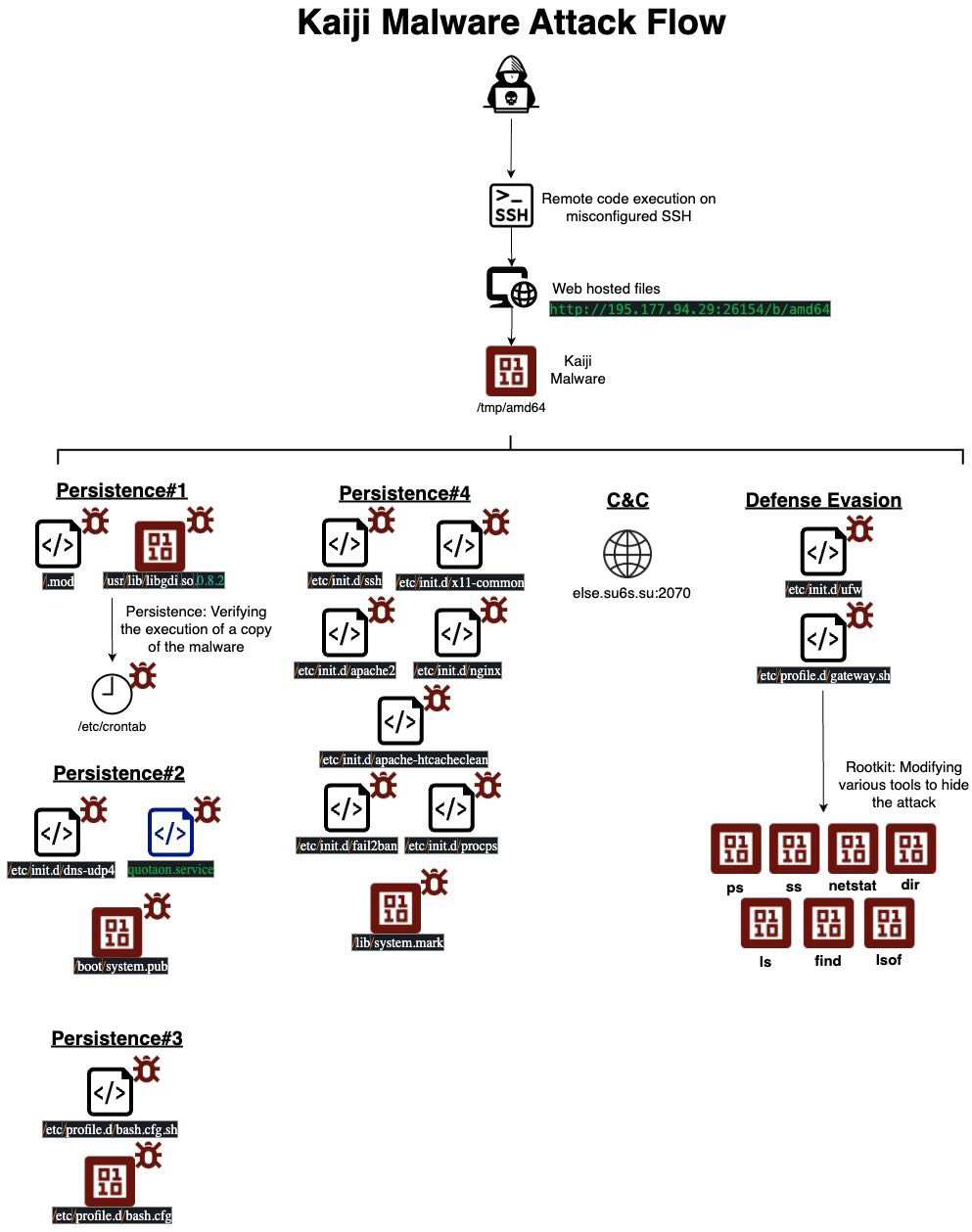
Kaiji is a Linux/IoT-focused Go-based botnet payload that gains access via exposed services (e.g., weak SSH, malicious PoC) and provides multi-protocol DDoS and proxying with rootkit-class stealth. The campaign uses distributed storage and HTTP file servers to host many architecture-specific binaries (e.g., amd64 MD5 fd05b94c016fd2eb7e26c406fa2266d0) and C2 domains such as else.su6s.su/#fd05b94c016fd2eb7e26c406fa2266d0 #su6s.su
Category: Threat Research

Threat actors (including APT28, APT29, Sandworm, and Gamaredon) use a range of living-off-the-land binaries, DLL side‑loading, scheduled task and autorun persistence, credential dumping (Mimikatz, LSASS access), lateral tools (PsExec, Impacket), and cloud/file-host exfiltration to conduct reconnaissance, lateral movement, and C2. Detection recommendations include targeted hunting alerts and queries (for masqueraded XML scheduled tasks, autorun key modifications, unsigned DLL loads, PowerShell/web requests, OAuth abuse in Microsoft 365, and more) plus broader controls like EDR/NDR, defense-in-depth, patching, and logging. #APT28 #APT29

