundll32.exe to execute the implant.
- The decoy documents (Notification for the Tax Office No. P4353.pdf and adobe.xml) lure victims with tax-related content while the LNK triggers the payload.
- CAPI Backdoor capabilities include privilege checks, AV enumeration via WMI, opening the decoy PDF, C2 communication over TCP port 443, command execution, browser data theft (Chrome/Edge/Firefox), screenshots, and system information collection.
- Virtual machine detection and multiple anti-analysis checks are implemented (hypervisor, SMBIOS, PnP, disk/video/MAC/GPU/battery/OEM checks) to avoid sandbox/VMs.
- Persistence is achieved by copying the implant to the user Roaming Microsoft folder and creating Microsoft.lnk in Startup, and by registering a scheduled task (AdobePDF) that runs rundll32.exe with the implant.
- Infrastructure includes a DGA-generated domain and a typo-squatted fake site carprlce[.]ru redirecting to hosted C2; hosting observed under ASN AS197695 and ASN 39087 (P.a.k.t LLC); relevant IOCs and file hashes were published.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – The campaign used a malicious ZIP containing decoy PDF and LNK to deliver the implant. Quote: ‘the ZIP had been used as preliminary source of spear-phishing based infection containing decoys with PDF and LNK extensions.’
- [T1204.002 ] User Execution: Malicious File (LNK) – The LNK file is designed to be executed by the user to run the payload. Quote: ‘the sole purpose of the LNK is just to run the malicious DLL implant CAPI using a Windows Utility known as rundll32.exe.’
- [T1218.011 ] Signed Binary Proxy Execution: rundll32.exe – The actor uses rundll32.exe to execute the .NET DLL export function ‘config’. Quote: ‘it is trying to execute the export function known as config which will perform malicious tasks leveraging the LOLBIN.’
- [T1564.001 ] Hide Artifacts: Hidden Files and Directories – The implant copies itself into AppDataRoamingMicrosoft and hides by using startup mechanisms. Quote: ‘copies the implant into Microsoft folder under the user’s roaming Application Data folder. It then creates LNK file named Microsoft.lnk, saves into the Current user’s Startup folder.’
- [T1047 ] Windows Management Instrumentation (WMI) – The malware queries WMI to enumerate installed antivirus products. Quote: ‘av – This function checks for all the installed Antivirus software … using the query SELECT * FROM AntiVirusProduct using WMI.’
- [T1083 ] File and Directory Discovery – The implant enumerates Local State and browser profile directories to collect data. Quote: ‘iterate through all the files and folders available in the Local State folder including the encrypted key of edge browser.’
- [T1555.003 ] Credentials from Web Browsers – The backdoor steals browser data including history, bookmarks, extensions and encrypted keys. Quote: ‘stores all the data such as Bookmarks, History, Favicons, Top Sites, Preferences, Extensions.’
- [T1113 ] Screen Capture – The implant captures screenshots with date/time and exfiltrates them. Quote: ‘This function takes screenshot of the current user screen and also marks the date and time and send the image in png format to the C2 Server.’
- [T1071.001 ] Application Layer Protocol: Web Protocols – The implant connects to C2 over TCP port 443 to receive commands. Quote: ‘Connect is contacting the C2 server 223.75.96 using TCP Client at port 443.’
- [T1041 ] Exfiltration Over C2 Channel – Stolen data (browser profiles, screenshots, system info) are zipped and sent to the C2 server. Quote: ‘stores all the collected data into a ZIP file … and send it to the C2 server.’
Indicators of Compromise
- [File Hash ] Malicious archive and components – c6a6fcec59e1eaf1ea3f4d046ee72ffe (Pereraschet_zarabotnoy_platy_01.10.2025.zip), c0adfd84dfae8880ff6fd30748150d32 (adobe.dll)
- [File Hash ] Malicious LNK – 957b34952d92510e95df02e3600b8b21 (Перерасчет заработной платы 01.10.2025.lnk)
- [Domain ] Malicious/typo-squatted domain used in campaign – hxxps://carprlce[.]ru (impersonates carprice[.]ru)
- [IP Address ] Command and Control – 91.223.75[.]96 (C2 callback observed; note original reference to 223.75.96 in text)
- [File Name ] Lure and payload filenames – Перерасчет заработной платы 01.10.2025.lnk (decoy LNK), Уведомление для налоговой №P4353.pdf (decoy PDF), adobe.dll / client6.dll (CAPI Backdoor)
Read more: https://www.seqrite.com/blog/seqrite-capi-backdoor-dotnet-stealer-russian-auto-commerce-oct-2025/