A targeted spearphishing campaign delivered a malicious ZIP containing an LNK that carved and executed embedded payloads (DLL/EXE) sideloaded via a Canon Printer Assistant binary, linked to long-standing SOGU/PlugX/Korplug activity attributed to Chinese actors and focused on espionage. Pivoting from obfuscation patterns and shared filenames revealed related samples across multiple European countries and infrastructure such as mydownload.z29.web.core.windows.net and naturadeco.net. #SOGU #PlugX
Keypoints
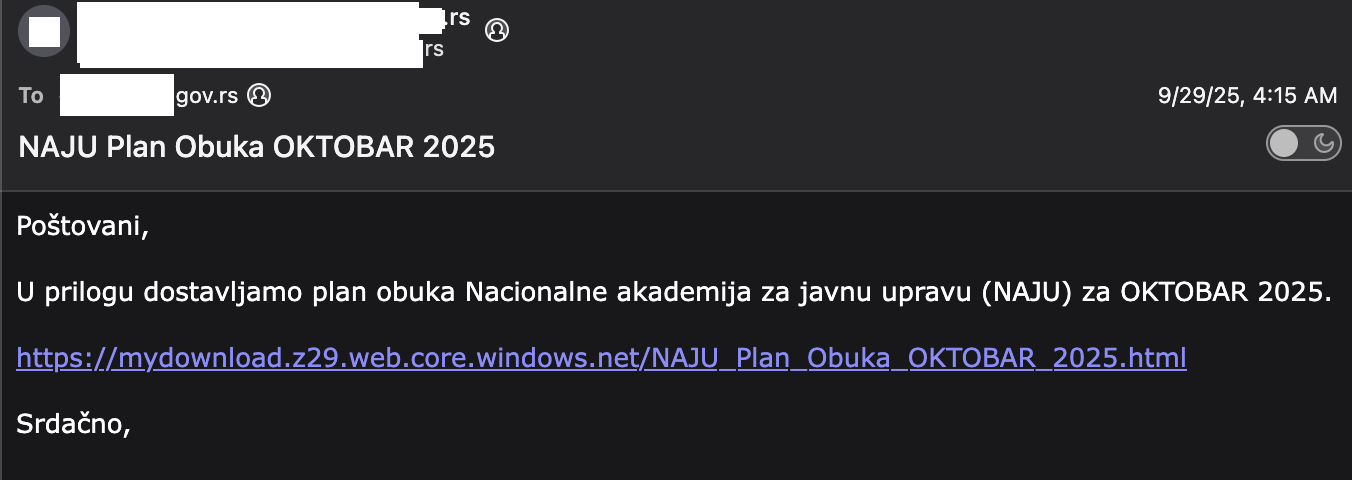
- The initial intrusion began with a spearphish targeting a Serbian governmental aviation department that led to similar activity in other European nations.
- Landing pages mimicked Cloudflare turnstile and used a decimal/XOR obfuscation to hide next-stage URLs, enabling pivoting by researchers.
- The ZIP archive contained an LNK that executed an obfuscated PowerShell which carved a payload from the ZIP by skipping bytes and extracting a tar file in %TEMP%.
- Extracted artifacts included cnmpaui.dll and cnmpaui.exe, with the DLL sideloading technique abusing a Canon Printer Assistant binary (cnmpaui.dll) — a consistent artifact across campaigns.
- Identified infrastructure and domains included mydownload.z29.web.core.windows.net and naturadeco.net, with related phishing links for other targets across Belgium, Hungary, Italy, and the Netherlands.
- Pivots based on shared filenames, sideloaded DLL names, and unique encoding patterns found additional malicious ZIPs/LNKs and MSI carving techniques from older campaigns.
- Attribution: long-standing linkage of the sogu/plugx/korplug toolset to Chinese threat actors, primarily for espionage, with occasional financial outliers and rare red-team/researcher builder sightings on VirusTotal.
MITRE Techniques
- [T1566] Phishing – The campaign used targeted spearphish emails with links to fake Cloudflare turnstile pages to lure victims (“spearphish email”, “links sent to targets”).
- [T1204.002] User Execution: Malicious Link – Victims clicked links that led to landing pages hosting obfuscated next-stage URLs and downloads (“Upon clicking the link, the target is presented with a fake Cloudflare turnstile-style page”).
- [T1105] Ingress Tool Transfer – The ZIP delivered to victims contained embedded payloads (DLL/EXE) that were carved and extracted then executed (“NAJU Plan Obuka OKTOBAR 2025.zip”, carving bytes then untarring to extract cnmpaui.exe/cnmpaui.dll”).
- [T1218.011] Signed Binary Proxy Execution: Mshta/Explorer/Winword-style – Sideloading was used by naming the malicious DLL to match the expected DLL for a legitimate Canon Printer Assistant binary (cnmpaui.dll) to achieve execution.
- [T1059.001] PowerShell – The LNK executed an obfuscated PowerShell command that read bytes from the ZIP, wrote a carved file to %TEMP%, and executed it (“the lnk executes an obfuscated powershell command -w 1 -c … [System.IO.File]::ReadAllBytes … Start-Process …cnmpaui.exe;”).
- [T1027] Obfuscated Files or Information – URL and payload obfuscation used decimal XOR transforms and byte-offset carving to hide next-stage URLs and payloads (“series of decimal values … key (23) and encoding mechanism (xor, ^)”, “reads data from the zip file after skipping 726 bytes”).
- [T1071.001] Application Layer Protocol: Web Protocols – The actor hosted landing pages and payloads on web hosting such as web.core.windows.net domains to deliver malicious content (“mydownload.z29.web.core.windows.net … mydownloadfile.z7.web.core.windows.net”).
Indicators of Compromise
- [File Hash] top-level and artifact hashes – NAJU Plan Obuka OKTOBAR 2025.lnk: 0d0dd1cbde02e4e138c352b82a0288cc; NAJU Plan Obuka OKTOBAR 2025.zip: f2d1fa1890e409996ed4a23bc69461fe.
- [File Hash] extracted payloads – cnmpaui.dll: 87e5299688e3fdae19bff67d760b533b; cnmpaui.exe: 0538e73fc195c3b4441721d4c60d0b96.
- [Domain/Hosting] malicious landing pages – mydownload.z29.web.core.windows.net, mydownloadfile.z7.web.core.windows.net (used for phishing landing pages and payload hosting).
- [Domain] C2/Callback – naturadeco.net observed as a SOGU connection during execution (decoy PDF shown during execution connected to naturadeco.net).
- [File Name] recurring filenames used as lures and for pivoting – NAJU Plan Obuka OKTOBAR 2025.zip / .lnk; Agenda_Meeting_26_Sep_Brussels.zip; and other related ZIP/LNK pairs.
Read more: https://strikeready.com/blog/cn-apt-targets-serbian-government/