LockBit 5.0 is a cross-platform ransomware family targeting Windows, Linux, and VMware ESXi with advanced obfuscation, DLL reflection, ETW patching, and anti-forensics to evade detection and hinder recovery. It appends randomized 16-character file extensions, clears event logs, and shares code with LockBit 4.0, indicating an evolutionary upgrade. #LockBit5.0 #LockBit4.0

Qilin (aka Agenda) is a RaaS group that has targeted organizations globally since August 2022 using spear-phishing, double extortion, and a portable Go/Rust ransomware that encrypts files with AES-256 or ChaCha20 and appends RSA-encrypted key material to each file. The ransomware disables recovery (shadow copies, event logs, backup/DB services), uses argument-controlled…

Q3 2025 saw a surge in email campaigns using obfuscated JavaScript attachments that act as downloaders to deliver .NET-based information stealers and RATs such as DarkCloud, Remcos, Agent Tesla and Formbook via PowerShell and steganography. Attack chains include ZIP/RAR attachments, base64-embedded payloads in PNG/TXT files, VM/sandbox evasion and process hollowing to exfiltrate data to dynamic DNS, FTP/SMTP, and Google Drive links. #DarkCloud #Remcos #AgentTesla #Formbook
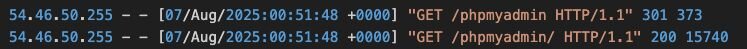
