A phishing SMS campaign impersonating Robinhood uses urgent “suspicious activity” warnings and fake login pages to harvest account credentials and additional personal data like tax documents and SSNs. Reported malicious domains include www-robinhood.cweegpsnko[.]net and www-robinhood.fflroyalty[.]com. #www-robinhood.cweegpsnko.net #www-robinhood.fflroyalty.com
Keypoints
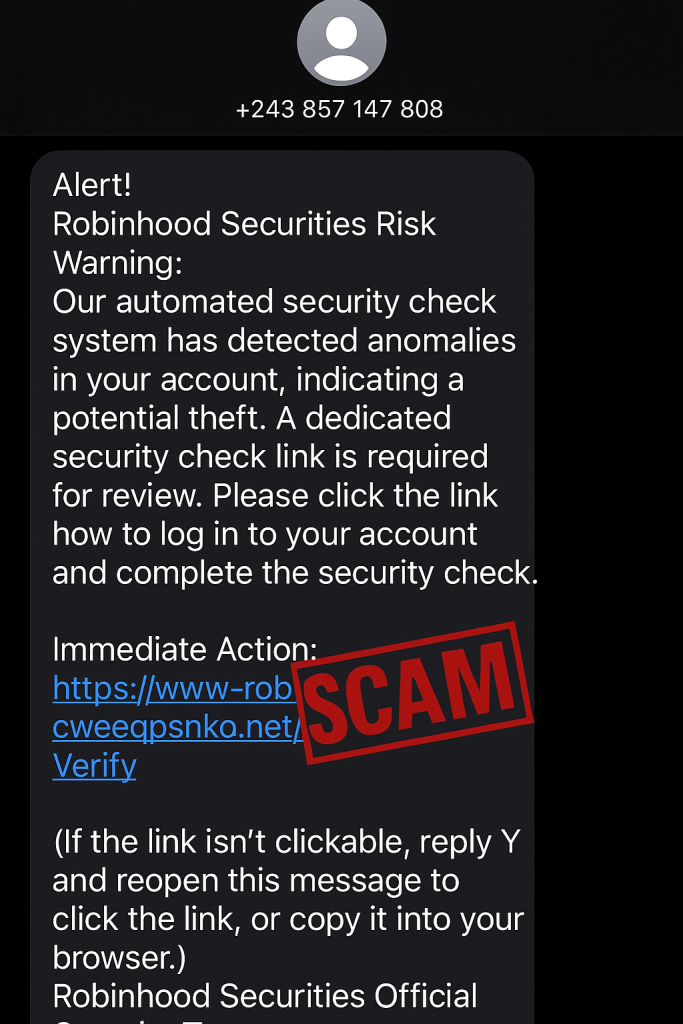
- Phishing texts impersonate Robinhood, claiming automated security checks detected anomalies and urging “Immediate Action.”
- Texts originate from foreign numbers (example: +243), which is inconsistent with a US-based service.
- Messages contain fake domains designed to mimic robinhood.com and include instructions to reply “Y” to enable link access.
- Visiting the links shows convincing fake Robinhood login pages that steal credentials and may redirect to the real site after “verification.”
- Scammers may also harvest sensitive personal information such as tax documents, full name, Social Security number, and bank account details.
- Safety advice: do not reply or follow unsolicited links, never share SSNs or bank details, contact companies via official channels, and use up-to-date real-time anti-malware with web protection.
- Malwarebytes Scam Guard can be used to submit suspicious messages that will be flagged.
MITRE Techniques
- [T1598] Phishing – Use of SMS messages impersonating Robinhood to trick users into visiting fraudulent login pages: ‘Our automated security check system has detected anomalies in your account, indicating a potential theft. A dedicated security check link is required for review.’
- [T1204] User Execution – Persuading users to respond or click via urgency and instructions like replying “Y” to reopen the message: ‘Immediate Action: https://www-robinhood.cweegpsnko[.]net/Verify (If the link isn’t clickable, reply Y and reopen this message to click the link, or copy it into your browser.)’
- [T1531] Account Discovery / Credential Harvesting – Fake login pages collect Robinhood credentials and may request additional personal data including SSNs and bank info: ‘Logging in there hands the scammers your Robinhood login credentials… some scammers will try to harvest additional personal data from the account, including: Tax documents, Full name, Social Security Number… Bank account information.’
- [T1202] Phishing: Spearphishing Link – Use of lookalike domains to direct victims to malicious sites that mimic the legitimate service: ‘The URL that tries to look like the legitimate robinhood.com website.’
Indicators of Compromise
- [Domain] Malicious phishing domains used to host fake Robinhood pages – www-robinhood.cweegpsnko[.]net, www-robinhood.fflroyalty[.]com (and robinhood-securelogin[.]com, robinhood-verification[.]net).
- [Phone number] Sender country code inconsistent with service location – example: +243 (Democratic Republic of the Congo) used to impersonate a US-based company.