A threat actor used log poisoning via an exposed phpMyAdmin instance to drop a PHP web shell (China Chopper-like) and then deployed Nezha RMM to manage compromised hosts before installing Ghost RAT. The campaign involved infrastructure such as 54.46.50[.]255 and 45.207.220[.]12 and targeted over 100 victims primarily in Taiwan, Japan, South Korea, and Hong Kong. #Nezha #GhostRAT
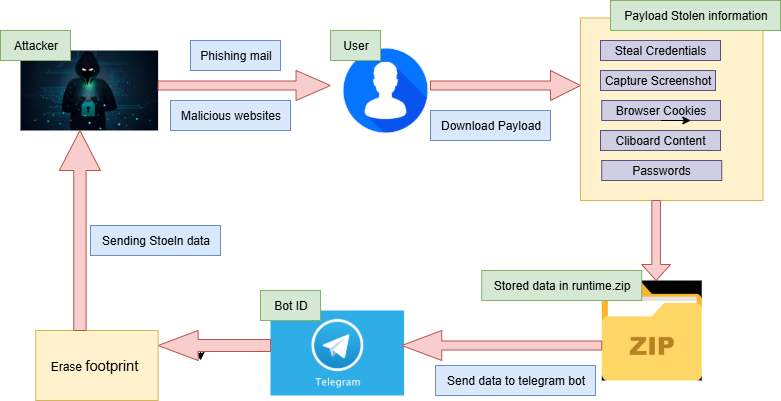
Shuyal Stealer is an infostealer that targets 19 different browsers to harvest browser-stored credentials, Discord tokens, clipboard contents, screenshots, and extensive system hardware/configuration details before exfiltrating data via a hardcoded Telegram bot. It uses WMI for system profiling, disables Task Manager and adds persistence through the Startup folder, then compresses stolen data to runtime.zip, sends it to a Telegram chat, and attempts self-deletion. #Shuyal #TelegramBot
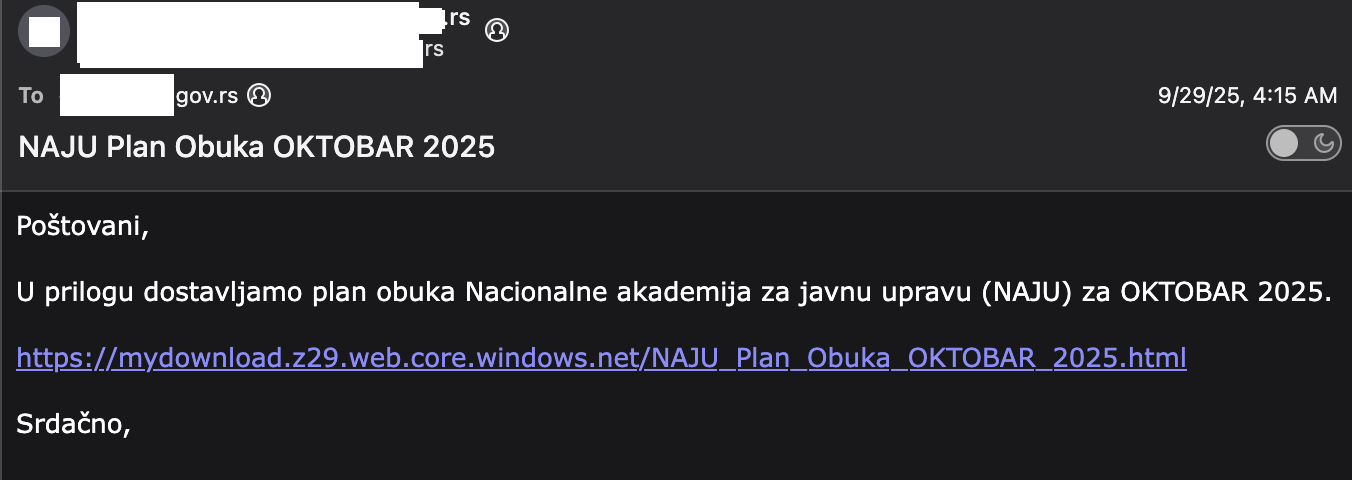
A targeted spearphishing campaign delivered a malicious ZIP containing an LNK that carved and executed embedded payloads (DLL/EXE) sideloaded via a Canon Printer Assistant binary, linked to long-standing SOGU/PlugX/Korplug activity attributed to Chinese actors and focused on espionage. Pivoting from obfuscation patterns and shared filenames revealed related samples across multiple European countries and infrastructure such as mydownload.z29.web.core.windows.net and naturadeco.net. #SOGU #PlugX
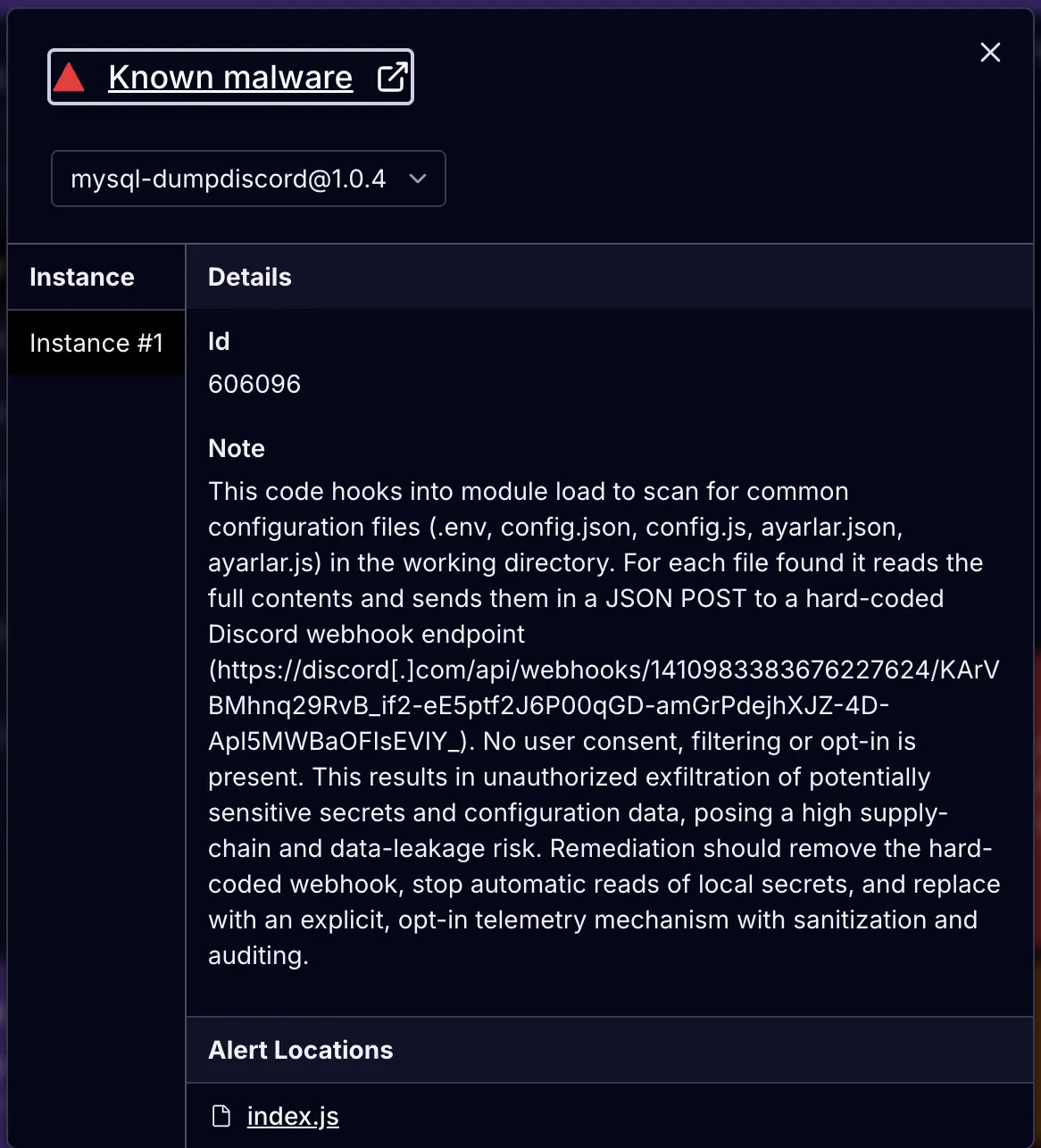
Researchers observed malicious packages on npm, PyPI, and RubyGems using hard-coded Discord webhook URLs to exfiltrate sensitive files and host metadata during install or runtime. These packages collect configuration files, environment secrets, /etc/passwd, public IPs, and other system details and POST them to attacker-controlled Discord channels for telemetry or C2. #DiscordWebhook #sqlcommenter_rails
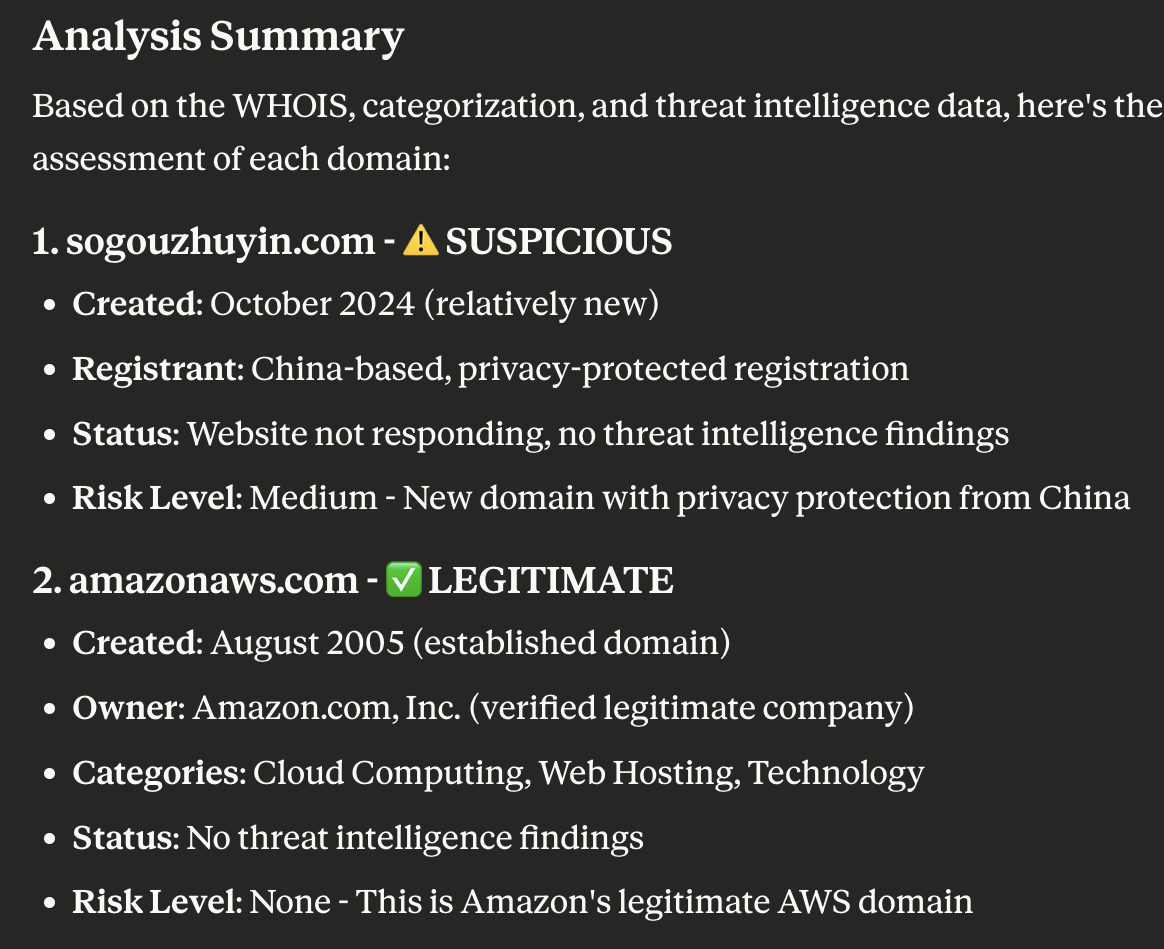
Trend Micro and WhoisXML API investigations into the TAOTH Campaign found targeted social-engineering lures (fake software updates, cloud storage, and login pages) aimed at dissidents, journalists, researchers, and leaders across East Asia and overseas Taiwanese communities. The joint analysis identified domains, subdomains, and IPs tied to the campaign and enriched IoCs with WHOIS, DNS history, geolocation, and traffic-sample data to prioritize eight IoCs for further action. #TAOTH #auth-web[.]com
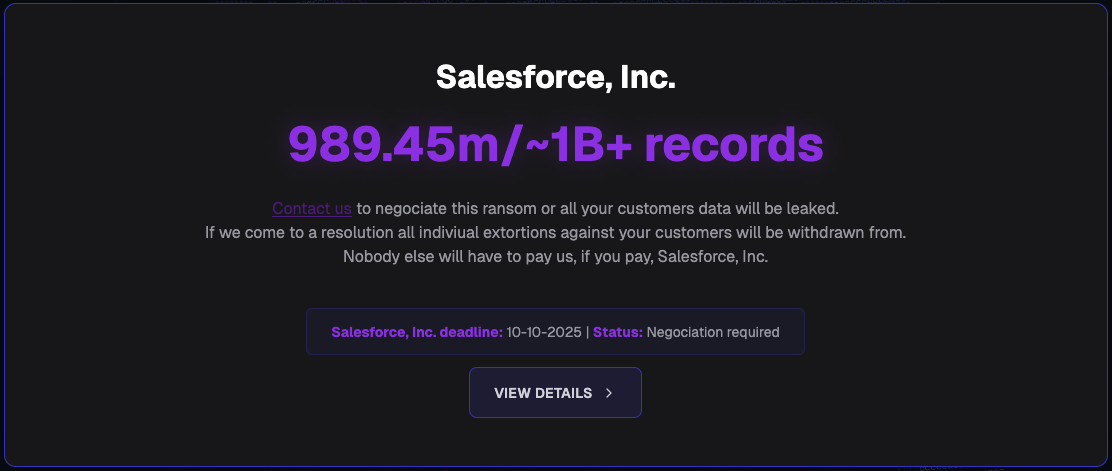
Scattered Lapsus$ Hunters (aka SP1D3R HUNTERS, SLSH) and affiliated groups like Bling Libra and Crimson Collective have been conducting large-scale data theft from Salesforce tenants and other cloud environments and are operating an extortion-as-a-service (EaaS) model to monetize stolen data. The activity has targeted retail and hospitality organizations and cloud providers…
Huntress observed a widespread compromise of SonicWall SSLVPN devices beginning October 4, with rapid authentications across over 100 accounts in 16 customer environments suggesting use of valid credentials rather than brute force. SonicWall disclosed an unrelated-seeming MySonicWall platform breach exposing encrypted firewall backup files, and organizations are urged to follow containment/remediation steps including resetting secrets and enforcing MFA. #SonicWall #MySonicWall
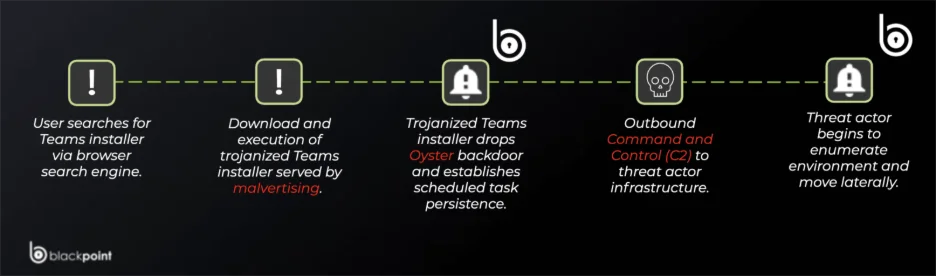
Attackers used SEO poisoning and malicious ads to distribute fake Microsoft Teams installers that drop the Oyster (Broomstick) backdoor, providing persistent C2 access via a malicious DLL, scheduled task CaptureService, and rundll32.exe execution. Key IOCs include domains like teams-install.icu and nickbush24.com, IPs such as 185.28.119.228, and multiple malicious file hashes. #Oyster #nickbush24.com

A WhatsApp Web–based campaign starting on September 29, 2025, targeted Brazilian users by sending ZIP attachments that contained malicious LNK files which launched multi-stage PowerShell payloads to disable defenses and fetch additional malware. The campaign used C2 domains such as zapgrande[.]com and delivered either a Selenium-based session hijacker or a banking trojan called Maverick, with possible links to the earlier Coyote campaigns. #zapgrande #Maverick
FortiGuard Labs observed an active Stealit campaign distributing Node.js-based stealers using the experimental Single Executable Application (SEA) feature and also reverting to Electron, with heavy obfuscation, anti-analysis checks, and multiple payload components for data theft and remote control. The campaign uses commercialized C2 panels (iloveanimals[.]shop / stealituptaded[.]lol), distributes via game/VPN installer lures and file-sharing sites, and targets browsers, messengers, game platforms, and many crypto wallet extensions. #Stealit #iloveanimals.shop